Why WAN interface needed DHCP option enabled?
-
Hello. I am new to the IT world and I don’t understand why the WAN interface needs the DHCP option if I have static ipv4 and default gateway data on the main routing interface. How does DHCP work for WAN? I now see that the WAN interface is assigned an IP xx.xx.xx.xx
How, then, does it provide routing through my provider's gateway? If I select “Set static IPv4” and set the data that the provider sent me (I have one static IP), the Internet will disappear on all devices connected to the local network interface. Thank. -
If you have a static address, you don't need DHCP. However, as a default gateway is normally provided by DHCP, you'll also have to manually configure that. Your ISP should be providing you with the address.
-
@JKnott thanks for answer. I entered all the necessary settings. WAN works, but here's a LAN without network access. I suspect that the matter is in the routes. The packet goes to my LAN gateway and then ends. I can’t find the settings I need in webGUI. All packets must go through the WAN default gateway. Is this the correct logic?
-
I don’t understand why the WAN interface needs the DHCP option if I have static ipv4 and default gateway data on the main routing interface.
The short answer is, It doesn't.
How does DHCP work for WAN?
This question is somewhat left up to interpretation, but DHCP works the same on WAN as it would with any other device configured for DHCP that is attached to a network. It sends broadcasts over the wire looking for a DHCP server. If you're looking for a more in-depth review of the DHCP process, that's a topic for another thread.
How, then, does it provide routing through my provider's gateway?
The DHCP server pushes all configuration parameters to the client for routing, dns, etc.
If I select “Set static IPv4” and set the data that the provider sent me (I have one static IP), the Internet will disappear on all devices connected to the local network interface.
If you purchased a static IP and configured the WAN interface with the necessary info, then your firewall should be functioning. If not, then I would first double check your settings for typos. If no typos are found, then I would call your ISP because they may have something misconfigured on their end, which I've seen before.
Once the ISP verifies their end, then you have to troubleshoot routing and firewall rules on your end. In order for clients to get on the internet, they need a default gateway, which is the IP configured on the LAN interface. So, first, verify that your clients are using PFsense as the default gateway. Next, verify that PFsense itself has a default gateway set (System -> Routing -> Gateways). You will see something similar to this:
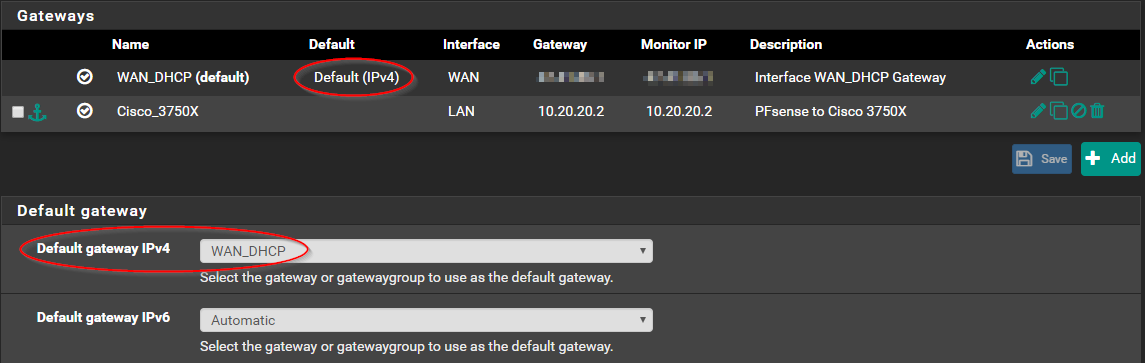
By default, the "Default gateway IPv4" option is set to "Automatic" and 99% of the time the system finds what it needs and everything works as intended, however, I have seen systems lose their default gateway on occasion which causes loss of internet connectivity on the LAN and prompts this setting to be specified manually. Which is what happened to me several months back and is why I have mine manually specified. If you do not see a "Default (IPv4)" designation or it's listed on the wrong interface, this is undoubtedly your issue. You may have to set your default gateway manually.
