Communicate with root servers via VPN and/or DoT
-
Hello,
I've started using pfSense as a "pure DNS resolver", without any external DNS servers defined under General Settings and without forwarding mode, but I'm not sure how to encrypt the requests.
I have the default LAN to any rule and I route it via a VPN gateway.
DNS Resolver > Outgoing Network Interfaces is set to "Localhost".
From what I understand from previous questioned I've posted here in this forum - a resolver won't be resolving when DoT is in use, only if forwarded.
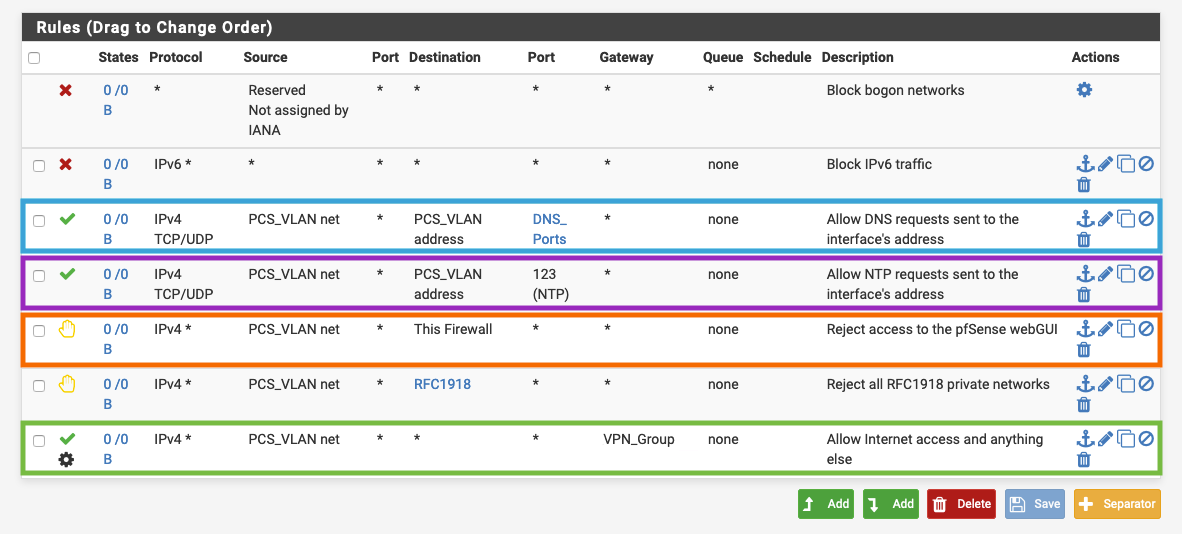
So my question is this: How do I both use pfSense as a resolver AND encrypt its communication with the root/tld/ns servers? If the default LAN to any rule that's being policy routed via the VPN gateway will also policy route the DNS requests to the root servers just like the rest of the traffic coming from the LAN, then I'd like to know how to achieve the same for an isolated VLAN with these rules below (ignore the useless bogon rule lol):
-
@techtester-m said in Communicate with root servers via VPN and/or DoT:
AND encrypt its communication with the root/tld/ns servers?
You can not do this... They do not support dot... You can encrypt your traffic through your vpn, which is only to the endpoint of the vpn service over your ISP.. Once it leaves the vpn service its not encrypted.
The only way to do encrypted traffic to whatever ns your using is forwarding... if your going to resolve the best you an do is encrypt the traffic from pfsense to your vpn end point..
-
@johnpoz said in Communicate with root servers via VPN and/or DoT:
Once it leaves the vpn service its not encrypted
I know...that's the same for every other traffic, since the VPN has to decrypt it in order for the data to be usable by the service your trying to use. That's a given.
@johnpoz said in Communicate with root servers via VPN and/or DoT:
if your going to resolve the best you an do is encrypt the traffic from pfsense to your vpn end point
Well...that's my question for the last 10 hours, but I'm trying to understand how the resolver act behind the scenes.
In the VLAN case above (screenshot) would policy routing the DNS Pass rule do the job and force the resolver to talk to the root servers via the VPN? If not then how the hell do I do that lol...sorry, I just wanna finish with that and move on with bulding the entire network. -
No unbound doesn't use any of the rules you have on any interfaces - we already went over this... If you want unbound to use your vpn, then set its outbound interface in the outbound config to be your vpn interface... Its not going to do anything with policy routing you put on any interface..
But your going to have issues with unbound starting if your vpn is not up, etc.
As already stated if you want route all traffic through your vpn for dns, then run dns on your network and policy route it like you would do with any other client.
Your going through a lot of effort to keep your ISP from knowing you went to freaking amazon.com ;) I really do not get the mind set here... So you vpn it, now all your doing is handing that info to your vpn service.. And you slowed down your connection to boot, and cost yourself more money - to hide your dns queries from a company you pay to provide you internet in the first place.
If I wanted to hide my dns from my isp, I would just setup dot/doh/dnscrypt/vpn on one of my vps boxes, and then forward to it via dot or doh, vpn, etc.. to it..
-
@johnpoz said in Communicate with root servers via VPN and/or DoT:
No unbound doesn't use any of the rules you have on any interfaces - we already went over this
I remember but then got confused by a different answer...never mind. Got it!
@johnpoz said in Communicate with root servers via VPN and/or DoT:
Your going through a effort to keep your ISP from knowing you want to freaking amazon.com ;)
I understand what you're saying but:
(1) That's not just for me. (2) I'm testing and learning and won't necessarily use it in the future...maybe for other setups.@johnpoz said in Communicate with root servers via VPN and/or DoT:
I really do not get the mind set here... So you vpn it, now all your doing is handing that info to your vpn service
You won't understand because you've probably never heard/seen an ISP give out information like a whore opening her legs...I've served in the intelligence force and seen and heard some disturbing stuff. Regardless...I can get OCD/Perfectionist/Paranoid when it comes to security. But never mind...let's get past that lol.
@johnpoz said in Communicate with root servers via VPN and/or DoT:
now all your doing is handing that info to your vpn service
Rather them than your local ISP. Your business is basically immune to state officials asking your ISP to give them your info or your clients' etc. NordVPN is listed in Panama. Good luck to the state officials lol.
@johnpoz said in Communicate with root servers via VPN and/or DoT:
If I wanted to hide my dns from my isp, I would just setup dot/doh/dnscrypt/vpn on one of my vps boxes
I imagine the vps boxes cost money too...
I really appreciate all your help and don't want to waste your time so....Conclusion: In order to encrypt the DNS traffic of a resolver, one should do one of these:
- Use forwarding mode to external DNS server + DoT
- Use a resolver that's inside the network - that would be either physical device or a virtual machine etc., right?
- Use a vps box as your own VPN service.
- Set the VPN interface(s) as the DNS Resolver > Outgoing Network Interfaces. NOTE: May cause some reboot/initialization problems when VPN is down etc.
Conclusion correct?