Pfsense being the gateway for another pfsense device
-
I have my main pfsense device connected to the internet through a pppoe connection to a BT openreach modem (WAN) which works fine. What I'm trying to do is have another pfsense device use the first pfsense as the WAN connection and create a seperate network from it.
Diagram as follows:
INTERNET(PPPOE) -> PFSENSE1 -> PFSENSE 1 NETWORK
-> PFSENSE2 -> PFSENSE2 NETWORKHow do I make this happen? so far neither the pfsense2 box or any client machines can connect to the internet.
-
Start with the basics. Can any pfsense2 clients ping 8.8.8.8? Can pfsense2 ping 8.8.8.8? That will tell us if its total connectivity or DNS only.
-
@KOM The device itself can't ping 8.8.8.8 from the box, so it's total connectivity
-
OK, what are the network details for both WANs and LANs?
-
Does the default route on PFSENSE2 to point to the PFSENSE1 LAN IP address ?
Also have you disabled Block private networks and loopback addresses on the WAN interface on PFSENSE2, assuming that the LAN interface on PFSENSE1 is using RFC1918 address space.
If you do a packet capture on the LAN interface on PFSENSE1 are ICMP pcakets hitting the interface ?
-
@NogBadTheBad @KOM Sorry for the late response, I needed to sleep. Revisiting it again. I've set the WAN ip on pfsense 2 to the DHCP from pfsense 1's LAN. This has resulted in me being able to access the pfsense 2 device from the pfsense 2's client which is good, so here's where I'm at now.
- Pfsense 2 can ping a remote host (8.8.8.8)
- Pfsense 2's client can access both pfsense 1 & 2
- Pfsense 2's client can't access the internet
I want pfsense 2's client to not be able to access the main subnet (192.168.1.0/24, only its own subnet 192.168.2.0/24) and for it to be able to access the internet. I've disabled the blocking of private networks on the WAN of pfsense 2. Open to suggestions, thanks.
-
Add a firewall rule on the LAN interface that rejects access to destination network. Below I'm rejecting access from LAN to the 1.2.3.0 network.
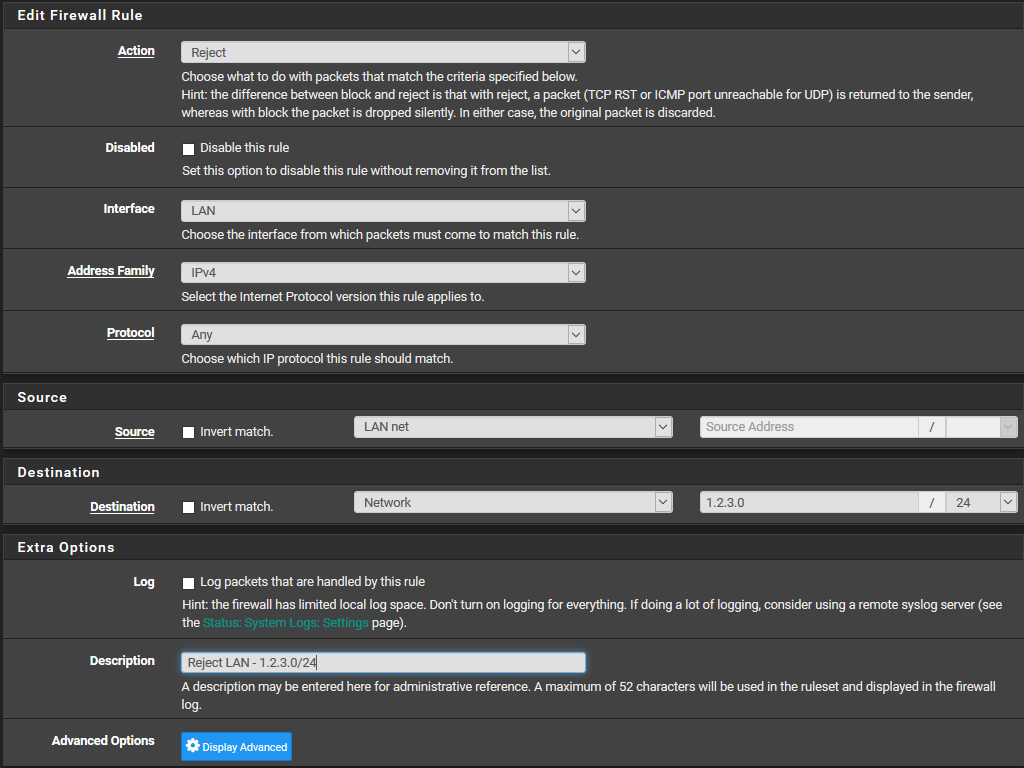
-
@KOM ~~The DNS of the pfsense's clients on the second device aren't working however the device itself is. Any ideas?
Also that rule isn't working but I'll need to configure them as I want the second pfsense device to have an openvpn connection and kill switch but that's probably another thread unless you can help with that.~~
The DNS was wrong on the client machine, sorry for wasting your time. The rule still isn't working though.