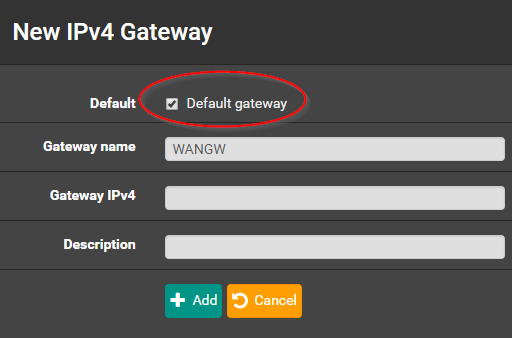
One thing that may have happened in the beginning is when you added the upstream gateway on your WAN, the "Default gateway" option may have been unchecked by mistake:
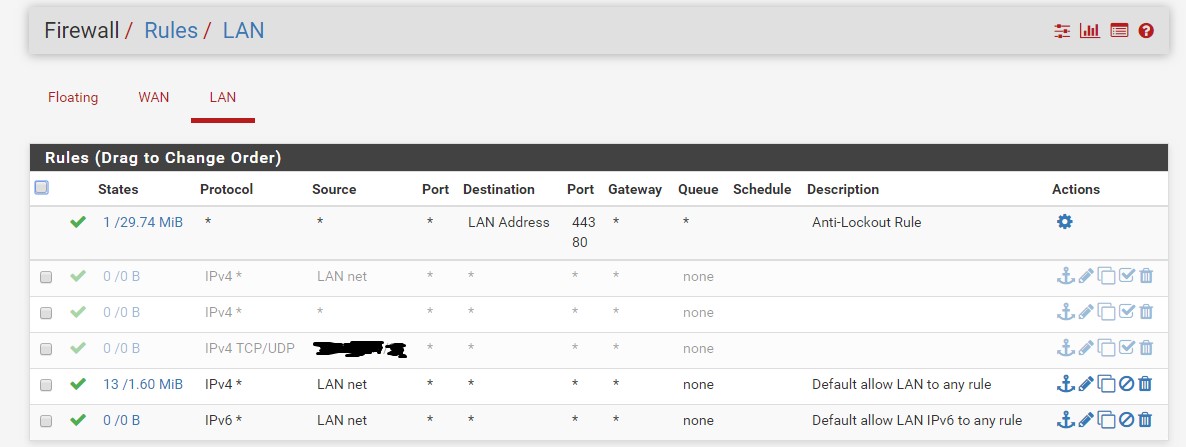
Next would be firewall rules (Firewall -> Rules -> LAN). Out of the box, there should be a LAN net/any rule. If that's been modified away from the default, the current rule will need to be inspected.
-
@marvosa, hello! Thanks for answer. I rechecked all the points about which you wrote: the default gateway is set correctly, the rules for the firewall are set correctly. I have a funny situation: virtual machines have an Internet connection if the external virtual adapter (WAN) is configured to receive parameters via DHCP. If I enter the static parameters for IP and gateway, then the Internet will immediately disappear on the virtual machines. I contacted the ISP and explained the situation. To be honest, I do not fully understand how this is possible. When DHCP is enabled for WAN - the Internet works correctly, but if I prescribe static parameters (IP, netmask and default gateway) - it is missing, although the ISP has given me these parameters.
-
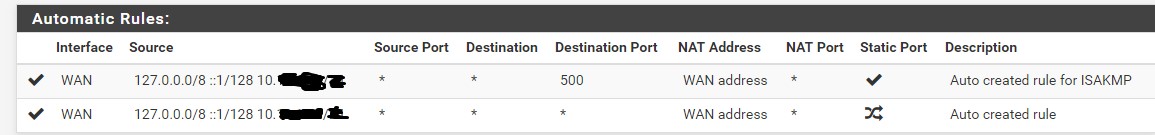
Sorry, I have to clarify what I need to do. Currently, addresses on the local network 10.xx.xxx.xx do not use NAT. In NAT, this rule is (created automatically). I have several virtual machines in Hyper-V, but only one static address (registered on the host). I am noob, and I don’t understand how to do it in pfSense. Screenshot of rules:
-
Ok, something's not adding up. We need a better picture of your design. Can you post a network map, so we can see how things are connected and configured?
