IPsec Stop working after few commands
-
2 site with static ip, ipsec from pfsense to pfsense
i configured ipsec with default option, i have only set remote gateway and pre-shared key
for phase2
on site A i have 192.168.3.0/24
on site B i have 172.16.0.0/24the tunnel is established, the phase2 say it's created,
i can ping from side A to side B,
i can ping from side B to side A
if i ssh from side A to side B, i can login, i can do some ls but if i do for example a dmesg i receve the first 10/15 lines then the connection drop, the same if i try to access samba, and i can't reconnect, ping stop working from both side. i need to restart ipsec or wait some times to make it respond to ping again
ipsec start to log thisAug 24 08:53:41 charon 38977 06[KNL] <con1000|8> querying SAD entry with SPI cc2d60b7 Aug 24 08:53:41 charon 38977 06[KNL] querying SAD entry with SPI cc2d60b7 Aug 24 08:53:41 charon 38977 06[KNL] <con1000|8> querying SAD entry with SPI c04d279c Aug 24 08:53:41 charon 38977 06[KNL] querying SAD entry with SPI c04d279c Aug 24 08:53:36 charon 38977 06[KNL] <con1000|8> querying SAD entry with SPI cc2d60b7 Aug 24 08:53:36 charon 38977 06[KNL] querying SAD entry with SPI cc2d60b7 Aug 24 08:53:36 charon 38977 06[KNL] <con1000|8> querying SAD entry with SPI c04d279c Aug 24 08:53:36 charon 38977 06[KNL] querying SAD entry with SPI c04d279c Aug 24 08:53:33 charon 38977 06[KNL] <con1000|8> querying policy 172.16.0.0/24|/0 === 192.168.3.0/24|/0 in Aug 24 08:53:33 charon 38977 06[KNL] querying policy 172.16.0.0/24|/0 === 192.168.3.0/24|/0 in Aug 24 08:53:33 charon 38977 04[NET] sending packet: from 217.xxx.xx.167[500] to 151.xxx.xxx.210[500] Aug 24 08:53:33 charon 38977 04[NET] sending packet: from 217.xxx.xx.167[500] to 151.xxx.xxx.210[500] Aug 24 08:53:33 charon 38977 06[NET] <con1000|8> sending packet: from 217.xxx.xxx.167[500] to 151.xxx.xxx.210[500] (80 bytes) Aug 24 08:53:33 charon 38977 06[NET] sending packet: from 217.xxx.xxx.167[500] to 151.xxx.xxx.210[500] (80 bytes) Aug 24 08:53:33 charon 38977 06[ENC] <con1000|8> generating INFORMATIONAL response 831 [ ] Aug 24 08:53:33 charon 38977 06[ENC] generating INFORMATIONAL response 831 [ ] Aug 24 08:53:33 charon 38977 06[ENC] <con1000|8> parsed INFORMATIONAL request 831 [ ] Aug 24 08:53:33 charon 38977 06[ENC] parsed INFORMATIONAL request 831 [ ] Aug 24 08:53:33 charon 38977 06[NET] <con1000|8> received packet: from 151.xxx.xxx.210[500] to 217.1xxx.xxx.167[500] (80 bytes) Aug 24 08:53:33 charon 38977 06[NET] received packet: from 151.xxx.xxx.210[500] to 217.xxx.xxx.167[500] (80 bytes) Aug 24 08:53:33 charon 38977 03[NET] waiting for data on sockets Aug 24 08:53:33 charon 38977 03[NET] waiting for data on socketsi also tried with openvpn, same problem, the only difference is that with openvpn on ssh i receve the error "broken pipe" instead of "network error"
site A is pppoe with static address assigned
site B is a /29 where one address is assigned to pfsense others ip are aliaslog of ipsec at connection
Aug 24 09:14:28 charon 38977 11[IKE] <con1000|9> received AUTH_LIFETIME of 27914s, scheduling reauthentication in 27374s Aug 24 09:14:28 charon 38977 11[IKE] received AUTH_LIFETIME of 27914s, scheduling reauthentication in 27374s Aug 24 09:14:28 charon 38977 11[IKE] <con1000|9> CHILD_SA con1000{41} established with SPIs cae1ccd1_i c05282cd_o and TS 192.168.3.0/24|/0 === 172.16.0.0/24|/0 Aug 24 09:14:28 charon 38977 11[IKE] CHILD_SA con1000{41} established with SPIs cae1ccd1_i c05282cd_o and TS 192.168.3.0/24|/0 === 172.16.0.0/24|/0 Aug 24 09:14:28 charon 38977 11[KNL] <con1000|9> updating policy 192.168.3.0/24|/0 === 172.16.0.0/24|/0 out Aug 24 09:14:28 charon 38977 11[KNL] updating policy 192.168.3.0/24|/0 === 172.16.0.0/24|/0 out Aug 24 09:14:28 charon 38977 11[KNL] <con1000|9> policy 192.168.3.0/24|/0 === 172.16.0.0/24|/0 out already exists, increasing refcount Aug 24 09:14:28 charon 38977 11[KNL] policy 192.168.3.0/24|/0 === 172.16.0.0/24|/0 out already exists, increasing refcount Aug 24 09:14:28 charon 38977 11[KNL] <con1000|9> updating policy 