Safe IKEv2 Configuration for pfSense and Windows 10 and macOS
-
I see a number of tutorials here that specify DH group 2 or some other insecure settings. This is the best way to configure IPsec IKEv2 on pfSense for security and efficiency with Windows 10 and macOS client support. Note that some of these may depend on your specific configuration; these settings are for mobile client VPN connections without machine authentication.
pfSense IPsec IKEv2 Configuration
Phase 1
Algorithm: AES256-GCM
Key length: 128 bits
Hash: SHA384
DH Group: 20 (nist ecp384)Phase 2
Protocol: ESP
Encryption Algorithms: AES256-GCM 128 bits or AES128-GCM 128 bits
Hash Algorithms: SHA256, SHA384
PFS key group: 20 (nist ecp384)Windows Configuration
Advanced settings for IKEv2 connections aren't available via GUI in Windows as of 1909. The only way to use ECC or any DH paramaters other than group 2 are with group policy or PowerShell. Open a PowerShell prompt as administrator and run the following commands.
Create a new VPN connection
Fill in the necessary information between the square brackets (and remove the brackets). Remove "-SplitTunneling" or "-RememberCredential" if you wish.Add-VpnConnection -Name "[VPN Connection Name]" -ServerAddress "[FQDN or IP]" -TunnelType "Ikev2" -SplitTunneling -RememberCredential -EncryptionLevel RequiredSet VPN connection options
This tells Windows to use the same parameters that were configured in pfSense.Set-VpnConnectionIPsecConfiguration -ConnectionName "[VPN Name Here]" -AuthenticationTransformConstants GCMAES256 -CipherTransformConstants GCMAES256 -EncryptionMethod GCMAES256 -IntegrityCheckMethod SHA384 -PfsGroup ECP384 -DHGroup ECP384 -PassThru -ForceTroubleshooting
Delete the following registry value if it exists. Even if the value is set to 1, it may force the use of DH group 2 and AES-CBC during phase 1, preventing the use of ECC or GCM-mode.
See the "AES-256-CBC and MODP2048" section of the StrongSwan wiki entry on Windows clients for details about this registry entry.HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\Rasman\Parameters\NegotiateDH2048_AES256macOS Configuration
macOS has the same problem as Windows; any advanced configuration requires the use of Apple Configurator 2. This was tested on macOS Catalina.
- Install Apple Configurator 2 from the App Store
- Save the root and VPN server certs to your Mac
- Open Apple Configurator 2 and select File -> New Profile
- Give the Profile a name on the General screen
- Select Certificates on the left
a. Click Configure and select the root CA certificate
b. Click + in the top right corner and select the intermediate CA certificate, repeat this step to include all certificates in the chain. - Select VPN on the left side, then click Configure on the right
- Configure as follows
- Connection Type is IKEv2
- Server is the public hostname or IP of the pfSense VPN server
- Remote Identifier can contain the same information as the Server field above
- Local Identifier is blank, which allows the installation of this profile on multiple clients. This field will be dynamic and based on the client IP or hostname when the client connects. Ignore the red arrow and warnings.
- Machine Authentication is set to None
- *Ignore the Certificate Type field, which is only necessary for machine authentication.
- Server Certificate Issuer Common Name should match the common name of the root or intermediate CA that issued the VPN server certificate.
- Server Certificate Common Name should match the common name of the VPN server certificate.
- Enable EAP should be checked
- EAP Authentication should be set to User name/Password
- Account and Password can be left blank, allowing the profile to be installed on multiple computers.
- Dead Peer Detection Rate should be High
- Check Use IPv4/IPv6 Internal Subnet Attributes
- Check Enable perfect forward secrecy
- IKE SA Params and Child SA Params should be the same, make sure they match Phase 1 and Phase 2 settings from pfSense, respectively.
-
- Encryption Algorithm should be AES-256-GCM
-
- Integrity Algorithm should be locked to SHA2-384
-
- Diffie-Hellman Group should be 20
-
- Lifetime In Minutes should match the Phase 1/Phase 2 lifetime configured in pfSense
- Save the profile, ignoring any errors due to the blank Local Identifier
- Install the profile and connect
-
Thanks for taking the time to post this. I decided on IPsec instead of OpenVPN due to built-in client support for Windows and Android, but it appears "built-in" is a stretch.
I think I have IPSec IKEv2 set up in pfSense, I'm getting through the firewall from a Windows laptop with the certificate, but then I get "policy match error", which I'm guessing is the lack of windows GUI configuration for the Netgate-recommended security settings at the pfSense end.
Going to try it now . . .
-
All the clients seem to suck unless you buy a high-end firewall and most of those are just GUI wrappers for IPsec that make it easy to configure and add some extra features. I attempted OpenVPN but the free version clients don't provide a great experience. I decided to switch to IPsec thinking that basically every client supports it; I had no idea that it was going to take me days to configure properly.
