Can't access XG-7100
-
@Chris-187 Not sure I understand the intricacies of your network design, I was just mentioning that on the XG7100 the Switch tab in the interface assignment is new and you need to pay attention to how the VLANs are assigned and how you identify members of that assignment. For me it was simply a question of adding ports 9 and 10 as they are part of the connection to the Denverton Soc. (From the manual: https://docs.netgate.com/pfsense/en/latest/solutions/xg-7100-1u/switch-overview.html) Without these members added to the switch config I could NOT access the internet.
-
@claferriere Ok thanks. The VLANs I created are on a separate switch, not the 7100 itself but I appreciate you taking the time to respond and for the info concerning the 7100 integrated switch.
-
Two uplinks for failover is a good idea, especially if they're not charging you for it.
It's the routed subnet that allows you to avoid transparent mode and that is also a very good idea.
You are going into the Cisco switch and back out into the XG-7100 switch unnecessarily though. Most firewalls do not have a built in switch so you would need to which is why you were instructed to do so but here you can just re-assign one of the Eth ports to WAN and connect both uplinks to it. Then use any of the other ports to connect to the Cisco switch which no longer needs to have any VLAN config on it.
Steve
-
To do that, change the PVID of port Eth2 to 4090 (the WAN internal VLAN) on the ports tab:
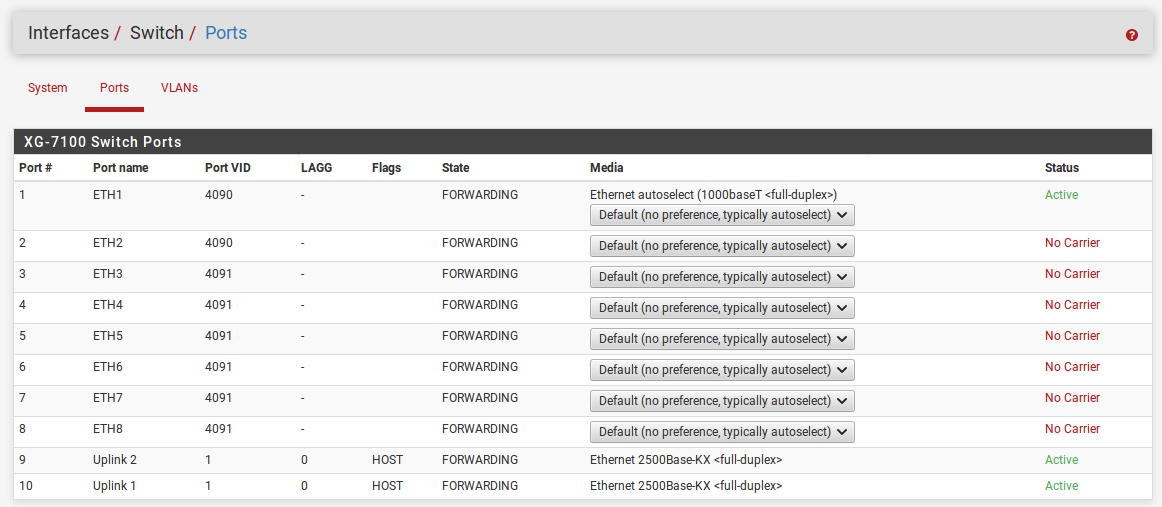
Then on the VLANs tab remove port 2 from LAN vlan group and add it to the WAN:
Now you can connect the two uplinks to Eth1 and Eth2 and everything else to the remaining ports.
Steve
-
@stephenw10 Thanks that's really helpful. My current predicament is that I can't connect to the 7100 at all. I need to be able to either connect to the web interface or reset it somehow. I think I can achieve this simply by connecting the uplink directly to the wan port ETH1, then it should spring into action hopefully.
-
By default there are no firewall rules to allow access on the WAN, you can only access it by connecting from the LAN side.
If you are unable to connect from either you can always connect to the serial console and add rules to allow you to connect to the GUI or reset the config and start over.
https://docs.netgate.com/pfsense/en/latest/solutions/xg-7100-1u/connect-to-console.htmlSteve
-
@stephenw10 I've connected one of the uplinks to ETH1 and my laptop to ETH2 by putting it on the same subnet. I can now access the pfsense GUI.
