Bring corresponding bridge link down on link failure
-
I want a script to determine if one link of bridge goes down then bring the other link down as well. Please provide any insight and pointers where to start.
I have Bridge with two interface, If one link in bridge goes down I want firewall to bring the other link down as well if link comes up then bring the other side of the link up.
The technical term I believe is Link Fail Propagation.
-
What is the purpose of this? There may be some easier way to accomplish it.
Does it have to work in both directions? That becomes more difficult.
Steve
-
Yes, it has to be both directions.
Why would get complex, so I have pfsense working in transparent bridge mode with snort inspecting traffic. Pfsense is sitting between switches with multiple links for redundancy. Since pfsense does not pass LACPDUs I had to set static LAG between these switches and with static LAG is one side of link goes then other side still stays up and all the traffic is black holed since one side of bridge is up and other is down.
-
You have two connections between the switches in a lagg group and pfSense is in only one if them?
There is nothing like this in pfSense currently so you would need to script it yourself. I could imagine something that runs when one interface goes down that marked the other one down. But once both are down how do you see them come back up? It would only come back up in the same direction. Unless you are able to mark it logically down whilst still seeing the link media status perhaps...
Steve
-
I have 2 connections between switches which are in static LAG with each other not with pfsense.
I can work with just link going down and not coming back up for now, it will at least help me stop black holing the traffic till I manually intervene.
For Diagram Purpose
SW1
| |
| . |
Pfsense (Transparent Bridge in IPS mode running snort)
| |
| |
SW2 -
The diagram is not entirely clear; is pfSense in both links there or just one?
The redundancy is in case pfSense stops forwarding traffic?
-
ok I will try to add more details
SW1
1 2
| |
| |
0 2
Pfsense
1 3
| |
| |
1 2
SW2SW1 (Trunk Ports 1 and 2)
SW2 (Trunk Ports 1 and 2)
With Trunk I mean Static LAG.Pfsense
Bridge Ports 0 and 1
Bridge Ports 2 and 3I am using it this way to have it in transparent mode and it can still inspect all traffic using snort and I do not have to worry about routing or anything.
Let me know if it gives a clear picture or not.
-
Ah, OK I see.
Could you not set those links as LACP LAGGS to pfSense on both sides and then bridge those?Stve
-
No, I already tried that, make a LAGG in pfsense but then there is not way to bridge it. Pfsense only allows bridging interfaces.
-
You have to assign the LAGG as an interface first but you can bridge lagg interfaces. I have that running here, not with two laggs but I see no reason why not.
Steve
-
Just to confirm,
You have a LAG1 and LAG2 bridged together.
Did you create LAG first or bridge first ?
-
Currently I have a lagg interface bridged to a single interface but there no reason it could not be two (or more) laggs.
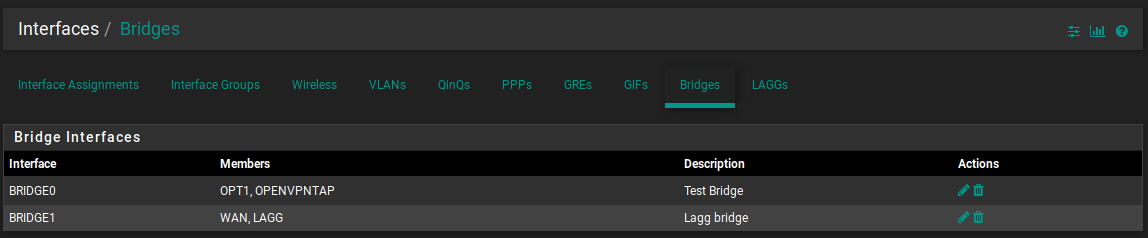
Create the two laggs. Assign and enable the laggs as interfaces but leave them with IP type none.
Add the lagg interfaces to the bridge.
Steve
-
Ah I get it, I have to add it as interface only then it shows up under bridge.
Thank you very much for your time, this is very very helpful. I will give it a shot.
Cheer

-
Btw I just though about it, the original problem will still persist.
Lets say SW1 links go down, SW2 link will stay up and the traffic coming back from network will still be blackholed.
-
Hmm, if pfSense was not there and sw1 was just lagged to sw2 directly. If sw1 failed so the lagg went down entirely what would sw2 do with the traffic? It has some failover ability?
Seems like a job for routing protocol, which would also work with pfSense in the way, the link would still fail.
Steve
-
Consider this scenario, I am telling as it happened in production.
One link of SW1 went down, so all the traffic was making to the network from the port 2 of the SW1. But on way back since SW2 saw two links up port 1 and 2, it was redistributing that traffic on those links, the traffic made to firewall but since port 1 of SW1 was down the traffic didnt know where to go or in other words one port of the bridge was down so traffic had no where to go and caused spontaneous drops and other weird issues.
Any way if one link of bridge goes down relayed to the other side of bridge will be useful in such scenarios.
-
Right but with LACP LAGGS on both side that won't happen. LACP would see the link down and send all the traffic to the firewall over the other one.
If the firewall fails or both links on one side fail (the switch fails) then you would get no traffic but that would be the same if the switches were connected directly.What won't happen is that SW1 won't see if SW2 goes down, at least not directly. But I'm not sure there is any scenario where that would be useful.
Steve
-
The LACP LAGG will be between SW1 --- Pfsense ---- SW2 not between SW1 --- SW2, so SW2 would never know if link 1 on SW1 has gone down for it both the link on the LAGG are up.
Pfsense does not support passing LACPDUs over a bridge interface, if that can be somehow enabled that might just resolve the problem from the root.
-
Right but you won't dump any packets. All the traffic will just use the remaining link. You jst need to make sure you are alerted to the fact it went down.
Steve
-
I will give it a shot. Thank you again for your time and insight.