Double NAT with no option to Bridge ISP router
-
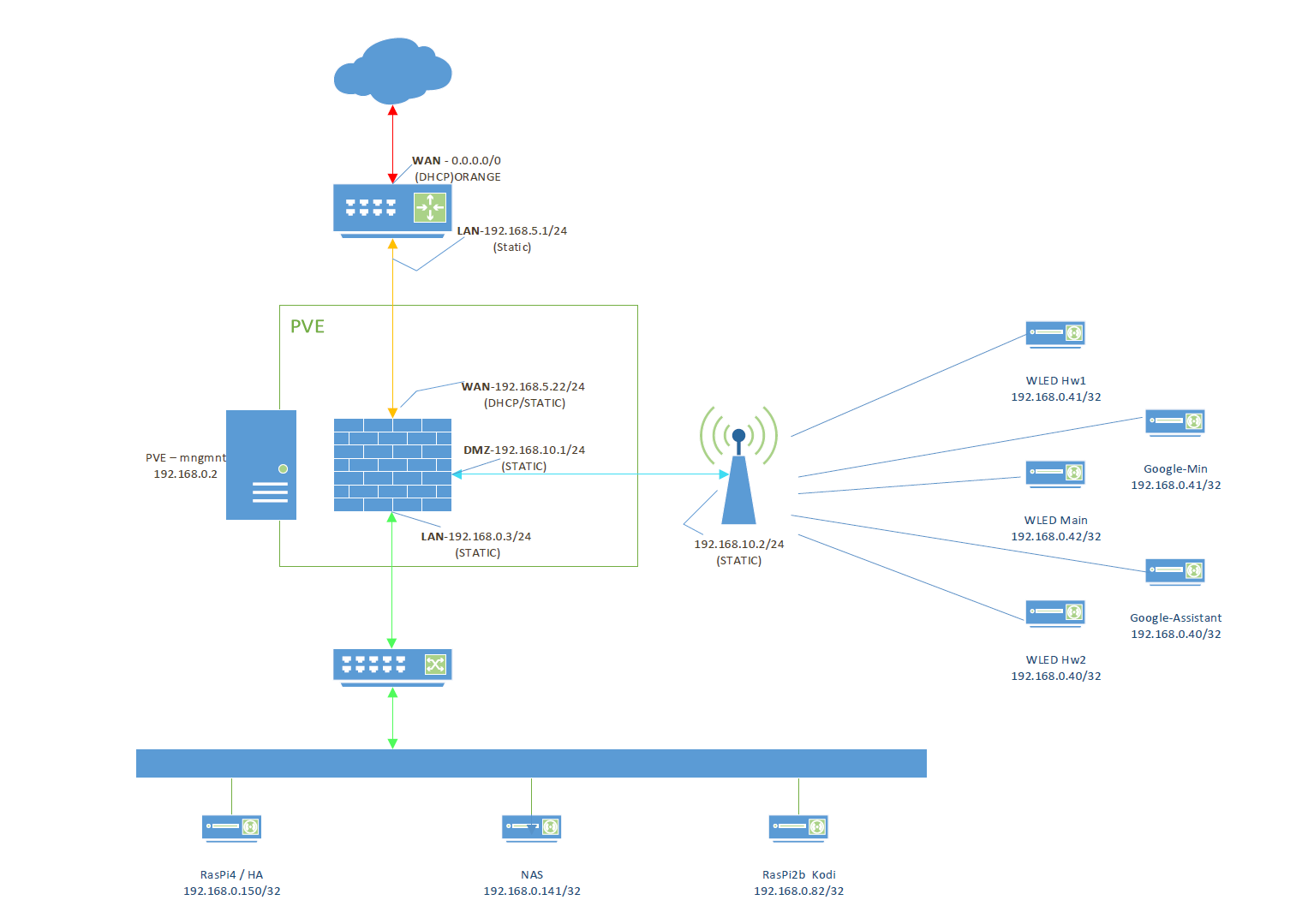
Here is a pic of my network setup. My ISP's router isn't able to go into bridge mode yet so I'm stuck behind a double NAT rule. Now I've been looking at the other solutions but nothing really fits and I've tried hybid mode in Firewall>NAT.