I've set up the WAN interface exactly as described. x.x.83.20/29 with gw x.x.83.17
I've set up the LAN interface to x.x.86.1/25 with a gateway of x.x.86.0I still can't access x.x.86.1 from outside.
-
I wonder if I can start this thread again....
I have an XG-7100 rack mount. It is now in my office to be pre-configured to be fitted in a data center.
My requirements are that I need to use the device to protect a bunch of servers that are on public IP's
I have two 1GB uplinks and my WAN is as follows...
x.x.83.20/29 with a gw x.x.83.17
I set up the WAN interface to a single uplink on ETH1as above for testing
My servers will need to be on the following network
x.x.86.1/25 with a gw of x.x.86.0 which has been statically routed to x.x.83.20
I set up the LAN interface as above on ETH2 but have been unable see the servers that are connected via a layer 2 switch to ETH2 and I can't connect to x.x.86.1 for the pfsense gui.
I couldn't get this to work after two attempts, so I have now removed the device from the data centre and brought it back to the office.
Any help greatly appreciated.
-
I still can't access x.x.86.1 from outside.
Have you added rules to allow that?
By default all inbound connections on WAN are blocked. Check the firewall logs Status > System Logs > Firewall
You have a laptop connected to Eth2. I assume that is still in the LAN at this point? You have not moved it to be the other WAN uplink yet?
Steve
-
@Chris-187 said in Can't access XG-7100:
I've set up the LAN interface to x.x.86.1/25 with a gateway of x.x.86.0
?
-Rico
-
Ah! Yes that's wrong.
If the pfSense LAN IP is x.x.86.1 then servers in the LAN subnet should be using x.x.86.1 as their gateway.
The LAN interface itself should not have a gateway defined on it.
Steve
-
Ok, there was no gateway defined - it was configured how you say in your most recent response.
You asked if I have set up firewall rules? No.
I couldn't see any rules defined so I just assumed I was starting with a blank slate. I hadn't got around to looking into the firewall yet - I just wanted to get this set up so I can start to configure it.
The documentation suggests that the deployment starts with setting up the WAN and LAN interfaces, then connecting to the GUI to continue configuring. I've done that but I can't connect to it. It doesn't say anything about the firewall. I guess it assumes you are always going to be on the LAN so you can connect to the LAN port at any time. I need to connect from outside so I guess it is different.
