DNS Resolver - SSL Handshake Fail/Server Cert Fail
-
Hello all,
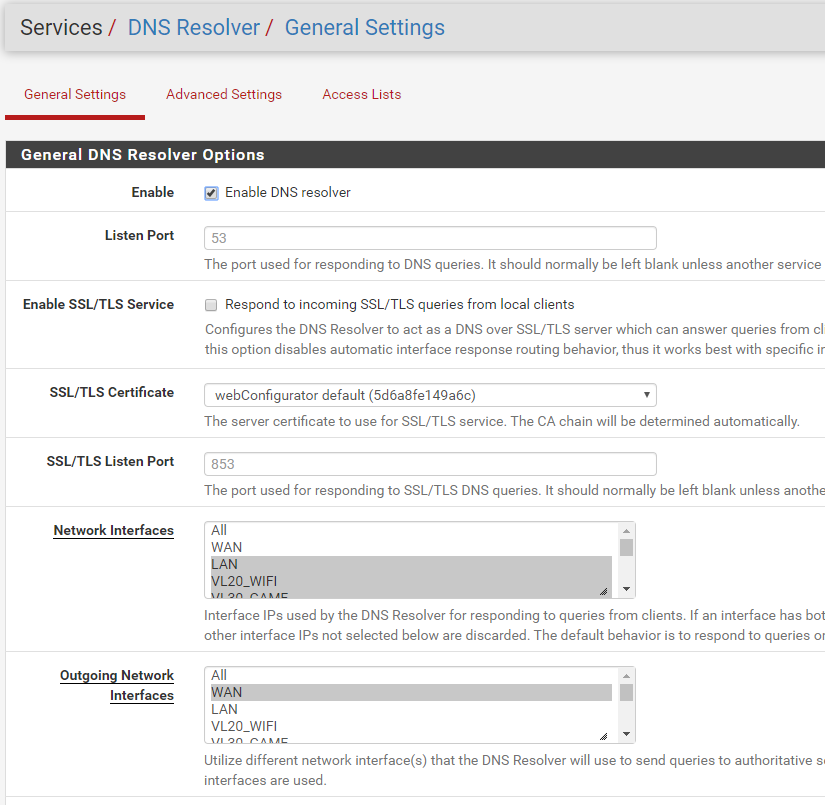
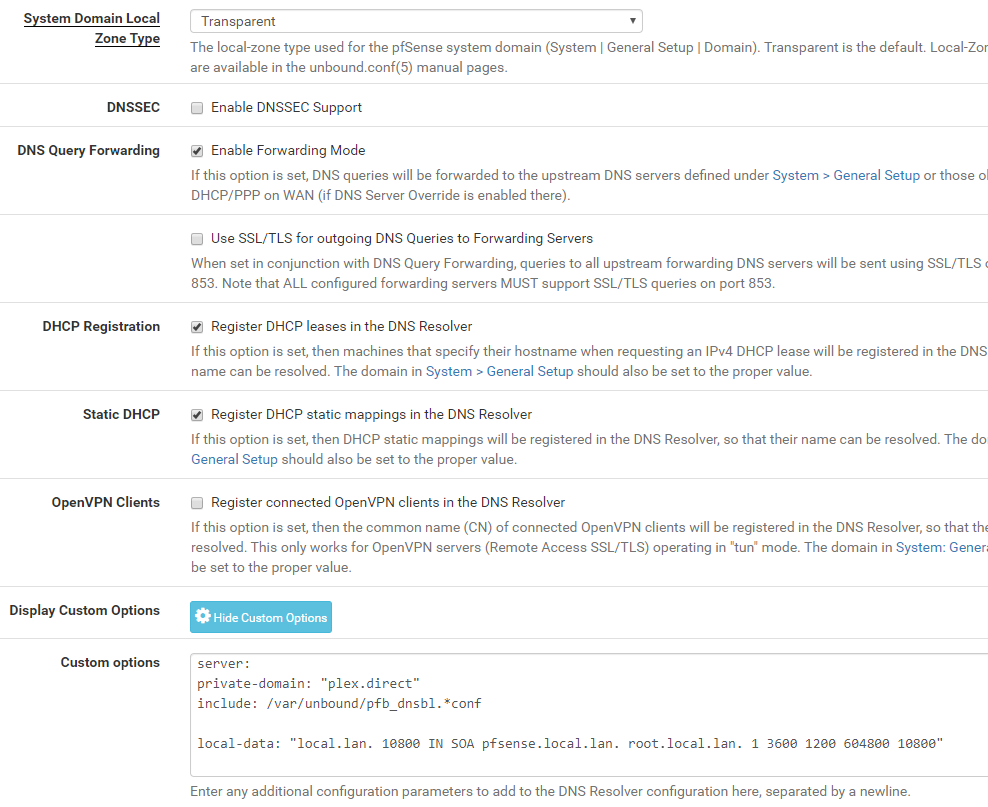
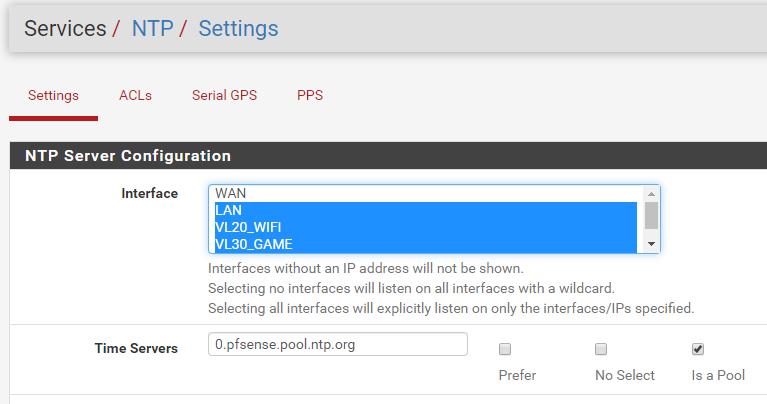
I have been using my pfSense home made box for about 6 months now learning all I can about it (double NAT'ed). About 3 weeks ago I went live with it can sent back my Comcast Modem (now using an ARRIS SB6183). I have, like most I would imagine, "broke the internet" for the house already several times! LOLMy latest, and current, major issue is getting "SSL/TLS for outgoing DNS Queries to Forwarding Servers" to work. I have looked high and low and have come up empty handed in trying to get this going on my own. I'm sure it's that "one thing" I overlooked or clicked by accident. Can you guys/girls give me a hand?