-
What are those clients using for DNS? Assuming they're Windows clients, what does
ipconfig /allreport for DNS server? Out of the box, pfSense enables the DNS Resolver (unbound) which queries the roots and doesn't need an upstream DNS. DNS should just work if your clients are using pfSense LAN for DNS. If the clients are static IP, make sure they're using the correct DNS. If DHCP, check what's being served to them for DNS.As for your others issues, get one thing working at a time and then make a new post for that specific problem.
-
@KOM The internet is working in all its glory, back to the segregation rules.Pfsense main's client can't access the pfsense secondary device however the second pfsense's clients can access the main pfsense. is there any way I could deny that? I followed the rule above. screenshot:
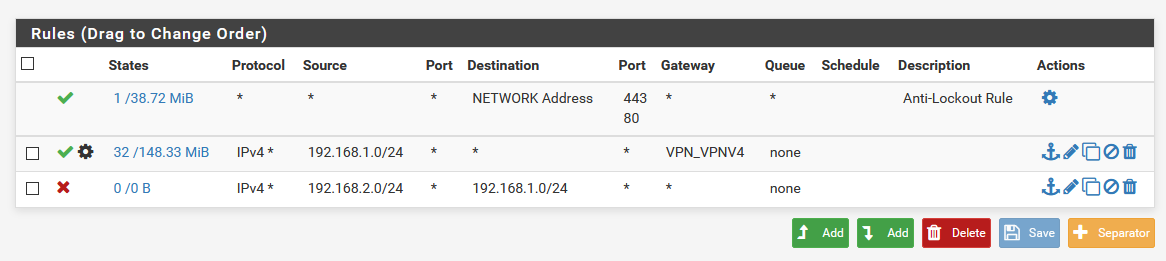
(LAN of the main Pfsense device)
-
Move your block rule above your VPN rule, and then go to Diagnostics - States - Reset States and reset them. Existing states aren't affected by a rule change.
Actually hold on. Why do you have two different networks showing in your rule list? The Source for these rules should always be the network of the interface it's connected to.
-
@KOM I've reset the table, here's the rules now:
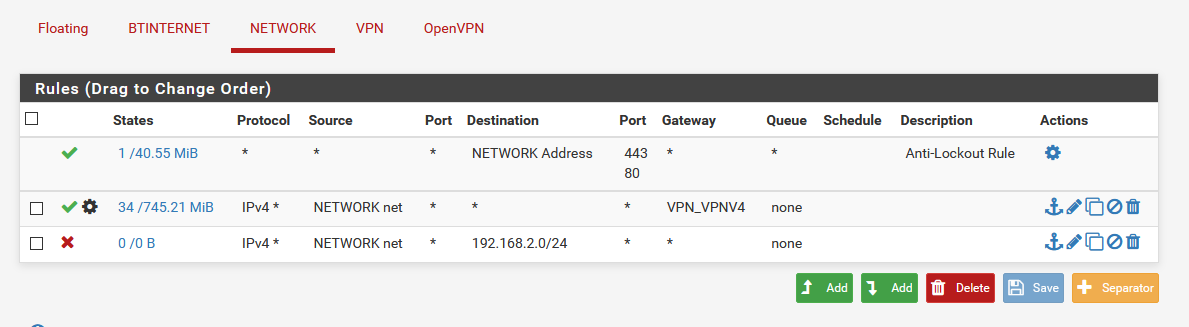
-
Rules are evaluated top-down, first match wins, so rule order is important. You almost always want to put block rules above allow rules.
-
@KOM I can still ping it from the client, does it have anything to do with the fact that it has to connect to the main pfsense device as a WAN that means I can't block it? or am I still missing something?
-
Did you reset your states like I told you to?
-
@KOM Yeah, I did.
-
If you are trying to prevent users of pfsense2 LAN from accessing pfsense1 LAN/pfsense2 WAN, you need to put the rules on pfsense2's LAN tab, not pfsense1.
This would be less confusing if I had a clue about your network configuration details for WAN and LAN on pfsense1 and 2. I did ask for them earlier but you didn't reply.
-
So you have this
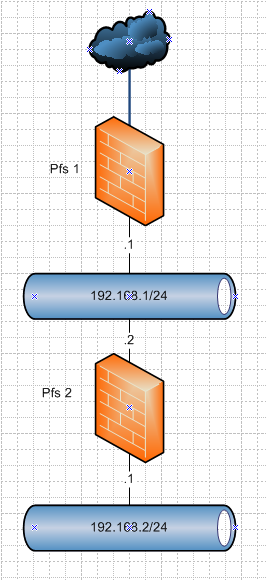
Not sure which network you have were exactly..
But if you don't want 192.168.2/24 (bottom network) from talking to 192.168.1 you would block it on the lan interface of pfs2
You would have allow rule to talk to pfs2 lan addres for dns, ping for example on the pfs2 lan rules
Then you would have a block rule to 192.168.1/24
Then you would have a any rule to allow clients to talk to the internet.. Blocking 192.168.2 on pfs1 lan would be completely pointless and never happen, since pfs2 is directly connected to it.edit: Ah @KOM beat me too it, but he didn't draw a pretty picture like I did ;) heheheh
-
This post is deleted!