Blocking constant attacks
-
Hi,
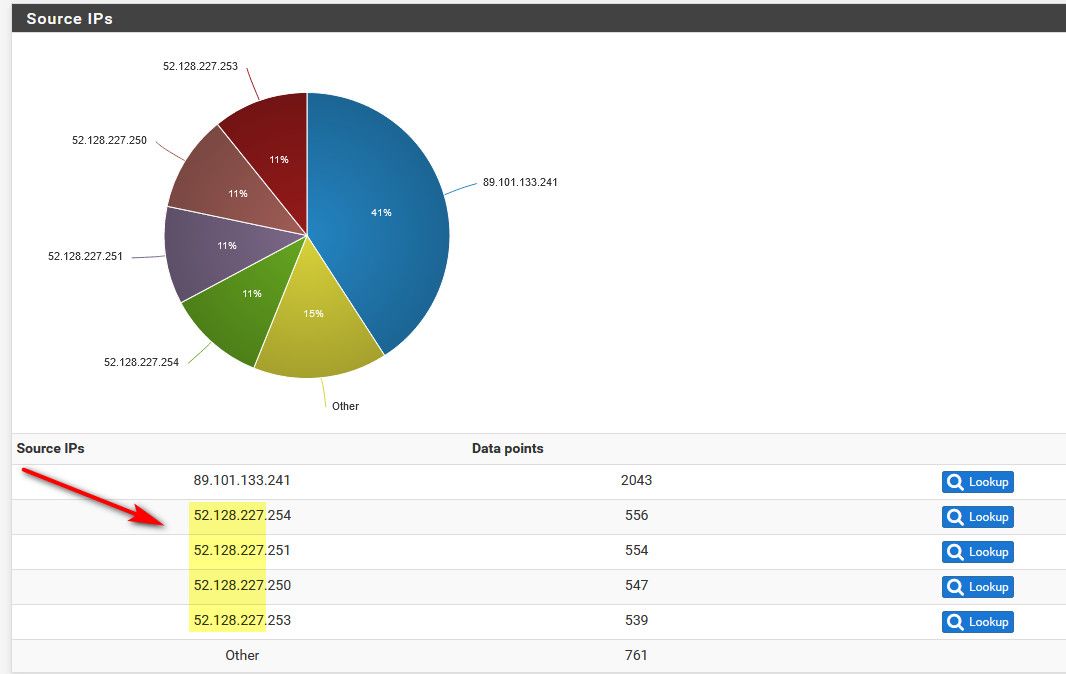
For a while now, I am getting constant attacks on my port 443 from various IP ranges. Right now, 52.128.227.x is hitting me a few times per minute. I am running OpenVPN on this port, so the connections do not actually succeed but the requests do pass through pfsense. I have tried blocking these /24 ranges only to find another range to hit a few hours later. Is there a way to detect and block these IP ranges?Thank you.
-
PfSense should be blocking them. Are they getting through somehow? PfSense can't stop them, until they reach it.
-
We all seeing them ;) See my pesky fly post in the general area.
Its just annoying noise is all.. You can use pfblocker to only allow the countries you want.. I also run openvpn on 443..
I just use pfblocker lists to allow for only allowing the countries I want/need to access my forwards.
That IP range is all out of HK... I just noticed all the hits from Ireland on mine - forgot I had a friend in IE on travel - they trying to hit my plex ;) Had to open it up for IE, hehehhe
-
@johnpoz: Thanks for your response. I will look up your previous post. I checked the various IP ranges and the country of origin is all over the place. I am using pfblocker to block the worst offenders, i.e., China and Russia, but I am hesitant to shut down the world. It sounds like it's just an annoyance, at least as long as OpenVPN is not (known to be) vulnerable.
The only thing I was wondering is whether there are are blocklists for these attackers. But there are so many of these blocklists that I would not know where to start.
-
You could look at firehol, or dshield for lists..
Also vs blocking the world, you just allow what you want.. I am not traveling - so why would any ip from outside us being using my vpn? So I only allow US..
All my friends and family are in US, so why would I allow anyone outside of US to talk to my plex server? I use to before make me give them their IP and put it on whitelist.. Bu that was a bit complicated for some of them - you know what your puplic IP and they just stare at you like a deer in your cars headlights..
-
FireHOL seem to have a gazillion lists. I tried firehol level 3 yesterday and that did not do the trick. I am on travel now and will take a look at the other lists when I return.
Regarding the blocking, you are right, everyone's needs are different. I do travel quite a bit including international so blocking complicates things for me. Being from Europe and living in the US I also use international sites quite a bit. I could probably tighten down unsolicited inbound traffic and may think about it. Usually snort takes good care of blocking bad traffic, so I am not generally concerned. This case just stuck out.
-
@revengineer said in Blocking constant attacks:
US I also use international sites quite a bit.
Not blocking outbound... You never know were a site might be hosted.
If I was going to travel to X, then I would open up my vpn from X... But I see little reason for some IP in xyz country to be talking to my plex or my vpn server.. There is zero point to it..
But I don't block outbound other than ads via pihole.. and ublock in my browser..You never know where some site I want to go to is hosted..
-
One way or the other, the FW has to make a call whether it's blocked by country or just blocked, so what's the point of country block? The FW still burns cycles. Curious. I just use pfB to block outbound.
-
Inbound blocking only makes sense when you have port forwards in place or access to services on the firewall open like OpenVPN in this case. Then you can restrict by source IP using pfBlocker rather than just open it to everywhere.
Steve
-
@stephenw10 I see. I guess that may give support to using some rando upper port for VPN rather than something common like 443?
-
Yeah, you will always get way more hits on 443 than anything else. Port 1194 also gets probed as it's the default OpenVPN port. 11194 not so much. But really that only cleans your logs, security through obscurity is not real security.

-
@stephenw10 Yeah, the only real security is an air gap... But with 128K+ ports to choose from, I can be pretty obscure!
-
I really need to use 443 to be able to get to the vpn from work... I would normally just lock it down to my work IPs for this use.. But you do run into issues where only thing out is 443 tcp, etc. So in that case I can still access my vpn.. So I do the best I can and restrict it to US.. But my vpn and ha proxy doesn't need to spin cycles dealing with nonsense - much easier to just not let them any farther up the stack then the firewall.
-
@johnpoz said in Blocking constant attacks:
I would normally just lock it down to my work IPs for this use.
That's what I did. And I managed the FW. Nowadays (retired) I just enable VPN when I'm out of town (or Lazyboy).
-
@stephenw10 @provels I travel a lot and find that half the hotels block ports other than those used for web browsing, i.e., 80 and 443. While I have a UDP instance of OpenVPN running on port 1194, I frequently need to revert to the secondary instance on port 443 using TCP. So for usability, there is really no way around this.
-
@revengineer said in Blocking constant attacks:
hotels block ports other than those used for web browsing
Yup unless you pay for their "premium" wifi ;) quite common for them to do that - which is why running on 443 to get around those restrictions. But it can also see a lot of traffic that is not your vpn.
-
@revengineer @johnpoz Good to know, thanks.