Issue
For some reason, as soon as I click/enable the "SSL/TLS for outgoing DNS Queries to Forwarding Servers" setting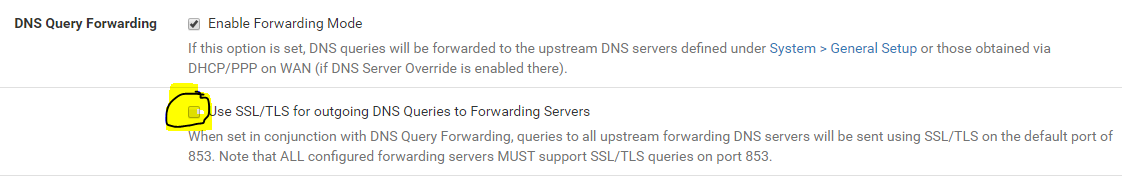
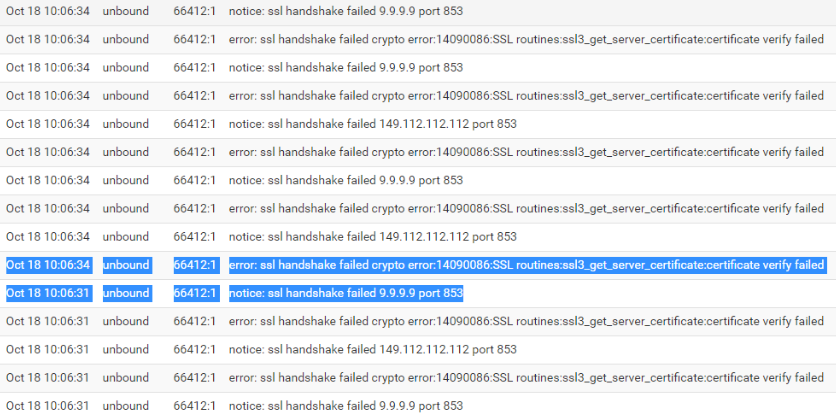
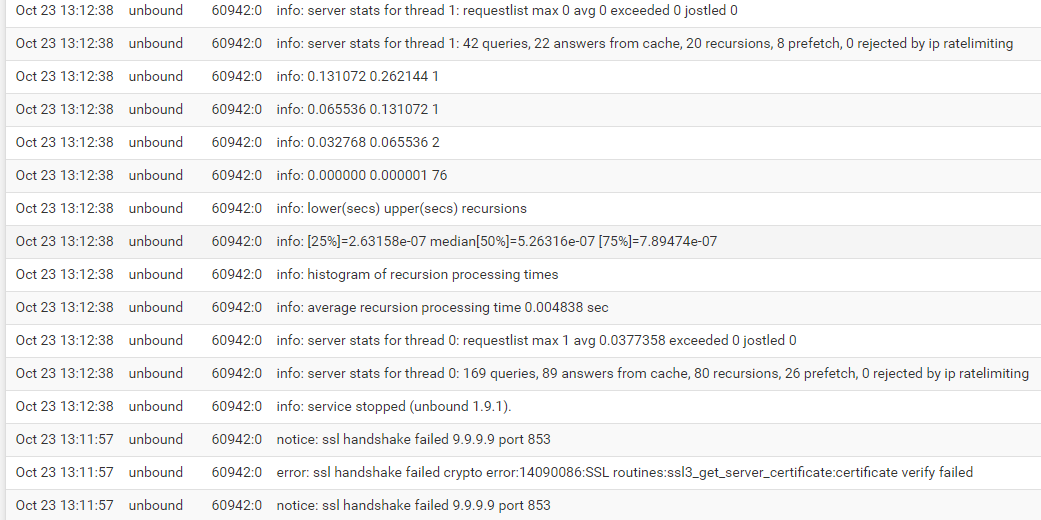
I loose all ability to go to websites and all software is unable to get outside the house. I still have a connection on the WAN, but can use it. As soon as I disable it, all goes back to fully working.I did some searching and discovered that i was getting a "ssl handshake..." error and notice (see below picture). After seeing that, i have tried several things and different "Custom Options" at the bottom of the DNS Resolver settings to no avail.
My few places I have looked for a resolution:
unbound-tls-forwarding
verify-tls-certs-unbound
configure-unbound-to-validate-dns
setup-dns-over-tls
And let's not forget... www.google.com :-)I've also tired disabling pfBlocker, restarting pfSense, clearing states, cussing, swearing, not sleeping well b/c I keep thinking about this, & being in an overall grumpy mood most of the time!
