Website won't load: operation timed out
-
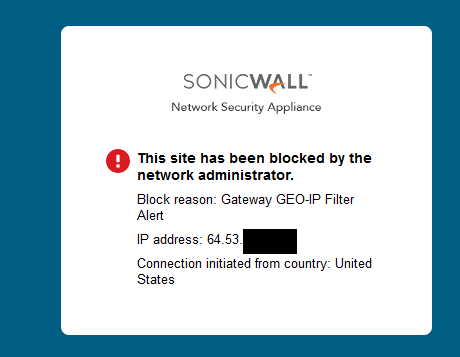
there is a sonicwall there with Gateway GEO-IP Filter enabled.
are you sure is not the sonicwall that have a ban on you? -
@Finduilas said in Website won't load: operation timed out:
5:51:27.777709 IP my.ip.. > 91.183.206.235.80: tcp 0
15:51:28.025853 IP my.ip.. > 91.183.206.235.80: tcp 0Well you sending.. but getting nothing back.. So its not pfsense blocking you.
Yup I get this
-
I am able to connect to it from the UK. It then invites me to login over http. If I try to use https I get a bad cert.
Those things tell me whoever is managing that site isn't paying much attention so you could well have been blocked by some automated system nobody ever checks.
Steve
-
@stephenw10 said in Website won't load: operation timed out:
It then invites me to login over http
Wow - that is a major vendor of yours? I would find a different vendor ;)
-
Yeah it's bad in numerous ways!
-
Sure hope maybe they do bathroom supplies or something and nothing to do with IT ;) Whatever they do, guess they don't want to do business with the US ;)
-
.. or italy, they do catering services anyway, i doubt they want to send food and staff to usa anyway :)
that subdomain is probably for sales representatives only -
But maybe a secretary in the US wants to have an event their company is throwing in Belgium catered ;) Blocking IPs from other countries prob not the best way to grow the business ;)
-
indeed ..
i can see that web page using a proxy
https://nl.hideproxy.me
from a security point of view it is useless -
Ok, I'm glad we found the problem.. I didn't got the Sonicwall message, and because the router is pretty new, I thought it was my own fault..
The vendor is now aware of the problem. They will fix it. Thanks for the help, sorry it wasn't really a pfsense issue.