Allowing users to add/remove/modify additional user accounts but not admin accounts.
-
I am trying to provide some granular access for my users. I would like to allow the following:
- User "admin" can add/remove other users
- User "admin" can update passwords for other users
- User "admin" CANNOT add/remove/modify actual admin accounts
The (user "admin") in this case would be a customers system admin who would be in charge of this type of management for the enduser's company.
The goal is to offload some administration onto the customer but only allow them specific access to do what is most common when it comes to administration of users. (password changes, add vpn user accounts, remove vpn user accounts, ect)
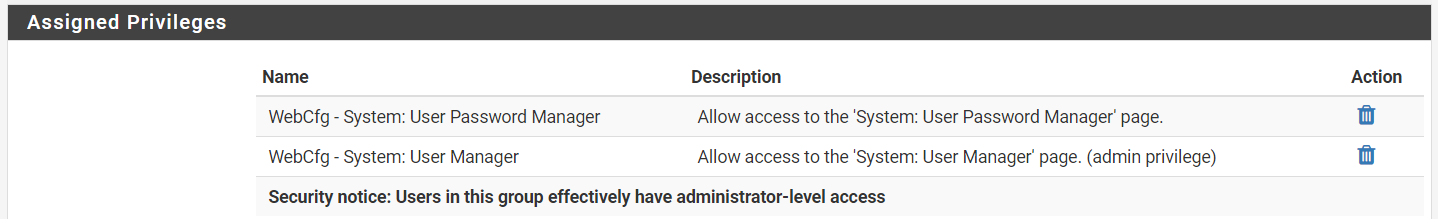
I have looked through the "Assigned privileges" section, but did not find a way to allow this access without also giving them the ability to remove admin accounts or give themselves admin privileges.
Is there a way to allow this specific access?
Version 2.4.4-RELEASE-p1 -
Bumping this to see if there are updated on this.
-
No, and there is no plan to allow that kind of user.
If you need that kind of fine-grained account management, you should be using an external authentication server.
-
Thank you for the clarification, but I don't believe an external auth server would meet these needs either since the user on the FW would still need administrative level access to modify passwords in PFsense. (WebCfg - System: User Manager).
I will still look into this but thank you for clarifying if there is an existing feature I was missing.
-
@jvansyoc said in Allowing users to add/remove/modify additional user accounts but not admin accounts.:
The goal is to offload some administration onto the customer but only allow them specific access to do what is most common when it comes to administration of users. (password changes, add vpn user accounts, remove vpn user accounts, ect)
Why dismissing external authentication? If you use e.g. FreeRadius as Auth Backend to VPN Users or other jobs, your users will be added/edited/updated in FR rather then the User Manager hence the customer has no need whatsoever to even have the privilege to access it. It's depending on your feature set of course, but it's possible with exceptions.
Also if you'd use external auth for pfSense access additionally the customer having access to the user manager wouldn't be a problem for you as your users come from external auth and PWs are not managed in pfSense but e.g. LDAP or AD.
-
@JeGr I see what you mean, the way I currently use the OpenVPN is local authentication. Moving them to the FreeRadius would allow the customer to add and remove VPN users but I will need to test this and see if this provides the granular approach I want.
My current setup is OpenVPN using SSL and user auth via the local database, so in order for users to be added, they would need to have the user made in the "User Manager" and would need the OpenVPN user certificate linked. Using the FreeRadius server package on Pfsense is something I have used as will for MFA on VPN.
Also if you'd use external auth for pfSense access additionally the customer having access to the user manager wouldn't be a problem for you as your users come from external auth and PWs are not managed in pfSense but e.g. LDAP or AD.
The concern is that a user would be able to remove administrator accounts from the firewall even with an external auth server. I should clarify that I'm looking to allow the end-user access to add and remove VPN users without having to contact me or have system administrator access. The suggestion to use FreeRadius is a great idea and I will get back to this with my testing.
-
@jvansyoc said in Allowing users to add/remove/modify additional user accounts but not admin accounts.:
Using the FreeRadius server package on Pfsense is something I have used as will for MFA on VPN.
I'd encourage you to try as - together with OpenVPN - you can actually use FR to implement things you normally would need CSO (client specific overrides) for such as handing out a static ip for specific users or time limits, logout times etc.
So for every RAS VPN setup I always encourage our customers to use OVPN+FR together as it provides them more flexibility.I should clarify that I'm looking to allow the end-user access to add and remove VPN users without having to contact me or have system administrator access. The suggestion to use FreeRadius is a great idea and I will get back to this with my testing.
Then I'd say go the route and couple OVPN with FR :) It will pay out in multiple ways ;)