Now, i'm turning to you guys for some help and guidance.
I have tired to give you any and all the info you may need about my system but i'm sure there is more you would like me to show, if so, please let me know.Thank you all in advance!
My info
Version: 2.4.4-RELEASE-p3 (amd64)
PC: Pentium(R) Dual-Core CPU E5300 @ 2.60GHz; 2 CPUs: 1 package(s) x 2 core(s); AES-NI CPU Crypto: No; about 3GB Ram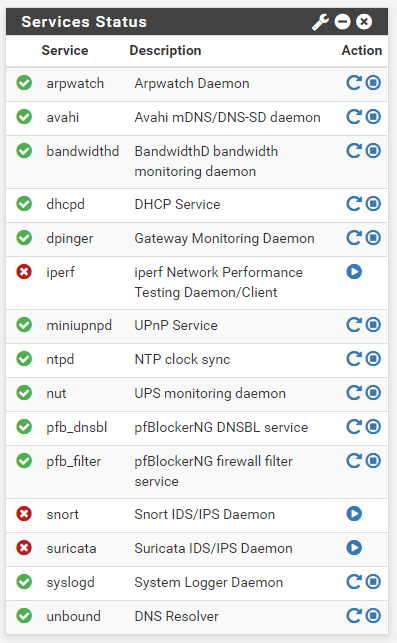
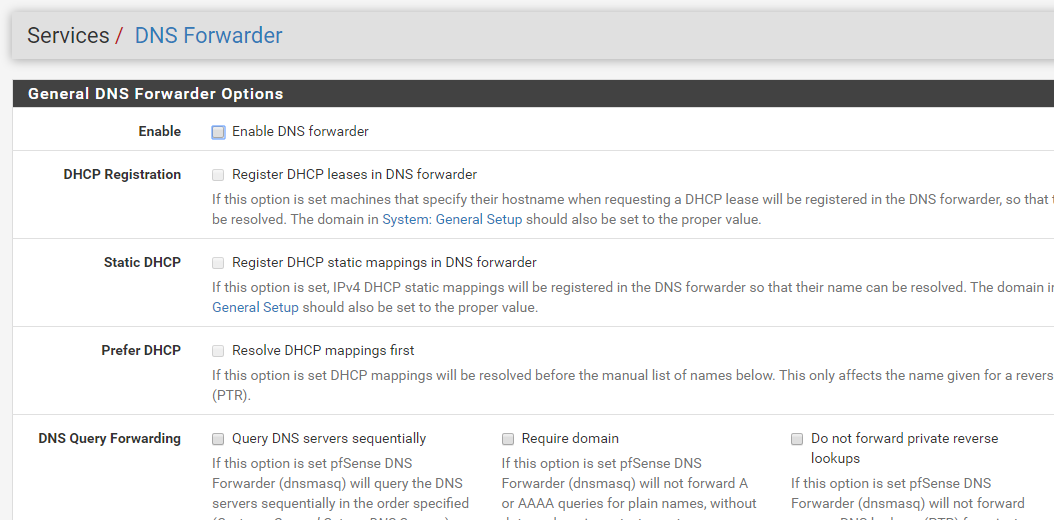
And b/c I read something about "time being off".
