One rule to rule them all, One policy to find them, One gateway to bring them all and in the darkness bind them
-
Hi,
I want to achieve this: An isolated VLAN(s) that can access only the Internet + having all the DNS requests sent to the pfSense box going through a VPN gateway.
Under a VLAN interface, I defined these rules:
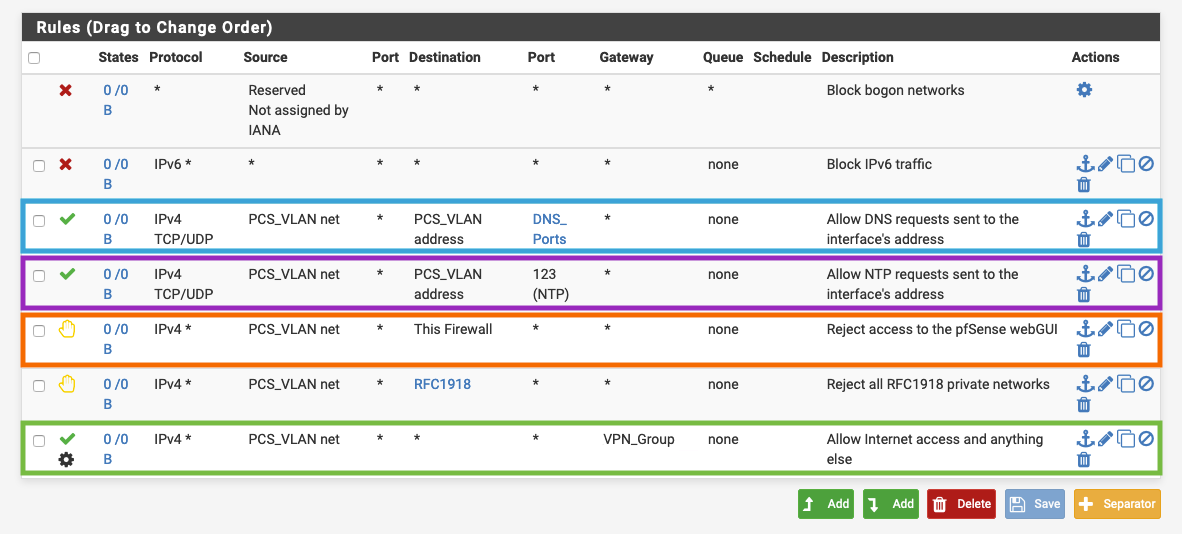
The BLUE rule will catch all the DNS (53, 853) requests made to the interface address.
The PURPLE rule will catch all the NTP requests made to the interface address.
The ORANGE rule will reject all the attempts to access the pfSense webGUI.
The GREEN rule will catch all the other traffic and pass it through the VPN group.Question 1: In order to pass all the DNS requests (to the interface address) through the VPN as well but without choosing the VPN as the default gateway, how should I achieve that? Would policy routing the BLUE rule work correctly allowing the DNS Resolver do its thing and change the interface address destination to whatever is defined under General Setup, or should I just use DoT, or even both - DoT and policy route?
Question 2: Can NTP requests be passed via a VPN gateway correctly with no issues, or would it get DateTime data that is relevant to the VPN server I'm connected to?
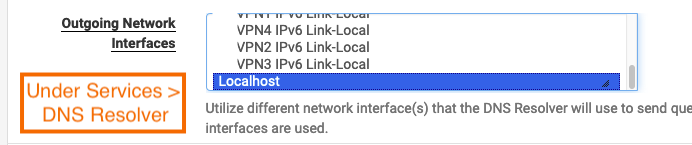
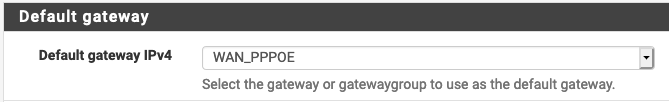
Question 3: If I set the WAN to be the default gateway (for proper pfSense functionality, VPN coming back after a reboot/shut down/failure etc.) and the DNS Resolver to use only Localhost as the Outgoing Network Interface and I'm policy routing DNS requests via the VPN gateway (with maybe NO_WAN_EGRESS), then DNS for this VLAN/Interface should never go through the WAN gateway, right?
Question 4: If instead of Localhost, the VPN will be used as the Outgoing Network Interface, would it affect the inner proper functionality of the pfSense box in case the VPN is down, or pfSense would still be able to resolve DNS/NTP for its own needs without needing the DNS resolver?
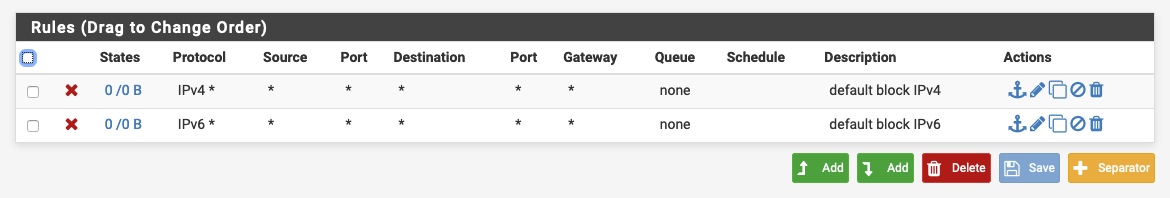
Question 5: In the screenshot above, these rules were added automatically after assigning a VPN interface, how does it work properly with IPv4* blocked? Seems weird to me...
Thank you, I'll appreciate any help.