em2: can't handle af***
-
Hello dear members
since I attached second wan to my pfsense VM and create outbound NAT for passing traffic from this gateway for example 6 client, print"em2: can't handle af***" on pfsense console and Status>System Logs>
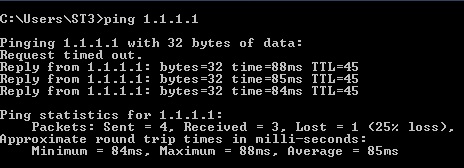
I pinged internet ( 8.8.8.8/1.1.1.1 and so on) from that client's who passing their traffic from second gateway and always the first packet is lost.***: represent random number
em2: represent second WAN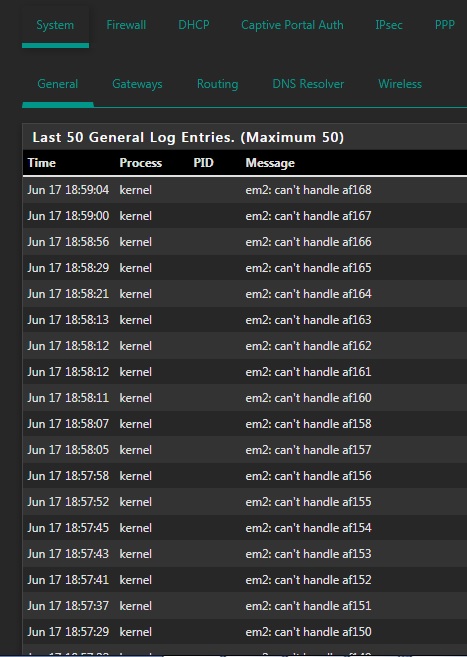
Please guide me
Thanks in advance -
@m2ghz said in em2: can't handle af***:
af***
Are they even valid af markings ?
I'd be tempted to pop a PC onto your second WAN and do a packet capture and look at the packet markings, I've never seem them in the hundreds.
From a Cisco device.
Router(config)# class-map match-all VOIP
1751-uut1(config-cmap)# match ip dscp ?
<0-63> Differentiated services codepoint value
af11 Match packets with AF11 dscp (001010)
af12 Match packets with AF12 dscp (001100)
af13 Match packets with AF13 dscp (001110)
af21 Match packets with AF21 dscp (010010)
af22 Match packets with AF22 dscp (010100)
af23 Match packets with AF23 dscp (010110)
af31 Match packets with AF31 dscp (011010)
af32 Match packets with AF32 dscp (011100)
af33 Match packets with AF33 dscp (011110)
af41 Match packets with AF41 dscp (100010)
af42 Match packets with AF42 dscp (100100)
af43 Match packets with AF43 dscp (100110)
cs1 Match packets with CS1(precedence 1) dscp (001000)
cs2 Match packets with CS2(precedence 2) dscp (010000)
cs3 Match packets with CS3(precedence 3) dscp (011000)
cs4 Match packets with CS4(precedence 4) dscp (100000)
cs5 Match packets with CS5(precedence 5) dscp (101000)
cs6 Match packets with CS6(precedence 6) dscp (110000)
cs7 Match packets with CS7(precedence 7) dscp (111000)
default Match packets with default dscp (000000)
ef Match packets with EF dscp (101110)
Router1(config-cmap)# match ip dscp af31 -
I recently had the same issue and I was able to fix it. I know it is probably to late for you but I'll provide the solution . Maybe someone else need it too.
The issue with 'can't handle afxxx' can be fixed by creating a firewall rule on the internal interface (LAN) and allow traffic thru the proper gateway. The steps needed to fix it are:Go to Firewall menu -> Rules then select LAN interface (instead of LAN you should use the name of your local network interface)
Click add to top button and fill the filelds properly.
and fill the filelds properly.How to fill the fields properly:
Action: Pass
Interface: LAN
Protocol: Any
Source: 'Single Host or Alias' or 'Network' and type the IP or Alias or Network you want to use with the second WAN
Destination: Any
Click Display Advanced button
Go to Gateway and select from the list the default gateway for your second WAN
Click Save

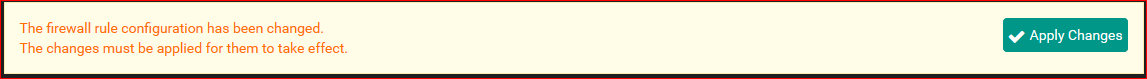
Click Apply Chnges