How to prevent users from LAN to know the external local WAN IP ?
-
@viragomann said in How to prevent users from LAN to know the external local WAN IP ?:
@Sergei_Shablovsky
That's by desing of TCP. Each packet a client sends to a server carrys the source and the destination address in its header. When your router send the packet out to the internet, it replaces the source address by its own WAN IP.
Otherwise a respond packet won't come back to the router.
So a destination server ever knows where a packet comes from.Thank You for answer!
I know this, but I try to find way to limit ability to determine local WAN IPs from inside LAN. For example even LAN user able to determine upstream ISPs router IP instead of our WAN IP - that would be great.
-
@Sergei_Shablovsky said in How to prevent users from LAN to know the external local WAN IP ?:
For example even LAN user able to determine upstream ISPs router IP instead of our WAN IP - that would be great.
You'd have to block traceroute to do that. But why do you consider the ISPs router to be an issue?
-
Send all your traffic over a tunnel to some IP you don't mind them finding. That's pretty much the only thing you can do.
Steve
-
@Sergei_Shablovsky said in How to prevent users from LAN to know the external local WAN IP ?:
I understand correctly that this is because of all ISPs broadcasting their structure (I mean OSPF, BGP, etc protocols) to keep connectivity better ?
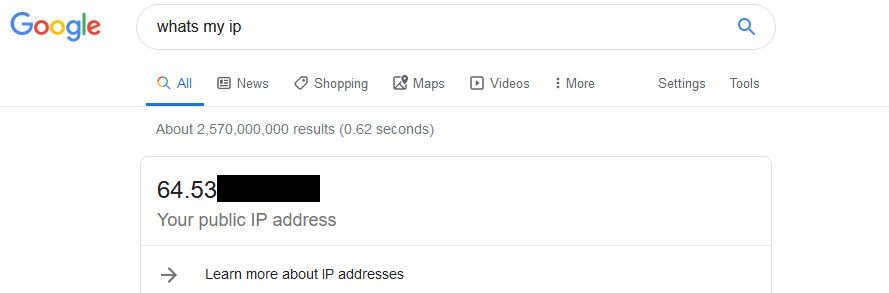
Huh?? No that has nothing to do with finding out IP your talking to a site from... Just google whats my IP, there are hundreds if not thousands of sites that will tell you what IP you talked to them from...
If your allowing access to the internet there is NO way to hide the IP your talking to the internet from... Just not possible!!! You could block traceroute, udp ports and icmp to stop someone from find the intermediate hops along the way, ie the isp gateway right after you router for example... But they would still be able to find the IP they are talking from by going to any of a 1000's different websites.. No possible way to block them all - also user could just hit any website/ip at all that they have access to the logs on to see the IP.
How exactly do you hide this for example - just a simple google, you going to block access to google?
Stephenw10 had the really only way you could attempt to hide it - by tunneling all traffic to some site your ok with them knowing the IP of, say a vpn - this way if they went to some site like whatsmyip - it would show that vpn endpoint IP and not your actual public IP.
What is the point of trying to hide your public IP from users of your network?? I am not understanding the use case here to be honest.
-
@johnpoz said in How to prevent users from LAN to know the external local WAN IP ?:
What is the point of trying to hide your public IP from users of your network?? I am not understanding the use case here to be honest.
+1
Add me to that query.. :) sometimes you have to choose your battles..
-
@JKnott said in How to prevent users from LAN to know the external local WAN IP ?:
@Sergei_Shablovsky said in How to prevent users from LAN to know the external local WAN IP ?:
For example even LAN user able to determine upstream ISPs router IP instead of our WAN IP - that would be great.
You'd have to block traceroute to do that. But why do you consider the ISPs router to be an issue?
I try to eliminate security hole:
- minimize ability to determine main gate entry IPs from outside attackers;
- minimize ability to determine main gate entry IPs from inside office lan (office secured WiFi, office open WiFi);
Of course outside attackers may try to obtain access to ISPs infrastructure (client database leaks, phishing emails, etc.) or (most used way nowadays) by social engineering (phishing emails, SMS, Twitter/Messanger/Telegram for stuff with exploit links, etc).