What do I need to do so I can connect to the public IP x.x.86.1 to login to the GUI?
-
From the LAN side you should be able to connect already there are default rules allowing that.
From the WAN side you need to add rules for any connection you want so to hit the pfSense webgui from WAN on the LAN IP (something you can do because it's a routable IP) add a new firewall rule on WAN like so:
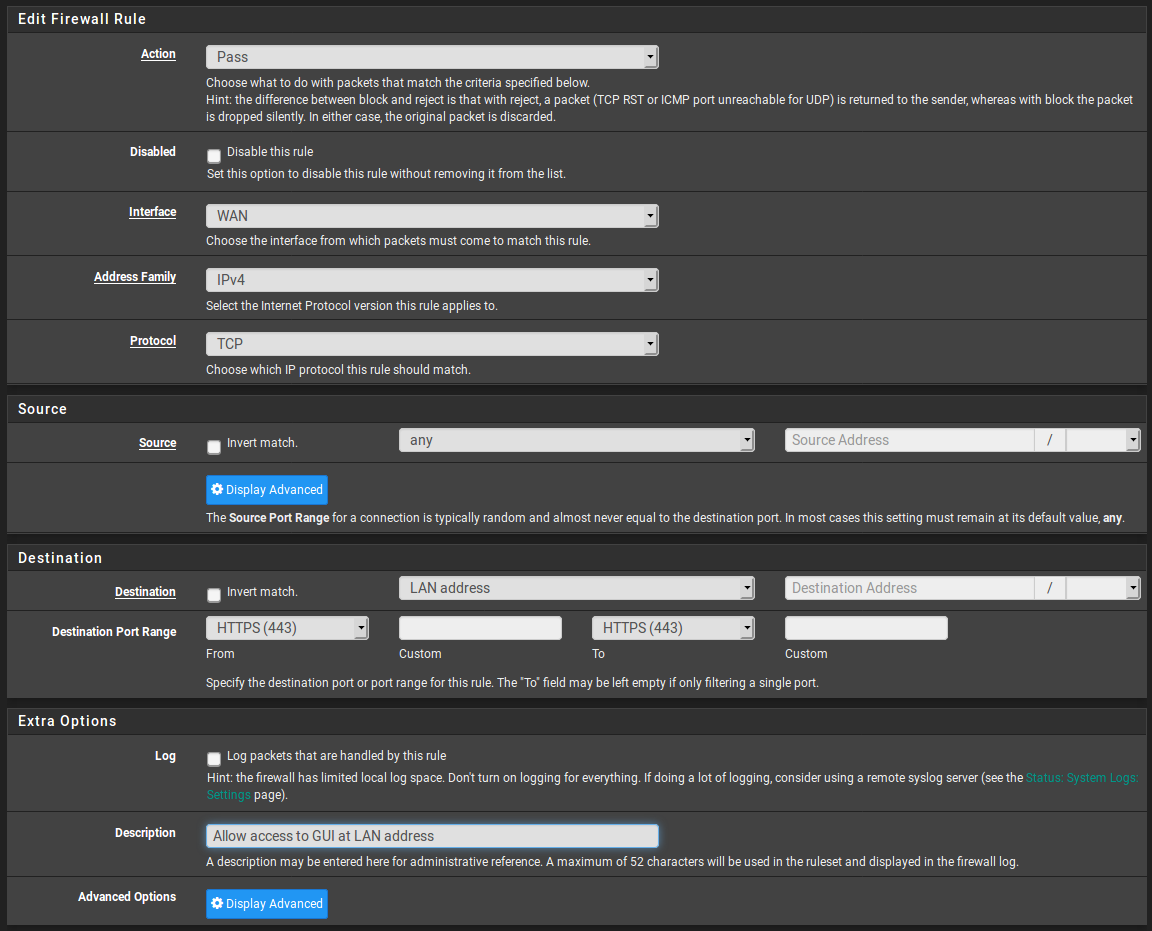
Steve
-
Thanks, I'm a bit confused. For clarity, there is no actual LAN here - so unless I connect directly to the XG-7100 I have no access to this device.
Do I need to set up individual rules for individual ports on the WAN interface for access to the LAN interface?
I assume I've not been able to connect to the "LAN" IP's from outside, simply because there are no rules set up to allow that via the WAN firewall rules.
The point of this is to protect the so called "LAN" IP's and all traffic inwards has to come through the WAN first, so if for example, I want to connect to a server in the LAN network on port 53, Do I have to set the rule both on the WAN interface AND on the LAN interface? Or just on the WAN, with destination of "Lan Address".
This interface is not what I'm used to. In other software it's possible to provide a comma separated list of ingress and egress ports, rather than setting a rule for each one. Is that possible here?
-
WAN and LAN are just the default names there, you could use External and Internal equally. Because the subnet you are using is public that make less sense but it's just two interfaces.
You can just add an allow all rule and you could access everything but that's probably not what you want.

You can use Aliases in the firewall rules to simplify them. The Aliases can be lists of ports or IPs so you can have a rule that says 'pass traffic for destination "Server_Group1" to ports "Allowed_Ports3"` for example.
Those are configured in Firewall > Aliases.
https://docs.netgate.com/pfsense/en/latest/book/firewall/aliases.htmlYou will probably want to disable outbound NAT in this configuration (in Firewall > NAT > Outbound) so that servers behind the firewall use their own IP for outbound traffic.
Steve
-
Still no joy with this at all.
I've disabled packet filtering altogether and I still can't connect to anything from outside. Doesn't make any sense.