-
OK, I believe the encryption protocols were negotiated after running the Powershell script in Windows. pfSense IPsec status page showed an incoming connection, but I got an authentication failure from the win client.
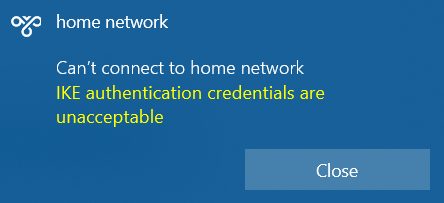
I am using a pre-shared key with EAP, and the certificate was installed on the Windows laptop per Netgate documentation. I didn't see anything in the Powershell script to connect the cert to the VPN setup, but maybe that isn't needed?
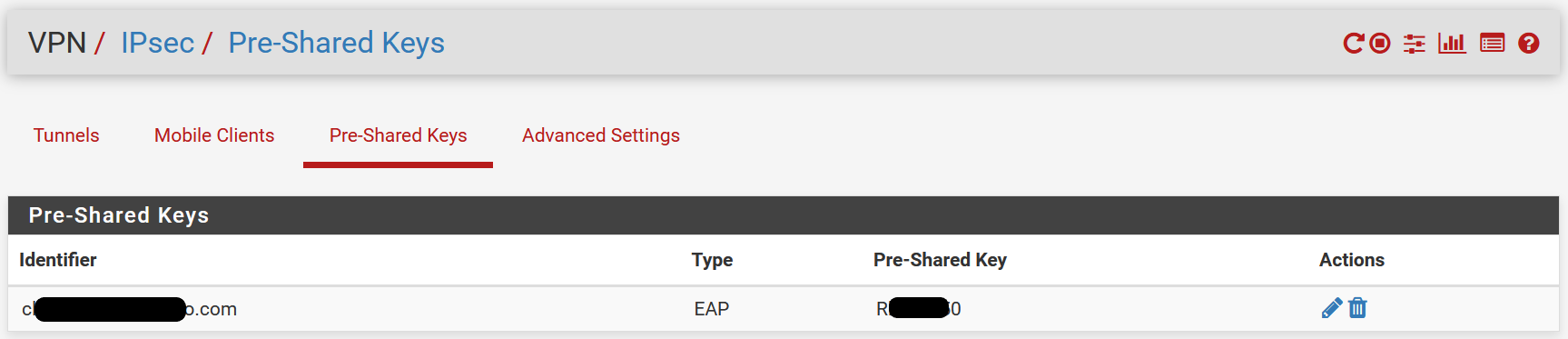
VPN/IPsecPre-Shared/Keys:
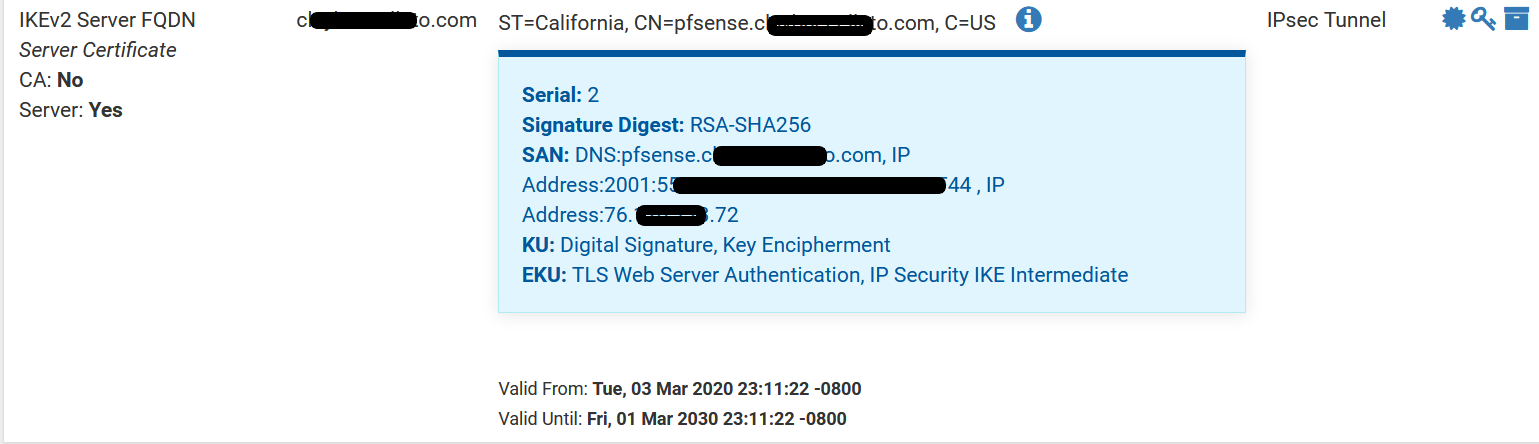
SystemCertificate/Manager/Certificates:
-
I'm using EAP-RADIUS with JumpCloud so no PSK here. You might take a look at MS docs for the PowerShell cmdlets.
