Unable to connect local network to PFSense Private LAN
-
I am new to PFSense and know very little networking.
I've managed to install my PFSense Box on my Hyper-V manager. I've configured a WAN and LAN on the PFSense router. I needed to be able to reach the WAN and LAN from my local network (again this is my PC, or the host machine hosting my VMs on hyper V).
I have been able to reach the WAN from my local machine by adding a WAN rule in PFSense.
My local machine is 192.168.50.3
My WAN in PFSense is 192.168.50.17
I tried to do the same thing with my LAN but my LAN is on a different subnet and I cannot ping it or connect to the WebConfigurator.
My local machine is 192.168.50.3
My LAN is 192.168.20.1
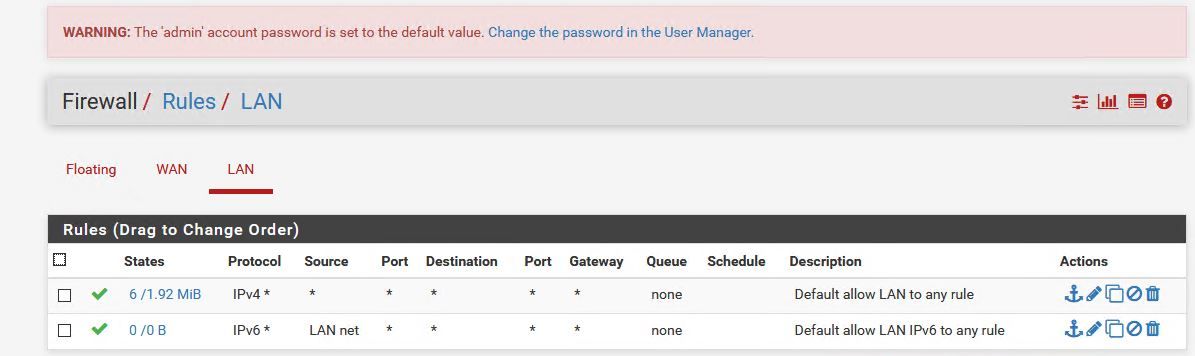
Below is what my PFSense rules look like for my LAN. Its basically open but my Windows host PC will not connect to it.
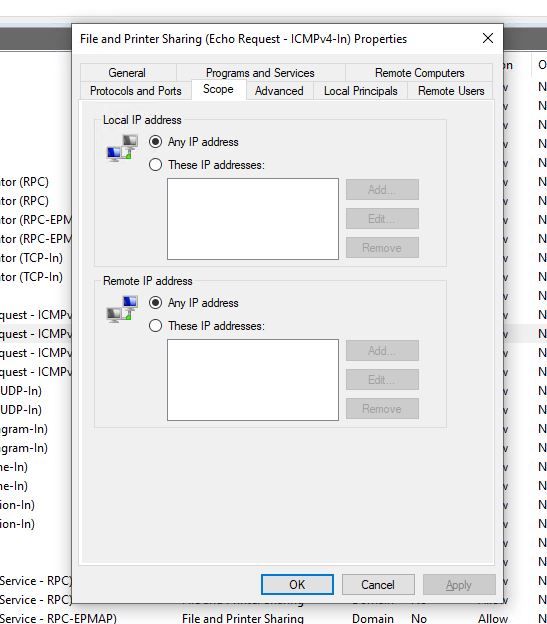
My PFSense VM will ping every device on my local network (so anything on the 192.168.50.x network) including the host PC. I looked on the windows firewall side of things and did the following:
That did not help either.
I have tried trace routing on both my workstation and the PFSense VM. The only machines that can reach the PFSense VM are in the 20.1 subnet and they are all VMs using the PFSense as their router.
Can anyone tell me what I am missing here? or what I can do differently? I need to access the PFsense box and all the VMs connected to it via my local pc network. I've been searching for a similar problem and I just cannot find one to reference from.
Thanks in advance
-
@pendelin said in Unable to connect local network to PFSense Private LAN:
The only machines that can reach the PFSense VM are in the 20.1 subnet and they are all VMs using the PFSense as their router.
This may be the point here, your devices in the .50.x subnet may use a different default gateway. So the devices in this subnet need a static route for the.20.x subnet pointing to the pfSense WAN IP to be able to communicate.
Another (better) solution is to span up a transit network between pfSense and the other router. -
Hi Viragomann,
You were right. I added a static route to my routing table on my workstation (192.168.50.3) and now I am able to ping my PFSense VM LAN (192.168.20.1) and the VMs that use it as a gateway.But the issue remains that I cannot load the webconfigurator page for PFSense nor can I remote into any of the VMs in 20.1 subnet. I can only ping them? What am i missing?
