Intermittent connection issue
-
@kevindd992002 said in Non-forwarding Resolver intermittent operation:
Here's a traceroute that I sent them a few months ago: https://pastebin.com/JqPx326v
That looks like the RTO starts from the hop that's within the ISP network. Is that enough evidence for them to conclude that the problem is in their network?
And then 3 minutes after the issue, it got resolved and the traceroute results became like this: https://pastebin.com/XYbNMiWy
@kevindd992002 That's not really proof of an issue on their network. Not all hops along the route will always respond. It's common to have hops that don't respond along the route. As long as at the end you get to the server, that's what matters. Also, the hops are not taking very long so that also looks OK.
-
@Raffi_ said in Non-forwarding Resolver intermittent operation:
@kevindd992002 said in Non-forwarding Resolver intermittent operation:
Here's a traceroute that I sent them a few months ago: https://pastebin.com/JqPx326v
That looks like the RTO starts from the hop that's within the ISP network. Is that enough evidence for them to conclude that the problem is in their network?
And then 3 minutes after the issue, it got resolved and the traceroute results became like this: https://pastebin.com/XYbNMiWy
@kevindd992002 That's not really proof of an issue on their network. Not all hops along the route will always respond. It's common to have hops that don't respond along the route. As long as at the end you get to the server, that's what matters. Also, the hops are not taking very long so that also looks OK.
Right, that's what I thought. I just posted the screenshots here in case you guys see something out of the ordinary.
-
@kevindd992002 said in Non-forwarding Resolver intermittent operation:
Yeah, I know how ISP's react when you say that. They panic and makes things solved faster. There are competitors, for sure, but in my condo there's only one offering FTTH connections, the one that I'm using now. The others are using crappy phone copper cables which are very substandard. And I just switched from that copper ISP to this fiber ISP since January 2019 so not long ago.
Off topic, but we're actually in the copper test industry. Believe it or not, they have technology now that is able to get close to Gigabit speeds on those old copper lines if the ISP is willing to invest in it. I'm curious are you in Australia? Here in the US, the old phone lines have been mostly abandoned in terms of further investment.
-
@Raffi_ said in Non-forwarding Resolver intermittent operation:
@kevindd992002 said in Non-forwarding Resolver intermittent operation:
Yeah, I know how ISP's react when you say that. They panic and makes things solved faster. There are competitors, for sure, but in my condo there's only one offering FTTH connections, the one that I'm using now. The others are using crappy phone copper cables which are very substandard. And I just switched from that copper ISP to this fiber ISP since January 2019 so not long ago.
Off topic, but we're actually in the copper test industry. Believe it or not, they have technology now that is able to get close to Gigabit speeds on those old copper lines if the ISP is willing to invest in it. I'm curious are you in Australia? Here in the US, the old phone lines have been mostly abandoned in terms of further investment.
I can imagine. I was mostly talking about how sub-standard the copper wires are here in our condo. Even the copper ISP's themselves tell me that the copper wires that the contractors used in this condo are crap. The copper wires in the building's cabinet are worse than how spaghetti looks like. And no one wants to invest to replace those. I'm in the Philippines, so a third-world country, but Internet service here came a long way already. My two service plans are 35 down/35 up (around $31) and 300 down/300 up (around $87).
-
The Asus router as the main router and without pfsense has been issue-free for the last two days. It's still too early to tell but I'll continue monitoring during the weekend (the time when the issue usually occurs most) before I come to a conclusion. If it does run flawless until Monday though, I'm not sure how to continue troubleshooting pfsense except to uninstall and reinstall it from scratch. I mean that's an easy task when I just need to reload the config but if I am to go that route I would want to not carry over any settings from the config (which might be corrupted or something, for all we know).
-
@kevindd992002 Interesting. Ok, that sounds like a good plan. Yea give it a little while to see how it goes. We'll see what the next step is from there. Have a good weekend.
