NAT Dual WAN
-
Hello,
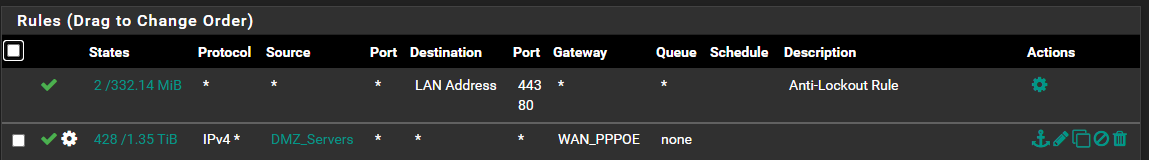
I've recently setup Dual WAN which is all working fine and i have a set of DMZ servers going directly out of WAN1 (non default) via the normal LAN rule. Everything else follows the default gateway via WAN2.

With one particular game i'm hosting on those DMZ servers, I am certain i have a NAT issue causing slow transfer times but can't narrow it down. My NAT rules are
-
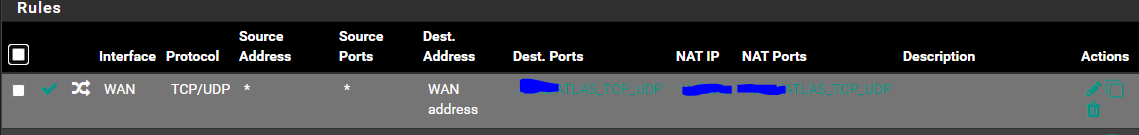
Interface: WAN1
-
Destination: WAN1 Address & Ports
-
Redirect Target: My DMZ Server & Ports
-
NAT Reflection: Pure NAT (So i can play on the server from local LAN)
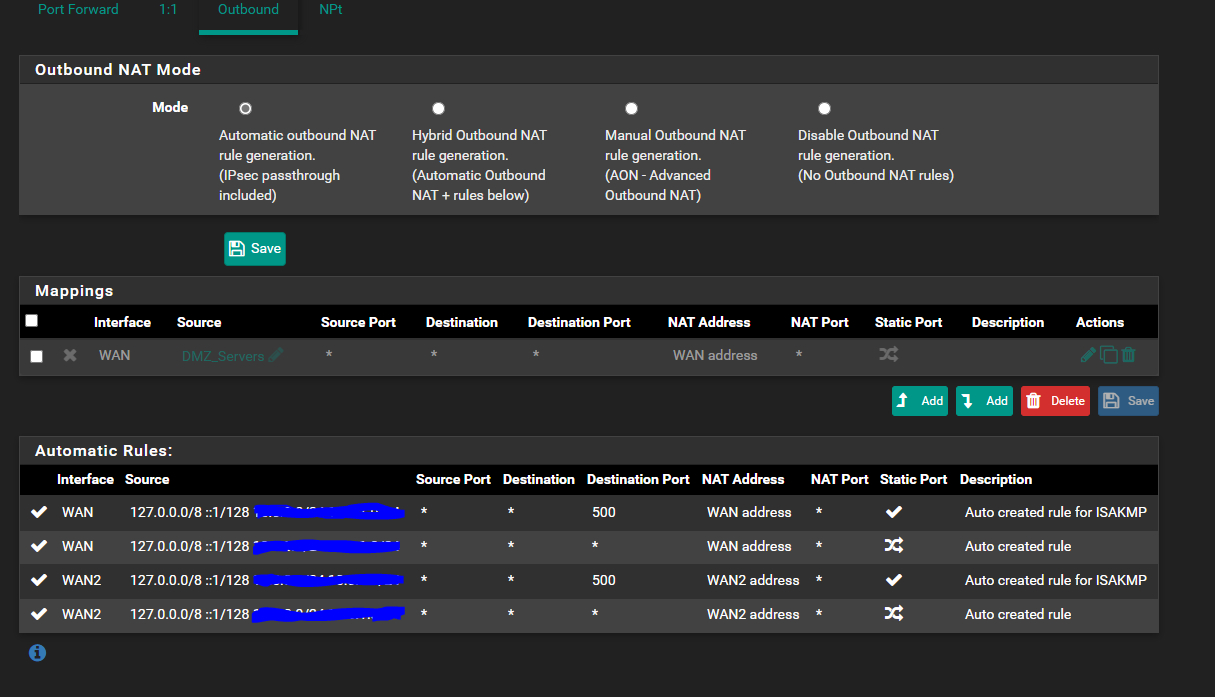
My main question is, do I need to setup an Outbound NAT rule to ensure the DMZ servers ONLY are using WAN1? Currently it's on automatic outbound NAT which has the same source addresses (/24) for both WAN 1 and WAN 2?
If it's not anything to do with Outbound NAT then is there any other considerations i should be making here to ensure DMZ and WAN1 responses are correctly aligned?
TL:DR
Since adding a second WAN connection and routing some servers through it, the old working NAT rules I used previously still work but cause delays.
Any help would be appreciated!
-
-
Take a look at https://docs.netgate.com/pfsense/en/latest/routing/multi-wan.html
You have to create firewall rules that use the WAN1 gateway for outgoing connections.