I'm trying to get access to my Home Assistant server from the internet via https://<duckDNS_URL> and forward that to my local server on the LAN on port 8123. I don't think I need to go into details that this is a PVE with NICs that are bridged to pfsense ;)
I can reach the internet from both DMZ and LAN so no issues there.
-
you just need to set wan of pfsense as dmz or forward everything to pfsense and from pfsense a nat rule, remeber to disable "block private network" from the interfaces.
also that 192.168.10.2 is another router ? if so it's a triple nat you are dealing with
from modem nat to pfsense from pfsense nat to 192.168.10.2 from here to your google stuff
what it's strange here is that you have wled hw1 and google mini / wled hw2 and google assistant with the same ip? that can't be good
personally i will remove that router and use an access point instead
another thing, you are using the same subnet for google/wled stuff and your raspi stuff. -
@kiokoman said in Double NAT with no option to Bridge ISP router:
192.168.10.2 is another router
Ok. so 1st My bad for the same IP addresses. That was a copy paste mistake. Don't pay attention to the DMZ. that's just an dumb TP-Link router with DD-WRT acting as a dumb AP where all of my wifi automation resides.
The IP's in the DMZ are actually 192.168.10.0/24. Again My bad for a horrible detail in the drawing.
the traffic I'm interested in is the Orange router 192.168.5.1>to PFsense WAN 192.168.5.22>LAN 192.168.0.150:8123
PS> i'll see if I can update the original drawing.
-
ok it's nothing special, as i said you need to set 192.168.5.22 as dmz inside your isp modem or portforward everything from your modem to it
and from pfsense you need a nat port forward from tcp wan address port 8123 to 192.168.0.150 port 8123
if it's not working use Diagnostic / packet capture to see if traffic is coming and where is going
and remember to disable "block private network" from the interfaces -
@kiokoman said in Double NAT with no option to Bridge ISP router:
et 192.168.5.22 as dmz inside your isp modem or portforward everything from your modem to it
and from pfsense you need a nat port forward from tcp wan address port 8123I'll take a look at the pfsense logs. Currently my pfSense WAN is in the DMZ router
"current DMZ is: 192.168.5.22" (From the modem UI)Edit:
So now when I'm trying to reach my HA web server I get the "pfsense" Potential DNS rebind attack detected. page -
I've made progress. At least now I can see traffic on the WAN trying to get from port 443 to port 8123
Ideas?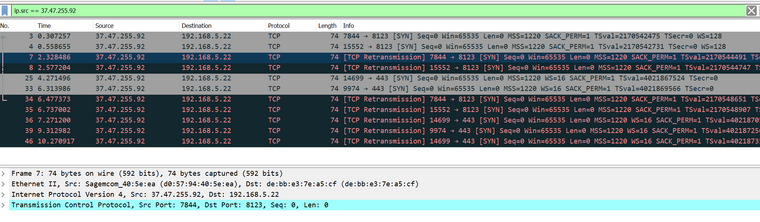
-
yeah port 443 is used by the webgui, you need to change that port from system / advanced / admin access or you need to change the port forward so to access your internal server you have to write https://<duckDNS_URL>:8123
-
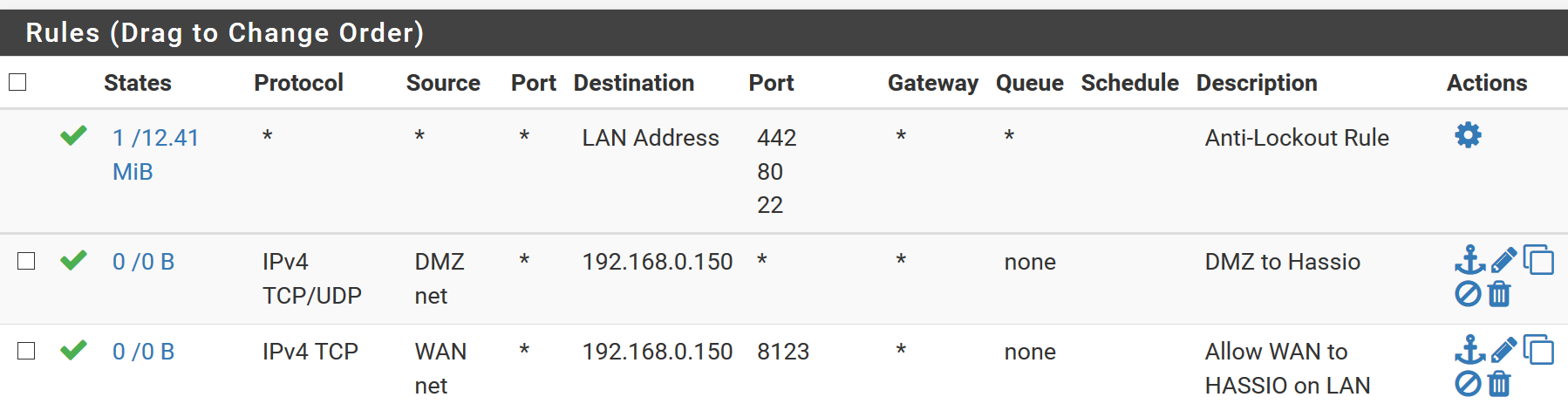
I'm at a loss. I changed mu pfsense GUI to 442 and also tried to use the url without and with port 8123 and still getting nowhere. Here is my portfwd rule from my firewall and I have NAT outbound as automatic.
