Loosing connectivity between pfsense and webserver
-
Hello,
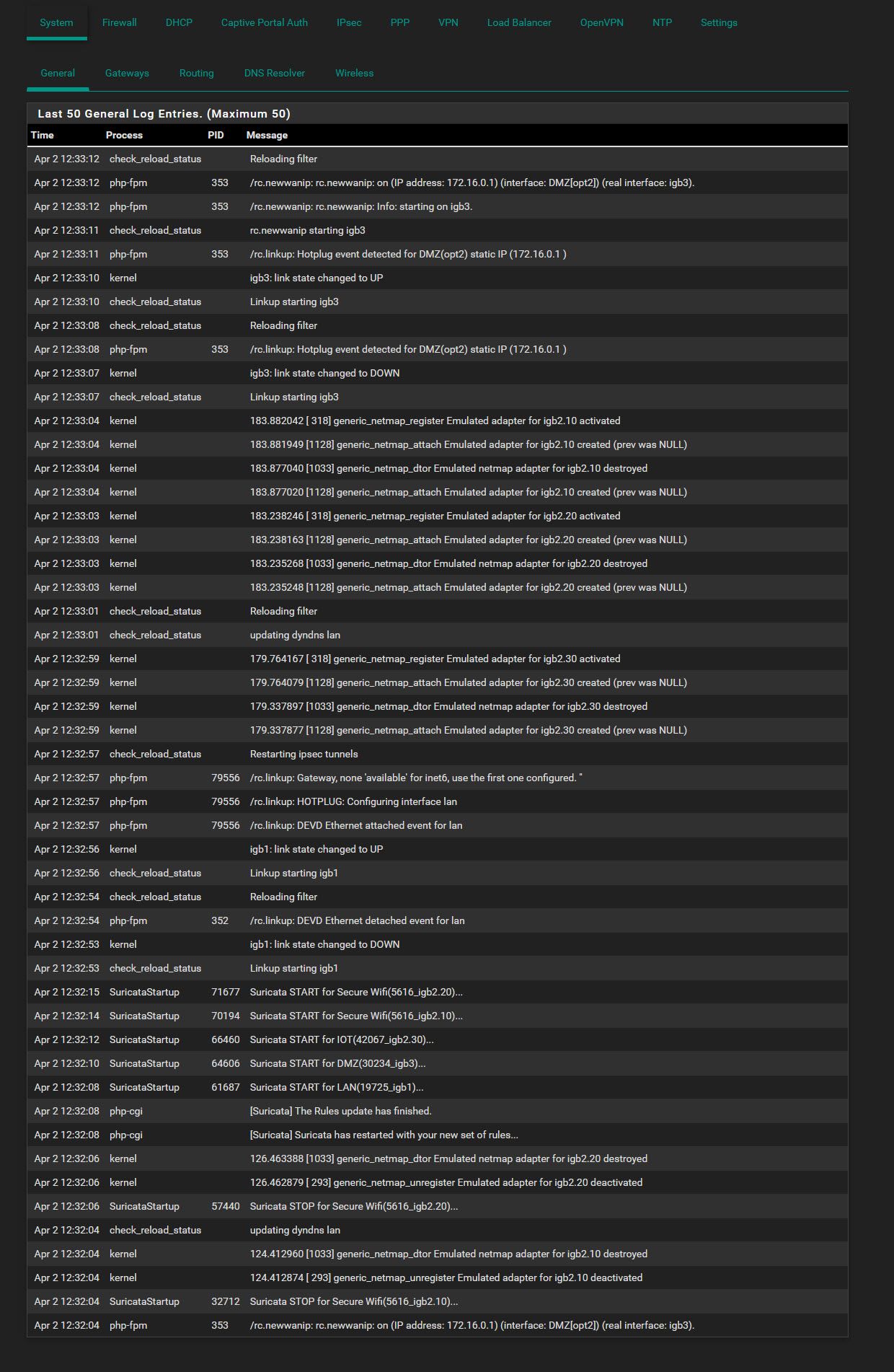
I need some help trouble shooting my connectivity problem between pfsense and my webserver (igb3)
This connectiviy drop issue has been happening around the same time each day after updating to 2.4.5 . In order for the webserver to go back online I need to reboot pfsense. All my other interfaces work fine igb0, igb1 and igb2.Your help would be much appreciated.
