Segmenting with seperate interfaces
-
Hey, so I'm using a WatchGuard XTM 505, it has different front ports. My goal was initially to use VLAN's but I'm pretty sure that I could use the interfaces themselves instead of creating a VLAN, so that's what I've done the problem is that now I've assigned a port to an interface it doesn't pick up and act like the normal network. It can't connect to the device itself, here's how I want the traffic to look:
LAN -> OpenVPN interface -> Internet
LAN1 - > OpenVPN interface -> Internet
etc etcI want each lan to be 100% seperate from each other so I can put one device on a different LAN for security then monitor and shape traffic for each interface. I've also followed this tutorial if this helps:
https://support.nordvpn.com/Connectivity/Router/1089079142/pfSense-2-4-4-setup-with-NordVPN.htmI'm open to posting any logs or explaining futher, thanks.
-
@templateunheard am I allowed to bump this? Still very much need help, thanks
-
I would get your interfaces working correctly first.. Then worry about routing them out vpn.
Say 192.168.1/24 on one network, 192.168.2/24 on the other network.
How are you connecting those ports to your network? You have a vlan capable switch right - or your using multiple switches? You can not just connect them to the same switch that does not isolate the traffic via vlans setup on the switch. Or you have to use completely different dumb switches connected to each port.
While the lan had default rules any any, when you create a new interface be it physical or vlan there are no firewall rules on it.
-
@johnpoz So thanks for the response, I really do appreceate it especially what's happened before.
I'm using a Watchguard XTM 505 So I believe that they are all seperate switches. So here's what I've done:
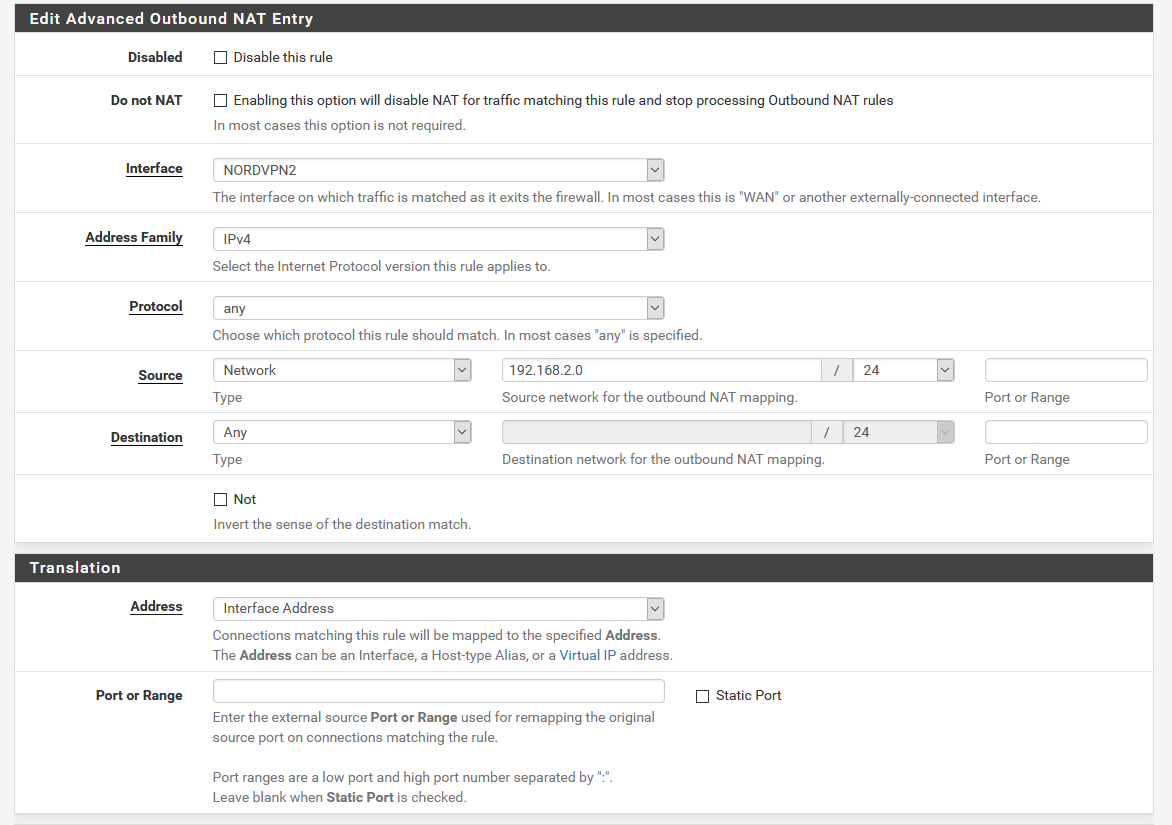
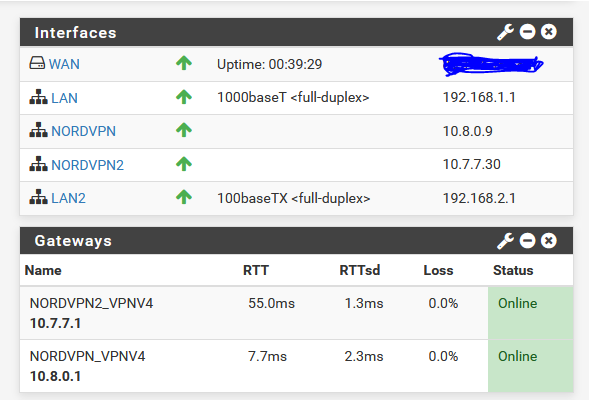
- Assigned a 2nd NordVPN interface (Albanian server) with the same properties as the existing interface
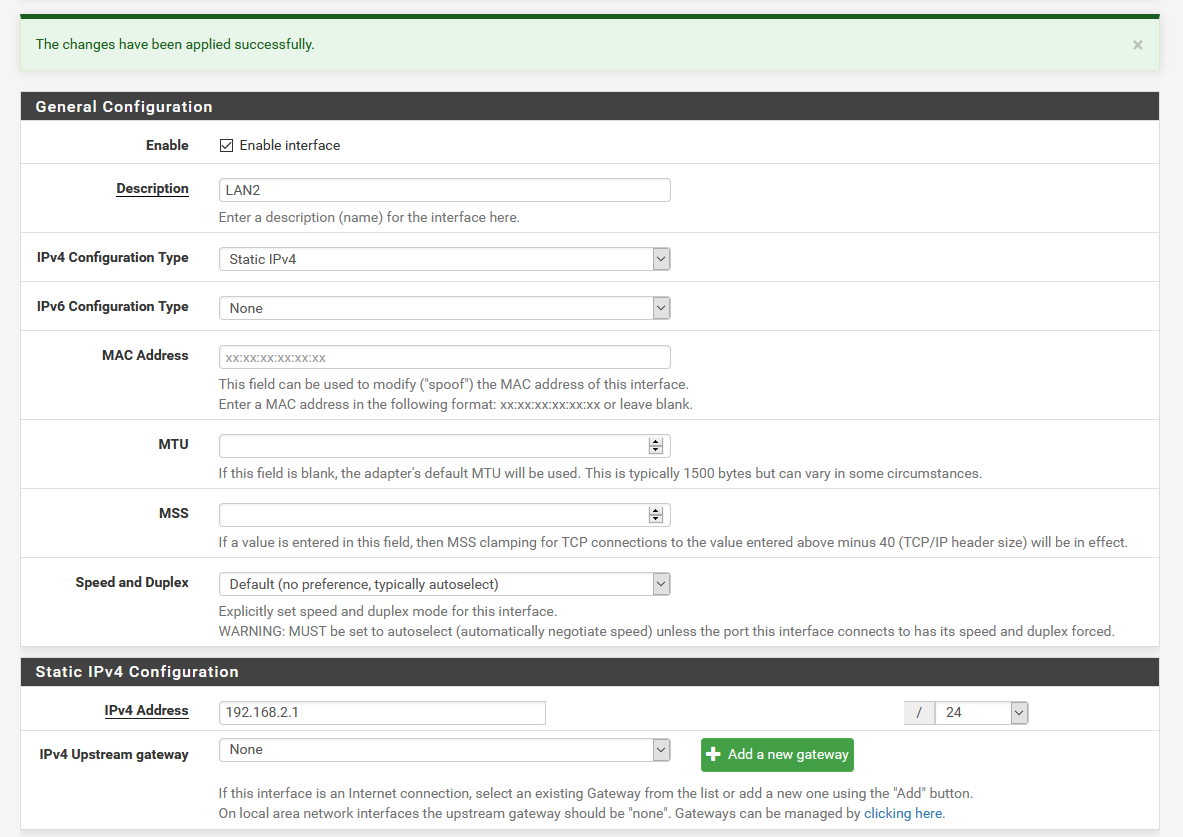
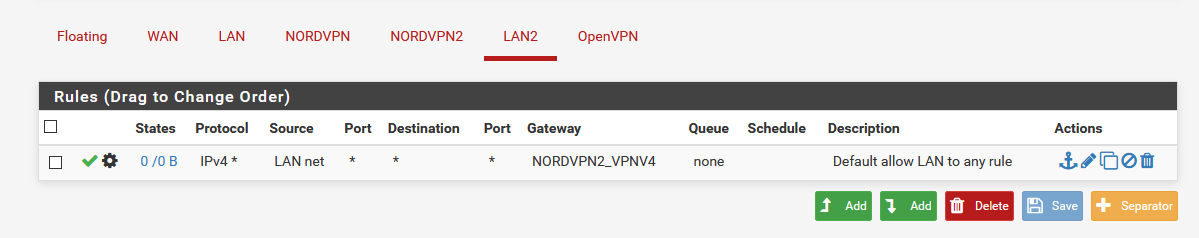
- Assigned a new interface (LAN2) to the port on the front (em2) to be the second LAN (with the subnet 192.168.2.0/24)
- Added a new NAT rule for the new nordvpn2 interface
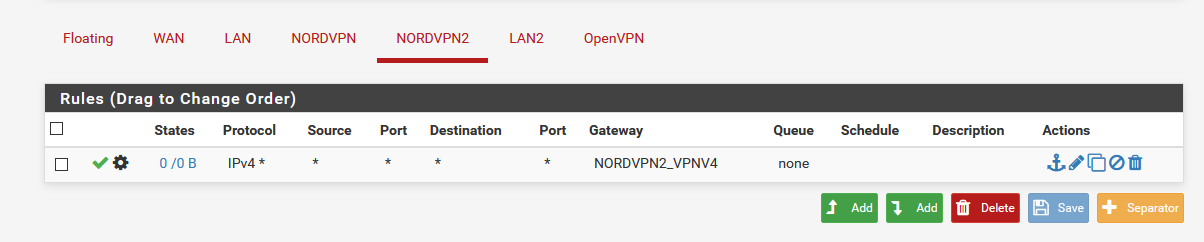
- Added a firewall rule to allow all lan traffic going through the nordvpn gateway (same on the second nordpvn interface)
My Linux machine which is connected to the LAN2 interface can't even access the network let alone go through the vpn, the interfaces themselves seem to be up and running constantly but the second land appears to be working just as good as the first lan, I have no idea why this is happening, any help?
thanks!
-
What your using for a router has ZERO to do what your using as switch(es)
If you connect a box directly to lan2, then it should get an IP and be able to use the internet before you do ANYTHING with vpns
Please attach any images you want me to look at. gyazo.com??
Why are you creating more than 1 vpn interface?
-
- Updated earlier post with images attached, my apologies.
- It should be able to get an IP address and I've assigned it a subnet range of 192.168.2.1/24 so it should work, I don't know why it doesn't hence why I'm asking for help
- I'm creating 2 seperate vpn instances because I want two seperate devices to use 2 vpn connections at once and be isolated from each other.
-
@templateunheard said in Segmenting with seperate interfaces:
It should be able to get an IP address and I've assigned it a subnet range of 192.168.2.1/24
lets fix that before you worry about routing it out a vpn..
So your interface is only 10/100 - so those normally do not support autocross. So is what your connecting to it gig, which does support auto cross? Put a switch between the interface and your device.
Your first step is to be able to get an IP from the dhcp you enabled.
