Can't access XG-7100
-
Hi, I've just configured an XG-7100 and can't access it. I went through the basic setup in our office before then installing it in a rack at the data centre. Here is what I have done...
- Set up two VLAN's on my switch. Ports 1-3 (outside) Ports 4-48 (inside)
- Set up ETH1 on the 7100 to x.x.83.20/29 with gw x.x.83.17
- Set up ETH2 on the 7100 to x.x.86.1/25 (x.x.86.0/25 has been static routed to x.x.83.20)
- Connected uplink 1 in the rack to port 1 on switch and uplink 2 to port 2
- Connected 7100 ETH1 to port 3 on switch and ETH2 to port 4 (inside VLAN) and connected a couple of servers to ports 5 and 6
I can't connect to the 7100 or anything else. Can't ping anything.
The networks guy at the DC says that he can't ping them but he's getting an ARP response...
I am seeing an ARP reply though:
x.x.83.20 00:32:04 MACaddr removed Dynamic ARPA GigabitEthernet0/1/0/10
But, I do however also seem to be seeing ARP entries for your routed subnet as well, which I'd not generally expect to see.
x.x.86.1 00:02:58 MACaddr removed (identical) Dynamic ARPA GigabitEthernet0/1/0/10
x.x.86.121 01:47:54 removed Dynamic ARPA GigabitEthernet0/1/0/10
x.x.86.122 00:02:37 removed Dynamic ARPA GigabitEthernet0/1/0/10(Of note is that both .20 and the .1 are both MACaddr removed- is that the MAC address you'd expect for eth1 or eth2?)
So for some reason both interfaces on the 7100 are returning the same mac address.
Any ideas why? Would appreciate some pointers on how to go about troubleshooting this. It's a little outside my comfort zone.
-
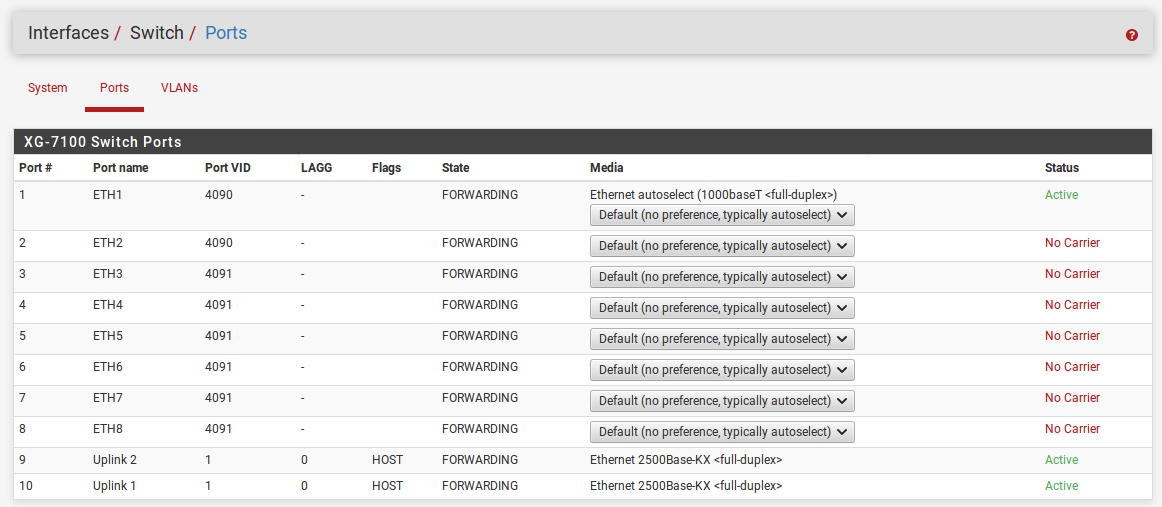
The XG-7100 has one 8-Port Switch, this is why you see the same MAC for all 8 Ports.
By default, ETH1 on the the switch is configured as a WAN interface (VLAN 4090) and ETH2-8 are configured as the LAN interface (VLAN 4091).
Did you touch anything there?-Rico
-
Thanks for the reply. I went through the basic set up wizard via the official documentation and configured both interfaces that way. Even if I made a mess of ETH2 I should still be able to connect to the device on the WAN port. I'm out of ideas.