Karl
-
There's nothing unusual there. Unless that is looping continually like that. It looks like you're running Suricata in in-line mode?
Does this still happen without Suricata running? Or running in legacy mode?
Steve
-
Thanks for the reply Steve.
I will monitor further.
-
@kiekar said in Loosing connectivity between pfsense and webserver:
Thanks for the reply Steve.
I will monitor further.
You are running Suricata with Inline IPS Mode active. That uses the FreeBSD
netmapdevice. Each time Suricata stops and restarts, thenetmapdevice will take the physical interface down and back up as Suricata first releases thenetmappipe when stopping and then re-establishes the pipe when starting again. That is normal for physical stops and starts of Suricata.The default, due to some folks having issues in the past with not enough memory, is for Suricata to stop and then restart for a rules update. You can override this default behavior by checking the Live Rule Swap on Update checkbox on the GLOBAL SETTINGS tab. This will enable a mode where Suricata will update the rules in memory without requiring a restart of the service (and thus the
netmapdevice won't cycle the physical interface). Be warned, however, that checking that box will cause Suricata to temporarily consume almost double its normal RAM useage because it needs to keep two complete copies of the rules in memory during the swap. Whether this adversely impacts you depends on the amount of RAM in your firewall and how many rules you have enabled. -
Thank you bmeeks for your detailed response. I'm far from being a guru with Suricata but how is it now effecting me all of sudden with pfSense 2.4.5. So far I haven't had to reboot pfSense today.
I'm also using IPS Mode on igb1 and igb2 interfaces with no issues of connectivity loss and having to rebooting pfSense.
I have 4 gigs of RAM where pfSense is consuming 56%
-
@kiekar said in Loosing connectivity between pfsense and webserver:
Thank you bmeeks for your detailed response. I'm far from being a guru with Suricata but how is it now effecting me all of sudden with pfSense 2.4.5. So far I haven't had to reboot pfSense today.
I'm also using IPS Mode on igb1 and igb2 interfaces with no issues of connectivity loss and having to rebooting pfSense.
I have 4 gigs of RAM where pfSense is consuming 56%
I don't know specifically why something affects you now and not before other than to offer that pfSense-2.4.5 is a new version of FreeBSD, the base operating system of pfSense. So it could be the
netmapdevice driver was updated in FreeBSD, or maybe your NIC drivers got new versions in FreeBSD 11.3, or who knows? There are many changes from FreeBSD 11.2/RELEASE, which is what pfSense-2.4.4 was based on, to FreeBSD 11.3/STABLE that pfSense-2.4.5 is based on.Also will note that the Suricata upstream developer team rewrote the
netmapportion of the Suricata binary code. Maybe something in there is in play. All I create on the pfSense side is a GUI wrapper to make creating the Suricata configuration file (suricata.yaml) easier.You could try switching over to the Legacy Blocking Mode to see if that works better for you.
-
Ok bmeek thank you again for suggestions. I will look into it.
-
@kiekar said in Loosing connectivity between pfsense and webserver:
I'm also using IPS Mode on igb1 and igb2 interfaces
Both are LAN type interfaces ? Or one of then a WAN ?
If so, and you have not have any NAT rules that you want to protect - or classic firewall rules that permit IPv6 to enter your network(s), you could remove that interface from the list used by Suricata.
"There is no need to protect a closed door."@kiekar said in Loosing connectivity between pfsense and webserver:
pfSense is consuming 56%
That is : pfSense uses more like 6 % on your system - mine is - and your packages ( Suricata ?) is using that wopping 2 gigs. That van double on rule reload, so be careful what option you choose. You'll be close of using swap space with all the drastic consequences that comes with it.
-
Both are LAN type interfaces ? Or one of then a WAN ?
Suricata is not set for WAN igb0 however is set for LAN igb1, WLAN igb2
If so, and you have not have any NAT rules that you want to protect - or classic firewall rules that permit IPv6 to enter your network(s), you could remove that interface from the list used by Suricata.
"There is no need to protect a closed door."@kiekar said in Loosing connectivity between pfsense and webserver:
pfSense is consuming 56%
That is : pfSense uses more like 6 % on your system - mine is - and your packages ( Suricata ?) is using that wopping 2 gigs. That van double on rule reload, so be careful what option you choose. You'll be close of using swap space with all the drastic consequences that comes with it.
Will look into it