LAN and DMZ Interface
-
@johnpoz model is s1700-24gr
-
What is the model number?
BTW - have moved this into vlan section.
-
@kirbyL said in LAN and DMZ Interface:
s1700-24gr
Yeah that is just dumb switch, can not do vlans... You can not isolate network with those - they are only 1 network switches. If you want to do more than 1 network you need to connect them like my first pic
-
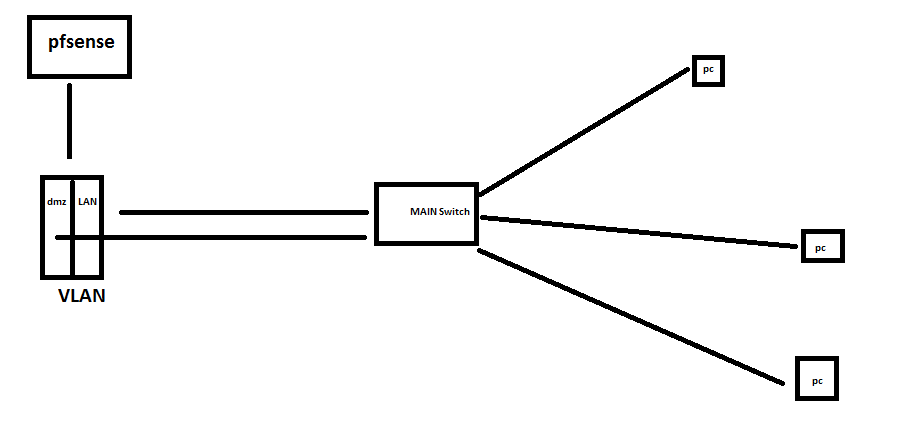
@johnpoz i have a VLAN switch model s5700s-28p-li-ac which is vlan capable. So if i connect my pfsense machine's LAN and DMZ on separate VLANs. It will look like this? (sorry for my drawing)
-
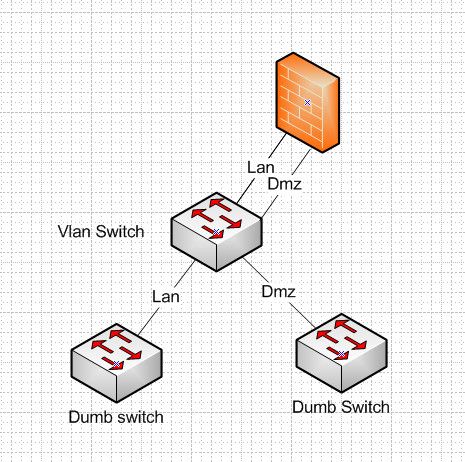
Your main switch needs to support vlans - if you want those pcs to be in different vlans.
That is great that the switch you connect to pfsense supports vlans.. But you can not connect both of those to a dumb switch and maintain isolation.
If you have a vlan capable switch, you can put dumb switch downstream of it, but each switch has to be its own vlan/network..
Once you have a dumb switch, its 1 network.. You can not run multiple networks on that switch with any isolation.. So you can do this..
-
copy that.. thank you much for the insights.. for now I guess, I will have to disable DMZ dhcp server
-
See my edit posted above with a picture
btw - be clear just because you disable dmz dhcp server doesn't mean you can just run multiple L3 networks over the same L2 and expect any security or isolation. Just because you setup the IPs on the device static.. There is no security there if your switches are not actually isolating the L2 networks.
-
@johnpoz thank you so much for the layout, so if LAN needs to talk to DMZ, it will be configured in FW rules?
-
Yes once you have your networks properly isolated, then yes the only way for network X to talk to network Y would have to be allowed by firewall rules.
-
@johnpoz noted.. thank you so much..