-
To be honest, I don't understand what your are building up there. So you have a public network connected to your pfSense WAN and another public one to your pfSense LAN? You won't hide RFC1918 networks when posting, right?

What is this static route for?
What exactly can't be accessed? pfSense WebGUI from either WAN and LAN?-Rico
-
@Rico It's configured so that the device doesn't have to be used in "transparent" mode. The firewall is protecting servers that are on public IP's.
The premise as it was explained to me...
.................
we should uplink your router to both of our routers (there will be no additional cost for the extra uplink) using HSRP over a /29 linknet. They will then statically route the /25 to your router for you to use inside of it (this then avoids to need to use transparent mode.HSRP would mean that you would need to connect our 2 routers and your router into an outside VLAN on your switch.
................So I've configured it the way they asked me to. I set up two VLANS on the layer 2 switch (cisco 2960X), configured the interfaces on the pfsense as advised and connected it all up. It's not working unfortunately. I can't see the webgui, or ping the pfsense, or access the two servers I've added.
My level of expertise is not in networking so this is slightly outside my comfort zone.
-
Did you check and follow https://docs.netgate.com/pfsense/en/latest/book/routing/routing-public-ip-addresses.html ?
-Rico
-
@Rico Ahh no I didn't see that! I just assumed the interfaces would be configured separately, although I'm not sure it would make any difference on the WAN port - I should still be able to access that shouldn't I?
This is more complicated than I was expecting. I really appreciate you taking the time to reply. Thank you.
The big question now is...
How do I get back into the 7100 to start again? Is there a "reset to default" sequence on the hardware?
-
You can factory reset via the Serial console.
Well for the WAN port any traffic entering the interface is blocked by the default Firewall Rules.
I would leave the default LAN as your management port, then you can't lock yourself out as happened now. Create a separate OPT Interface for your internal server network.-Rico
-
@Rico Ok thanks for the advice. This may sound like a dumb question but how do I get the second network on the switch? does it all go through ETH1 with this "OPT" interface? So I only need to connect ETH1 to the switch? what about my VLANs? Do I now need to configure the switch differently?
-
The switch config is very good explained by @jimp in this hangout: https://www.netgate.com/resources/videos/configuring-netgate-appliance-integrated-switches-on-pfsense-244.html
For example, I have all 8 switch ports as complete discrete ports for my XG-7100. But you can build any switch config you want. The VLANs are only used pfSense internally in this example.-Rico
-
@Rico Sorry I was referring to my network switch. I set up two VLAN's to accommodate this config but I'm not sure if that is relevant now you have advised about the OPT interface?
-
Assuming we talk about untagged VLANs (Port based) you don't need to change anything there.
If you work with tagged VLANs on this Cisco Switch...well maybe we found your culprit.
-Rico
-
@Rico They are just normal VLAN's
Can you explain what the OPT interface is for? I'm a little puzzled how I would connect the pfsense to my network switch if I'm not using ETH2?
Currently I have ETH1 connected to the first VLAN on my switch for outside - and ETH2 connected to the second VLAN on my switch for inside. If you are saying I should not use ETH2 and configure some sort of "virtual port" OPT1" - how can I connect my servers to it?
-
It's possible to trunk all the VLANs to pfSense across one connection if you need to but that doesn't sound like what you're doing.
There looks to be some confusion here between ports and interfaces. Eth1-8 are ports on the internal switch.
By default the XG-7100 has two interfaces defined:
WAN is connected (by internal VLANs) to port Eth1.
LAN is connected to ports Eth2-8.The way you describe connecting it in your first post seems correct for those defaults. But the fact the provider is seeing ARP replies for the routed subnet implies your Cisco switch is not correctly segregating those two sets of ports. I would check that first.
Because the XG-7100 has an internal switch you could just connect everything to it directly and not use VLANs on the Cisco (or eve at all until you need more ports).
You would have to reconfigure the 7100 switch ports so that WAN was then Eth1+2 to provide connections to both uplinks and LAN was Eth3-8 for connections on the routed subnet.
