Disable or whitelist sshguard
-
SG-1100 running 2.4.4-RELEASE-p3 (arm64)
I am randomly unable to logon to gui via https from the machine running our network mgmt apps. I found this logged which is the IP of the mgmt machine:Jun 19 17:33:48 sshguard 27748 Blocking "192.168.25.121/32" for 960 secs (3 attacks in 1571 secs, after 4 abuses over 15079 secs.)
Based on the 2.4.4 p3 release notes I believe sshguard is overriding the firewall rules allowing connections to ports 22, 443.
I am unable to find any documentation re. how to disable or whitelist sshguard. Where is the documentation and settings for this "feature".
Thank you.
-
Try: System > Advanced > Login Protection
-
I have whitelisted, thank you for the pointer.
I'm unable to find any documentation for "Login Protection" or sshguard other than it's a new feature. Netgate, pls document everything.
-
@pfnewb2016 said in Disable or whitelist sshguard:
believe sshguard is overriding the firewall rules allowing connections to ports 22, 443.
Its not overriding the rules - the rules still allow you to TALK to the port... sshguard is just blocking you from logging in because of failed login attempts..
The login protection section in the gui is pretty straight forward on the settings..
-
@johnpoz
Nope, sshguard blocks talking to the port, the webpage doesn't load. This is not a failed login, it happens before that and is documented here. The effect is that sshguard is overriding the Firewall Allow rules. In my case sshguard saw failed logins on snmp and ssh and blocked the the source IP from all service ports.Re. "Login protection is straight forward": the gui simple enough, however:
-
It's not documented that by default, even with Firewall allow rules in place, it is possible for Login Protection to prevent access to the inside interface on both ssh and https.
-
There is no GUI that shows IP's currently or previously blocked by Login Protection. The log entry only shows the "attack", not the action or duration. IMO, there should be more logging and it s/b either under Firewall or it's own category.
-
The logs are not under Firewall rules, so when you can't login from one PC and then go to the firewall logs and don't see the block it's hard to troubleshoot.
-
The log entries in General are sourced or labeled sshguard, not Login Protection. This make it difficult to correlate the sshguard entry with Login Protection, particularly without any pfsense documentation.
-
-
You should see logged immediately before the sshguard line what triggered it's attack response:
Jun 24 00:17:49 php-fpm 30238 /index.php: webConfigurator authentication error for user 'admin' from: 172.21.16.5 Jun 24 00:17:50 sshguard 65461 Attack from "172.21.16.5" on service 380 with danger 10.That should only ever be for services on the firewall itself.
Steve
-
I am facing the same problem!!
Did you found any solutions for it ?? -
@bhagya_jani2277 said in Disable or whitelist sshguard:
I am facing the same problem!!
What problem ?
The 'solution' was and still is : stop using wrong login name and/or passwords.For SSH login : skip the password login all together, using a cert login.
Web login : have the browser remembering your password and you'll be ok.If some (other) process in pour device (pc, portable, etc) is hammering port 22 or 80 or 443 on pfSRnse, then yes, your device - the IP - will get blocked.
-
@gertjan I am trying to access my pfsense from wan but SSHGUARD is blocking the both GUI and SSH ports and whenever I try to access from WAN so it refuses .
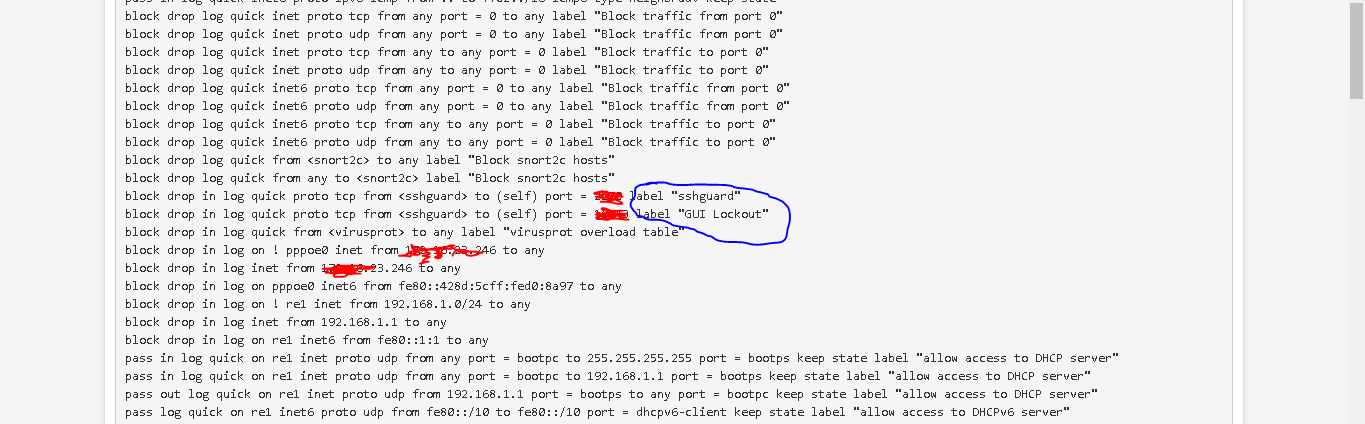
I found this thing by running this code pfctl -sr and in result i found this :
-
Those are default rules. They only block you if you've been locked out by entering the wrong credentials enough times.
https://docs.netgate.com/pfsense/en/latest/troubleshooting/locked-out.html#locked-out-by-too-many-failed-login-attempts
Steve
-
Why are 2 threads for the same thing?
-
@johnpoz I was searching for solution and saw this post, So just asked here that they get the solution or not.
-
Ok, let's continue this in the other thread since this appears unrealed to sshguard.
https://forum.netgate.com/topic/160415/having-issues-in-accessing-pfsense-using-ssh