Issue with NAT?
-
Hi,
I was wondering if someone else has happened to them something similar?
Currently put a new pfSense 2.4.4p3 fresh installed, then i configure the VPN which wasnt working, so i thought it was the pfSense so i put in a new 2.4.5 and same issue. So then i tried to NAT port 8006 and nothing, i checked in the states and saw no traffic. Then was really odd is that externally from another WAN IP i can ping the WAN ip of the pfSense which by default its blocked, So i called my lSP and told them that it has to be them, they told me that everything good by their part. Now how can i prove that its their issue because im sure if i cannot NAT its because their modem is blocking. -
@killmasta93 said in Issue with NAT?:
has happened to them something similar?
its you who is failing. Allow traffic from WAN to your correct vpn port.
-
Thanks for the reply, i checked the rules see the link i have the correct NAT
https://imgur.com/dOobah8.png
-
Hi,
@killmasta93 said in Issue with NAT?:
i configure the VPN
First things first.
You configured "VPN" on what ? Your car ? Phone ? Some network device ? Your pfSense ?
And when you say "VPN" : is it an OpenVPN server ? OpenVPN client ?@killmasta93 said in Issue with NAT?:
Then was really odd is that externally from another WAN IP i can ping the WAN ip of the pfSense which by default its blocked
That's true.
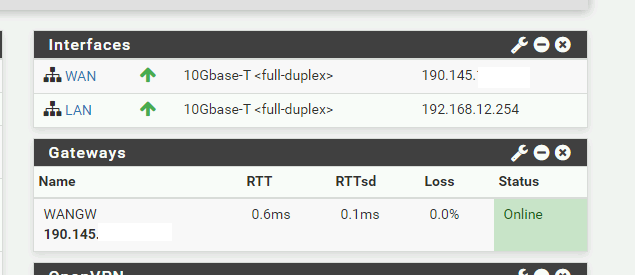
So, let's check something. Does the IP of your pfSense WAN interface matches your the IP your using on the Internet ?So, this IP :
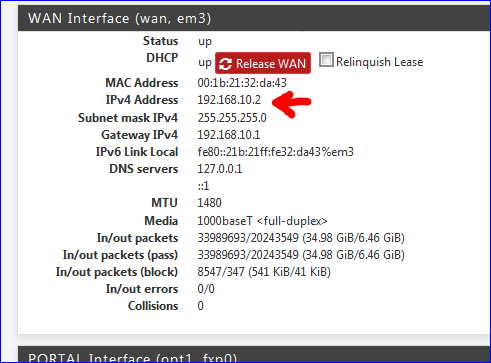
matches the you see when you click on this one http://checkip.dyndns.org link ?
Mine doesn't as you have figured out (192.168.10.2 can not be a "Internet WAN IP" , because I have a router in front of my pfSense.
The WAN interface of pfSense initially does not contain any rules when you set up pfSense.
This means pfSense will block everything. ICMP included. This means : no ping reply.
If you still get a reply from your WAN IP, using some other, remote WAN IP (you using the internet connection of the neighbours) then you know that something in front of pfSEnse is replying to you.
This is most often (99,99 %) your ISP device that is in router mode, not modem or bridged device.If your ISP device is in router mode, you have to NAT also that device if you want traffic to come in.
@killmasta93 said in Issue with NAT?:
So then i tried to NAT port 8006 and nothing
A NAT rule to 'NAT' what traffic to what device ??
When you use the OpenVPN server wizard to setup OpenVPN server on pfSense, it will create a firewall rule for you on the WAN interface. Your image shows it as the first rule ! The one that opens port 1194 UDP on WAN, the default config.
A firewall rule only, not a NAT rule, because their is no need to NAT if you run OpenVPN server on pfSense.
@killmasta93 said in Issue with NAT?:
So then i tried to NAT port 8006 and nothing
You're NATting to what device ?
Keep in mind : a NAT rule has it's own page in the GUI. It lists the NAT rules. Every NAR rule has also an underlying firewall rule, which is auto generated (and shouldn't be edited directly). If your "8006" rule is an OpenVPN server rule, why is this firewall rule using UDP and TCP, knowing that OpenVPN can only be one or the other, not both.@killmasta93 said in Issue with NAT?:
hem that it has to be them, they told me that everything good by their part
That's the normal answer. These people - if you managed to actually speak to a human - have a certain know-who about your Internet connection. They know actually a little bit more then you. That is, if you give them the right question, they give you the right answer (they are just reading the answers from a screen in front of them).
Only when you manage to escalate your question to support level 2 or 3 or what ever index they use, you will get real analyses. But these guys will never ever try to make you learn something. That's not their role. If they see that your ISP device is connected and active on their network, all is fine for them. They don't care what you do on your side of the network (== "LAN"), what devices you hooked up.
