IPSec site to site with access to other sites
-
Hello,
We have 3 sites connected with a site to site IPSec VPN. Theses sites uses :
- Site A : 192.168.0.32/27
- Site B : 192.168.0.0/27
- Site C : 192.168.0.64/28
All of these 3 sites can communicate successfully between them.
We also have an external office connected using IPSec VPN (site to site) to Site B.
We like to give access to all other sites by using the existing VPN to this external office (rather than creating a VPN per each other site). So our external office can access to servers on Site A and on Site C.
We have tested using NAT/BINAT with a specific range of address, but this fail.
How can we give/create this kind of access ?
Hope I'm clear.... :-)
Thanks a lot for your help.
Regards,
-
Configure the VPN for site B to Sites A and C to carry the traffic between Sites A and C and the fourth site (Site D?)
Configure the VPN between sites B and D to carry the traffic between Site D and Sites A and C.
-
Hi,
Thanks for your reply.
Do you mean that I need an IPSec phase 1&2 for each sites with external Office ? This is what I want to avoid...
Sites A, B, C have a good Internet bandwidth, not external Office.
Or there is something I don't understand.
Thanks !
-
Just Phase 2.
-
Hi,
Thanks for your help and sorry for my late reply (I'm too busy).
(Site D naming is use for our external office.)
I'm not sure to understand, so this is what I've done :
On Site A:
- IPSec VPN with site B including phase 2 for site B network access and site D.
- Adding a static route (System | Routing) for network of site D (like I've done for network of site B).
- Adding a rule on IPSec tab to allow traffic (with log enabled)
On site B:
- IPSec VPN with site A including phase 2 for site A network access (working good) and site D (I think this is necessary, no ?).
- Adding a static route (System | Routing) for network of site D (like I've done for network of site A).
- Adding a rule on IPSec tab to allow traffic (with log enabled)
Can you tell me if I'm wrong or not ?
During my tests, I can see packets from site D to site A transit in the access rule of site B. But no packets are logged on site A from site D...
I think something is bad on my config but I can't understand what...
Thanks !
-
Please use real subnets in describing what you have put where. I can't make any sense out of site A to site b, etc.
Maybe use this to describe what you have done:
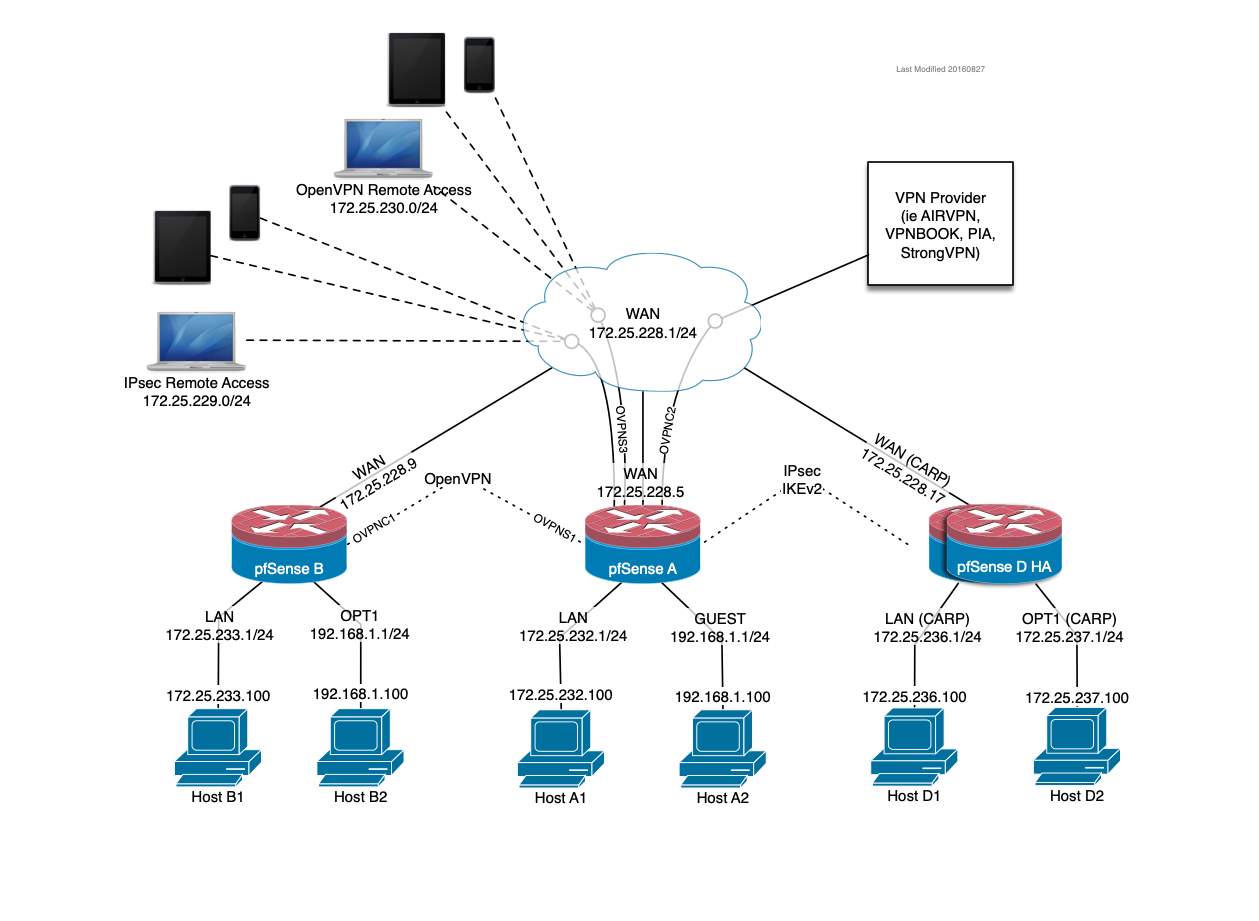
-
You don't use static routes for IPsec unless you're using VTI.