Raffi -
After 5 days of continuously using the ASUS router, I've never had any single occurrence of the issue! That isolates the ASUS router, cables, and ISP modem from being the root cause of the issue.
I've decided, just now, to switch to pfsense and as soon as I've plugged it in and waited for everything to go green in the Dashboard, I experienced the issue. It's got to be either the pfsense software itself or the physical hardware that hosts pfsense (although I doubt this). What can you recommend as a next step here?
-
And your asus router was actual resolving for dns?
You title says non forwarding problems.. I find it unlikely that your asus router was resolving for dns vs forwarding..
Do you understand what the difference is?
-
@johnpoz said in Non-forwarding Resolver intermittent operation:
And your asus router was actual resolving for dns?
You title says non forwarding problems.. I find it unlikely that your asus router was resolving for dns vs forwarding..
Do you understand what the difference is?
Yes, I understand the difference between DNS resolver and DNS forwarder. I've already established this a few posts above. How can I rename the title for this whole thread and move it to the correct section? So that we can all be over the technicalities. Are my test results still not convincing for you that pfsense is causing my issue? What can I do to convince you?
The ASUS router is NOT a DNS resolver. It is a DNS forwarder and I was forwarding to the OpenDNS servers. That's the only main difference I see: pfsense was set as a DNS resolver (using root hints and not forwarding) while the ASUS router does not have this feature and is simply doing DNS forwarding.
-
So then - troubleshoot your dns problem when your "resolving" Or set pfsense to forward to opendns like your asus was doing.
-
@kevindd992002 said in Non-forwarding Resolver intermittent operation:
How can I rename the title for this whole thread and move it to the correct section?
FYI, you can change the title of this topic by going up to your very first post, then click on the 3 dots and go to edit. Then above the text box where it shows the title, you can go in and edit it to help avoid any confusion. Maybe something more generic like intermittent connection issue or whatever you like. As for moving it to the correct section, that would have to be done by someone else. You can start a new topic in the correct section if you'd like, but I think we already made some progress here.
After 5 days of continuously using the ASUS router, I've never had any single occurrence of the issue! That isolates the ASUS router, cables, and ISP modem from being the root cause of the issue.
I've decided, just now, to switch to pfsense and as soon as I've plugged it in and waited for everything to go green in the Dashboard, I experienced the issue. It's got to be either the pfsense software itself or the physical hardware that hosts pfsense (although I doubt this). What can you recommend as a next step here?
Here is what I would suggest doing if you haven't already.
- Make a backup of your current pfSense config.
- Do a fresh install of the latest pfSense (2.4.4-RELEASE-p3).
- Configure your interfaces as needed.
- Do not install any additional packages.
- Leave all the default settings. pfSense is pretty darn secure out of the box, certainly more secure then the Asus anyway.
Then let's see where that gets you.
Raffi
-
@johnpoz said in Non-forwarding Resolver intermittent operation:
So then - troubleshoot your dns problem when your "resolving" Or set pfsense to forward to opendns like your asus was doing.
I thought even you agreed that this is not a DNS problem? So why would I concentrate on troubleshooting DNS? I'm pinging an IP address when the issue happens so that in itself tells everyone already that it isn't a DNS issue.
@Raffi_ said in Non-forwarding Resolver intermittent operation:
@kevindd992002 said in Non-forwarding Resolver intermittent operation:
How can I rename the title for this whole thread and move it to the correct section?
FYI, you can change the title of this topic by going up to your very first post, then click on the 3 dots and go to edit. Then above the text box where it shows the title, you can go in and edit it to help avoid any confusion. Maybe something more generic like intermittent connection issue or whatever you like. As for moving it to the correct section, that would have to be done by someone else. You can start a new topic in the correct section if you'd like, but I think we already made some progress here.
After 5 days of continuously using the ASUS router, I've never had any single occurrence of the issue! That isolates the ASUS router, cables, and ISP modem from being the root cause of the issue.
