let out anything IPv4 from firewall host itself
-
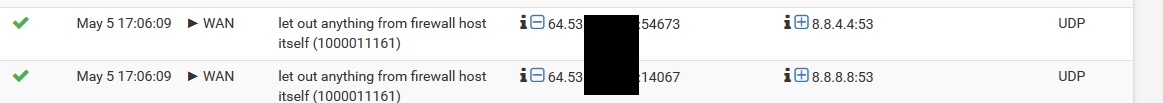
Assuming my WAN IP address is the fictitious 999.99.999.99 as shown in the illustration....
What's the best way to silence these message from the logs (keep them out of the logs completely, (not just use a log filter). ?
-
those are not normally logged, you must of turned on
Log packets matched from the default pass rules put in the ruleset
-
Does he even have that firewall rule (1000003811) on the correct interface? Out rules, like it says in his description, usually don't go on the WAN interface, right?
Jeff
-
@akuma1x said in let out anything IPv4 from firewall host itself:
Does he even have that firewall rule (1000003811) on the correct interface? Out rules, like it says in his description, usually don't go on the WAN interface, right?
Jeff
Jeff, I'm not sure I even created THAT particular rule (1000003811) I can't find it maybe it's a hidden rule?
Is there a way (in pfSense) to do a Rule Lookup by Rule ID Number? Such as some way to search for a particular rule and see it, OR to list ALL rules in a nice neat list? Like I said, I don't see this rule in FLOAT, LAN, WAN OR OPT
-
@johnpoz said in let out anything IPv4 from firewall host itself:
those are not normally logged, you must of turned on
Log packets matched from the default pass rules put in the ruleset
Right. Forgot about that....but IIRC, it seemed to Carte Blanc turn off some other Log Entries that I WANT to see.\
-
@HansSolo I don't know if there's a way to lookup rules by ID number like that, but if you look thru your WAN pass rules, there's a code at the bottom of the settings page.
You didn't name any of your WAN rules "let out anything from firewall host itself"? That should be the rule you're looking for, right there.
Are those YOUR actual firewall logs, or did you grab that image from the internet somewhere?
Jeff
-
he clearly did something with the image because its not freaking possible to have 999 as an octet in an IP address.
You can look up the rule numbers of all rules
https://docs.netgate.com/pfsense/en/latest/firewall/viewing-the-full-pf-ruleset.html[2.4.4-RELEASE][admin@sg4860.local.lan]/root: pfctl -vvsr | grep firewall @111(1000011065) pass out inet all flags S/SA keep state allow-opts label "let out anything IPv4 from firewall host itself"Turn off that log all pass and you wont see those in the log.
Here just turned it on - and yeah its going to be a shitton of noise!
-
@akuma1x said in let out anything IPv4 from firewall host itself:
@HansSolo I don't know if there's a way to lookup rules by ID number like that, but if you look thru your WAN pass rules, there's a code at the bottom of the settings page.
You didn't name any of your WAN rules "let out anything from firewall host itself"? That should be the rule you're looking for, right there.
Are those YOUR actual firewall logs, or did you grab that image from the internet somewhere?
Jeff
No, I didn't name any of them that. That's apparently a pfsense default.
-
That creates the states for the outgoing interface.
If you pass traffic into LAN from a client, that rule creates the state on the outbound interface (typically, but not necessarily, WAN).
Like @johnpoz said, those are not usually logged.
If the pfSense defaults, that work for a great many people, do not meet your needs, you can create specific pass rules with logging enabled to catch the logs you want to see.
-
@Derelict said in let out anything IPv4 from firewall host itself:
That creates the states for the outgoing interface.
If you pass traffic into LAN from a client, that rule creates the state on the outbound interface (typically, but not necessarily, WAN).
Like @johnpoz said, those are not usually logged.
If the pfSense defaults, that work for a great many people, do not meet your needs, you can create specific pass rules with logging enabled to catch the logs you want to see.
Yeah thanks. will do. This firewall is VERY good and at a price noone can complain about. It has a few quirks if you come from a different platform but I'm very happy to have found it. I figure in time as I learn more about it it'll become even easier to use and even better.
-
@johnpoz I know this is old but THANK YOU! I was seeing a million of these entries on a bunch of interfaces, LAN, S2S_VPNs, etc on ONLY ONE of my pfSense appliances and couldn't figure out what the hell was going on!