Bug? - Different PSK per tunnel results in other IPSec tunnels to become unavailable.
-
I have 6 or 7 IPSec VPN Tunnels to different sites, all of them share the same PSK (don't ask me why). If I add another tunnel using a different PSK, restart IPSec, then all of the other connections fail. The log says something about possible preshared key mismatch for those in question. So I changed the PSK on my new tunnel and then BAM! they all start connecting again.
Is this a bug? Am I doing something wrong? Is there a work around if this is a bug?
Please assist!
-
Does the new tunnel share a remote peer address or remote identifier with any of the others? Usually something like that happens because strongSwan can't match up the remote ID+PSK combination properly. If there is an overlap, that would explain the confusion.
-
@jimp Nothing is shared. Its all very unique everything.
-
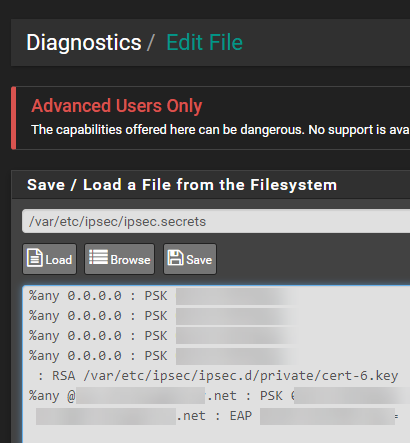
Check the logs and compare against what pfSense has in
/var/etc/ipsec/ipsec.secrets-- that would be how it looks up the PSKs -
This post is deleted! -
@jimp said in Bug? - Different PSK per tunnel results in other IPSec tunnels to become unavailable.:
/var/etc/ipsec/ipsec.secrets
Not sure what I am looking at here, but it seems like it should all be OK right?
-
You should have one entry in there for each tunnel. Why are there so many with
0.0.0.0? -
@jimp I do have 4 of them that are using distinguished names of 0.0.0.0 for both sides.
-
No wonder it's broken. Every tunnel should be using a unique set of identifiers. Otherwise nothing can be distinguished from each other.