I've decided, just now, to switch to pfsense and as soon as I've plugged it in and waited for everything to go green in the Dashboard, I experienced the issue. It's got to be either the pfsense software itself or the physical hardware that hosts pfsense (although I doubt this). What can you recommend as a next step here?
Here is what I would suggest doing if you haven't already.
- Make a backup of your current pfSense config.
- Do a fresh install of the latest pfSense (2.4.4-RELEASE-p3).
- Configure your interfaces as needed.
- Do not install any additional packages.
- Leave all the default settings. pfSense is pretty darn secure out of the box, certainly more secure then the Asus anyway.
Then let's see where that gets you.
Raffi
Changed the title already, thanks.
I was afraid that the only step I'm left with is to reinstall. But yeah, I can do that, but I'll probably not be able to until next week because I don't have a serial-to-USB adapter with me right now. I'll report back when I'm done with this but I'll continue monitoring while using the current pfsense installation.
-
@Raffi_ , since I didn't have time to start pfsense from scratch yet, I decided to just reset to factory defaults and restore the config. Same thing still happens.
One semi-consistent thing that I observed though is that the issue happens when I turn on my desktop computer from a state where it is turned off for a couple of hours. I say "semi-consistent" because when I restart or shut it down now and turn it back on immediately, the issue cannot be recreated. I've been observing this for a couple of days and it's as if that it is the one bogging down the whole network. Then I wait for 5 to 10 minutes and things come back to normal.
There's no special network configuration with my desktop computer aside from these things:
- Uses NUT (Network UPS Tools) to connect to the UPS master connected to pfsense.
- Wireshark/NPCap is installed but not running (the Npcap Loopback Adapter is installed)
- Hyper-V Manager is installed and the default virtual switch (has its own internal subnet) is configured.
- A mapped drive connecting to the Synology NAS on the other end of the OpenVPN tunnel is configured.
Can you think of anything out of those that could cause this?
Could it perhaps be a broadcast storm caused by the desktop PC? If so, how can I confirm this?
-
@kevindd992002 said in Intermittent connection issue:
how can I confirm this?
Sniff and see - be it on any device on that same L2 or pfsense... If you want to know what is going on - just look.
-
I agree with what John said. If you suspect something like the desktop traffic being an issue, run a packet capture on pfsense using the LAN interface.
I would suggest starting a packet capture on pfsense LAN before you turn on that PC which is causing the issues. Then while the capture is running, turn on the PC (after it's been off long enough to cause trouble) and see what's happening. Take note of the time when you first connect the PC so you can figure out at what point in the capture the PC was connected. I think it's a little coincidental that the default DHCP lease time in pfsense is 2 hours and the time it takes for your PC to stay disconnected before it starts causing trouble matches up with that.
Have you tried manually configuring a fixed IP on that PC instead of requesting a DHCP lease?
Raffi
-
@Raffi_ said in Intermittent connection issue:
I agree with what John said. If you suspect something like the desktop traffic being an issue, run a packet capture on pfsense using the LAN interface.
I would suggest starting a packet capture on pfsense LAN before you turn on that PC which is causing the issues. Then while the capture is running, turn on the PC (after it's been off long enough to cause trouble) and see what's happening. Take note of the time when you first connect the PC so you can figure out at what point in the capture the PC was connected. I think it's a little coincidental that the default DHCP lease time in pfsense is 2 hours and the time it takes for your PC to stay disconnected before it starts causing trouble matches up with that.
Have you tried manually configuring a fixed IP on that PC instead of requesting a DHCP lease?
Raffi
Ok, I'll try that and report back.
No, I have not tried a static IP on the PC but it has an IP reservation from the DHCP server, like all my other servers/PC's that I need to RDP from outside do. But yeah, I'll see if a static IP makes a difference to rule out DHCP.