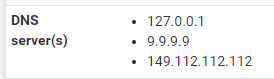
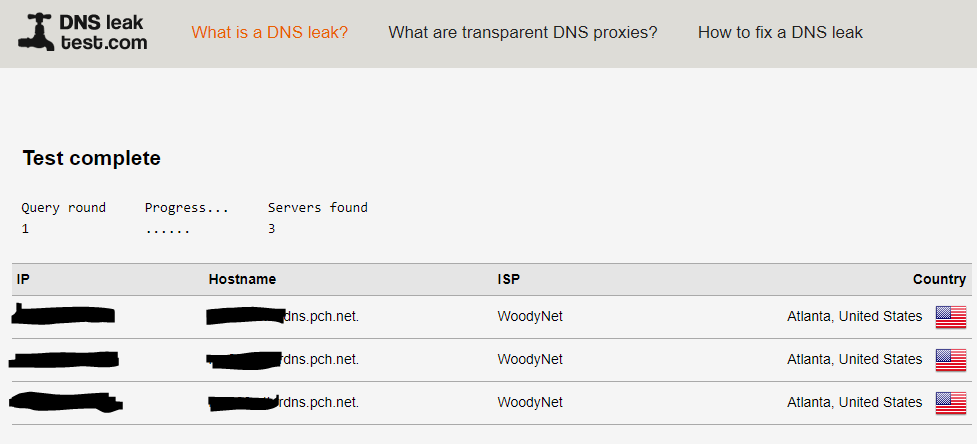
https://dnsleaktest.com
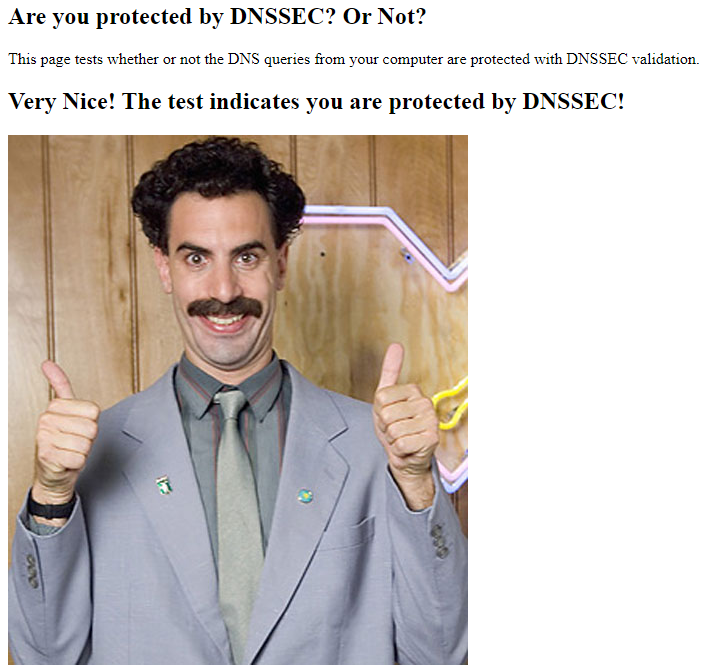
http://www.dnssec-or-not.com/
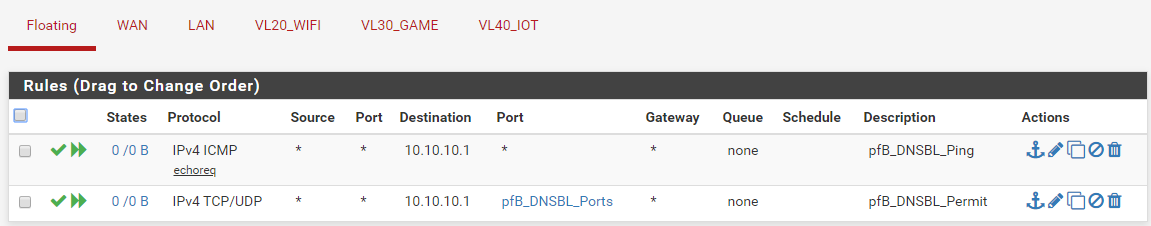
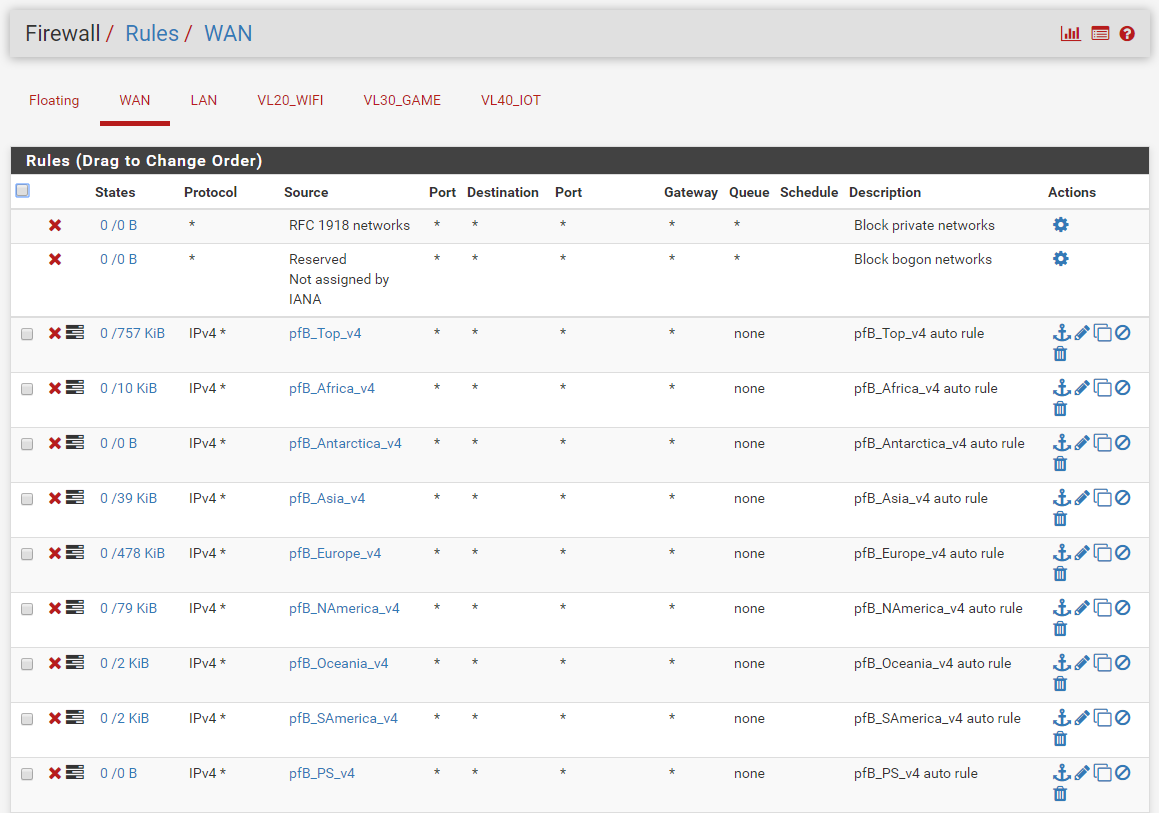
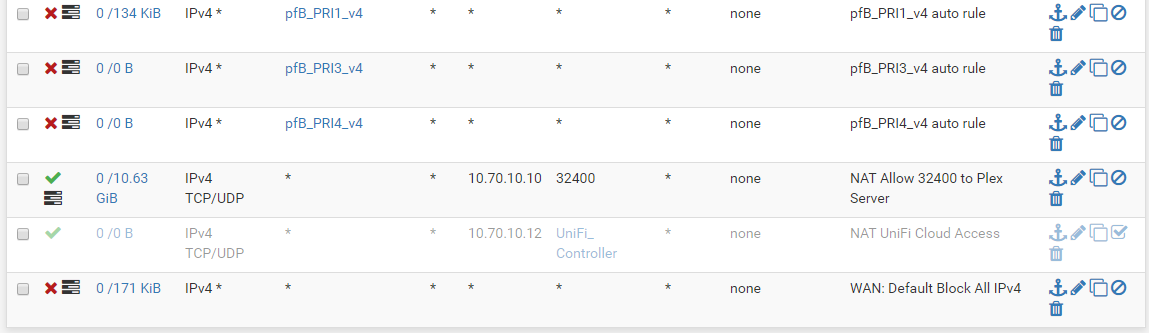
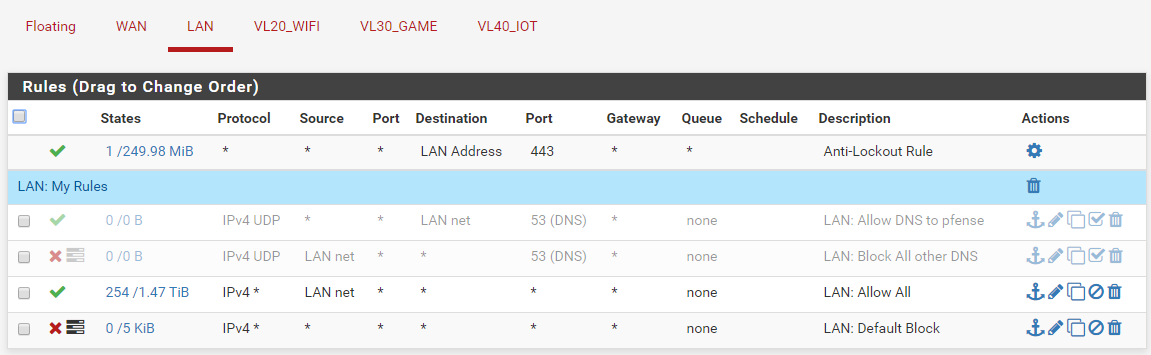
Firewall Rules
Errors/Notices
-
I tried setup-dns-over-tls and the instructions in that post worked right away (DNSSEC should be disabled of course, as it make no sense to use DNSSEC when forwarding).
