DNS Resolver and static DNS in DHCP reservation - problem
-
I am using pfSense's DNS resolver in order to take advantage of DNS over TLS for the upstream resolver I am using. All works great except for one device that I need to bypass these resolvers. I have tried setting up a static DHCP reservation and add the DNS servers to this reservation. No luck, the device still queries the gateway IP for DNS. Same when I add a FW rule specifically allowing DNS outbound for this device.
Is there another way to accomplish this or am I missing something?
Thanks!
-
This has zero to do with pfsense, unless you put in a redirect for dns as well?
If you hand your client some dns server, and it doesn't ask that.. My first thought would be the client didn't actually get the NS.. Just because you create a reservation, doesn't mean the client has updated their info yet..
Actually check on the client - does it show its using your reservation info, it lists the dns its suppose to use?
Many of the guides for using tls, also direct the user to put in a redirect for dns.. This could be your problem as well.
-
hmmm i do this for a few of my devices. and it works as it should
what does IP config /all show if its winders based?
-
No way to check on the device (Rachio sprinkler controller) but it is powercycled and reset. Gets the static DHCP I have setup for it and ignores the hard coded DNS servers in the reservation (which I can see by looking at the firewall logs - port 53 is going to the gateway, not the servers I have set).
-
-
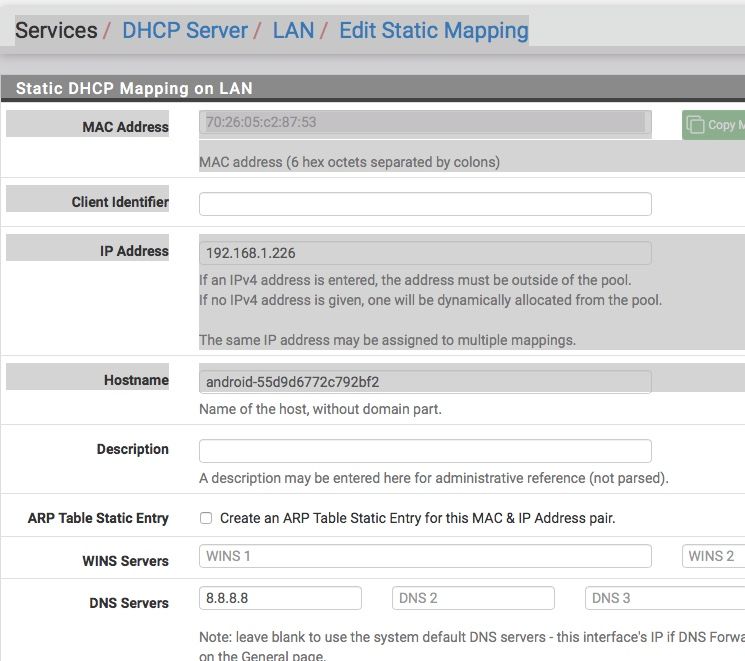
This is exactly what I have set. I suspect the problem is somehow tied up with the DNS resolver and the use of DNS over TLS. Is this somehow modifying the flow?
-
its the configuration if the resolver then. im guessing you don't have all checked? for outgoing ?
-
@bcruze I have WAN checked for outgoing
-
You do understand android devices are notorious for doing their own thing when it comes to dns right?
Heres the thing if you tell your reservation to send out dns 1.2.3.4, there is nothing saying the client HAS to use that.. But there is nothing you can do but hand it to the client.
Simple enough to sniff on the dhcp offer, is 8.8.8.8 listed. If your client not using that - that is on the client.
Your options would be to redirect that specific clients IP queries to where you want them to go via a port forward.
The issue has zero to do with the resolver, and zero to do with forwarding on that resolve to some dns using tls.