-
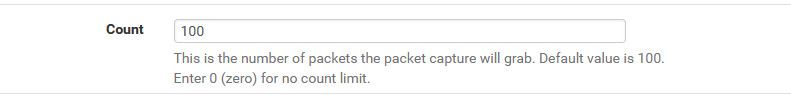
Keep in mind that default packet capture on pfsense is set to 100, so you will most likely want to adjust that.. 0 would be a good setting.. Just don't forget its running ;)
-
Alright, so after some more testing I can say it's not the desktop causing the issue as it was more like a coincidence that happened. I've did more steps regarding DNS and the results were reproducible this time:
- Changed from regular DNS Resolver to DNS Resolver with forwarding (set to forward to 192.168.100.1 which is the modem's IP/gateway). Ping'ed 208.78.70.23 (one IP I saw in Status -> DNS Resolver) from pfsense's ping utility and there were no issues. Internet is back up and running.
- Changed back to regular DNS Resolver. Ping'ed the same IP from pfsense's ping utility and no response from 192.168.100.1.
So it looks like the problem is DNS but not the resolution part of DNS per se. For some reason, when DNS Resolver without forwarding is set the WAN gateway doesn't respond properly (or responds intermittently) as well, at least that's what's happening during my testing. So if you try to resolve with DNS Resolver, it's "as if" it is not resolving properly because of course it doesn't get any responses from the root hints servers consistently.
I know, the issue doesn't make sense but will getting a WAN packet capture while recreating the issue help in this situation? Or both WAN and LAN?
EDIT:
Also, I get a ton of Timeout A's under Status -> DNS Resolver when forwarding is NOT set. When forwarding, I get 0.
-
@kevindd992002 said in Intermittent connection issue:
Alright, so after some more testing I can say it's not the desktop causing the issue as it was more like a coincidence that happened. I've did more steps regarding DNS and the results were reproducible this time:
- Changed from regular DNS Resolver to DNS Resolver with forwarding (set to forward to 192.168.100.1 which is the modem's IP/gateway). Ping'ed 208.78.70.23 (one IP I saw in Status -> DNS Resolver) from pfsense's ping utility and there were no issues. Internet is back up and running.
- Changed back to regular DNS Resolver. Ping'ed the same IP from pfsense's ping utility and no response from 192.168.100.1.
So it looks like the problem is DNS but not the resolution part of DNS per se. For some reason, when DNS Resolver without forwarding is set the WAN gateway doesn't respond properly (or responds intermittently) as well, at least that's what's happening during my testing. So if you try to resolve with DNS Resolver, it's "as if" it is not resolving properly because of course it doesn't get any responses from the root hints servers consistently.
I know, the issue doesn't make sense but will getting a WAN packet capture while recreating the issue help in this situation? Or both WAN and LAN?
EDIT:
Also, I get a ton of Timeout A's under Status -> DNS Resolver when forwarding is NOT set. When forwarding, I get 0.
Ooooohhh I can't believe it didn't hit me sooner. This is a pretty well known issue with the DNS resolver (unbound) in pfSense. Here is one thread on it that I ran into when I had similar issues. https://forum.netgate.com/topic/120838/unbound-appears-to-restart-frequently-and-fails-to-resolve-domains-sometimes.
There are a number of solutions to this. As you found, use DNS forwarding. I would suggest forwarding to servers like Cloudflare (1.1.1.1 and 1.0.0.1) or Google (8.8.8.8 and 8.8.4.4). If you are going to use pfSense for resolving, go into the DNS resolver settings and uncheck the DHCP Registration option. That would explain exactly the issue you were seeing. When a PC is connected after 2 hours, it would request a new DHCP lease. When that lease is handed out, it also causes Unbound to restart because Unbound has to update its info since DHCP leases are being registered. This was a major pain for me. If you also have things that slow down the unbound startup process like lots of pfblocker IP lists, that will make matters worse.My current setup has DHCP registration disabled in the DNS Resolver options. I also have forwarding enabled to 1.1.1.1 and 1.0.0.1. Ideally, I wanted to have DNS resolution done by pfSense without having to forward, but it was not always reliable. I think the better solution would be to have a DNS resolver completely separate from pfSense, like Pi hole. I hear good things about it but never had a chance to play around with it.
