New to pfSense just trying to make it work for internal lab.
-
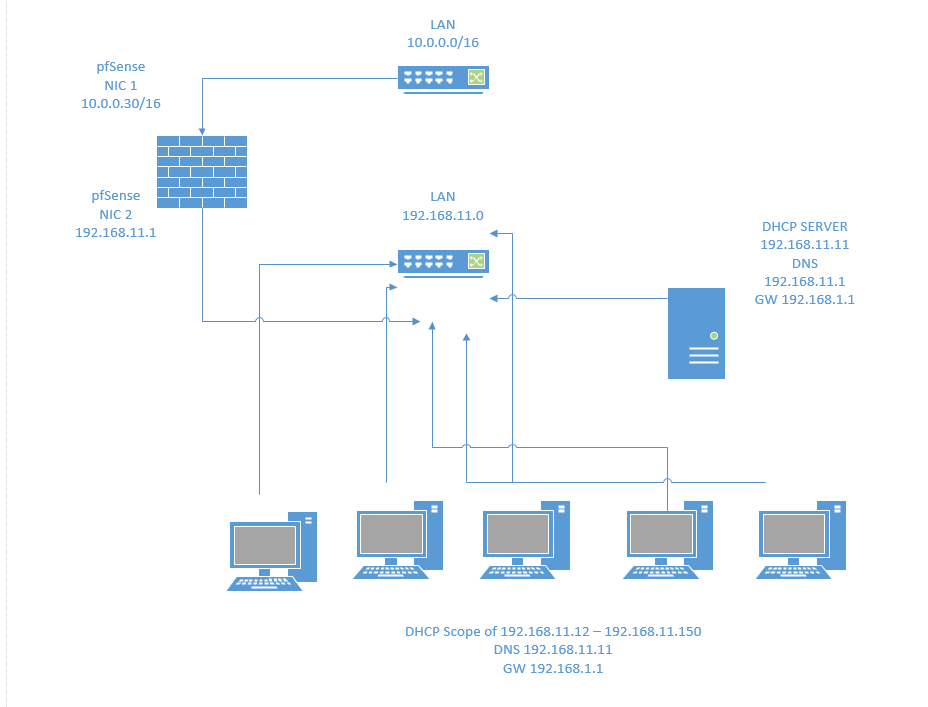
Is this correct?
PF Sense :
WAN NFE0 10.10.0.30/16
LAN NFE1 192.168.11.1/24WebUI:
Routing > Create a new gateway
LAN Interface
IPv4
Address is internal
192.168.11.1Routes >
Destination Network 10.10.0.0 /16
Gateway 192.168.11.1Firewall > Rules > LAN
LAN int
Protocol ANY
Source Network 10.0.0.0/16
Destination any -
No, there is no gateway to be created on LAN and no routes to add.
The LAN IP is the gateway for your LAN devices, but there is nothing to set on pfSense.The only gateway you need is the upstream gateway on WAN for Internet access. Best way to create it is in the WAN interface settings.
On LAN there is an allow any to any rule by default.
-
I am not sure.
I have a direct connection to a switch that provides the 10.0.0.0/16 Network
Plugged directly into my pfSense NIC 1 and gets the DHCP address.NIC 2 plugs into a 48 port switch.
All devices plug in to my lab switch and a DHCP server provides IP addresses for the 192.168.10.0/24 network.
I manually assign the LAN interface on the pfSense NIC 2 to 192.168.10.1 address.But all of my devices on that switch are not able to get internet access?
[pfSense NIC 1]
^---cable---->[WAN Switch]
[pfSense NIC 2]
^---cable---->[48 Port Managed Switch]---cable-> [DHCP Server &[Computers] *Cant get online....Hope that helps explain what I am trying to accomplish.
-
@drock615 said in New to pfSense just trying to make it work for internal lab.:
Plugged directly into my pfSense NIC 1 and gets the DHCP address.
Does pfSense also get a gateway from that DHCP? You should find it in System > Routing > Gateways.
@drock615 said in New to pfSense just trying to make it work for internal lab.:
All devices plug in to my lab switch and a DHCP server provides IP addresses for the 192.168.10.0/24 network.
So your lab devices get their network settings from an other DHCP, not from pfSense?
Have you told that DHCP the new gateway, the LAN IP of pfSense, so that it is delivered to the clients? -
Yes NIC 1 the network with internet.
Yes it is getting an IP address 10.0.0.30, assuming its is getting GW 10.0.0.1, I will check.Yes NIC 2 devices get IPs from a DHCP Server.
I statically set NIC 2 192.168.10.1 in pfSense. And previously added it to the Windows DHCP manager.Hope that makes sense. Let me know. And appreciate your help.
-
@drock615 said in New to pfSense just trying to make it work for internal lab.:
Yes NIC 2 devices get IPs from a DHCP Server.
I statically set NIC 2 192.168.10.1 in pfSense. And previously added it to the Windows DHCP manager.The question here is, which gate do the LAN hosts use? Check the clients interface settings.
-
Oh ok. LAN 192.168.10.0/24
WAN 10.0.0.0/16
Finally some success.
unchekced enable DNS resolver
enabled DNS forwarder
have a firewal rule for any anyWe can get online.
Does that sound like it should be ok?
-
The DNS resolver and forwarder should work both. The resolver has some more features and is the default.
However, why do you not run the DNS on your internal DHCP server? Running both on one box has some advantages.If you run the DNS on another device, you have to tell that your DHCP, cause it has to provide the settings to the clients as well as the default gateway.
An allow-any-to-any rule is also default on LAN and at least for getting the installation up and running helpful. If you want you can restrict the access later.
-
I do run it on my DHCP server DNS is 192.168.10.11
I will have to see if I can add it because it to DHCP because of the subnet .
I see that rule. And will restrict soon. Top down. I am setting up the scheduler for internet access now.
-
-
Ah figured it out I added the 10.0.0.30 up to my dhcp under scope options dns servers.
All is working great now.Thank you so much for all of your help!!!!!!
-
This is going to be the attacker's machine if you want to have an internal pentesting environment.