NAT Reflection mode for port forwards not working for internal IPs to access through Public IP.
-
Here's the detail : We have cloudflare DNS to resolve Name to our public IP. Means if someone hits test.domainname.com
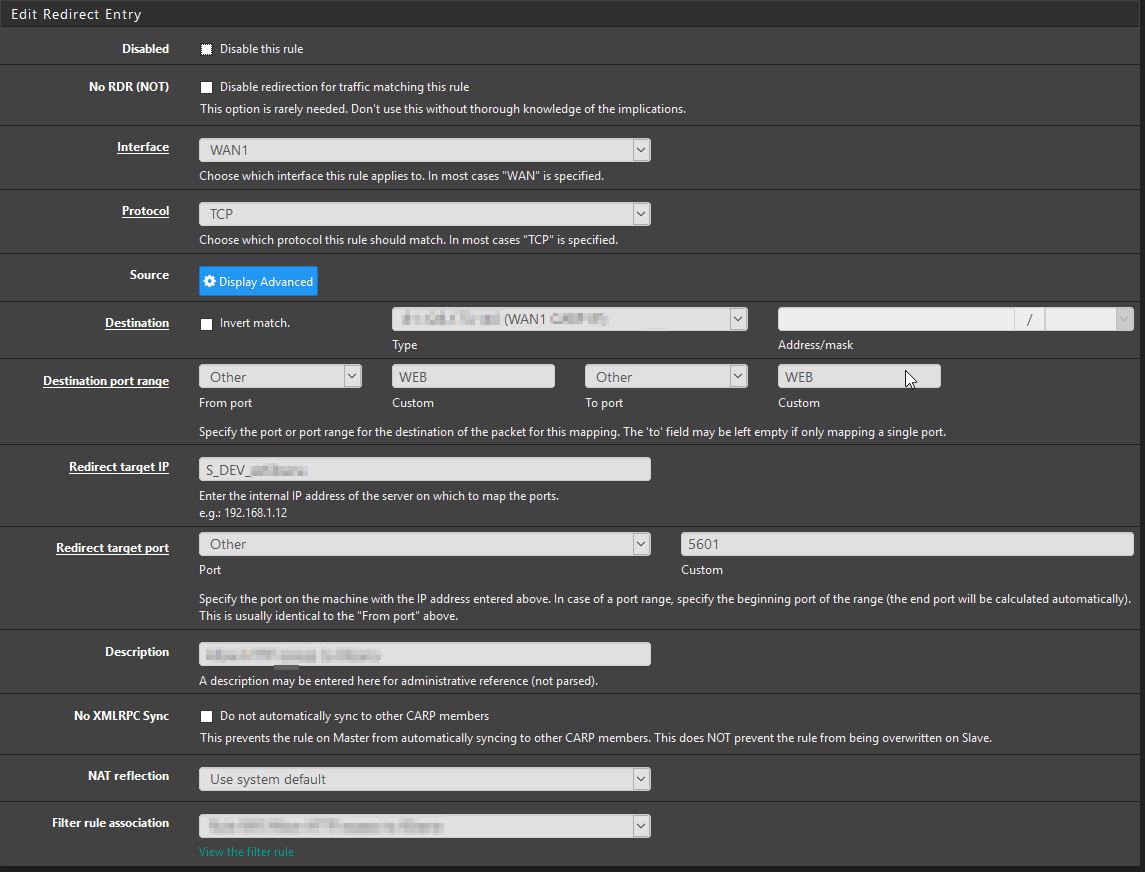
then it will resolve to our firewall's one of the public IP.Now we have created NAT rule to allow our internal resource to be accessible from outside which is inside the one of the VLAN on port 5601 so if someone hits the 80 port on test.domainname.com they will reach to firewall and firewall NAT the traffic to internal resource on 10.10.x.x:5601.
Now the problem is, it is working fine from external network but when someone from internal network behind the firewall hits the test.domainname.com then they get the DNS rebinding error after n number of changes in NAT rule now the error says this site cant be reached.
I found article - https://docs.netgate.com/pfsense/en/latest/nat/accessing-port-forwards-from-local-networks.html
so best match for me is to implement Method 1: NAT Reflection but it doesnt work. I am very much disappointed as it works for everyone i see in forum commenting but why not for us.Here I am uploading NAT reflection rule screenshot which is enabled.
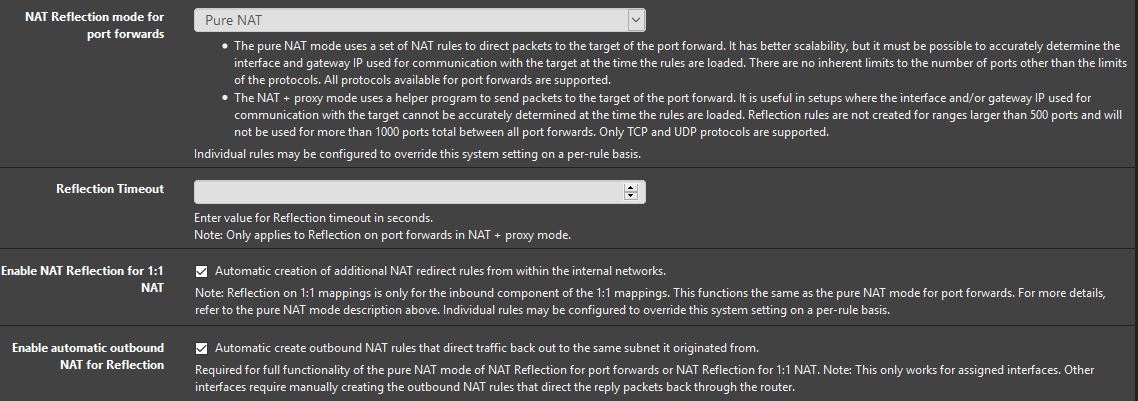
This is a NAT rule which i configured. for NAT reflection tab, i tried with system default/PureNAT/with proxy as well but did not work.
WEB is port 80/443.
Further, I have disabled internal firewall of server as well but no luck. To be clear, We are using internal DNS server, not using firewall's DNS.
I need urgent help on this. We do not want to implement split DNS.
-
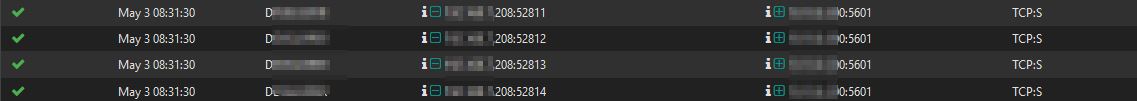
I got logs as below. sync request coming in but no reply goes out.
-
I did something similar before for a client, the NAT rule needed to have NAT Reflection set to Enable (NAT + Proxy). But you may also need a Firewall rule for your VLAN too (depends on your setup), a NAT automatically creates a firewall rule but that is focused on the WAN interface.
In TCP dump you should see the SYN reply on your VLAN or LAN interface not on the WAN interface.
-
@9thplayer said in NAT Reflection mode for port forwards not working for internal IPs to access through Public IP.:
To be clear, We are using internal DNS server, not using firewall's DNS.
So why not add an A record to your internal DNS that resolves your FQDN to its LAN IP address which is method 2 split DNS? Much better than hairpinning out and then back in again just to reach a local resource.