-
@Raffi_ said in Intermittent connection issue:
@kevindd992002 said in Intermittent connection issue:
Alright, so after some more testing I can say it's not the desktop causing the issue as it was more like a coincidence that happened. I've did more steps regarding DNS and the results were reproducible this time:
- Changed from regular DNS Resolver to DNS Resolver with forwarding (set to forward to 192.168.100.1 which is the modem's IP/gateway). Ping'ed 208.78.70.23 (one IP I saw in Status -> DNS Resolver) from pfsense's ping utility and there were no issues. Internet is back up and running.
- Changed back to regular DNS Resolver. Ping'ed the same IP from pfsense's ping utility and no response from 192.168.100.1.
So it looks like the problem is DNS but not the resolution part of DNS per se. For some reason, when DNS Resolver without forwarding is set the WAN gateway doesn't respond properly (or responds intermittently) as well, at least that's what's happening during my testing. So if you try to resolve with DNS Resolver, it's "as if" it is not resolving properly because of course it doesn't get any responses from the root hints servers consistently.
I know, the issue doesn't make sense but will getting a WAN packet capture while recreating the issue help in this situation? Or both WAN and LAN?
EDIT:
Also, I get a ton of Timeout A's under Status -> DNS Resolver when forwarding is NOT set. When forwarding, I get 0.
Ooooohhh I can't believe it didn't hit me sooner. This is a pretty well known issue with the DNS resolver (unbound) in pfSense. Here is one thread on it that I ran into when I had similar issues. https://forum.netgate.com/topic/120838/unbound-appears-to-restart-frequently-and-fails-to-resolve-domains-sometimes.
There are a number of solutions to this. As you found, use DNS forwarding. I would suggest forwarding to servers like Cloudflare (1.1.1.1 and 1.0.0.1) or Google (8.8.8.8 and 8.8.4.4). If you are going to use pfSense for resolving, go into the DNS resolver settings and uncheck the DHCP Registration option. That would explain exactly the issue you were seeing. When a PC is connected after 2 hours, it would request a new DHCP lease. When that lease is handed out, it also causes Unbound to restart because Unbound has to update its info since DHCP leases are being registered. This was a major pain for me. If you also have things that slow down the unbound startup process like lots of pfblocker IP lists, that will make matters worse.My current setup has DHCP registration disabled in the DNS Resolver options. I also have forwarding enabled to 1.1.1.1 and 1.0.0.1. Ideally, I wanted to have DNS resolution done by pfSense without having to forward, but it was not always reliable. I think the better solution would be to have a DNS resolver completely separate from pfSense, like Pi hole. I hear good things about it but never had a chance to play around with it.
I'm aware that DHCP registration restarts unbound but it does it just for a few seconds and everything should be back to normal. It doesn't explain what I was seeing with my desktop because that machine has an DHCP IP reservation. I thought those won't restart unbound? Also, if the unbound restart is the issue I won't be experiencing the issue for more than a few seconds. But in my case, I experience it for around 5 minutes or so, every single time.
Another weird thing is that I have the same exact setup on my network in the other end of the tunnel. That network also uses unbound without forwarding. And that network is 10x bigger than the network I'm trying to troubleshoot here. The network in question in this thread is made up of just 1 desktop, 1 nas, 1 laptop, 2 mobile devices, 1 nvidia shield, and 1 ps4. That's it.
Also, if it was a matter of unbound not working, I should be able to ping a public IP address (that's known to be pingable, of course) using pfsense. But like I said above, as long as I use unbound without forwarding, the issue of me not being able to ping presents itself right away.