The test as mentioned :
I could resolve just fine ....
Several observations :
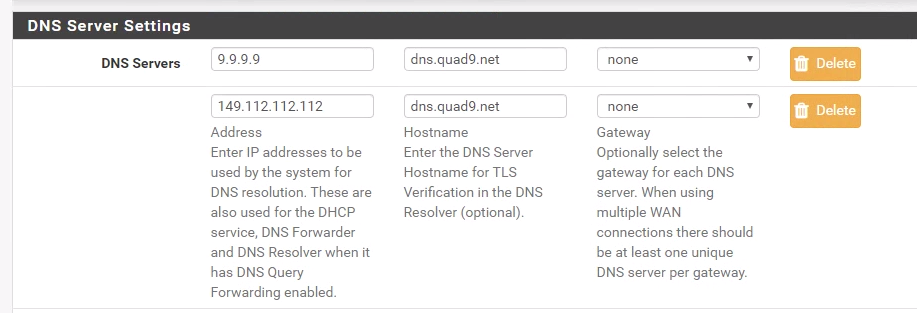
DNS Gateway should be None I guess :
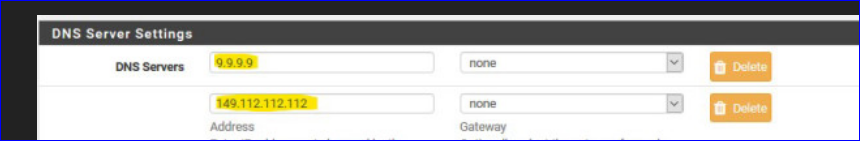
You have something different.
Also : verify that you have "Verify that you selected ALL network interfaces." selected. I did.
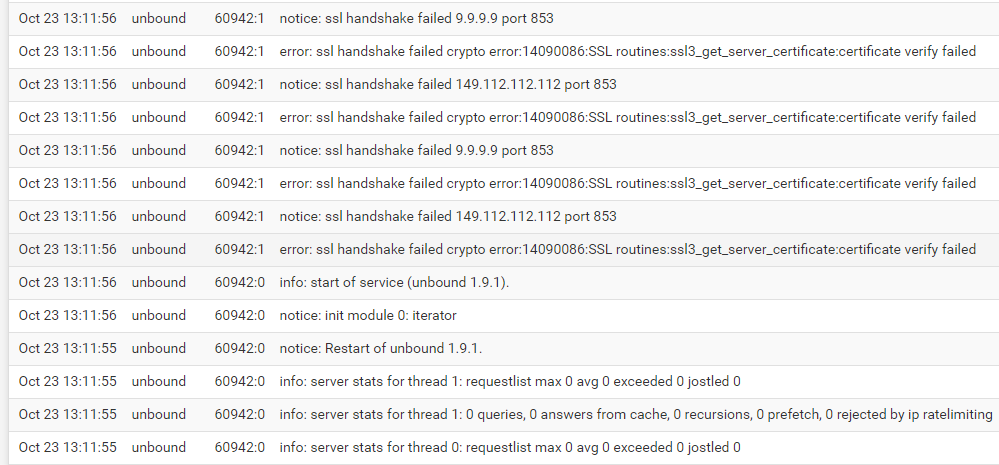
Your logs states -as you high lighted :
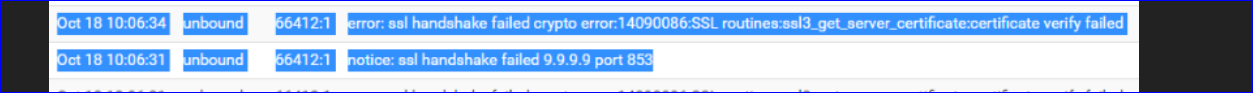
Thus, your certs failed verification.