SIDE NOTE: What did you mean by Span up a transit network? What is that?
Thanks again for your help.
-
@pendelin said in Unable to connect local network to PFSense Private LAN:
But the issue remains that I cannot load the webconfigurator page for PFSense
Have you added a firewall rule on WAN interface to allow such access? pfSense doesn’t allow anything on WAN by default.
@pendelin said in Unable to connect local network to PFSense Private LAN:
I can only ping them
That’s often an indicator for asymmetric routing.
Ensure that pfSense is set as default gateway on the destination devices in the 20.x subnet.
Also ensure that the destination devices firewall allows that access. The Windows FW rule you posted above allows only ping (ICMP).A transit network is the way to go if multiple networks use different default gateways.
So network A use router A and network B use router B parallel for upstream traffic. No you connect an additional network interface of router A with an additional network interface of router B (this may also be VLANs on an existing physical interface) and configure an additional subnet on it.
Now you set a static route on router A for the network behind B pointing to its transit networks IP and vice versa.
So both networks use their separate upstream gateway and traffic to the other network is provided by static routes on both routers. -
Yes, you have an asymmetric route if you are coming from any other machine in the .50 subnet that does not have a static route directly.
https://docs.netgate.com/pfsense/en/latest/firewall/troubleshooting-blocked-log-entries-due-to-asymmetric-routing.htmlAre the VMs in the .20 subnet able to accept TCP traffic from outside their own subnet?
Steve
-
@viragomann and @stephenw10
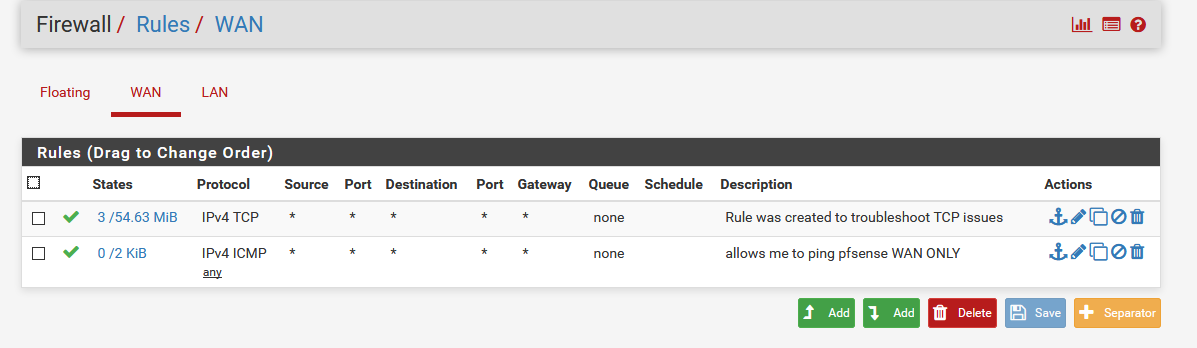
OK here's what worked."Have you added a firewall rule on WAN interface to allow such access? pfSense doesn’t allow anything on WAN by default."
Ok so here's how I solved this problem. But before I say what I did, remember this is a testing environment, security is not a concern.
Like I said earlier I could ping each network from the other (50.x could ping 20.x and vice versa), however I could not remotely login to any VMs in hyper-v nor could I browse to PFSense's web configuration interface.
Apparently the reason I could ping was because of 2 things:- I added a static route to my local PC for the 20.x subnet ---> allowing me to ping the 20.x subnet from the 50.x subnet.
- I added a rule in my PFSense WAN to allow me ping the WAN. -----> this allowed me to ping the WAN (the wan is a 50.x subnet address)
Once again, neither of the additions above allowed me to remote to a VM or view the web configuration page of PFSense. After your help and some more inquiry. I just found that well ICMP is what PING uses. In my PFSense WAN rules all I had was to allow for PINGS, so I added one more rule for TCP (see below): Gave it a swirl and it worked!!!! I can now remote to the any VM in hyper on any client as long as I added a static route for the 20.x to that client (there are only 4 client devices that need this)
-
Ah, OK. Yes you would need firewall rules to pass the traffic. That should have appeared as blocked traffic in the firewall log before you added that TCP rule.
You might want to just change that rule to allow 'any' protocol but set the source as WANnet and destination as LANnet. That will restrict it to local connections only.
You will still need the static route to the .20.x subnet on every client that needs to access it. An alternative would be to put the static route on your upstream router instead. However you will hit asymmetric routing issues if you do.
Steve