Let me know if you want to go that way and I'll set something up.
Steve
-
In your Switch assignment for VLANS if you are tagging traffic always ensure that you include ports 9T and 10T (uplink ports) in the port member list otherwise nothing will get through. I had this problem and although Jim Pingle's presentation is clear, this part is not...well it wasn't to me anyways. The XG7100 is different from other appliances because of the built-in switching which is complicated to understand at first.
-
@stephenw10 Thank you for your reply Stephen, I really appreciate it.
I have more than 40 servers to connect, so I need the cisco switch.
It's really hard work standing in the hot aisle trying to configure these on the fly, so I will bring back both the switch and the pfsense to the office and try again. I was sure I had set up the VLAN's correctly.
@claferriere Thanks for responding too. I don't believe I'm using VLAN tagging on the Cisco switch - I haven't set anything up to do that.
I believe the networks guy at the DC recommended I use VLANs in order to prevent running the pfsense in "transparent" mode - so while I'm dealing with two public networks, one is inside and one is outside as far as the firewall is concerned. If this isn't the best way to achieve it, I'm very open to suggestions, especially a configuration that is more simple. I can reset both these devices to factory defaults and start again. (not sure how to do that on the pfsense).
I can ask them to change the network to a single uplink for just the /25 I need (which is what I'm accustomed to).
-
@Chris-187 Not sure I understand the intricacies of your network design, I was just mentioning that on the XG7100 the Switch tab in the interface assignment is new and you need to pay attention to how the VLANs are assigned and how you identify members of that assignment. For me it was simply a question of adding ports 9 and 10 as they are part of the connection to the Denverton Soc. (From the manual: https://docs.netgate.com/pfsense/en/latest/solutions/xg-7100-1u/switch-overview.html) Without these members added to the switch config I could NOT access the internet.
-
@claferriere Ok thanks. The VLANs I created are on a separate switch, not the 7100 itself but I appreciate you taking the time to respond and for the info concerning the 7100 integrated switch.
-
Two uplinks for failover is a good idea, especially if they're not charging you for it.
It's the routed subnet that allows you to avoid transparent mode and that is also a very good idea.
You are going into the Cisco switch and back out into the XG-7100 switch unnecessarily though. Most firewalls do not have a built in switch so you would need to which is why you were instructed to do so but here you can just re-assign one of the Eth ports to WAN and connect both uplinks to it. Then use any of the other ports to connect to the Cisco switch which no longer needs to have any VLAN config on it.
Steve
-
To do that, change the PVID of port Eth2 to 4090 (the WAN internal VLAN) on the ports tab:
Then on the VLANs tab remove port 2 from LAN vlan group and add it to the WAN:
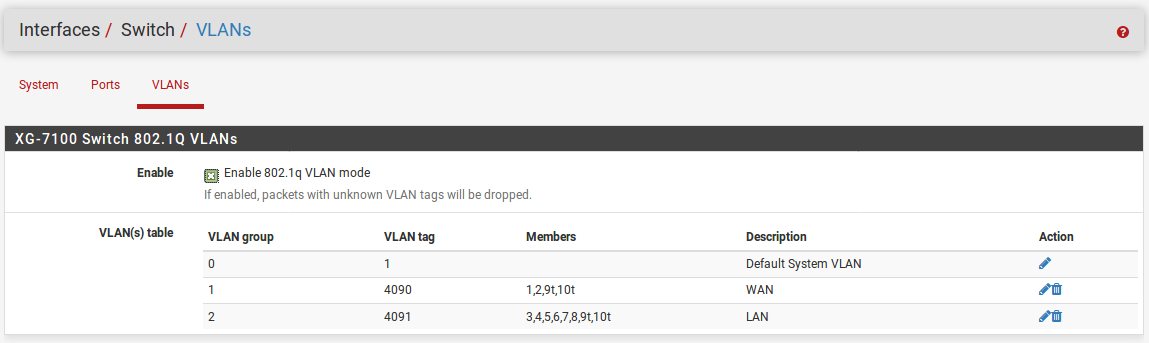
Now you can connect the two uplinks to Eth1 and Eth2 and everything else to the remaining ports.
Steve