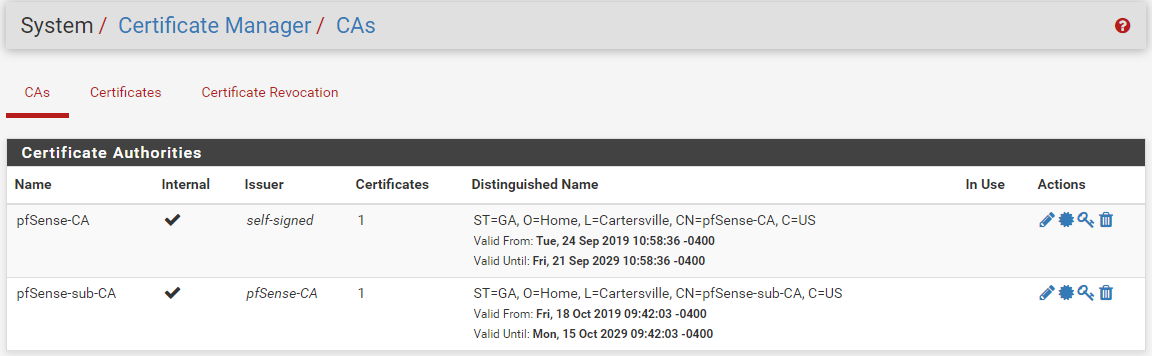
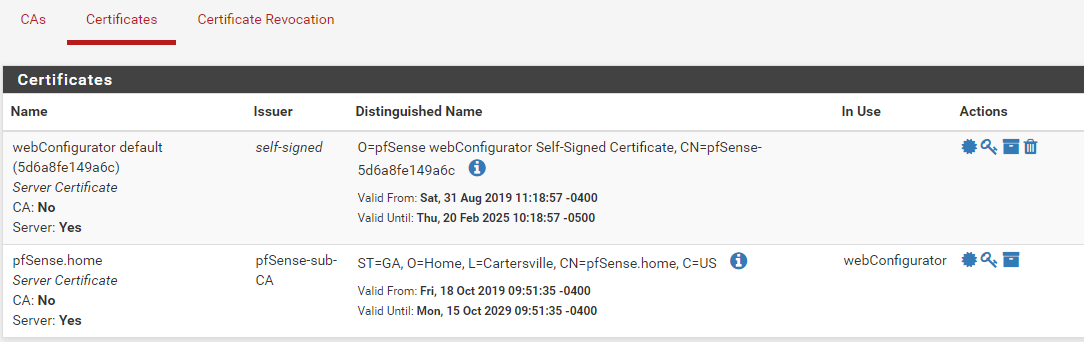
I tried 'real' certs from Letenscrypyt, and the auto-created "Web" cert from pfSense :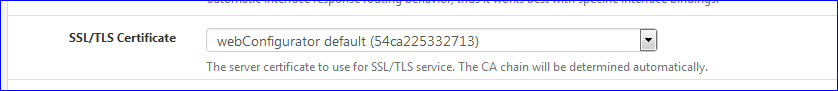
both where accepted.
Your pfSense system time is ok ?
-
Thanks for the feedback.
None of that seemed to help though... :-(Here is what I just tried:
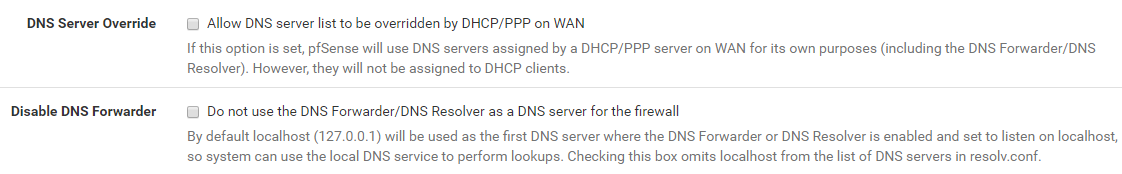
Changed my Gateway for both DNS Server under settings from "WAN gateway" to "None".
Changed the my interfaces to "ALL" on the "Network interfaces" and "Outbound Interfaces".Not sure how to make sure my certificates are in the right location on my system.
