Port Forwarding
-
Hello All,
First post here so please go easy on me.
I am new to pfSense and haven't been able to figure out the correct port forwarding settings to access my security cameras remotely.
On my old router I was able to set the following and access cameras through my app.
HTTP Port 1 7080
HTTP Port 2 7081
TCP Port 90Would somebody be willing to point me in the right direction on replicating that in pfSense.
Thank you very much!
NoSenseAtAll
-
Here are the docs:
https://docs.netgate.com/pfsense/en/latest/book/nat/port-forwards.html :) -
You want to open up your camera's to the public internet - JFC that just a horrible horrible bad idea!!
Why would you not just vpn into pfsense and then securely view your camera feeds?
-
@johnpoz said in Port Forwarding:
open up your camera's to the public internet
Ha, yeah, in my head I guess I was assuming there were some source limitations on the NAT rules.
-
@teamits said in Port Forwarding:
Ha, yeah, in my head I guess I was assuming there were some source limitations on the NAT rules.
Yes, true, you can lock it down to a source address. If you don't VPN (highly recommended), you can do source-based rules. I use that from work-to-home sometimes to get into my network. However, I have static IP addresses at both ends, so it's really easy.
Jeff
-
Do you know what your source IP will be, like from work or something - then sure that is fine..
-
@teamits Thank you - already been through the port forward docs and still too new to assimilate that into something that works :)
-
@johnpoz I have an app that I use that interfaces with my camera DVR. So, yes, I guess essentially it is open to the public if they know my IP address and can get past the firewall. I don't have enough skills yet to "vpn into pfsense and then securely view your camera feeds", but love that idea. Where should I go to learn how to do that?
-
you may be overthinking it...here is a NAT entry sending 443 (HTTPS) to LAN IP 192.168.1.12:
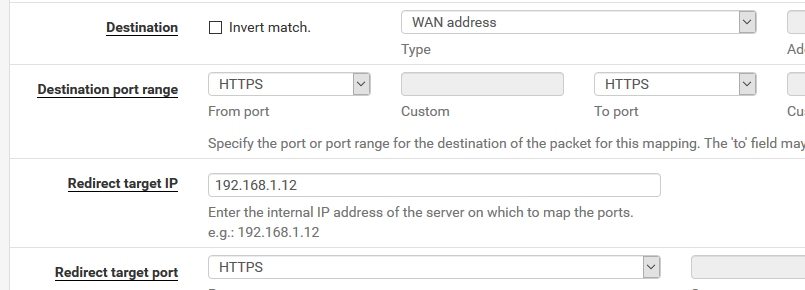
For your purpose change the "destination port range" to Other and enter the port. Usually one entry per port but you could use from 7080 to 7081 in your case since they are sequential, with the destination port of 7080. -
Hello!
The netgate docs are exceptional and contain a wealth of information.
The link here:https://docs.netgate.com/pfsense/en/latest/firewall/remote-firewall-administration.html
talks about remotely accessing the pfsense admin interface, but the concepts could also be applied to accessing your cameras or any other device remotely.
As the docs and others have noted, restricting access to a source IP is a good idea.
While others might disagree, I am more in line with the docs when it comes to changing access to non-standard ports.Port 7080 is a standard port for unifi cameras (and maybe others) and I would definitely have that on my list if I were running a port scanner. Personally, I use a high port prefix naming convention to help me remember, i.e. 3xxxx, 33xxx, 333xx.
John
-
@nosenseatall said in Port Forwarding:
c if they know my IP address and can get past the firewall
Get past what firewall - when you port forward, you disable the the firewall for that port.
Do what you want - most camera's don't need any open ports to view... They create the connection outbound.. And you use a go between with the company to view your stream..
How it should work is company runs a stun server on the public internet that allows your remote device and your camera's to exchange info and create a direct peer to peer connection without you having to open inbound traffic on your firewall.
You understand video camera's are some of the worse security devices on the planet.. If you want to directly hit your camera or nvr IP, then you should vpn.. Unless you can lock down your source IP in your port forward.
