DNSSEC Lookaside Validation
-
With DLV (DNSSEC Lookaside Validation) having been decommissioned, though zones still exists that does not provide a fully signed path from root to zone, i.e. .com.au , co.za etc, how would an administrator enable / implement DNSSEC validation for these zones ?
-
"DLV" was a temporary solution, and shut down years ago since the real DNSSEC was adopted.
Enabling DNSEC for a domain is done by the registrars of your domain.
Most often, registrars have have some site that enables you to configure all kind of settings related to this domain name.
Name servers and/or even complete zone info is also handled with this interface.
Setting up DNNSEC implies you posting a DS DNS record which you have to generate first : the KSK key.
Locally, on your own master names server, you will be using ZSK keys.These keys, for security have to be rotated the intelligent way (do remove old keys before the new keys are synced among names servers).
This asks scripting .... if you liked the acme pfSense package, that consider this : handling DNSSEC is a whole new higher level.Be careful : setting up DNSSEC is not a click-and-go push-button functionality.
None of this can be done with pfSense.
pfSense uses a resolver (unbound) that is capable of 'checking' the DNSSEC info, and if the info is present, but wrong, the Resolver refuses to resolve ... ==> hard fail. But if DNSSEC info is present and ok, you will be sure that DNS info is correct.btw ;: one of my domains : http://dnsviz.net/d/test-domaine.fr/dnssec/
-
Thanks for replying @Gertjan.
I'm successfully using DNSSEC within pfsense's Unbound (resolver) aspect.
The issue is with the domains at the registrars. Though namecheap.com supports the import of the DS records for .com domains, they do not support it with .com.au domains. With the co.za. domains, the registrars simply state they do not support DNSSEC.
Is there thus another workaround ?
-
@Peek said in DNSSEC Lookaside Validation:
Is there thus another workaround ?
Move your domain to a different registrar..
Your problem is some tld do not support it, so no registrar can support it either.. So use a different tld for your domain if you want dnssec
http://stats.research.icann.org/dns/tld_report/
If the tld does not support it, you would have to complain to the owner of the tld.. But those are not actually tlds, those are subs off the tld.. You would have to get with the owners of those to get them to support dnssec, before you could ever get yourdomain.com.au or yourdomain.co.za
I just checked and both com.au and co.za are delegated with dnssec from their parents... So you should be able to find a registrar that supports it.
The easier option would be to just use different domain that is supported at the registrar you like ;)
edit: So I looked in to co.za a bit, and they for sure support dnssec.. If your looking for actual registar you can use that supports it for that domain you might want to contact
https://registry.net.za/contact.phpOk sure looks like they support it
https://vweb.co.za/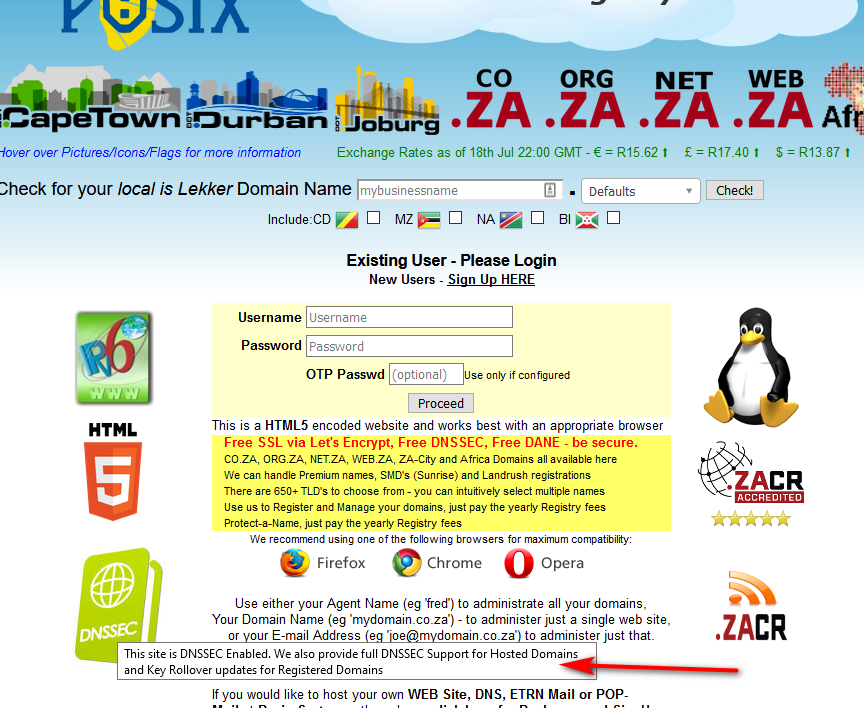
The site does look a bit lame ;) But pretty sure they support it, so you could contact them - and if they do.. You can just transfer your co.za domain to them as registrar.
That sad part in the whole thing - is pretty sure if the registrar is accredit pretty sure there is a rule that says they need to support dnssec for any domains they accept.
https://www.internetsociety.org/blog/2013/09/icanns-2013-raa-requires-domain-name-registrars-to-support-dnssec-ipv6/That went into effect back in 2014..
Here is the RAA
https://www.icann.org/resources/pages/approved-with-specs-2013-09-17-en
Here is direct link to the dnssec section
https://www.icann.org/resources/pages/approved-with-specs-2013-09-17-en#operationDNSSEC
Registrar must allow its customers to use DNSSEC upon request by relaying orders to add, remove or change public key material (e.g., DNSKEY or DS resource records) on behalf of customers to the Registries that support DNSSEC. Such requests shall be accepted and processed in a secure manner and according to industry best practices. Registrars shall accept any public key algorithm and digest type that is supported by the TLD of interest and appears in the registries posted at: http://www.iana.org/assignments/dns-sec-alg-numbers/dns-sec-alg-numbers.xml and http://www.iana.org/assignments/ds-rr-types/ds-rr-types.xml. All such requests shall be transmitted to registries using the EPP extensions specified in RFC 5910 or its successors.
And here is the list of accredited registrars - per that doc, they are really required to support dnssec..
https://www.icann.org/registrar-reports/accredited-list.htmlSince they all signed the RAA.
So guess you could BITCH to your current registrar, or complain to icann about them not actually supporting it.
If you ask me its the registrars that are holding it back from how it should be.. They don't make it simple enough to do, some do namecheap for the domains they do it for is easy, dynadot is pretty easy to use... I have domains with both that are dnssec enabled. I know for fact cloudflare supports it, but don't have any domains with them. Might move at some point?
But many don't have any interface for any of their domains they support.. Which per the RAA they signed puts them in violation.. And they could loose their accreditation.