If you decided to hook up an industrial capable device like pfSense, then you would be the expert ;) So never tell them you use pfSense, support will be over right away ...Like entering the cockpit of a plain. You're the pilot - or the terrorist. Pilot trainees are at school, or in a flight simulator. They don't call traffic control for 'advise'.
-
@Gertjan Thank you so much for the reply sorry for not being clear,
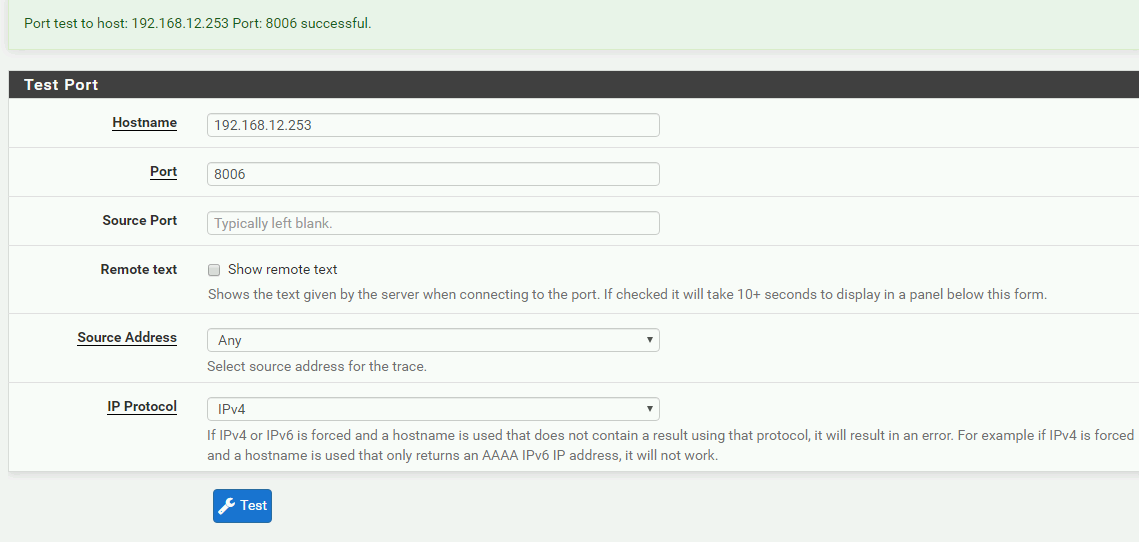
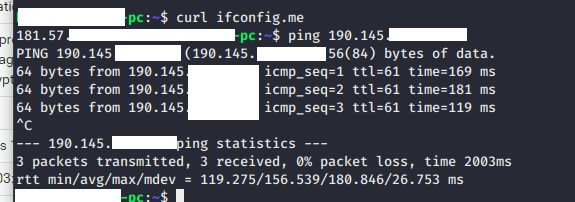
Currntly my WAN shows the true IP which is not an internal IP address see picture but what I was trying to do is to configure the VPN which is port 1194 but was not working on a normal computer, i checked the states no traffic. So what i did is opened port 8006 which is proxmox thinking it might the pfSense. So i did a clean install with 2.4.5 and same issue. called the ISP told then i had a basic TPlink because i know saying that i have pfSense they will blame the firewall.
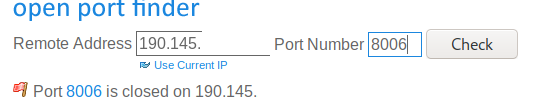
so i did a test port which shows the 8006 is alive. checked on a site to see if the port is opened and is not see picture. and here is the kicker, for some odd reason i can PING the WAN ip of the pfSense being on another WAN ip and i know by default pfSense blocks that. So i now dont know what to do.
-
What are your WAN firewall rules ?
-
Thanks for the reply these are the WAN rules as you see no traffic
https://imgur.com/p0NjyZZ.png
so something funky is going on
-
Not funky.
All goes as planned.
Look at that address, and ask yourself : how is some IP on the Internet going to send something to that non-routable = RFC1918 address ?
It's not. It can't.
Your VPN rule seems fine ;) -
Thanks for the reply, as for the VPN it does not connect either which why i opened the port 8006 to see if was a firewall issue, as for the that rule for got to mention i did that rule though the NAT which creates an auto rule on the WAN
https://imgur.com/ca0cWl8.png
-
Use https://docs.netgate.com/pfsense/en/latest/nat/port-forward-troubleshooting.html to guide you.
The test 5 : use tcpdump to see if there are actually packets coming into your WAN. If not, the problem is upstream.
-
forgot to post back it was an issue with the lSP they had the NAT on the modem and i was going crazy