Cant route to bridged external IP's. All other users can. Just not my internal LAN
-
Some small problem I am sure....
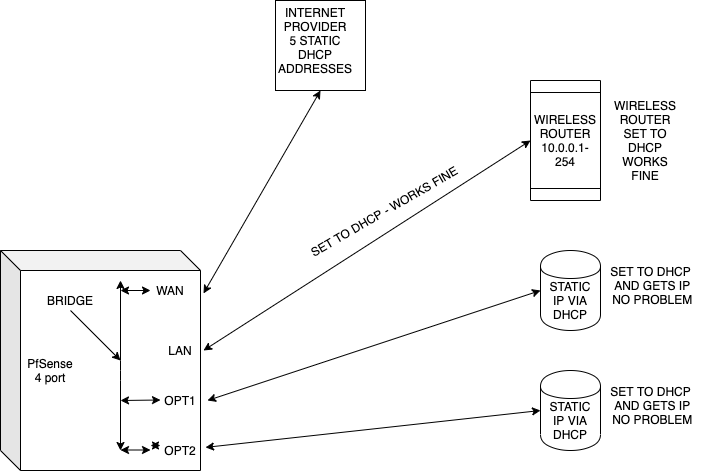
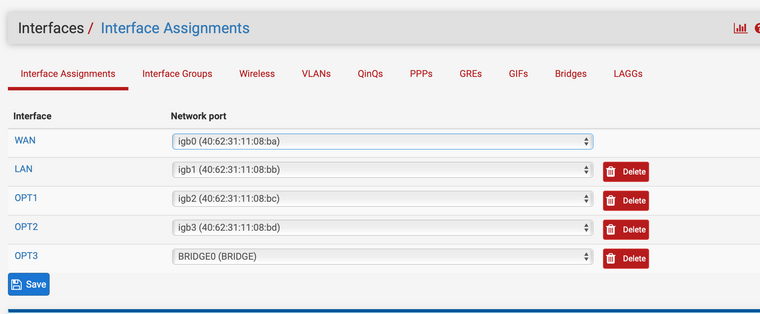
I have a 4 port PfSense. WAN with LAN connected and all working fine.
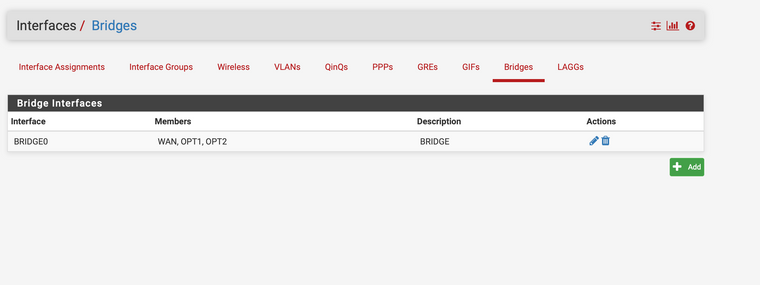
I also have a bridge with WAN and OPT1 and OPT2 (makes and OPT3 BRIDGE)
From the LAN network (private 192 addresses) I can get anywhere on the net, but not my bridged public IP's.
Other external users can get to the bridged IP's (http, ping etc.. ). Just my LAN cannot. But I can get anywhere else on the internet.... Strange.
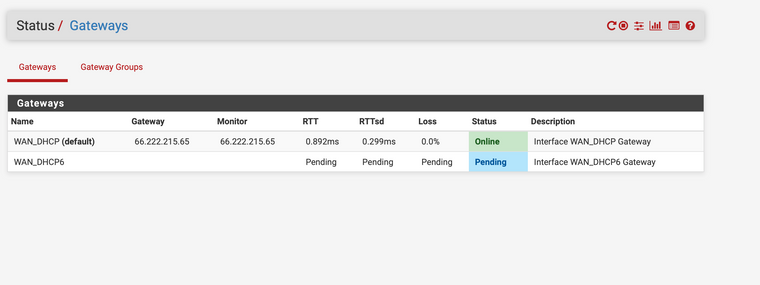
When I trace route to one of the bridge public IP's it stops at the WAN gateway and stops:
1 10.0.0.1 (10.0.0.1) 7.615 ms 2.382 ms 1.261 ms
2 192.168.0.1 (192.168.0.1) 1.388 ms 1.334 ms 1.251 ms
3 66.222.215.65 (66.222.215.65) 1.841 ms 48.825 ms 2.866 ms
4 * * *
5 * * *
6 *^C.65 is the WAN gateway.