https://docs.microsoft.com/en-us/powershell/module/vpnclient/set-vpnconnectionipsecconfiguration?view=win10-ps
https://docs.microsoft.com/en-us/powershell/module/vpnclient/set-vpnconnection?view=win10-ps
https://docs.microsoft.com/en-us/powershell/module/vpnclient/add-vpnconnection?view=win10-psAlternatively, take a look at JumpCloud. I think it's free for up to 10 user accounts, I only have 4. https://jumpcloud.com/ It gives you username/password based authentication with a public web-facing password reset portal with MFA for free. It has some other cool stuff like a Linux agent that updates local accounts/groups for SSH access, you can use password or public key auth and configure passwordless sudo and SSH MFA directly from the user portal. It also does Windows account management for RDP logins with MFA. LDAP and RADIUS servers. Pretty cool and I was amazed at how easy it was to configure everything.
This sounds like an ad but I'm just excited that some enterprise stuff that's traditionally been relegated to the LAN or very difficult to safely implement over the public Internet is finally get some SaaS offerings.
-
@groupers said in Safe IKEv2 Configuration for pfSense and Windows 10 and macOS:
I'm using EAP-RADIUS with JumpCloud so no PSK here. You might take a look at MS docs for the PowerShell cmdlets.
https://docs.microsoft.com/en-us/powershell/module/vpnclient/set-vpnconnectionipsecconfiguration?view=win10-ps
https://docs.microsoft.com/en-us/powershell/module/vpnclient/set-vpnconnection?view=win10-ps
https://docs.microsoft.com/en-us/powershell/module/vpnclient/add-vpnconnection?view=win10-psAlternatively, take a look at JumpCloud.
While I am sure JumpCloud is cool, I'm not looking to add any more moving parts to this setup at the moment. I would be happy to just have a working VPN.
Still not sure if or where in the powershell setup the authentication was configured. I did see this in your links:
[[-AuthenticationMethod] <String[]>] [[-EapConfigXmlStream] <XmlDocument>] -
I'm afraid I'm not really sure where to go with this. It seems like I got through the firewall, the myriad of possible configurations on both the client and server end, and somehow authentication is failing? No wonder people just settle for an "insecure" setup that falls within the intersection of Windows and pfSense GUI configuration.
-
This wasn’t intended to be a full IPSec configuration guide but a guide to configuring strong IPSec crypto on pfSense and clients. My configuration does not use certificates for machine or user authentication.
If you have a configuration that is working using EAP-RADIUS it will work with these changes. I have no experience using the powershell cmdlets to configure IPSec with TLS auth and am not paid pfSense support.
-
@groupers said in Safe IKEv2 Configuration for pfSense and Windows 10 and macOS:
This wasn’t intended to be a full IPSec configuration guide but a guide to configuring strong IPSec crypto on pfSense and clients. My configuration does not use certificates for machine or user authentication.
You could have led with that. I have a working pfSense setup, just trying to configure the Windows client. Thanks for your efforts.
-
This post is deleted! -
@lifespeed said in Safe IKEv2 Configuration for pfSense and Windows 10 and macOS:
tup, but maybe that isn't needed?
VPN/IPsecPre-Shared/Keys:I don't think it's necessary as long at the trusted key is installed. I automated that in an earlier script (which I'm still adapting, but the cert portion is relevant). I have another version which maps out multiple subnets, I just don't have access to it from here.
$Name = "NAME" $Server = "HOST" $DnsSuffix = "DnsSuffix" $RemoteNetwork = "xxxxxxxx/24" $Cert = @' -----BEGIN CERTIFICATE----- CUT AND PASTED KEY HERE -----END CERTIFICATE----- '@ ## Add the cert $EncodedCert = [system.Text.Encoding]::UTF8.GetBytes($Cert) $pfx = New-Object System.Security.Cryptography.X509Certificates.X509Certificate2 $store = new-object System.Security.Cryptography.X509Certificates.X509Store(“Root”,”LocalMachine”) ## Download the cert file $pfx.Import($EncodedCert); $store.Open("MaxAllowed") $store.Add($pfx) $store.Close() ## Add the connection try { Add-VpnConnection -Name $Name -ServerAddress $Server -TunnelType "Ikev2" -EncryptionLevel "Required" -AuthenticationMethod Eap -SplitTunneling -AllUserConnection -RememberCredential -PassThru -DnsSuffix $DnsSuffix } catch [Microsoft.Management.Infrastructure.CimException] { ## Ignore } Add-VpnConnectionRoute -ConnectionName $Name -DestinationPrefix $RemoteNetwork