What is proper way to add P2 routes for additional networks?
-
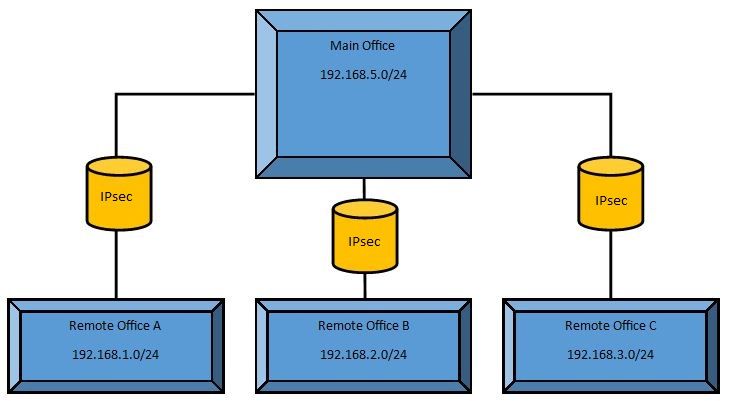
Maybe this is a fault in my base config or I'm just not getting the right grasp on the P2 routing in regular IPSec tunnel mode. Reference the image below. I'm testing VPN connections between a few locations and they are working great. All remote locations can access the main site and share network resources. The main site can also access all remote locations and share resources. The issue I'm trying to figure out is how to get the remote sites to be able to see each other directly.
Basically browse the IP of a printer or device in Office B or C from Office A.
Is this a functional scenario using additional P2 entries or is this something that requires a VTI type setup with manual routing entries. If this is possible with P2 entries, what is the proper entry format to add the additional remote lan segment? Or does it need another P1 between each remote location to create a full ring?
Thank you for your help. Always trying to learn new stuff.
-
It can work in any of the scenarios you describe. If you want the traffic to go through the main office from A to B, for example, it can do that in regular tunnel mode. You need the right P2s on every leg, though.
For example:
Main Office - Office A
P2: Main<->A
P2: B<->A
P2: C<->AOffice A - Main Office
P2: A<->Main
P2: A<->B
P2: A<->CMain Office - Office B
P2: Main<->B
P2: A<->B
P2: C<->BOffice B - Main Office
P2: B<->Main
P2: B<->A
P2: B<->CMain Office - Office C
P2: Main<->C
P2: A<->C
P2: B<->COffice C - Main Office
P2: C<->Main
P2: C<->A
P2: C<->B -
@jimp Thank you. Perfect explanation and I think you may have solved my issue. I was not doing the P2 segments at the hub correctly. I didn't have any P2 entries with links between remote offices. I kept trying to create them with the hub as the distribution point.