NAT Before IPSEC Issue
-
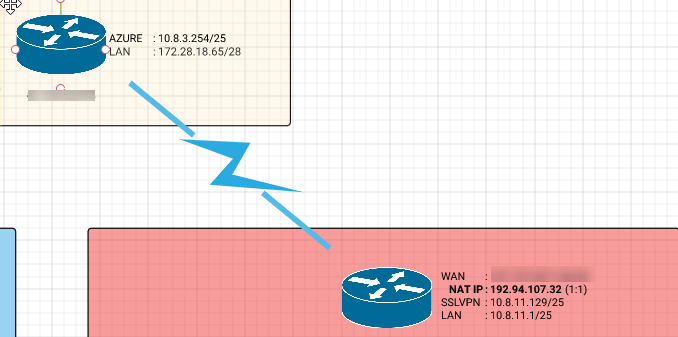
I have a pfsense box setup in azure that I use as an ipsec termination box. It has an active ipsec tunnel that, when on the pfsense cli, can reach all of the services on the other end of the tunnel. The problem lies with the inbound traffic from the "WAN" interface (labeled AZURE in the diagram). There is an outbound nat on the LAN so that any traffic destined for the tunnel network on the remote end, get's NATd's to the LANs interface IP. In the below screen cap of the states, you can see the external connection come in, get translated, traverse the tunnel, and get replies but the replies don't go back across the existing nat.
States during test:
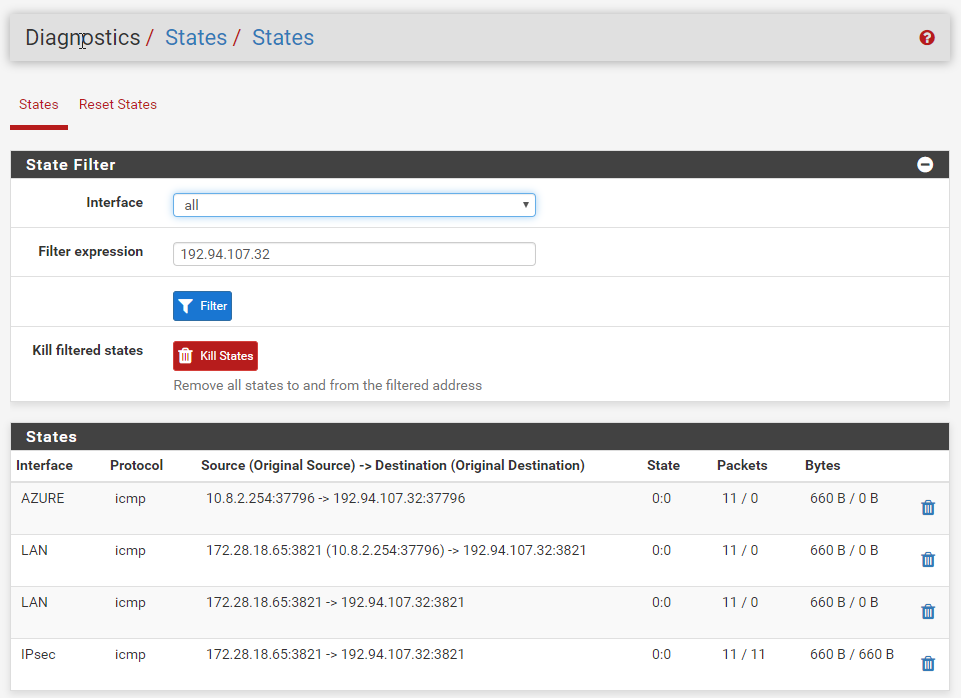
Source: 10.8.2.254
Destination: 192.94.107.32Network diag:
I have tried a packet capture on the 3 interfaces. I see the requests and replys on the ipsec interface as the state table indicates. I see the pings coming in on the AZURE interface and no replys but what is really peculiars is that with no filters, there are 0 packets on the LAN interface. There is nothing in the firewalls indicating and blocks and both ipsec and LAN interfaces have allow IPv4 any/any.
Something seems to be blocking the response from responding symmetrically on the already existing states once it leaves the ipsec interface. Any thoughts?