How to distribute connections between two wan-ip interfaces
-
Dear,
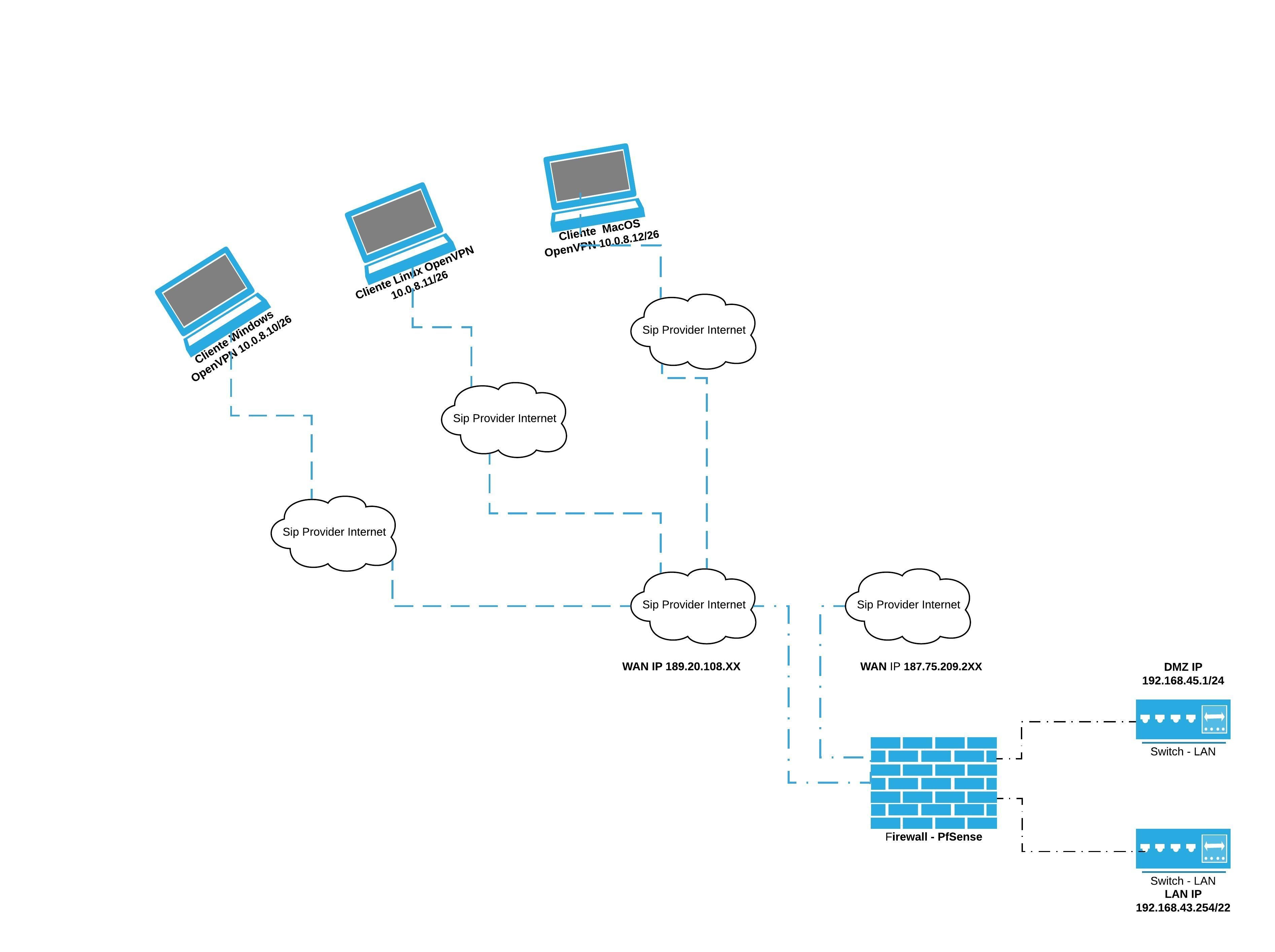
Please help me with the sizing of my OpenVPN server. I'm using pfsense 2.4.4-RELEASE-p3 (amd64), as shown in the diagram below, two wan-ip connections, the 189.20.108 Internet interface. xx 10 MB full duplex and the second wan-ip interface 187.75.209.2xx is a 100 MB PPOE connection. My demand for remote connections has increased a lot, so it is creating bottlenecks in the dedicated link for remote connections via OpenVPN. Help me with the configuration and distribution of these demands between the two links.
I'm reading the documentation on Use Multiple Servers, but I don't know if that's the path I should take.
https://docs.netgate.com/pfsense/en/latest/vpn/scaling.html#scaling-openvpnUse Multiple Servers OpenVPN is not multi-threaded so any single instance of OpenVPN is limited to using a single CPU. If a router has fast cores and not too many users, that may be OK, but it does not scale well. A workaround for this is to split users onto multiple servers. There are various means to reach this goal, including (but not limited to): Multiple servers on different WANs or ports, each with unique tunnel networks but otherwise identical settings (Same CA structure, encryption, etc). Administrators could choose to manually configure pools of clients to connect to specific servers, but that does not scale well. Clients may connect to any server configured in this manner so long as their settings line up properly. Multiple servers can be listed in a single client configuration with additional remote statements. Add remote-random to the client configuration so that clients will pick a random server when starting, which avoids overloading whichever server is listed first. Servers could be run on multiple WANs to overcome single-circuit throughput limits. Multiple servers with completely unique settings (Different CA structure, different clients, etc) More secure but more difficult to manage. Clients must use different configurations to reach each server, no automated/built-in way to pick between them unless a specific client supports that function. Good for isolating separate security levels (e.g. remote workers, remote administrators, vendors).Best Regards,
Wesley Santo
Copyright 2025 Rubicon Communications LLC (Netgate). All rights reserved.