172.16.0.0/24|/0 === 192.168.3.0/24|/0 in Aug 24 09:14:28 charon 38977 11[KNL] updating policy 172.16.0.0/24|/0 === 192.168.3.0/24|/0 in Aug 24 09:14:28 charon 38977 11[KNL] <con1000|9> policy 172.16.0.0/24|/0 === 192.168.3.0/24|/0 in already exists, increasing refcount Aug 24 09:14:28 charon 38977 11[KNL] policy 172.16.0.0/24|/0 === 192.168.3.0/24|/0 in already exists, increasing refcount Aug 24 09:14:28 charon 38977 11[KNL] <con1000|9> using integrity algorithm HMAC_SHA2_256_128 with key size 256 Aug 24 09:14:28 charon 38977 11[KNL] using integrity algorithm HMAC_SHA2_256_128 with key size 256 Aug 24 09:14:28 charon 38977 11[KNL] <con1000|9> using encryption algorithm AES_CBC with key size 128 Aug 24 09:14:28 charon 38977 11[KNL] using encryption algorithm AES_CBC with key size 128 Aug 24 09:14:28 charon 38977 11[KNL] <con1000|9> adding SAD entry with SPI c05282cd and reqid {3} Aug 24 09:14:28 charon 38977 11[KNL] adding SAD entry with SPI c05282cd and reqid {3} Aug 24 09:14:28 charon 38977 11[KNL] <con1000|9> using integrity algorithm HMAC_SHA2_256_128 with key size 256 Aug 24 09:14:28 charon 38977 11[KNL] using integrity algorithm HMAC_SHA2_256_128 with key size 256 Aug 24 09:14:28 charon 38977 11[KNL] <con1000|9> using encryption algorithm AES_CBC with key size 128 Aug 24 09:14:28 charon 38977 11[KNL] using encryption algorithm AES_CBC with key size 128 Aug 24 09:14:28 charon 38977 11[KNL] <con1000|9> adding SAD entry with SPI cae1ccd1 and reqid {3} Aug 24 09:14:28 charon 38977 11[KNL] adding SAD entry with SPI cae1ccd1 and reqid {3} Aug 24 09:14:28 charon 38977 11[KNL] <con1000|9> deleted SAD entry with SPI cae1ccd1 Aug 24 09:14:28 charon 38977 11[KNL] deleted SAD entry with SPI cae1ccd1 Aug 24 09:14:28 charon 38977 11[KNL] <con1000|9> deleting SAD entry with SPI cae1ccd1 Aug 24 09:14:28 charon 38977 11[KNL] deleting SAD entry with SPI cae1ccd1 Aug 24 09:14:28 charon 38977 11[CFG] <con1000|9> selected proposal: ESP:AES_CBC_128/HMAC_SHA2_256_128/NO_EXT_SEQ Aug 24 09:14:28 charon 38977 11[CFG] selected proposal: ESP:AES_CBC_128/HMAC_SHA2_256_128/NO_EXT_SEQ Aug 24 09:14:28 charon 38977 11[IKE] <con1000|9> received ESP_TFC_PADDING_NOT_SUPPORTED, not using ESPv3 TFC padding Aug 24 09:14:28 charon 38977 11[IKE] received ESP_TFC_PADDING_NOT_SUPPORTED, not using ESPv3 TFC padding Aug 24 09:14:28 charon 38977 11[IKE] <con1000|9> maximum IKE_SA lifetime 28428s Aug 24 09:14:28 charon 38977 11[IKE] maximum IKE_SA lifetime 28428s Aug 24 09:14:28 charon 38977 11[IKE] <con1000|9> scheduling reauthentication in 27888s Aug 24 09:14:28 charon 38977 11[IKE] scheduling reauthentication in 27888s Aug 24 09:14:28 charon 38977 11[IKE] <con1000|9> IKE_SA con1000[9] established between 217.xxx.xxx.167[217.xxx.xxx.167]...151.xxx.xxx.210[151.xxx.xxx.210] Aug 24 09:14:28 charon 38977 11[IKE] IKE_SA con1000[9] established between 217.xxx.xxx.167[217.xxx.xxx.167]...151.xxx.xxx.210[151.xxx.xxx.210]i tried to set MSS clamping to 1300 as suggested from https://docs.netgate.com/pfsense/en/latest/vpn/ipsec/ipsec-troubleshooting.html
nothing changed
all interfaces have different subnets Site A != Site B
site A is 2.5.0
site B is a vm with 2.4.4-p3what can i try?
-
Sounds like something is killing your states. Either the states for the VPN connection or the states for the connections across the tunnel.
-
i'm still testing if now it's all good before i can say that it's resolved
after what you told me I realized that sometimes I have to reload the web pages and that the forum itself sometimes tells me that I lose the connectionthe first thing that came to mind that could kill the states without any apparent reason was this setting...
Disable Gateway Monitoring Action
for the moment the problem is not present. let's see if it continues
-
Probably not. It's usually this one:
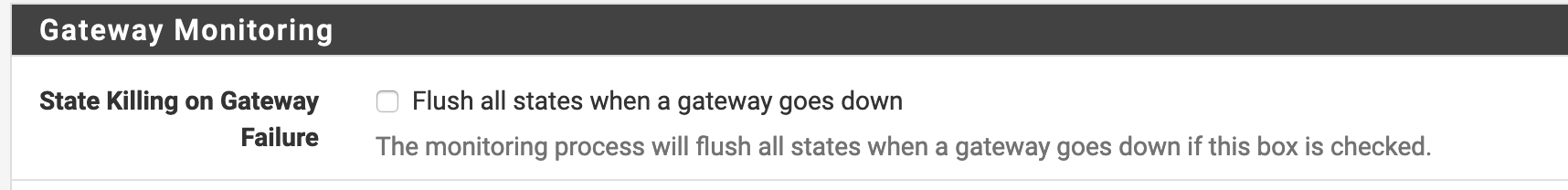
-
nope i don't have that checked, plus i never saw my gateway down

-
Either the states are being removed or you have some asymmetric routing happening that is cutting off the connection after the half-open state times out.