Is this a routing problem perhaps?
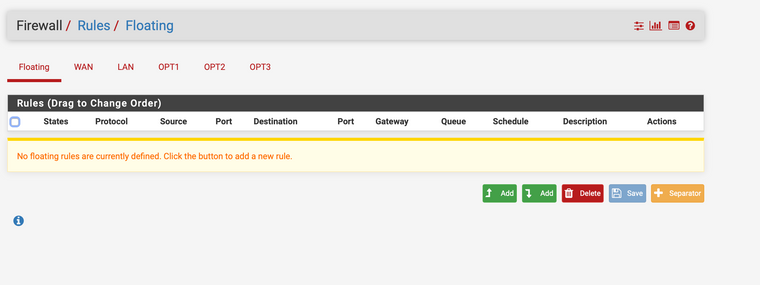
Any ideas on how to fix this are very welcome. I dont have any firewall rules in place that would prevent this.
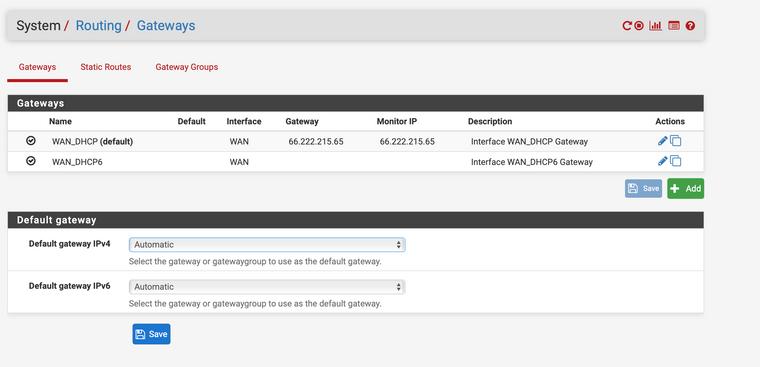
Seems like a WAN gateway issue, but only for the 2 IP's I have bridged (they are public IP's).Thanks!
-
If those other IPs are in the WAN subnet it should go directly and not hit the gateway.
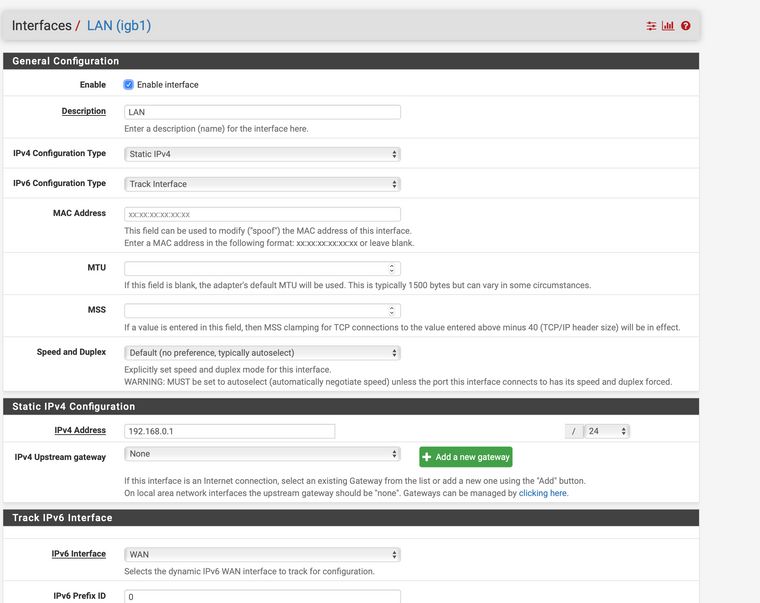
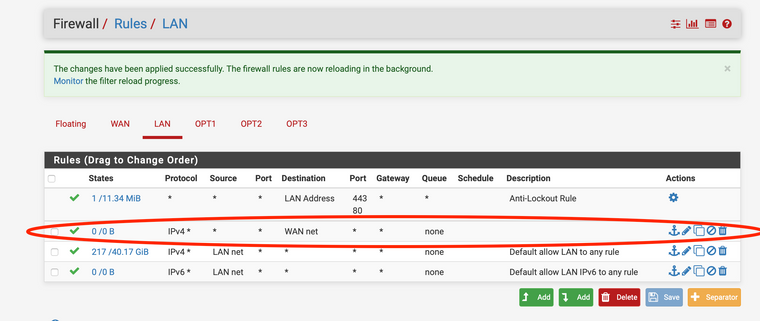
One reason it might not do that is if you are policy routing traffic from the LAN to the gateway.
If so you would need another pass rule on LAN above the policy routing rule to just the WAN subnet.Steve
-
Sorry, can you dumb it down a little. I dont really understand what you are saying.