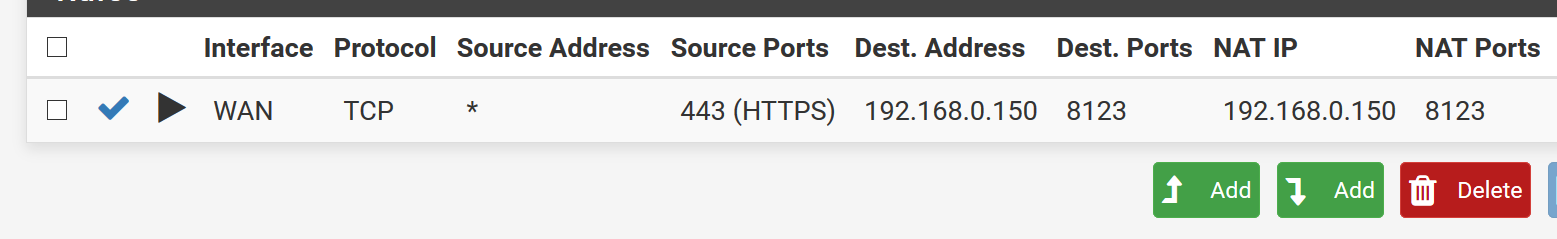
WAN rules
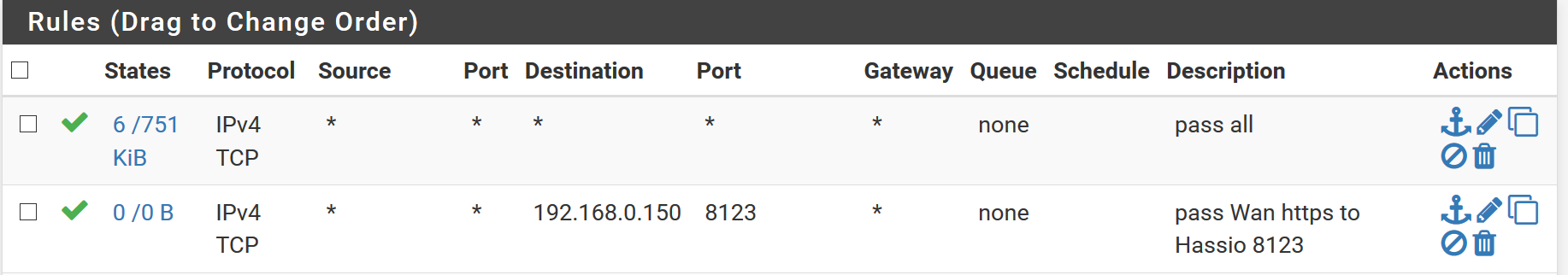
LAN
-
no, that rule is wrong,
most of the time you don't know the source port, it's random
the destination is your WAN address not your internal ip, that is your destination for the NAT
the rule should be
source *
source port *
dest address WAN
dest port 443 (HTTPS)
NAT IP 192.168.0.150
NAT Ports 8123 -
I'm an idiot. I'm so used to cisco fw rules that I totally misinterpreted this. I feel Sheeeeepish ;) Thanks man! you truly deserve the thumbs up.