And earlier or sooner, the attacker get the main gate IPs.
But anyway, time is money, and any wall behind the attacker goal - are good.
Regarding Your question: if attacker DDoS-ing the ISP upstream appliance - this is ISPs security job and attack may be eliminate on ISPs level more effectively than on our main gate applience, agree?
-
@stephenw10 said in How to prevent users from LAN to know the external local WAN IP ?:
Send all your traffic over a tunnel to some IP you don't mind them finding. That's pretty much the only thing you can do.
Steve
Thank You Steve!I know about this ability but because keeping tunnel mean extra loading for hardware and lowering the overall bandwidth - I wrote to forum trying to find another way :)
-
@Sergei_Shablovsky said in How to prevent users from LAN to know the external local WAN IP ?:
I try to eliminate security hole:
minimize ability to determine main gate entry IPs from outside attackers;
minimize ability to determine main gate entry IPs from inside office lan (office secured WiFi, office open WiFi);Of course outside attackers may try to obtain access to ISPs infrastructure (client database leaks, phishing emails, etc.) or (most used way nowadays) by social engineering (phishing emails, SMS, Twitter/Messanger/Telegram for stuff with exploit links, etc).
Better put your tin foil hat on. You have nothing to worry about in that respect. It's the ISPs responsibility to protect their network. Hiding it from your users will accomplish nothing.
-
@johnpoz said in How to prevent users from LAN to know the external local WAN IP ?:
What is the point of trying to hide your public IP from users of your network?? I am not understanding the use case here to be honest.
Thank You John for kindly reply and efforts to understanding my needs!
Primary the topic mean hiding (or making very sophisticated to determine) from attacker external IPs of main gate from both side external and internal from doing the most used types of attacks like DDoS, DNS amplification, etc.
For example Incoming RST-packets detecting to prevent DNS-amplification/Malicious Activity Abuse attacks.
How You work with this type of attack?When You keep all Your business/services in a cloud, - this not an issue because cloud SaaS provider (Amazon, DigitalOcean, Google, Akamai, etc...) doing all protection job for You. Just pay the price. Thousands of $USD.
But anyway you need to extra alarm work during attack to reconfigure infrastructure.But here we all have pfSense as software installed on real hardware, more or less powerful. And we all are obligation to keep all services working well 24/7/365.
So due this we need to take all possible efforts to prevent attacks and secure our clients as much as possible.
For example, the cost of DDoS-ing nowadays are from $20 / hour to $2-5k / hour depend on type of attack. And how much Your client lost for 1 hour of all its services (public we, warehouse databases, emails, survival equipment, climate control, power control,...) are down?
Now there are no any solution from DDoS attacks rather than switch to failover uplink. If You have it already, of course.Thinking this manner about hospitals, medicine clinics with a lot of blood pumps, heart support devices....
Most of users here on forum are quite away from this so-called “enterprise” questions. But only due the moment that really happened with them!
If 70% of ordinary users on this forum not thinking about things like DNS amplification not mean this attack not exist at all.
P.S. Example: Easy way to create attack vector by create gmail address -> register on this forum,-> look at this tread https://forum.netgate.com/topic/51312/show-your-pfsenses-thread-bandwidth-warning -> determine the real users with most explained hardware/software setup -> find in LinkedIn, FB company where this person work -> try to go inside and dump some sensitive databases -> obtain real IPs of entry -> prepare DDoS attack -> send email with proposition to pay by crypto -> make DDoS if payment not make.
$2,000-10,000 USD is not a big amount for business, compare to 3-7 days of all it’s online-oriented services are down and profit lost due this.
