Cannot Access Internet (or LAN over OpenVPN) when Site-to-Site IPSEC VPN Connection Established
-
Hello,
We have a netgate XG-7100 (WAN: static IP address, LAN: 10.0.0.0/18) for our on-premises network with an OpenVPN server running (on tunnel network 172.31.0.0/16) for remote employees to connect to.
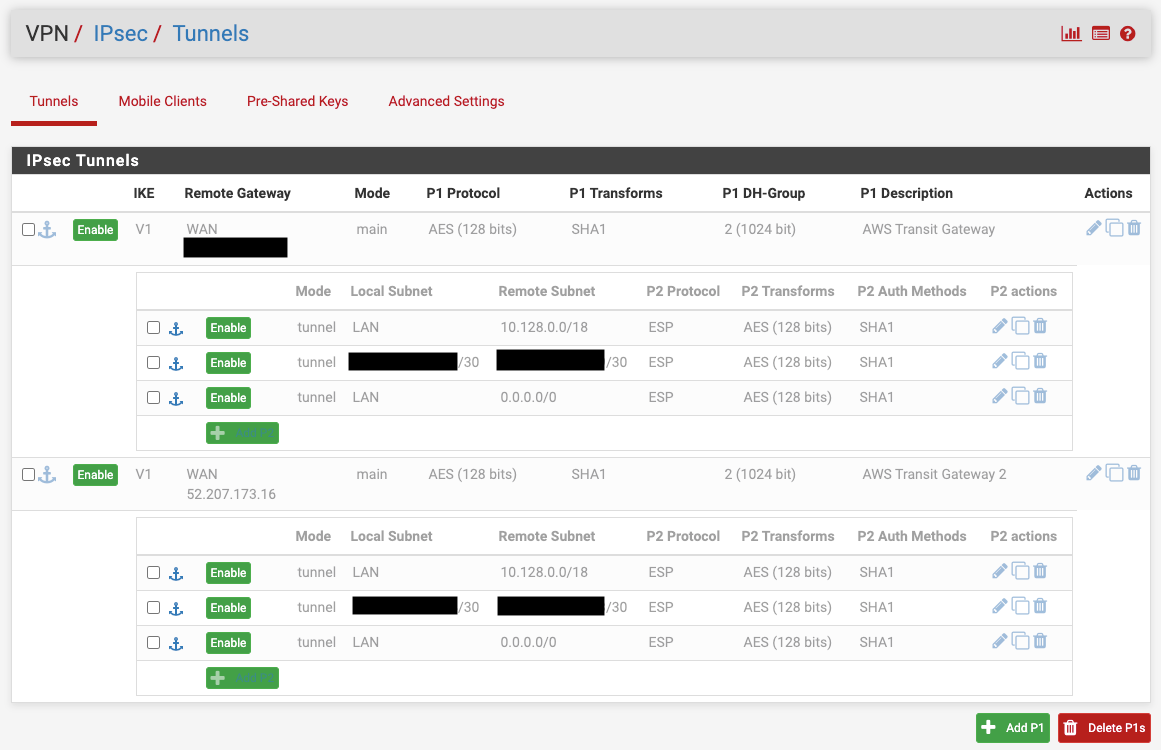
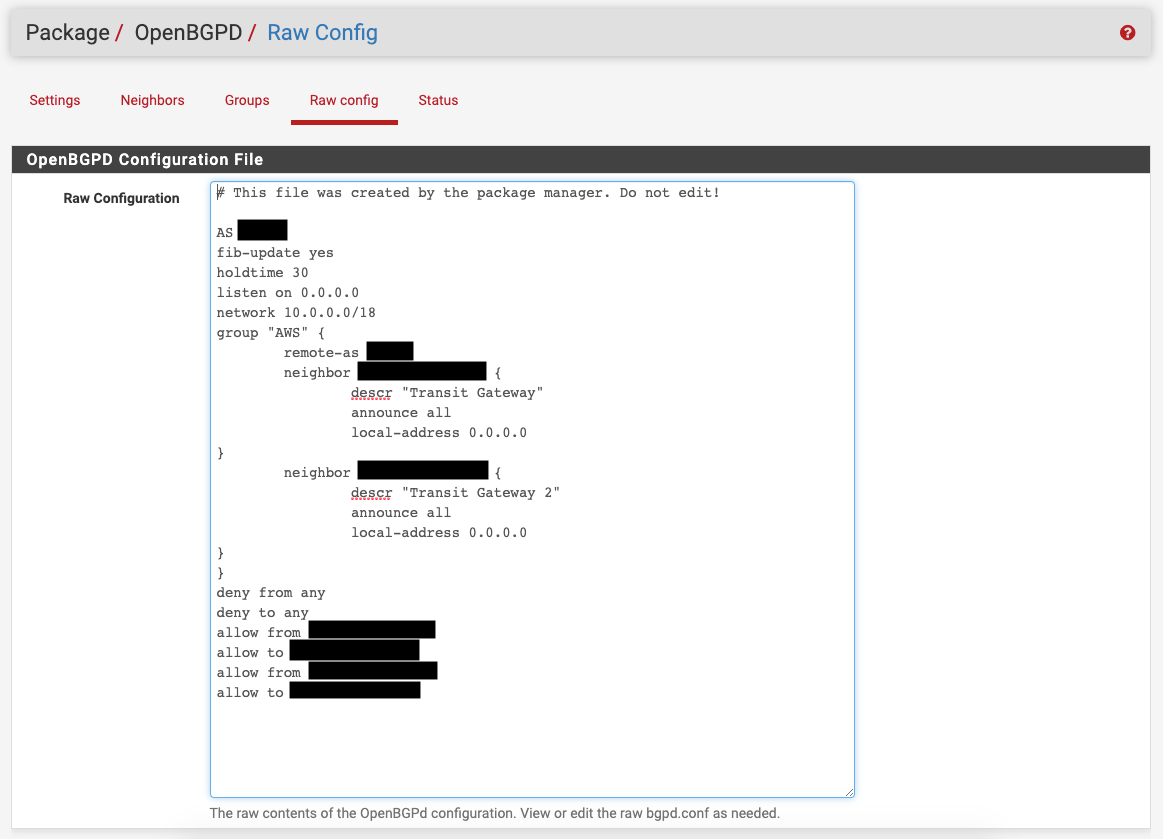
We are also looking to establish an IPSEC site-to-site VPN with AWS Transit Gateway (AWS VPCs on 10.128.0.0/18) using BGP (OpenBGPD) so that we can access internal applications hosted on AWS. We only want traffic destined for AWS to be sent over the IPSEC tunnel, and any general internet traffic should go through the XG-7100. Also, we do want for remote employees connected to the OpenVPN server to be able to also access the AWS resources.
This seemed to work successfully on Friday, but then when checking back 2 hours later, IPSEC tunnel 2 went down, and even after reconnecting it we experience 3 issues. When the IPSEC connection is established:
- Computers on the on-premises network connected to the XG-7100 can no long access the internet
- Remote employees can successfully connect to the OpenVPN server but cannot access the on-premises network (not even the XG-7100 GUI at http://10.0.0.1) or the internet
- We no longer see the AWS BGP neighbors subnets advertised in the route table (under OpenBDPG status), though we did on Friday and did not change any settings
These issues are reproducible as they disappear if we disable the IPSEC connection.
Can you please help point us in the right direction for how to resolve this? Screenshots of settings are attached. Thank you in advance! (Note: We disabled IPSEC due to the above issues, but normally only enable the LAN-0.0.0.0/0 Phase 2 rule for each tunnel per AWS Support's instructions.)
