IPv6 only subnet. How to turn off logging blocked ipv4 link local?
-
I have setup a subnet that is ipv6 only for testing and it works pretty well (I have a separate NAT64 gateway setup also) so far.
The issue I have encountered is that many clients are still dual stack, and my logs are filled with "Block IPv4 link-local (1000000101)" entries.
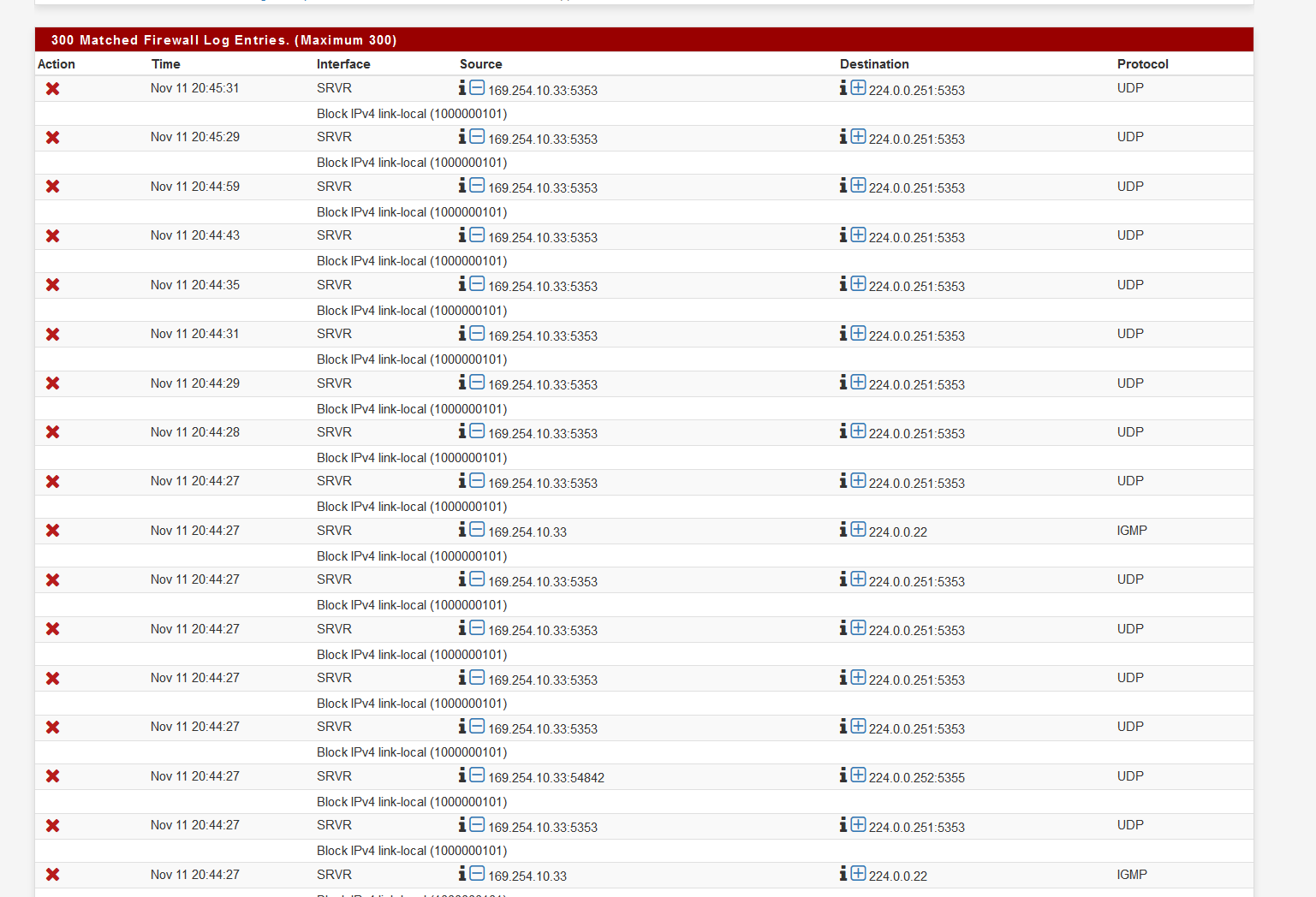
I have tried setting up rules that would block but not log, but the rule that blocks ipv4 link local traffic apparently fires before the interface rules.
