Snort problem
-
Hi, can anyone help me with Snort's problem? The problem started when the Snorta package was last updated.
Since no correction has been made during this time, I wonder if anyone else has this problem. I myself have a problem at two locations.
Error:
PHP ERROR: Type: 1, File: /usr/local/pkg/snort/snort.inc, Line: 2478, Message: Allowed memory size of 402653184 bytes exhausted (tried to allocate 268435464 bytes) @ 2019-12-03 20:26:30The Rules update has finished. Generating snort.conf configuration file from saved settings. Generating configuration for WAN... PHP ERROR: Type: 1, File: /usr/local/pkg/snort/snort.inc, Line: 2478, Message: Allowed memory size of 402653184 bytes exhausted (tried to allocate 268435464 bytes)pkg-static: POST-INSTALL script failed ===== Message from python27-2.7.16_1: -- =========================================================================== Note that some standard Python modules are provided as separate ports as they require additional dependencies. They are available as: bsddb databases/py-bsddb gdbm databases/py-gdbm sqlite3 databases/py-sqlite3 tkinter x11-toolkits/py-tkinter =========================================================================== ===== Message from barnyard2-1.13_4: -- Read the notes in the barnyard2.conf file for how to configure /usr/local/etc/barnyard2.conf after installation. For addtional information see the Securixlive FAQ at http://www.securixlive.com/barnyard2/faq.php. In order to enable barnyard2 to start on boot, you must edit /etc/rc.conf with the appropriate flags, etc. See the FreeBSD Handbook for syntax: http://www.freebsd.org/doc/en_US.ISO8859-1/books/handbook/configtuning-rcng.html For the various options available, type % barnyard2 -h after install or read the options in the startup script - in /usr/local/etc/rc.d. Barnyard2 can process unified2 files from snort or suricata. It can also interact with snortsam firewall rules as well as the sguil-sensor. Those ports must be installed separately if you wish to use them. ===== Message from snort-2.9.15: -- Snort uses rcNG startup script and must be enabled via /etc/rc.conf Please see /usr/local/etc/rc.d/snort for list of available variables and their description. Configuration files are located in /usr/local/etc/snort directory. Please note that, by default, snort will truncate packets larger than the default snaplen of 15158 bytes. Additionally, LRO may cause issues with Stream5 target-based reassembly. It is recommended to disable LRO, if your card supports it. This can be done by appending '-lro' to your ifconfig_ line in rc.conf. ===== Message from pfSense-pkg-snort-4.0_10: -- Please visit Services - Snort - Interfaces tab first to add an interface, then select your desired rules packages at the Services - Snort - Global tab. Afterwards visit the Updates tab to download your configured rulesets. >>> Cleaning up cache... done. Success -
Hello, I am having a very similar issue what did you do to solve it?
-
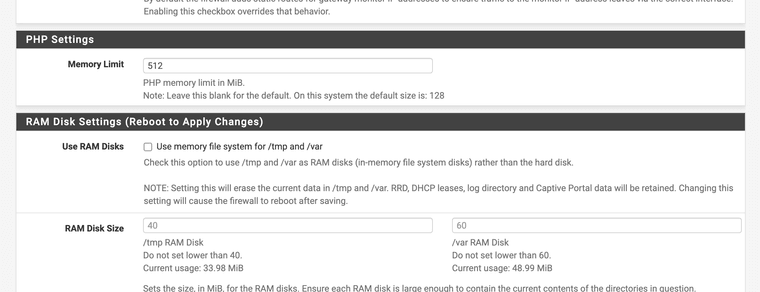
Have you tried to change your PHP limit in advanced configuration >??
Change it to a bigger value
-
I raised it to 2048 and I still have this error.
PHP ERROR: Type: 1, File: /usr/local/pkg/snort/snort.inc, Line: 1033, Message: Allowed memory size of 402653184 bytes exhausted (tried to allocate 54642640 bytes)pkg-static: POST-INSTALL script failed -
@PF_User can you disable some ips rules for a test or set it to balanced?? Or is this during the pkg install?
-
@JonathanLee First off thank you for taking the time to help me. I was using suricata and tonight I decided to switch to Snort. Unfortunately I have not even been able to start it. So I tried to re-install and that is the error at installation. I will disable a bunch of rules now. That is probably the problem.
-
@JonathanLee I can't even access that anymore because it fails on re-install. I guess I need to delete all data and try again.
-
@PF_User what version of pfSense are you on?
-
This post is deleted! -
@JonathanLee I am running 2.7.2-RELEASE and everything is the latest.