no EAP key found for hosts RADIUS config for Mobile Ipsec VPN
-
Hi all... following my success at getting an ipsec vpn configured... I figured it would be good to get the connection to authenticate with our NPS server.
I've verified that my PfSense can authenticate with the NPS server by using the diagnostics, authentication option, so far so good.I change the mobile clients section to use the RADIUS server I've setup and try to connect my VPN client. This fails with a "the user name or password is incorrect"... checking the log it states the following;
09[IKE] <con1|11> no EAP key found for hosts
Checking the NPS server the PFSense doesn't even seem to be asking the question of it since there's nothing logged.
any ideas anyone?
-
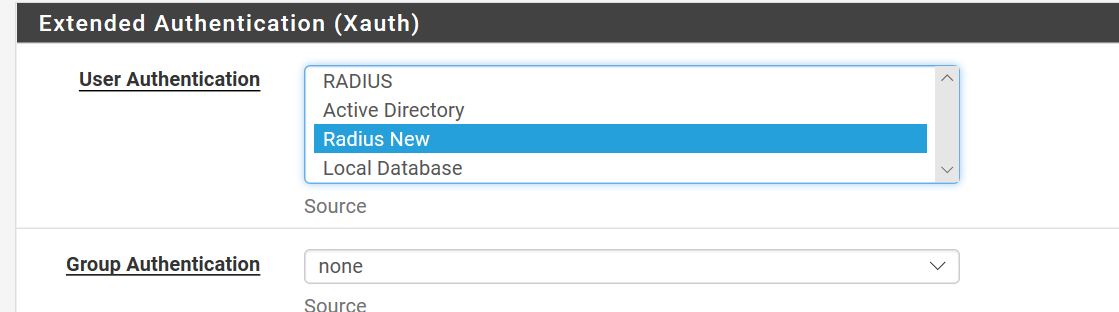
@cre8toruk Just to add a little to this... and to reiterate, my mobile clients section is set to use my Radius server
However if I try and use a valid AD login I get the above... If I use my prepared shared secret I get a connection...Clearly the issue is between the client and the PFSense settings but I'm struggling to see where. -
Double check your NPS configuration against the suggestions in the docs at https://docs.netgate.com/pfsense/en/latest/book/thirdparty/radius-authentication-with-windows-server.html
Specifically, this part.
-
@jimp Hi... yes I checked it anyway but the FW isn't hitting the RADIUS as I'm not seeing any events logged on the NPS server (failures or otherwise), this seems to be an initial connection issue.... as I say, if I supply the shared secret credentials to the client I get a connection...
-
This post is deleted! -
ok turns out that I need to change the auth method in phase 1 to EAP-RADIUS which I've now done.
I'm now getting "The remote connection was denied because the username and password combination you provided is not recognized, or the selected authentication protocol is not permitted on the remote access server".... Progress of sorts but not quite what I was looking for....
FW log states ;
08[IKE] <con1|28> loading EAP_RADIUS method failed -
ok a bit more on this... after reading somewhere about stopping and restarting the service (due to some bug) I did this... I have the same error on the client however the logs now say;
RADIUS Access-Request timed out after 4 attempts
-
new update: So increased the time out value on the RADIUS to 30 seconds.
I note now in the NPS log I get another error :-( "An Access-Request message was received from RADIUS client <<my pfsense>> with a message-Authenticator attribute that is not valid.Research points to this being a problem with the shared secret, so I reconfigured this to be the same on both the NPS Radius client setting for the pfsense and updated it on the pfsense, though logic tells me that if this can authenticate on diagnostics authentication, then it's not likely to be the issue....
-
PHEW ! Well that was emotional... ok so all working now. Basically I had to stop the IPSEC service (and I mean STOP not restart)… wait a few seconds and then start it again and now it all connects just fine....