Validate by sniff your dhcp traffic that your actually offering the client what you want to offer it for dns.. If you are - then its on the client if uses it or not. Nothing pfsense can do about that other then a redirection of clients traffic... Part of the problem with dot and doh - is the iot device might start doing their dns via that - then what the F you going to do ;)
I hand out different name server other than pfsense interface on that network all the time.. To many devices - works as designed.. Give me a sec and will sniff some dhcp for you and show you how it works.
edit:
here... Here I handed client gets handed 192.168.3.10 as its NS
I then change it to hand out 8.8.8.8
did a ipconfig /renew on the client
You see it is now listing that as its only NS
And as you see from the capture the dns it sent it was 8.8.8.8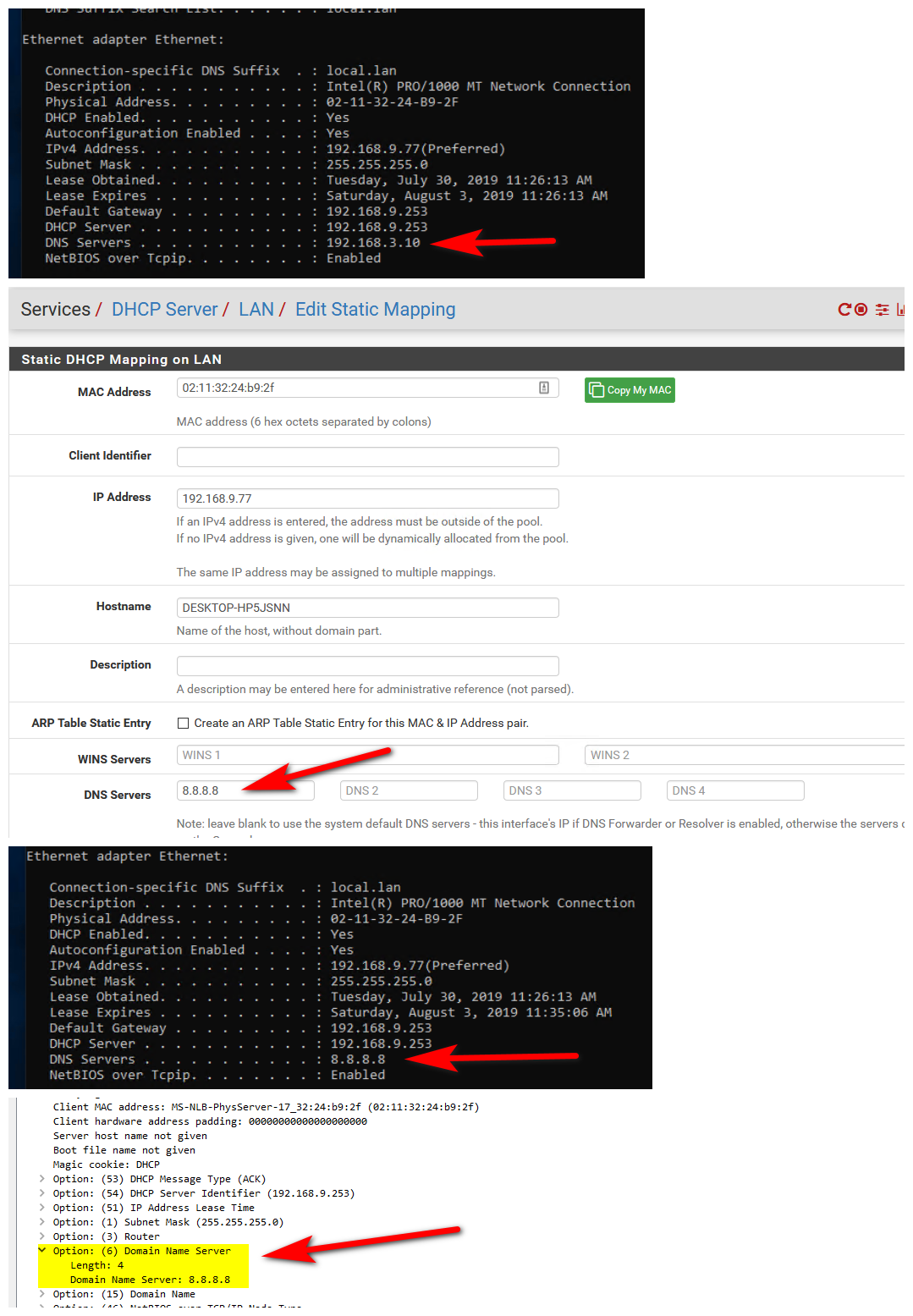
If you validate via sniff that pfsense is handing out the dns you want the client to use - and its not using it.. Then that is on the client, and the best you can hope to do is manually edit it on the client or redirect the traffic from that client from dns.. If its not hiding it in a doh or dot tunnel ;)