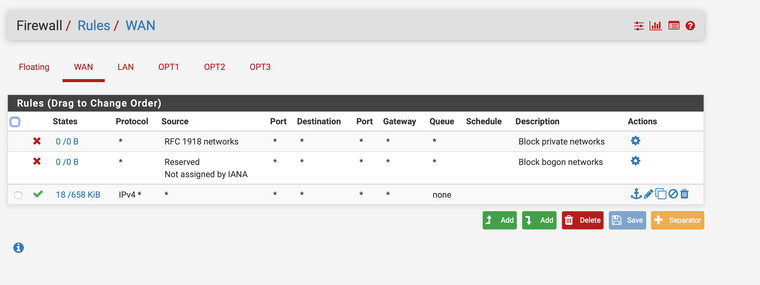
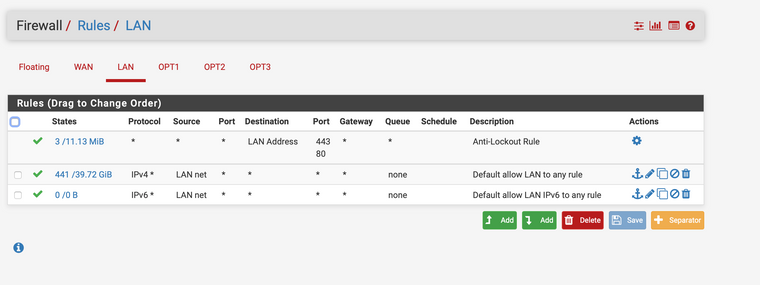
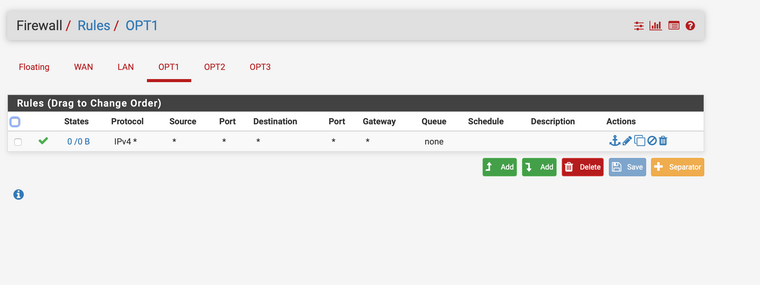
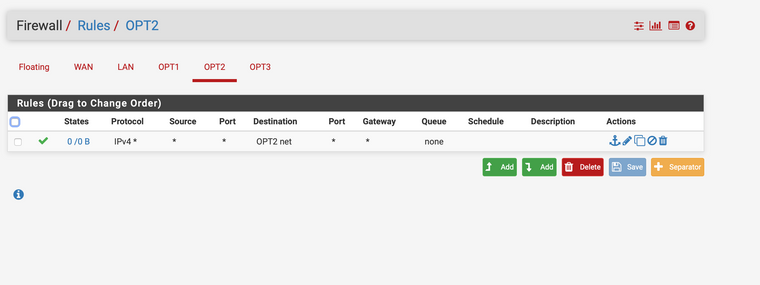
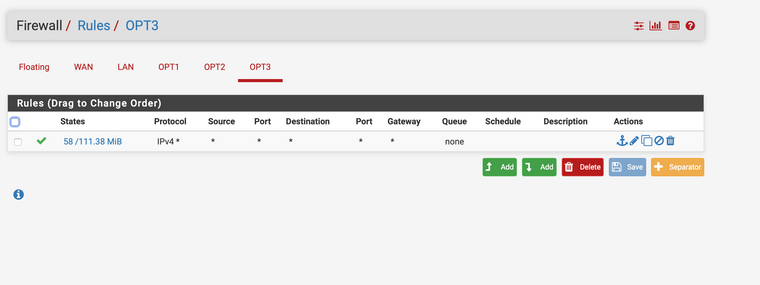
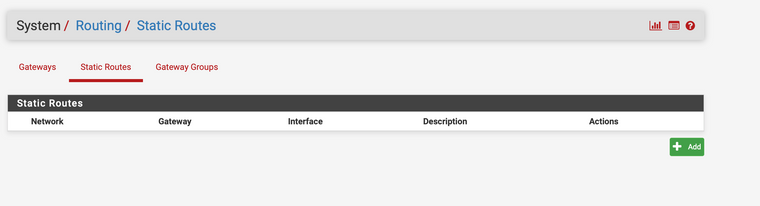
I am going to include some screenshots to help and maybe you can tell me what you mean?The really weird part is that every other external web site I go to is fine. Its just the two servers I have behind the bridge are not available to me. Everyone else on the net is fine accessing them. Just those two IP's I cant get at from my LAN. Maybe you can spot the problem then.
Sorry for all the screenshots. Hoping they help!
Thanks for replying and helping!
-
I added this rule, but cant drag it above the anti-lockout rule.