I think this criminal way is easy for understanding even someone are student in tech college. It’s reality. And no one ISP protect You against this, just switch off on a time of attack.Another one example: forum user not only show his wan IPs, but pfSense Device ID and much more https://forum.netgate.com/topic/139433/resolved-pfsense-hangs-when-wan-is-unstable-or-lost
This is only one example how people not care about security. And I really not understand why doing this.
-
@JKnott said in How to prevent users from LAN to know the external local WAN IP ?:
@Sergei_Shablovsky said in How to prevent users from LAN to know the external local WAN IP ?:
I try to eliminate security hole:
minimize ability to determine main gate entry IPs from outside attackers;
minimize ability to determine main gate entry IPs from inside office lan (office secured WiFi, office open WiFi);Of course outside attackers may try to obtain access to ISPs infrastructure (client database leaks, phishing emails, etc.) or (most used way nowadays) by social engineering (phishing emails, SMS, Twitter/Messanger/Telegram for stuff with exploit links, etc).
Better put your tin foil hat on.
Nice suggestion. :) But better to be serious in this case.
You have nothing to worry about in that respect. It's the ISPs responsibility to protect their network. Hiding it from your users will accomplish nothing.
May be You newer going under attacks: only one thing that 99% of local ISP in any country doing - is just send You abuse email and after 30min-2h of channel to upstream appliance are overhead -> blackholing all requests to Your IPs.
You may only sitting and waiting....
And after a You never receive money compensation for “losing profit because service not given to a You from ISP side” and pay a lot for lawyers to proofing the issue.
Live in reality :) Only a huge business able to win law battles. Other businesses may resolve security / attacks issues themselves.
So better to focus on topic, ok, transform it to “”How to make impossible of sophisticated to know real main gate IPs from inside office lan”
That's ok ok foil hat still needed? ;) -
On WAN block all incoming traffic.
On LAN block all outgoing traffic.Set up a proxy server and install certificates on all you clients.
Chose an ISP that offers a proxy server.
Point your Proxy server to the ISP's upstream Proxy.
Alternative:
Purchase a VPS somewhere. Built a tunnel to that VPS and send all the internet traffic through the tunnel.If your security needs are really that strict spending a few $$$ on a VPS shouldn't break the bank...
-
Sorry dude you can not HIDE your public IP from your users...Without tunnel them to some other endpoint
It is not possible..As stated already if you let them talk from it to the internet - then there a bajillion ways.
But sounds like your wanting to hide your IP from where you go to... This is the case then use proxy/vpn... If you don't want pfsense.org knowing your IP, then that is vpn or proxy. But can promise you users will have issues with being blocked... Many sites block such access - especially forums.. Because people hiding their IPs are normally spammers!
If your concerned with ddos mitigation, then use a service that provides it.. Every major ISP provides this service - at a COST!! Or get your own IPs, and use a service that can route your traffic through them... At work we use these guys
https://www.netscout.com/arbor-ddos
If an attack is detected against any our public IP space, we can reroute that network through their network before it gets to us, they mitigate the attack traffic. It ain't cheap ;)
Your only possible solution is vpn.. Be it you use a service or roll your own. This hides IP from your own users, it also hides your IP from destination.. But it comes with its own issues. This is the only ma an pa type shop sort of solution.
-
@gcu_greyarea said in How to prevent users from LAN to know the external local WAN IP ?:
On WAN block all incoming traffic.
On LAN block all outgoing traffic.Set up a proxy server and install certificates on all you clients.
Chose an ISP that offers a proxy server.
Point your Proxy server to the ISP's upstream Proxy.
Alternative:
Purchase a VPS somewhere. Built a tunnel to that VPS and send all the internet traffic through the tunnel.If your security needs are really that strict spending a few $$$ on a VPS shouldn't break the bank...
Ok. I just try to find another way, let’s say, I open to learn ;)
ISP here are not stable due a couple of reasons, so VPS or even collocation - great way.
Thank You for efforts! ;)
-
@johnpoz said in How to prevent users from LAN to know the external local WAN IP ?:
then there a bajillion ways
I thought it was closer to a gazillion.