Using a hypervisor adds a layer of complexity, but your VM's shouldn't care about how the WAN on your firewall is configured. Is PFsense virtualized?
-
@marvosa yes, pfSense is virtualized.
I'm sorry, this is my first experience in drawing a network card. But I see it somehow.
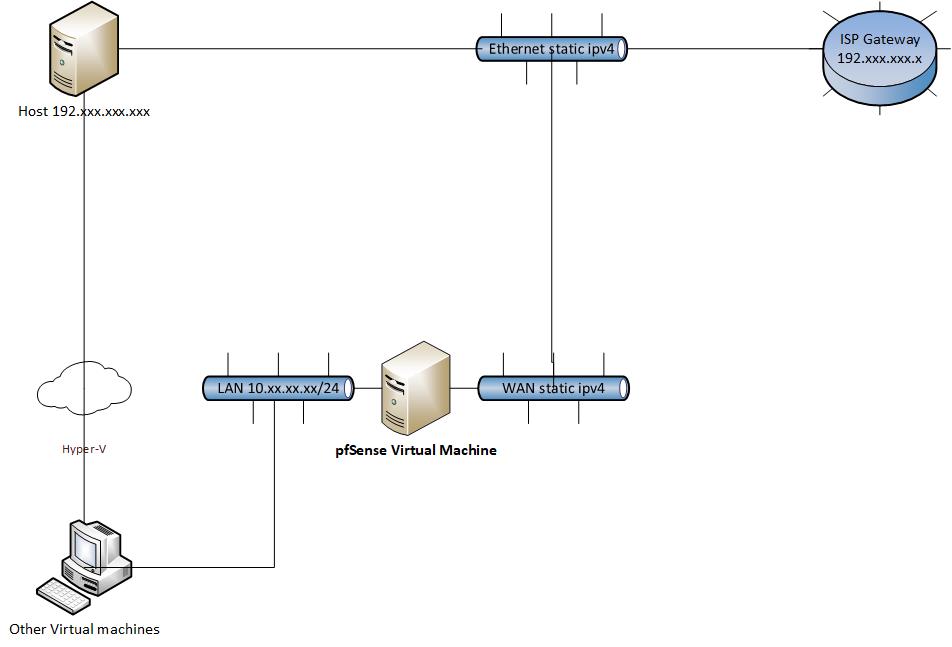
LAN and WAN - its a virtual hyper-v adapters.
WAN - Exnternal virtual adapter - static ipv4. WAN - copy of physical adapter settings.
LAN - Internal virtual adapter, works in sub network 10.xx.xx.xx/24 and use DHCP.
Internet on virtual machines does not work if I prescribe static settings issued by my ISP. But I do not understand what's the matter, if the same settings are registered on the physical Ethernet adapter on the host - everything works fine.
I created another forum topic with a more detailed description of my problem (yes, I know that it is wrong to copy-paste, but initially I did not know what the specific reason was, i'm sorry).
Here more detail: https://forum.netgate.com/topic/142123/pfsense-on-vm-internet-not-working/7
Thank you for help! :) -
The fact you're seeing automatic rules for the 10.x.x.x, LAN, subnet there shows you have the gateway correct when you made that screenshot. But was that using DHCP?
Even if you have the gateway not on the actual interface that would break NAT for clients behind pfSense the gateway should still show as up as long as it responds to ping.
I see you have a gateway on LAN too which can confuse things but since that is not in the auto rules that too looks correct.
I'm not sure why you have obscured the subnet you're using on LAN. It's in the private 10/8 range. No body can do anything with that info and obscuring it just means we can't spot any possible mistakes.
Steve
-
@stephenw10 i'm sorry for incorrect information about my LAN network. My LAN subnet is 10.10.10.1/24. I use this guide for setup my virtual adapters: https://docs.netgate.com/pfsense/en/latest/virtualization/virtualizing-pfsense-with-hyper-v.html
In my case, LAN connection type is Internal, not a private network.