But forwarding on pfsense is no different than any other soho router.. Just more powerful, but when it comes down too it, its a 4 clicks..
For most things its Port, IP and Port - save.
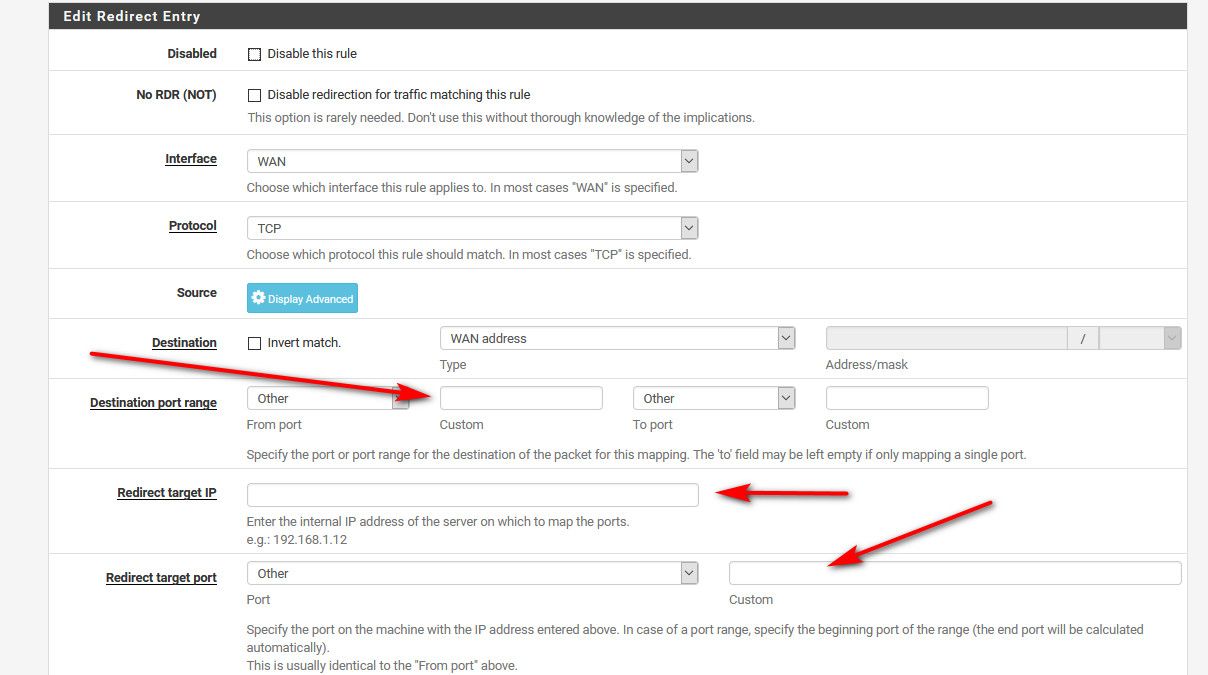
And you only have to put in the ports if what port your wanting to forward is not in the dropdown boxes. This is ZERO different than any soho router..
The defaults will normally be all you need.. And normally the port is the same.. So really 2 things you need to know, the port and the IP of your server... 192.168.1.12 or whatever and the port..
But again... I would not suggest you open your camera's to the public internet.. But you know what, I told you the safety is on - if you blow off your little toe with the loaded gun, not my problem...
https://docs.netgate.com/pfsense/en/latest/nat/forwarding-ports-with-pfsense.html
Here is vpn docs
https://docs.netgate.com/pfsense/en/latest/vpn/openvpn/openvpn-remote-access-server.htmlIt really is follow the bouncing ball (wizard)
-
Yup, use a VPN for this if you can.
We did a hangout on this with a walk-through, OpenVPN starts here: https://youtu.be/qscIIZ10WTQ?t=2407
Steve
-
@johnpoz Thank you - I appreciate your help and information. I would much rather have my network closed off and not open to public internet. I'm in the learning curve (nothing unusual for me) and look forward to learning more about how to secure my network.
-
@stephenw10 Thanks for the link - I will definitely watch.