Strange problem with Synology NAS after installing pfSense
-
<Also posted this on the Synology forum, but this is probably a firewall-related issue>
Wanted to have a separate zone for my IoT devices, so I implemented a pfSense firewall with three NICs: WAN, DMZ (IoT devices that do not need access to e.g. Synology NAS) and LAN (laptops, NAS etc). Seems to work fine, but after the implementation I can no longer access the Synology DS413 web interface. The network shares work perfectly.
Setup before implementing the firewall:
Internet <--> ISP FRITZ!Box 5490 modem <--> 16-ports Netgear GS116 <--> Synology DS413
Setup after implementing the firewall:
Internet <--> ISP FRITZ!Box 5490 modem <--> WAN interface <--> pfSense firewall (v2.4.5) on Lenovo M73 (i3, 4GB/500GB) <--> LAN interface <--> 16-ports Netgear GS116 <--> Synology DS413 (+the other devices)
Changes after firewall implementation:
-
Network range changed from 192.168.178.x to 10.10.10.x (LAN) and 10.10.20.x (DMZ).
-
NAS had a DHCP IP address in the old situation, but this was always the same (configuration in the FRITZ!Box; IP tied to MAC address). In the new situation, I assigned a fixed IP address to the NAS.
-
The Synology Assistant does not find the NAS in most cases, but sometimes it does. After trying many times, I was able to change the NAS's IP address to a fixed address (also specified the right gateway).
-
Moved some devices from the 16-ports Netgear switch (now connected to the LAN NIC) to another switch (connected to the DMZ NIC).
-
Tried to disconnect pfSense firewall from the switch and access the NAS with a laptop with fixed IP. Also doesn't work.
Symptoms I see:
-
Administration web interface does not work. A couple of times I noticed that the certificate warning message is given when trying with a different laptop, but after that warning the connection times out.
-
The NAS can not be pinged.
-
The network shares work fine.
-
The Squeezebox package works fine (port 9002).
-
When doing an nmap scan, I see that the following ports are open: 80, 137, 138, 139, 443, 445, 515, 631, 3483, 9002.
-
I don't have problems with other devices.
Any ideas about what could be the problem here ? I don't have any more myself :-)
-
-
Hello!
I think DSM runs on ports 5000/5001 by default. Are those ports accessible?
John
-
Here you have it :
@oisec said in Strange problem with Synology NAS after installing pfSense:Tried to disconnect pfSense firewall from the switch and access the NAS with a laptop with fixed IP. Also doesn't work.
You're saying :
[ laptop ] <=> [ switch ] <=> [ Synology DS413 ]Also : " NAS's IP address to a fixed address (also specified the right gateway)."
Which excludes the used router as an issue.When there is no router present, the gateway setting isn't needed any more, because non present anyway.
You need an IP and a mask, like,
10.10.10.2 /24 for the [ Synology DS413 ]
10.10.10.3 /24 for the [ laptop ]Thus : for the moment : both should have a minimal static IP setup. Just IP and mask, DNS and gateway are not relevant.
Then you can visit the GUI of the NAS using http://10.10.10.2:5000 or https://10.10.10.2:5001 (just accept and override the cert errors if needed).
This will work if you didn't change other settings on the NAS.As soon as you have access :
set :
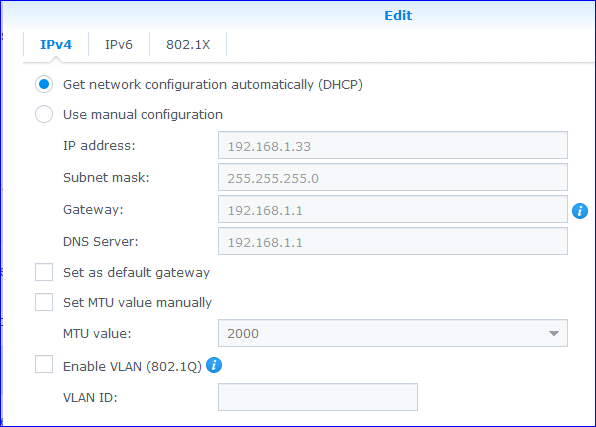
and do what you did on the fritz : set a static mac lease on pfSense as soon as you see the DHCP lease of the NAS on pfSense.
Btw : if you used one of those "how do I protect my Syno NAS" video's on Youtube, it's time to remember that. For example : auto lock out after x login failures ? ;)
@oisec said in Strange problem with Synology NAS after installing pfSense:
The Synology Assistant
What is that ? The thing that came with Syno on a CD ? You should have thrown away that CD right after unpacking the NAS. They are useless, not needed, already outdated when it shipped, will not repair already present broken network setups, will pollute your PC with yet another rather useless program.
Every device on earth is sold with DHCP activated, which means : hook up the device (NAS). Check the local network bookkeeper == your local DHCP server status page, your biggest friend in network world, copy the IP, and your can access your device using the default login codes, written on the box of the NAS or paper that came with the NAS.
This will work ... always. -
@serbus Yes, you're right. And it worked before implementing the pfSense firewall, but after the implementation only the webinterface stopped working. I changed everything to the old situation (removed the pfSense firewall) and now it works fine, including the web interface.
Your question triggered me to do an nmap scan in the current setup and I got some interesting results. Without doing any changes on the Synology, I now see that more ports are open (the ones in bold were not open with pfSense):
The following ports are now open: 22, 80, 111, 137, 138, 139, 443, 445, 515, 631, 2049, 3483, 5000, 5001, 9002, 9090.I didn't do an nmap before starting this whole endeavor with pfSense, but I guess the results would have been the same then. I did not change anything to the Synology configuration (other than its ip address) before or after implementing pfsense.
Must be something with the firewall rules. However since I am already behind the firewall of my ISP's router, I created any/any rules for my WAN, LAN and DMZ interface. I figured that because of that, all traffic would be allowed. My plan was to put my ISP router in bridge mode after fully understanding&configuring pfSense, but I guess that will have to wait.
-
Hello!
I am sure there are lots of people in the forum that could eyeball your firewall/nat rules when you are ready to monkey around with it again.
I run a synology box behind just about every router I setup. It really helps to have a solid firewall in front of those devices and the pfsense/netgate units are a great fit in all sorts of ways.
John
-
Thus : for the moment : both should have a minimal static IP setup. Just IP and mask, DNS and gateway are not relevant.
Good point, but I would expect that having a gateway listed in your network config doesn't hurt even though you don't need it.
As soon as you have access :
set :Indeed, I have changed all remaining devices to DHCP now and will avoid fixed IP's as much as possible. Had some Wifi AP's with fixed IP's, but there's no real need for that. It's very easy to have the FRITZ!Box always assign the same IP address to devices. I noticed that it's a bit more complicated with pfSense, but also quite straightforward.
Btw : if you used one of those "how do I protect my Syno NAS" video's on Youtube, it's time to remember that. For example : auto lock out after x login failures ? ;)
Didn't look at those yet, I just wanted to have a separate network for IoT devices. Next to that I also want to have more monitoring capabilities, so Snort is high on my wish list.
What is that ? The thing that came with Syno on a CD ?
Indeed. I forgot all about that utility until I couldn't access my Synology anymore. Should not be necessary anymore, since I will only use DHCP from now on :-).