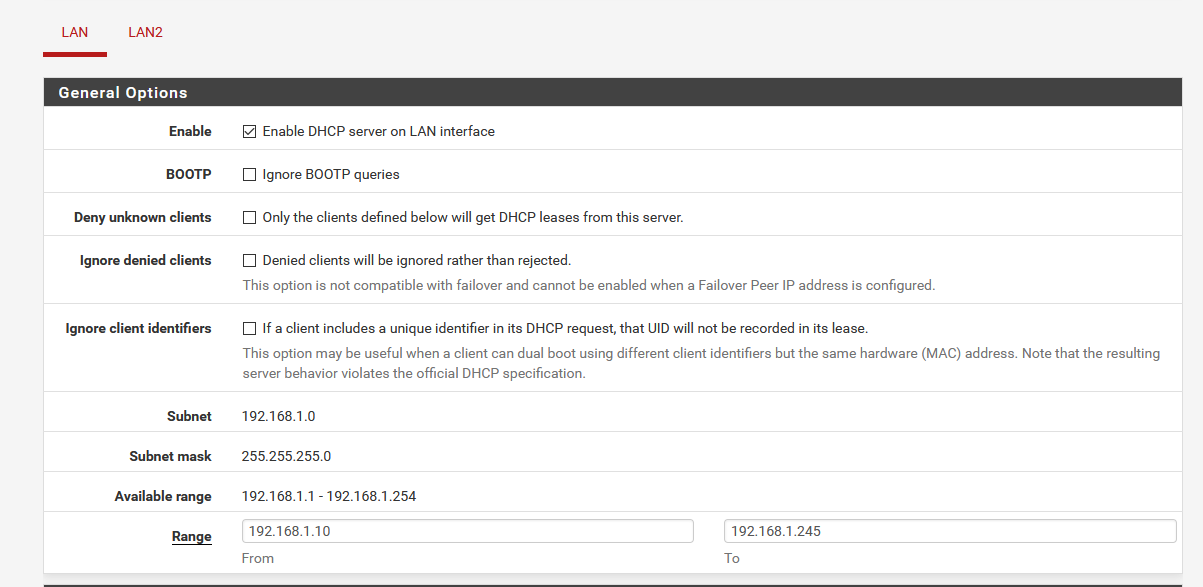
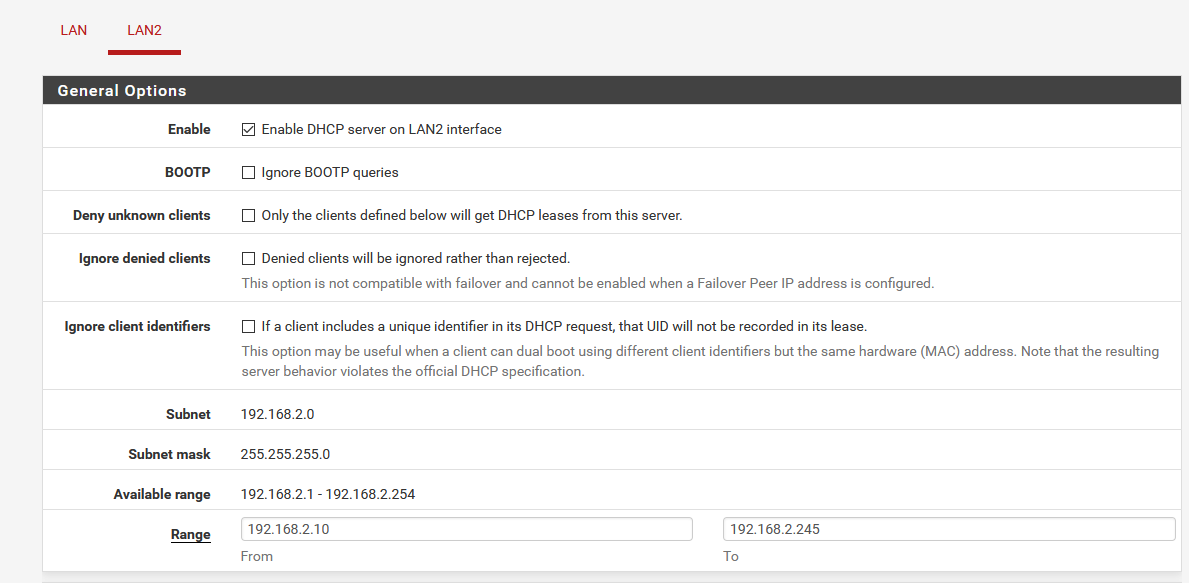
So pfsense IP on this interface is 192.168.2.1/24, great you sure - /32 is a common mistake. Is dhcpd running what range did you pick, etc.
Your never getting out a vpn until you get an IP, etc.
so you don't even want these devices traffic going over the same vpn?? They can be isolated and still use the same vpn connection.
-
@johnpoz
So your interface is only 10/100 - so those normally do not support autocross. So is what your connecting to it gig, which does support auto cross? Put a switch between the interface and your device.So I'm not sure if it supports autocross however there's only going to be one device per interface, on your reccomendation I've put a netgear GS105 between them (pfsense -> Switch -> Computer) and it has the same results
Your first step is to be able to get an IP from the dhcp you enabled.
As far as I know I've enabled the DHCP server on both interfaces and the interface options match./32 is a common mistake.
As far as I know I haven't chosen /32, both my lans operate on /24.Is dhcpd running what range did you pick, etc.
I've chosen 192.168.2.10 - 192.168.2.245 under the 192.168.2.0 subnet (pics attatched for both primary and secondary lan
-
Yeah that looks like dhcpd is enabled. If you had picked /32 you wouldn't of been able to enable dhcpd.
If your device can not get an IP, then its never getting to the internet.. Do you see dhcp requests from it in the dhcp log?
If not then no dhcpd would never hand give it an IP.
You sure your connected to the correct interface - and the cable and this device are good?