Port forward through another pfSense
-
Hi,
I have a server, which is running proxmox as a hypervisor and a pfsense vm (pfsense A). I have a /29 public subnet which is routet to my main ip.
Additionally, I have a server which is located at a private household, so with a daily switching public ip.
My goal is to archive getting the traffic to and from a public ip on the second server.
On the second server is also running a proxmox and a pfsense vm (pfSense B)I have established a OpenVPN tunnel between both hosts, pfsense A is the server, and B acts as the client.
My goal is now to forward all traffic from a virtual ip on pfsense A to pfsense B, so pfsense B can act like it has a public ip and can port forward to its local hosts.
Is this setup somehow possible?
-
Yes, you should be able to port forward to the OpenVPN IP on the pfSense B from pfSense A. No different to how you would forward to local host behind A.
The OpenVPN client at B will need to be assigned as an interface so it gets a gateway etc in order that states are tagged 'reply-to'. Otherwise it will send replies out of it's WAN directly which will obviously fail.Steve
-
Is it possible to forward the completly portrange from 1-65535 to pfsense B to manage the portforwards to hosts connected to pfsense B only from pfsense B itself? Is this possible through a 1:1 NAT or through Portforwarding?
-
You could do either. 1:1 NAT is probably more appropriate from a public IP not used for anything else.
-
Ok, so I've setup a 1:1 NAT, but I'm not able to establish a connection to the pfsenseB through pfsenseA anymore.
Have I done something wrong?
pfSense A Rules
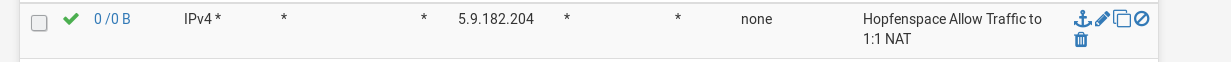
pfSense A 1:1

pfSense B Rules
The OPENVPNTOOMIKRON is the interface I have assigned to the OpenVPN client.
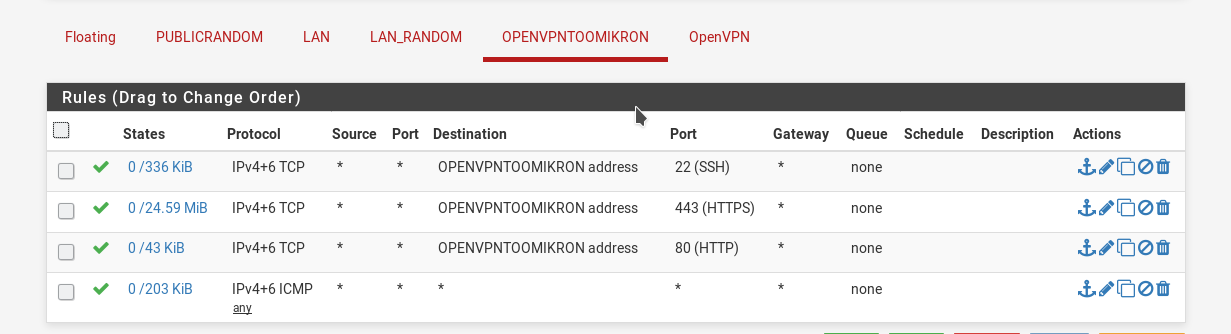
The OpenVPN tunnel has been established. I have the IP 10.100.100.1 on pfsense A and 10.100.100.2 on pfsense B.
I am able to ping between those addresses. -
Your firewall rule on pfSense A should be destination 10.100.100.2.
Incoming traffic hits the 1:1 rule and then the firewall rules.
Steve
-
Ah okay, that was the issue. Now I'm able to make port forwards on IPv4.
What would be the procedure for IPv6? I have a /64 Subnet for the hole pfsense A environment. (So I cannot use the hole subnet for pfsense B)
-
Indeed you cannot use a /64 for that. If you can pull a larger prefix from your provider you could potentially use a /64 from that at site B and route it over the VPN.
Steve
-
Okay so 2 last questions:
- I assume, I can't split up the /64 subnet in let's say /80 for the pfsense B.
- Is it possible to forward a port to a host, which doesn't have the pfsense as its gateway? This would be the case to forward e.g. the SSH Port from the Hypervisor.
Thanks for your time
-
@Omikron said in Port forward through another pfSense:
Is it possible to forward a port to a host, which doesn't have the pfsense as its gateway?
And how would the traffic get back.. You would have to host route on the device so it knows to send traffic back to pfsense. Or you would have to source nat the traffic so it looks like it came from pfsense, so the device would send the return traffic back to pfsense.
As to splitting a /64 - yeah that would be borked.
-
Yep, that ^. You can't split a /64 without expecting all sorts of problems.
You could set a very specific outbound NAT rule to workaround the asymmetric routing you would otherwise have with a device that isn't using pfSense as it's gateway. It would be better to avoid it but if you have no other option it could be done.
Steve