Interface LAN stay master
-
Good morning, sir,
My network infrastructure :
2 pfsenses on two different hosts "ESX vmware"
4 WAN
1 LANUse of failover for WANs.
Expected situation :
1 WAN is down another one takes over.
When all WANs are down, pfsense 2 takes over by becoming MASTER of the LAN interface.Problem encountered:
The WANs follow one another well, when the first WAN is down, the second one takes over...
But once all the WANs are down the LAN interface remains MASTER.
So the computers on the LAN don't have access to the internet anymore because their "VIP" gateway always sends back to the first pfsense.More information :
When a WAN interface does not work anymore on the first pfsense, the second pfsense becomes MASTER on this interface.
The promiscuity mode is activated on vmware.
The Skew seems to me to be good.
The DHCP gives well the VIP address in gateway by default.
IPv6 is not authorized on our network.
The synchronization of the data on the first pfsense, is well done on the second pfsense.
And if all the interfaces are active on both pfsenses, the first pfsense is MASTER on each of its interfaces.I don't know how firewall redundancy works at the LAN interface, I thought that the LAN would automatically switch to slave if it no longer had access to the gateways, therefore to the internet.
-
You will never get an HA failover for a multi-WAN event. Only for interface down events.
If a WAN link is up but the monitoring fails, that is not an HA event.
You are confusing Multi-WAN monitoring events with HA events.
-
Thank you for your response.
So, if I understood correctly, my LAN interface will not change its state to "slave" automatically, if all the WANs become "slave" following a network card failure on?
Do you have an idea to automate the change of state of the LAN interface to "slave" if the WAN no longer responds?
-
There is no "SLAVE" so I am not sure what you're talking about.
CARP VIPs are MASTER or BACKUP.
High-Availability looks at interface down events to demote a MASTER node triggering a failure to the BACKUP node.
Multi-WAN looks at pings to a monitoring host IP address to trigger routing table changes. These events do not trigger High-Availability demotion of that node.
Please see the sticky at the top of this category.
-
@Derelict said in Interface LAN stay master:
There is no "SLAVE" so I am not sure what you're talking about.
CARP VIPs are MASTER or BACKUP.
High-Availability looks at interface down events to demote a MASTER node triggering a failure to the BACKUP node.
Multi-WAN looks at pings to a monitoring host IP address to trigger routing table changes. These events do not trigger High-Availability demotion of that node.
Please see the sticky at the top of this category.
Sorry for the use of the word "Slave" I meant "Backup" actually.
Without taking into account the failover that I set up, I would like to know if a LAN interface switches to BACKUP automatically when the other WAN interfaces are in backup?
In France we use the term "Master and Slave" to designate the status of the interfaces, sorry for this misuse of English.
-
I'm not 100% sure what you are asking, but if, for example, the master firewall has a WAN interface go down (let's say the cable gets knocked loose), then the virtual IPs on ALL the interfaces- LAN and WAN should go into carp backup so the other firewall can take over.
-
This is exactly the question I asked.
However, I do have a problem, if what you say is true.
Because when a "Wan disconnects" cable the interface becomes BACKUP and that of the other pfsense it becomes MASTER BUT my other interfaces do not change state and remains in MASTER on the first pfsense and BACKUP on the second.
Would you like to have screens to better understand?
I make you a small diagram:
Pfsense 1:
Wan 1 = MASTER
Wan 2 = MASTER
LAN = MASTERPfsense 2:
WAN 1 = BACKUP
WAN 2 = BACKUP
LAN = BACKUPIf I unplug the WAN 1 cable from pfsense 1, this happens:
Pfsense 1:
Wan 1 = BACKUP
Wan 2 = MASTER
LAN = MASTERPfsense 2:
WAN 1 = MASTER
WAN 2 = BACKUP
LAN = BACKUPand if I cut the second WAN:
Pfsense 1:
Wan 1 = BACKUP
Wan 2 = BACKUP
LAN = MASTERPfsense 2:
WAN 1 = MASTER
WAN 2 = MASTER
LAN = BACKUPthen the people on my LAN no longer have access to the internet because they always go through the first pfsense.
-
This usually indicates a problem with the layer 2 connection. Verify each firewall can ping all interfaces of the other firewall.
-
When a CARP interface loses link, all CARP interfaces on that node get demoted by an advskew of 240 for every down interface.
This makes the backup assume MASTER functionality because it starts receiving CARP advertisements from the primary (on the interfaces that still have connectivity) with a higher advskew (240 if only one interface is down on the primary) than the default secondary advskew of 100.
The secondary will assume MASTER on the interface that is down on the primary because it will stop receiving advertisements altogether.
If this is not happening you have misconfigured your cluster. My first suspicion would be that the secondary can receive advertisements from the primary but the primary cannot receive advertisements from the secondary.
-
Thank you for your answers.
I'm taking a closer look at that.Wouldn't the communication be over all interfaces or just the one used for the synchronization mentioned in "high availability synchronization in system"?
I just checked that the interfaces are pinging each other and it is the case with diagnostic and ping proposed by pfsense.
Then I had configured a Vlan on the "CARP" interface and it is good.
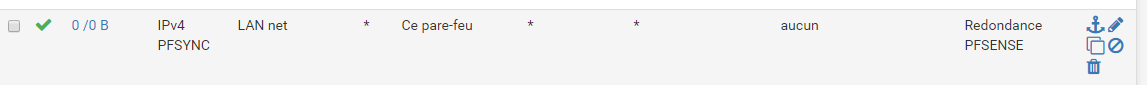
I added the following "access list" on all interfaces:
I'll do some tests early next week.
If you have ideas of bad configurations don't hesitate to let me know.
-
Please read the sticky in this category.
-
That rule makes absolutely no sense on a LAN interface. I don't think it makes any sense on any interface. See the above referenced sticky post.
-
Thanks, I've been going over the sticky post again.
So it's the CARP protocol that toggles the state of the interfaces.
My problem comes from this protocol and more particularly the "layer 2" link which is not good.
Would it be interesting to change the protocol of the "Pfsync" rule to "CARP", if the problem comes from a firewall block because of an ACL?
Or doesn't it make sense? -
No.
You do not need to specifically pass CARP. It is passed automatically.
You probably want to read everything here:
https://docs.netgate.com/pfsense/en/latest/book/highavailability/index.html
And here:
https://docs.netgate.com/pfsense/en/latest/solutions/reference/highavailability/index.html
The second one is tailored to Netgate devices but the general principles are the same for all HA clusters.
-
Thank you, I'm going to look at all this documentation and I'll come back to tell you the solution to the problem or more specific questions for more specific help.