-
Yeah, if you allow users behind the firewall to connect out then they can trivially find the IP they are connecting from.
The only thing you can do is change that IP to something else using a tunnel or proxy.
Steve
-
@johnpoz said in How to prevent users from LAN to know the external local WAN IP ?:
Sorry dude you can not HIDE your public IP from your users...Without tunnel them to some other endpoint
It is not possible..As stated already if you let them talk from it to the internet - then there a bajillion ways.
I understand that but asking here, because hope that someone suggest me another way, than VDS/VPS. :)
I open to learn.But sounds like your wanting to hide your IP from where you go to... This is the case then use proxy/vpn... If you don't want pfsense.org knowing your IP, then that is vpn or proxy. But can promise you users will have issues with being blocked... Many sites block such access - especially forums.. Because people hiding their IPs are normally spammers!
I know that. Last 2-3 years a lot of people start to care about privacy much more and start blocking cookie, pop ups, js, using anonymizes, VPN services, etc. But this impact on websites coding, frontend of services coding,... forums...
For example a lot of journalists (even in US, not only in small countries in 3rd world) need to hide their IPs, security and forensic pro, etc...
New world become with a new types of attacks and a new type of defense.If your concerned with ddos mitigation, then use a service that provides it.. Every major ISP provides this service - at a COST!! Or get your own IPs, and use a service that can route your traffic through them... At work we use these guys
https://www.netscout.com/arbor-ddos
Thank You for kindly suggestion!
I repeat another one time: technically not possible to against the DDoS attack on Your IPs, only pull Eth jack off ;)
No one ordinary local ISP able to against 10G - 20G traffic come to Your Eth port.Because of this CloudFlare exist. But CloudFlare (or any other company, Amazon, DigitalOcean,...) only able to protect You if DDoS point on Your FQDN.
But if attack pointed on Your real main gate IPs - You would have only one way: sitting and smoking great cigars from Cuba. ;)If an attack is detected against any our public IP space, we can reroute that network through their network before it gets to us, they mitigate the attack traffic. It ain't cheap ;)
This work only attack point on FQDN, but if attack pointed on Your real main gate IPs - nothing to do with this :)
Your only possible solution is vpn.. Be it you use a service or roll your own. This hides IP from your own users, it also hides your IP from destination.. But it comes with its own issues. This is the only ma an pa type shop sort of solution.
Thank You for time and efforts to understanding my point.
As we see, VPS/VDS on a very fast fiber-connected DC able to mask/hide real IPs of main gate...
Thank You all !!!
-
@Sergei_Shablovsky said in How to prevent users from LAN to know the external local WAN IP ?:
This work only attack point on FQDN, but if attack pointed on Your real main gate IPs - nothing to do with this :)
Huh? Has zero to do with what fqdn might point to an IP.. We advertise what networks are used, the actual route is changed for network 6.15.0.0/16 as an example.
We have multiple networks routed to our connections in our DCs - multiple customers using different networks, /24s for example.. These routes are advertised via bgp to the internet...
So no dns record pointing to an IP has zero to do with the mitigation of such volumetric ddos attack.
I suggest you take a look at how such a service I linked to works.
But no such services don't work for small ma and pop setups where the ISP gives you IP address X to work with..
You trying to hide your IP is not a security anything - security through obscurity doesn't fix the actual problem.. Its trying to hide your head in the sand hoping the bad guy doesn't find you.
-
Yeah, that^. Works great in that sort of situation... if you are willing to pay for it.
Not really possible for 5 static IPs at your office though. Only the ISP can do anything there.
See my earlier 'use a tunnel' comment.

Steve
-
^ exactly... The only solution to "hide" for a ma and pop setup is vpn service or proxy... But that doesn't actually fix the problem... Its just trying to hide.. If they get your IP, they still can ddos you...
This is why you need to work with your ISP when your such a small fish.
-
There are advantages to dynamic IPs. Not many but this is one.