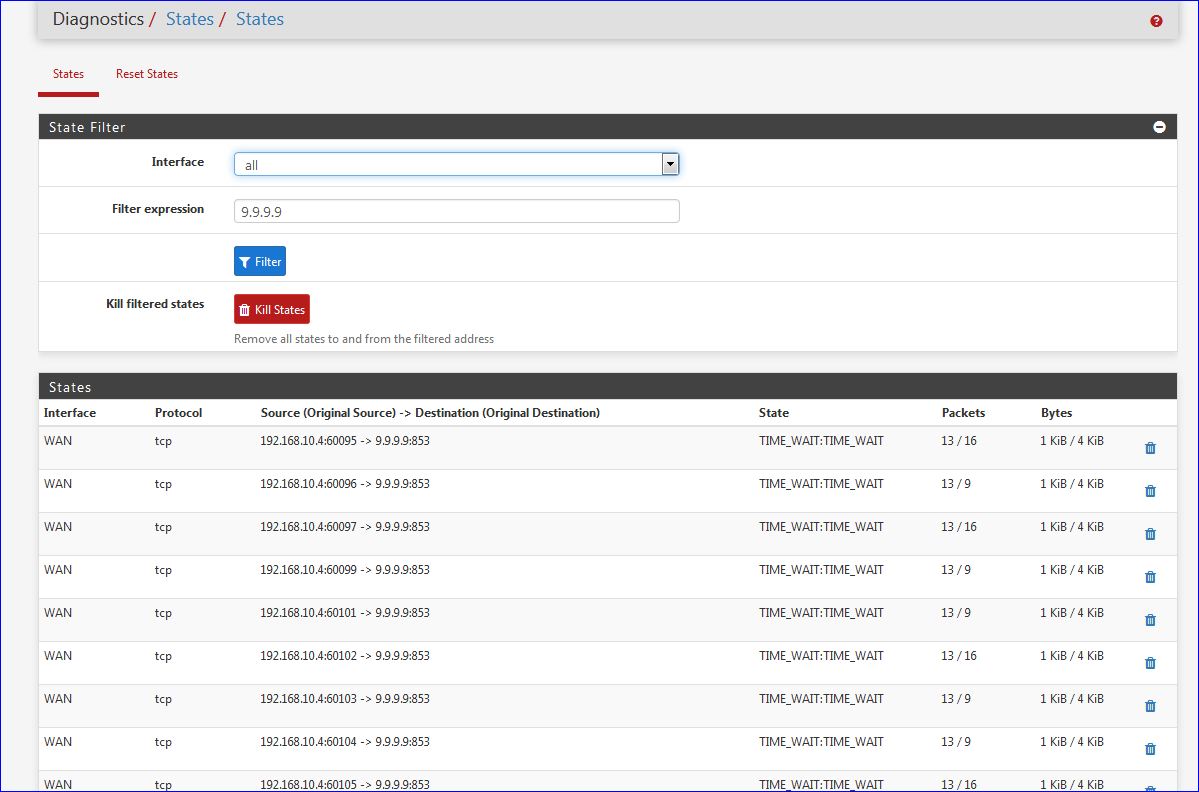
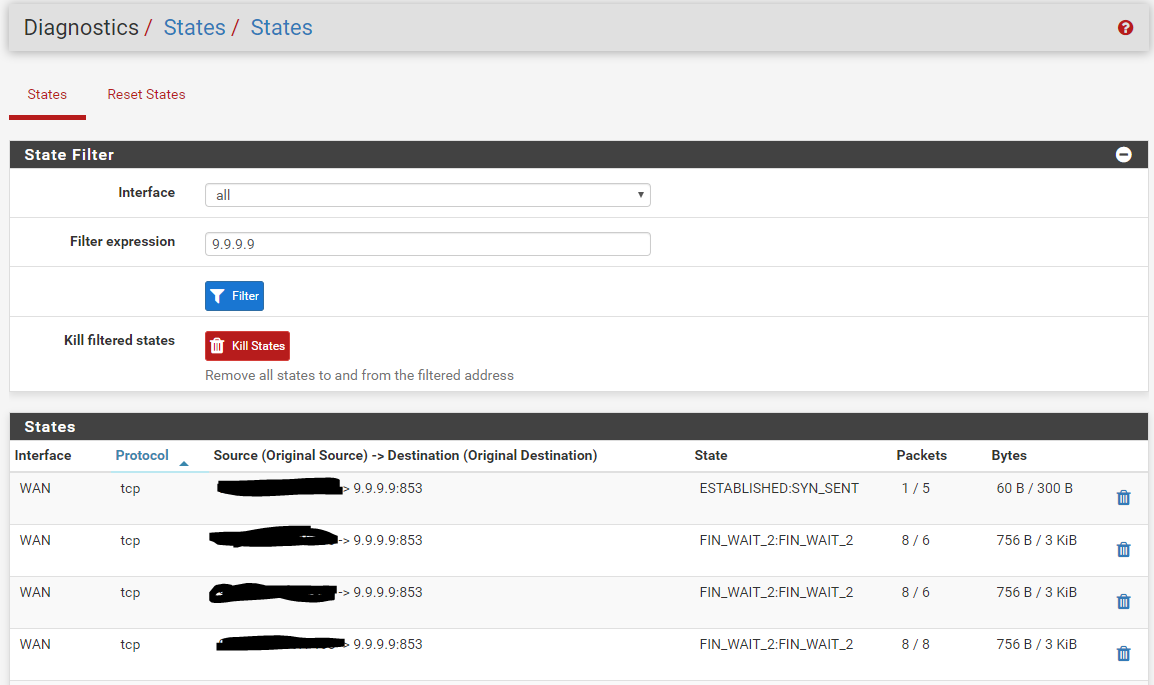
I tried using my other Cert but no luck.My results while I had "853" enabled
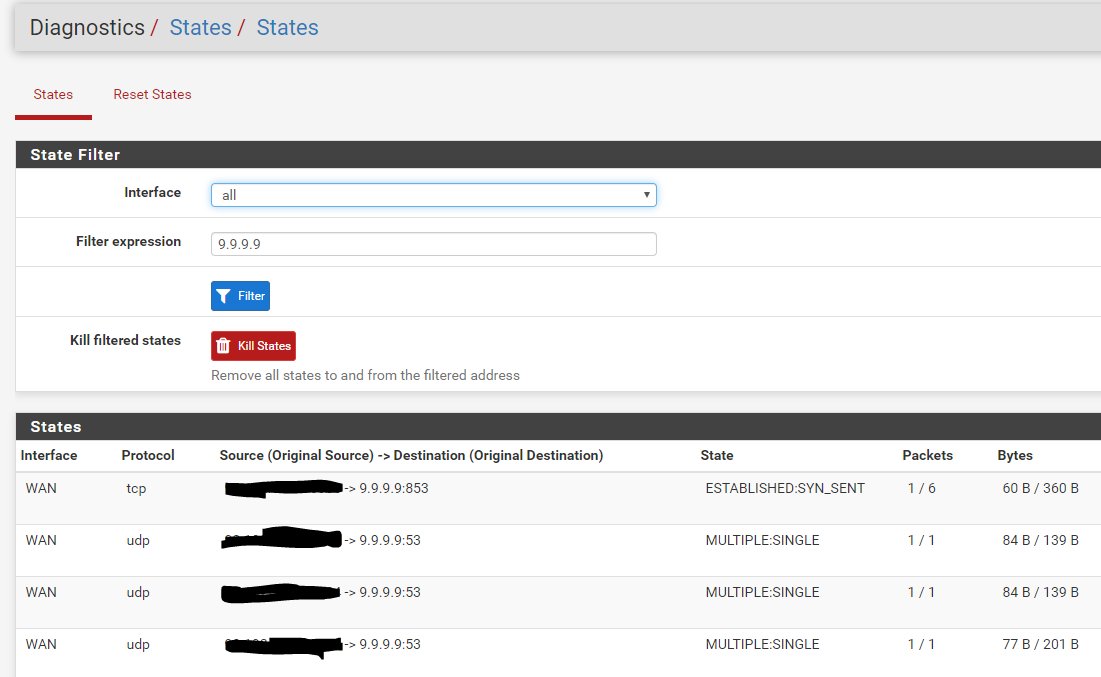
My Results after disabling it
Also, I verified my time is correct.
Compared it to time.govNow, I didn't do a full reset after I enabled "SSL", I'll have to try that later, but i'm pretty sure I've already done that too.
-
Are you sure about DNSSEC?
@jimp said in Setup DNS over TLS on pfSense 2.4.4 p2 - Guide:
DNSSEC is for validating authenticity (prevent spoofing, hijacked authoritative nameservers, etc).
DNS over TLS is for encrypting transport (privacy).
They do different things and are both are useful, especially together, for increased security and privacy.
There is no reason you can't run both, unless whatever you are forwarding to does not support one or the other.
-
@CiscoX said in DNS Resolver - SSL Handshake Fail/Server Cert Fail:
Are you sure about DNSSEC?
Yep, because you (have to) trust the server you forward to.