-
@Crunk_Bass said in NAT Dual WAN:
Take a look at https://docs.netgate.com/pfsense/en/latest/routing/multi-wan.html
You have to create firewall rules that use the WAN1 gateway for outgoing connections.
Appreciate the reply, been so hard getting a steer on this one!
So I think I understand what you mean and that document helped! Does this look correct?
I have added the rule for DMZ_Servers to map to my WAN 1 Address and will then remove the automatic rule created for the WAN 1 (it currently includes the whole subnet!)
-
I'm sorry. It seems like I did not read your post careful enough.
I though you had problems getting the servers in the DMZ out the WAN1 interface.Your Outbound NAT looks good. You should not have to add the manual rule.
Your issue seems to be that your servers in the DMZ take too long to answer an incomming connection?
Which game is it? Maybe it has some trouble with port address translation.
Did you verify the servers use your WAN1 when initiating a connection? -
@Crunk_Bass No problem, yep for the routing out everything seems to be fine. My DMZ servers correctly resolve to WAN 1's IP and everything else to WAN 2's IP.
So in my DMZ I host a website, ARK Game servers and ATLAS Game servers. Everything there is working fine, people can access the site, join the servers no problem.
The issue is specifically with ATLAS, which if your not aware of the game is effectively a collection of servers (in my case 25) making up a single 5x5 map and when you get to the edge of the map it transfers you to the next server grid.
It is these transfers that now take a long time since i've had my second connection. In my case the servers are all on one physical host, but they can be hosted across different hosts.
My understanding is that when they communicate with one another they go out and then back in to the network by default, which is I think where the problem lies. It will transfer me eventually, but it should take all of a couple seconds and instead takes 30+. That is why i wondered if the outbound NAT had something to do with it, but i'm really at a loss :x
For reference -
LAN Gateway rule
NAT Rule for ATLAS
-
Do other players have the same problem or is it just you when you are connecting through pfSense WAN2 to the your own server on WAN1?
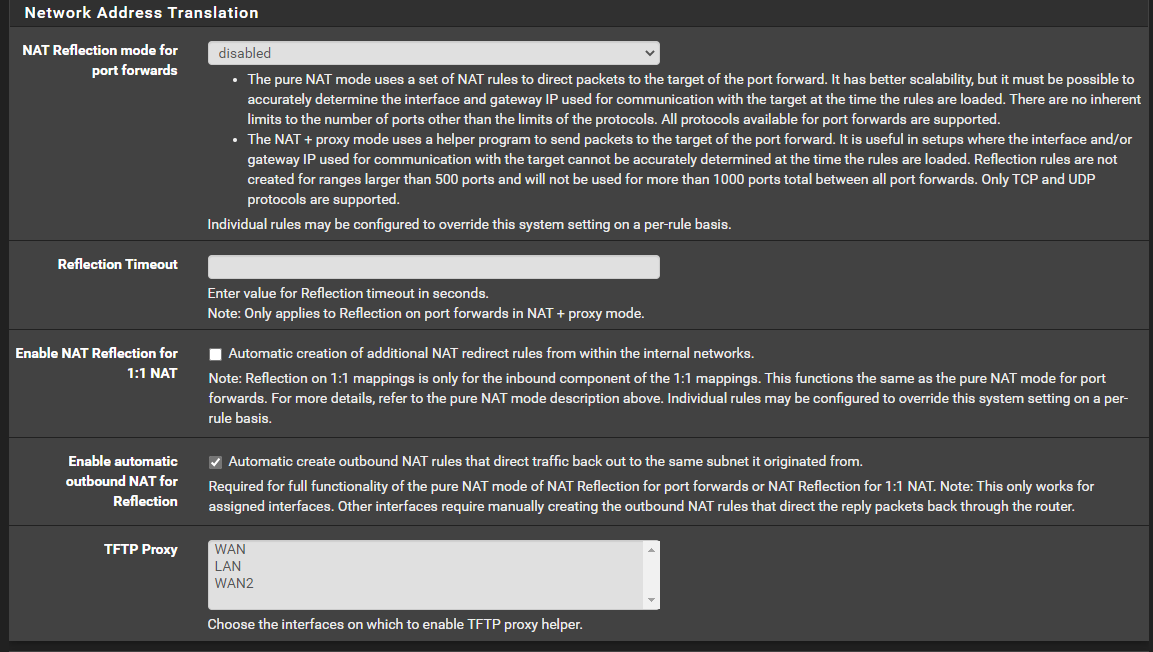
Did you already play with NAT Reflection settings? You can find this unter System / Advanced / Firewall & NAT
https://docs.netgate.com/pfsense/en/latest/nat/accessing-port-forwards-from-local-networks.html -
It happens to both me and other players. As far as NAT reflection goes I do have it set in my NAT Rule for the ports as i previously couldn't join the server when on a single connection. I imagine i might be able too now as my client will come out of WAN 2.
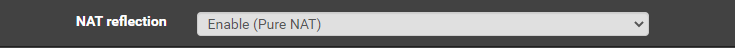
However I do not have it set in the advanced settings, not sure if I now need it for some reason?
Would the fact that the server tries to go out and back in cause an issue? Almost feels like it goes out, but never makes it back and then falls back to the firewalls default routing? Really not sure.