-
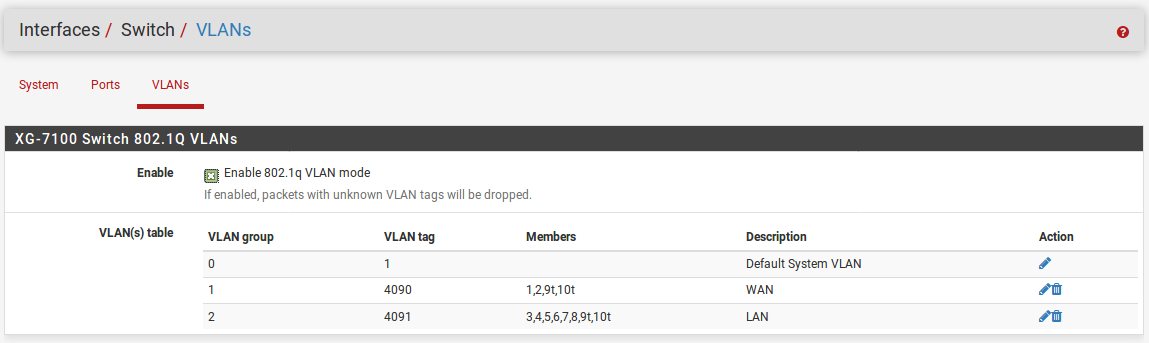
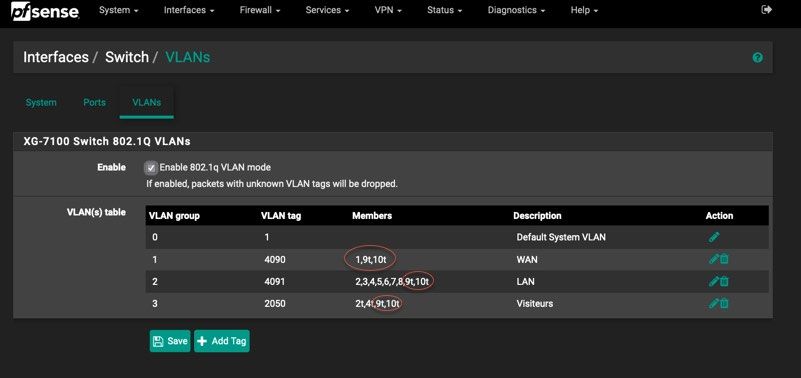
@Chris-187 I think you may need to look at your interface assignments, specifically the VLAN and Switch settings. I had similar problems and when creating VLANS, you MUST ensure that you include members 9T and 10T. These are the Denverton Soc. Check the manual as the Switching implemented on this unit has a Switch LAGG where ix2 and ix3 (switch uplink ports 9 and 10), are configured as a load-balanced LAGG. This provides an aggregate uplinkcapable of 5Gbps for ethernet switchports ETH1-8. So you cannot disregard them as members of your VLAN configuration.
Under the Switch tab for VLANs in the Interface assignments, you must list the members of a VLAN. IF you omit to include 9T and 10T, it will NOT pass anything through.
Manual Page 6 and 7:
https://docs.netgate.com/manuals/pfsense/en/latest/xg-7100-1u-security-gateway-manual.pdf
Check out an image of what I had to do (for a simpler setup) You see 9t and 10T in ALL assignments. If you miss this, it will NOT work...
-
@claferriere That's definitely not the problem. The VLAn's are set up exactly as @stephenw10 showed in his screenshots. All I did was remove eth2 from the LAN and add it to the WAN when setting it up for both uplinks.
I don't believe I have any settings wrong. I have configured the interfaces correctly and I've disabled the firewall but I can't access the LAN IP from outside. I wonder if the static routing hasn't been configured by the network team here. How can I test that?
-
Now that I've disabled the firewall shouldn't I at least be able to ping the WAN IP assigned to the pfsense?
-
Yes you should. Can you ping out from pfSense?
You can try running a packet capture on the WAN in pfSense whilst you ping it. You should see those pings arriving even if pfSense is unable to respond.
You might see ARP requests from the ISP if pfSense cannot respond to ARP.Try running a traceroute to the LAN side subnet from somewhere external. You should see that go through your WAN subnet.
Steve