Newbie Setup Advice - Few General Questions
-
At present I have the following setup:
Dual Router/Modem [Asus DSLAC68U]
Wired Devices:
- UnRaid Server for Plex / Nextcloud
- Hue Bridge
- Main 4K TV (Through Powerline)
- Old Qnap NAS for onsite backups
WiFi Devices:
- Linux Desktop PC / Laptop / Harmony Hub / Hifi's / Chromecast Audio / Secondary TV / Phones etc
I access Nextcloud through a subdomain / reverse proxy setup within UnRaid and Plex is currently port forwarded for outside LAN access.
Now everything works and I have no real need for Pfsense firewall other than I like to tinker and i'm curious! Perhaps I'm totally wrong so advice please as all I have is a tiny bit of knowledge, enough to be dangerous to myself:
- I'm thinking it may be better to separate out various things such as having all the I.O.T stuff kept apart from other bits or does this not matter? Would this be done by putting it on its own VLAN?
- Setup a guest WiFi, apart from everything else.
- Possibly make the Nextcloud connection more secure than reverse proxy? If so how?
- Anything else strike people as needed with current setup?
I can get hold of a Qotom like pfsense box with i5-7200u CPU / 6 1Gbit Lans / 8GB Ram and 128GB SSD.
- Thinking of getting a Draytek Vigor 130 modem and then using the current combined thing as just an access point for Wifi. Good or bad plan? Should I use a better AP than this?
- Do I need a switch to achieve the above or can I do all this from just the pfsense box?
Again I must stress this is just a home hobby / learning experience. I've read lots of threads but think I'm getting myself confused now.
Any advice on the above much appreciated.
-
Hello,
There are many questions, but this should not be a problem:
I. Is the ASUS device currently in modem or router mode?
(double- NAT or not)you should use the pfSense, if you really want additional protection around you and your IT enviroment
it's a firewall + everything else (so you also need to change your mind when you start using it)I see you have - usual SOHO stuff, these will be clear from your description, but in fact they require a serious configuration:
(precisely, because these are so many things)according to your steps:
-
absolutely right, you definitely need to segment your network = VLANs (or many real
interfaces) (IoT / WLAN / home / office/ game / etc) -
this is the minimum (guest WiFi and guest VLAN)
-
I think, have to talk about this later, if you have mastered pfSense
-
hmmmm???
-
Yes, that's for sure, look for one that can handle VLANs
UBNT UniFi , Cisco WAP series, etc. -
the pfSense is not a switch, it is a NGFW + router + etc., but in factory releases there are some type that has a switch chip
but yes I suggest getting a good, manageable switch (VLAN capable), like Cisco SG350 series or other (I prefer these)
this Qotom is chasing me, but I have no experience with it so I can't say anything .... (slant-eyed)
just to say that for starters, if you can afford it you would prefer this:
https://www.pfsense.org/products/+++++(but don’t think it’s a place for advertising...(I have no such intention)
it just helps you avoid lots and lots of problems like Qotom)
-
-
This post is deleted! -
@DaddyGo thanks for the time taken to reply, it's much appreciated.
Thanks for the time taken to reply it's appreciated and cleared a lot of queries up that I had.
I shall look at discarding current modem / router and getting a better dedicated AP to go with the Draytek and a dedicated switch. Currently leaning toward a UBNT device for an AP and shall look at Cisco for a switch.
The pfsense device I was looking at wasn't actually a Qotom, just very similar. With six Lans I assumed it would act like a switch too. Obviously not?
The reason I went for Chinese single box was it seemed more powered than the official Netgate stuff with an i5 intel..
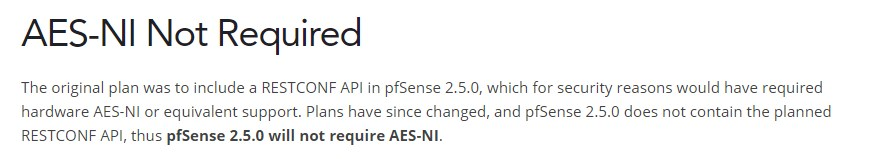
Looking at a SG-3100 for example it doesn't seem to have AES-NI which I was led to believe was vital for future support. It also doesn't have much ram?.
Is this not that important then?
-
I recently installed pfSense for the first time on my home network, and your question #1 was what I used it for. Having a strong perimeter doesn't accomplish as much as it used to, if there are devices on the network that are mobile, and will leave the network and come back on a regular basis. Risk they get compromised off network and then come back on and infect everything else.
I used pfSense to isolate my Qnap on it's own segment. One segment for all user devices - laptops, desktops, phones, TVs, Rokus, etc. Qnap on its own segment. Restricted file sharing, Qnap management console and Plex to only the devices that need it. I also loaded the Snort package on pfSense and enabled the Qnap specific rules.
Overkill yes, considering I could have just made sure I had regular offline backups of my Qnap instead. But this was a fun project.
-
Hi,
my experience is that, all kinds of "big" Chinese boxes = end is always crying
Netgate HW:
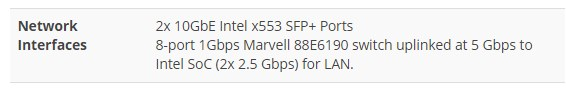
there is also support for the original Netgate hardware, which you can use, if you are a complete beginner@TheYetiWakes "With six Lans I assumed it would act like a switch too. Obviously not?"
you're on the right track, and the answer really "NO"
(it is unlikely that those many ports also have switch properties)from XG-7100 the official hardware series includes a switch capability
if we consider redundancy, it is better to have a separate VLAN capable switch, so if NGFW breaks down, it will still work within your network (internaly)AES-Ni theme (future):
A lot of colleagues run pfSense on older older hardware with 2 to 4 GB of RAM, so muscle strength is not always relevant
I think for your purposes and to be able to learn, a SG-5100 is enough for the first time
-
Thanks for the clarification on a few things.
It's helped me get my mind round everything better and giving me a clearer idea of what direction I need to go to get everything as I want.