Its looks like:
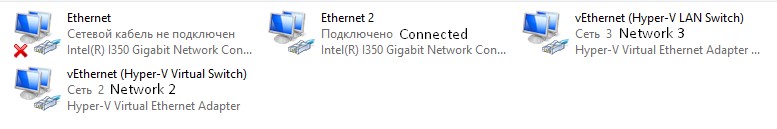
Ethernet 2 - Network Bridge - vEthernet (Hyper-V Virtual Switch).
Yes, LAN using DHCP. -
Hmm, if you have only on static IP in the 192.x.x.x range when you set the pfSense WAN to use it are you removing it from the host? Only one of those things can use that IP at a time.
Steve
-
@stephenw10 Yes, I am trying to use the same IP address for the host and the pfSense virtual machine. I'm sorry for wasting your time. Tell me, please, in my network pfSense filters only traffic addressed to virtual machines, right? Host not protected by pfSense? And can I implement NAT for pfSense in order not to buy an additional public IP?
-
It is possible to do that, yes. However I'm not familiar with the exact terms used by Hyper-V to do it.
You could just set the host to DHCP since that seems to work. But you might lose connectivity to it. You need to have some out-of-band connection to it to be sure you can revert that change if necessary.
Steve
-
@stephenw10 I'm sorry for disturbing you, will it be possible to implement such a network scheme using virtualized pfSense: Global Nework -> pfSense Firewall (virtualized) -> Host (192.xxx.xxx.xxx) -> Other VMs
Is it realizable? Or required physical gateway on which pfSense installed? -
It is possible to do that.
Pass the physical NIC through to the pfSense WAN interface or a switch connected to it without the host using that NIC directly. Then give the host a virtual NIC in the LAN subnet so it only has connectivity through pfSense.
As I said though I'm not familiar with the exact way that might be done in Hyper-V.
You should probably ask in the Virtualisation sub-forum.
Steve
-
@stephenw10 Thank you very much for help and advice!
-
To keep things straight, and for performance reasons, I'd recommend adding a 3rd NIC at a minimum (if not a 4th) and dedicating 2 NIC's to your PFsense VM. The configuration would look like this:
4 NIC setup
NIC 1 = Assign to vSwitch0, create vMkernel port group used for management, connect to switch
NIC 2 = Assign to vSwitch1, create port group labeled "VM Network", connect to switch
NIC 3 = Assign to vSwitch2, create port group labeled "PFsense WAN", connect to ISP modem
NIC 4 = Assign to vSwitch3, create port group labeled "PFsense LAN", connect to switch3 NIC setup
NIC 1 = Assign to vSwitch0, shared vSwitch for VMkernel port group (Management) and VM Network port group, connect to switch
NIC 2 = Assign to vSwitch1, create port group labeled "PFsense WAN", connect to ISP modem
NIC 3 = Assign to vSwitch2, create port group labeled "PFsense LAN", connect to switchI use ESXi, so you may have to translate the terms into Hyper-V speak.
A 2 NIC setup will work as intended but has to be configured and addressed properly... much like stephenw10 mentioned.
-
This is going to be significantly more difficult because as understand it hyper-v is running on a hosted appliance. Access to it may be limited. Adding NICs is probably not an option.
Steve
-
Thank you all. I setup network, it turned out pretty simple. I thought External Virtual Switch - its a network bridge in Hyper-V, but its works differently. Probably, i dont uderstand how it works - I watched IP conflict, because my public IP (192.xxx.xxx.xxx) belonged to host, at the same time pfSense tried to use it (because of this there was no network on pfSense VM). I delete ipv4 parametr from External VS, create Microsoft Network Bridge for External VS and Ethernet 2 (my physical adapter with public IP). And its works for me! Now i have internet on all my virtual machines. Also, NAT is work. pfSense routes all packets. Tracert gives me the: 10.10.10.1 -> ISP gateway -> google.com (example). Thank you guys! Without your help, I would hardly have succeeded. :) Very friendly forum!
-
Glad it's working!
Just a note for down the road, eventually you will want to remediate your double NAT situation. In other words, have the ISP configure their modem in bridge mode, so PFsense gets a public IP.