Here are the firewall rules for the subject interface:
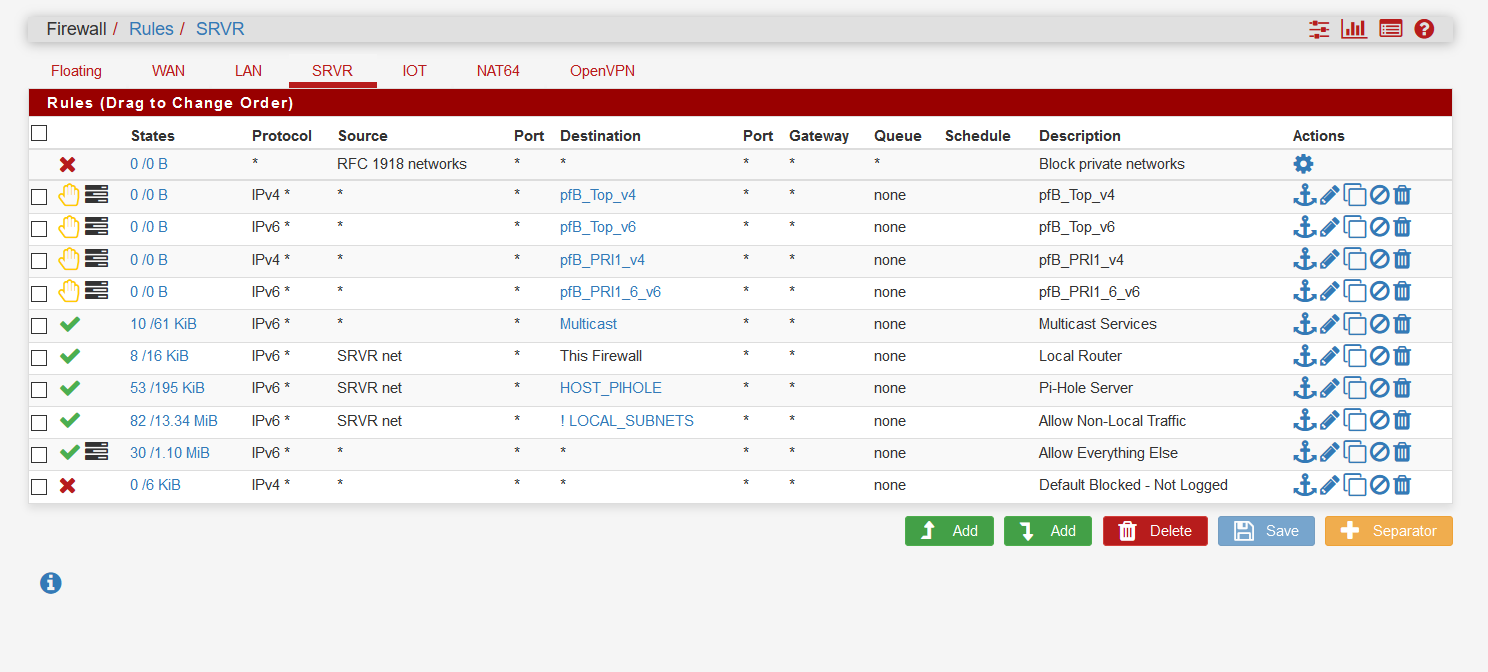
As you can see I have tried just blocking all ipv4 traffic with no logging but no luck.
Is there a setting I have overlooked?
I was thinking of submitting this to the bug tracker but would you consider this to be a feature request or a bug?
-
What is that source your using for rfc1918? Its not a alias? And shows no hits.
And from you log you have a rule called block IPv4 link-local blocking it - do you have something on the floating tab?
What version of pfsense is this?
edit:
Ah your hitting the hidden block link-local rule[2.4.4-RELEASE][admin@sg4860.local.lan]/root: pfctl -vvsr | grep link-local @3(1000000101) block drop in quick inet from 169.254.0.0/16 to any label "Block IPv4 link-local" @4(1000000102) block drop in quick inet from any to 169.254.0.0/16 label "Block IPv4 link-local"You can turn it off - see here.
https://redmine.pfsense.org/issues/2073Another option would be to just turn off logging of default blocking, and then just create rules that log what you want logged.. Prob better option in your case.
-
It is probably the case that I still want to have a rule to block the ipv4 link-local on the other interfaces that are dual stack.
I wonder why they didn't have this rule fire after the user defined rules? There must be a reason I am not seeing yet. We are told that everything on an interface is blocked unless a rule is written to pass.
I will try turning off logging of default blocking tonight, and see if that works.
Do you think I should open a feature request? It is probably acting as designed so not a bug?
-
Link local is not suppose to route so it should be blocked.. If you log default rules then you will see it when its blocked.
If you do not want to see it, turn off logging of default blocks. It really is that simple.
If you don't want to turn off default logging, then you would need to turn off the default block to not see it in the default block logs..
-
@johnpoz said in IPv6 only subnet. How to turn off logging blocked ipv4 link local?:
Link local is not suppose to route so it should be blocked.. If you log default rules then you will see it when its blocked.
If you do not want to see it, turn off logging of default blocks. It really is that simple.
If you don't want to turn off default logging, then you would need to turn off the default block to not see it in the default block logs..
I did confirm that turning off logging of default rules does turn it off. I will probably leave it on for now as it is just a test subnet.
-
But thought you said it was too noisy? Just leave it off, and put in the block rules you want that log.. For example in your block rule that you log source is your net, then noise like link-local which is not your network would not be blocked by that, and fall through to the default and be blocked, but not logged.
-
@johnpoz I like to be able to still see in the log items such as tcp:a that are captured by the default rule.
Right now the ip6 only subnet is a test for me. Everything else is dual stack.
As far as the noise it only becomes a real issue when it is the WiFi net being tested. iPhones use link local multicast constantly for bonjour.
-
Like I said turn off default logging and only log what you want... So you can set it up to block and log your tcp stuff, but not the multicast