See the discussion, the last 20 messages or so at the bottom of that guide.It might probably work with DNSSEC activated.
But, jey, we're looking here why things are not working for @ryan810cows - so I tend to stick with the guide, and taking out all the other stuff out of the equation. -
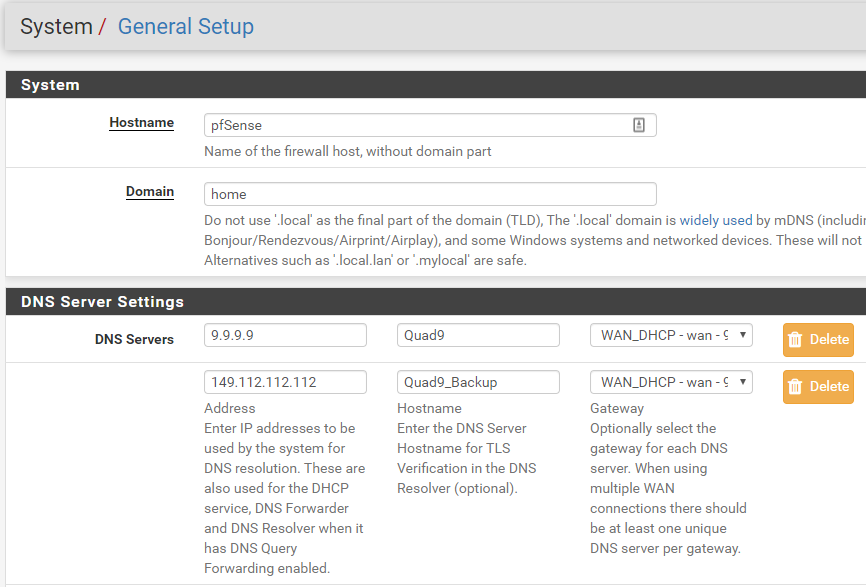
Where did you get those host names for quad nine on the General tab
-
I just made up the Host names for quad nine.
I thought that was just for organizational purposes.
MAYBE that's it!!!
I'll try it in a little while and report back! -
Does Quad9 support DNS over TLS?
We do support DNS over TLS on port 853 (the standard) using an auth name of dns.quad9.net.
https://www.quad9.net/faq/
-
Interesting. I just read that too.
Does that mean i need to put "dns.quad9.net" in both of the Host Names in the General settings of just leave them blank? -
that is how mine is configured
-
OMG.. That was it! I'm SOO happy that worked!!
THANK YOU SOO SOO MUCH!! The community support here ROCKS!