Is this what you were thinking?Screenshot attached of what I added.
-
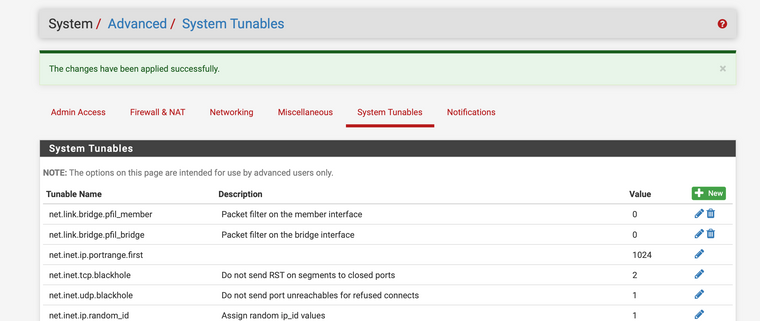
This seemed to fix it. Have I opened up any security problems with making member and bridge 0?
Will I still be able to change firewall for OPT1 and OPT2?
Or have I opened a security hole?
Info welcome on what I have done to get this working......
Thanks
-
Ok, you don't have a gateway set on the LAN rules so you are not policy routing.
In which case you should be able to connect to those IPs directly as long as they are in the same subnet as your WAN. Are they?
Can you ping them from pfSense in Diag > Ping?
You have filtering disabled on both the bridge members and the bridge itself. That's not normally how it would be configured, most people want to filter the traffic to the hosts in the DMZ.
Steve