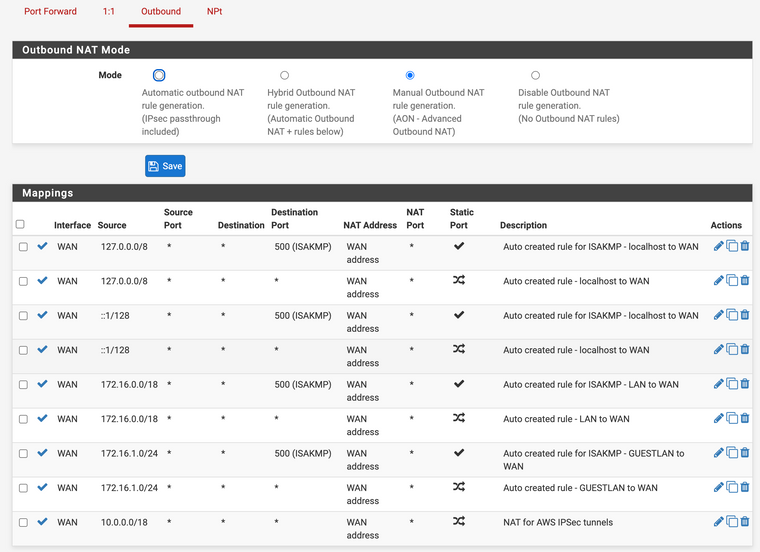
Firewall NAT Outbound Rules:
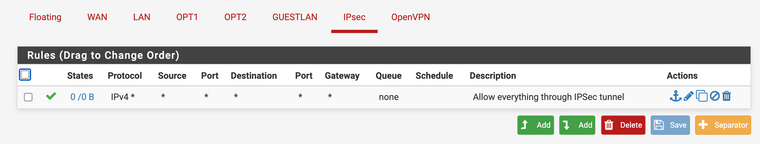
Firewall IPSEC Rules:
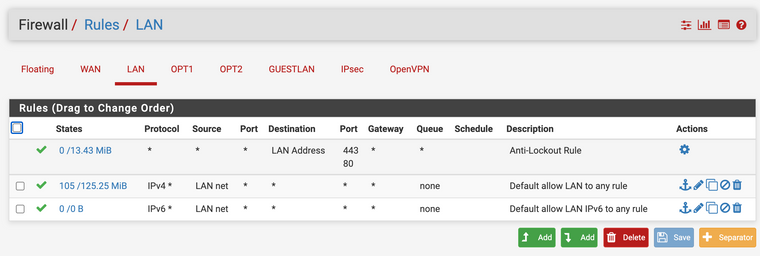
Firewall LAN Rules:
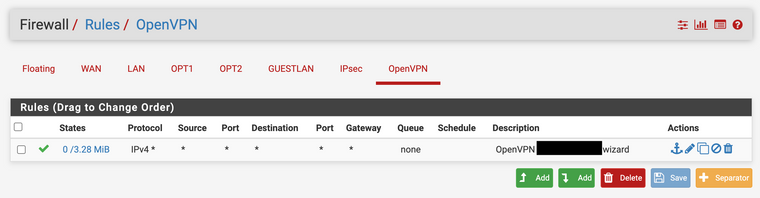
Firewall OpenVPN Rules:
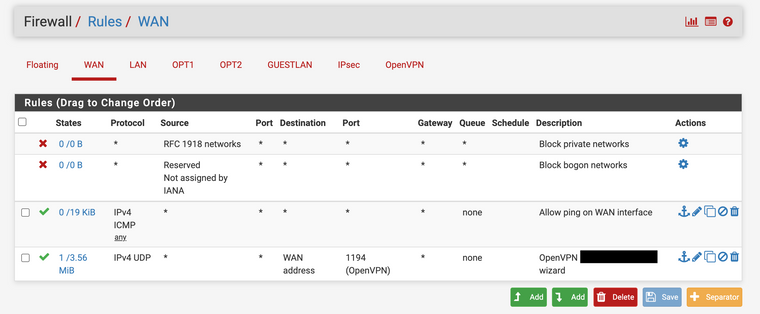
Firewall WAN Rules:
IPSEC Tunnels:
OpenBGP Configuration:
-
Any ideas here? Thank you!