Help with redirect port 53 rule and allowing a client to bypass rule
-
I'm trying to allow a client (unRaid box) to bypass at NAT rule that redirects all DNS traffic on port 53 to my piHole.
I have the redirect rule set up and working properly on pfSense, but I want my unRaid client to be able to use static DNS so it doesn't have to get filtered through the piHole as it's unnecessary and slows down certain apps within unRaid.
I've tried going into the static DHCP settings for the client and setting the static DNS, but that doesn't work as the NAT rule still catches everything.
I think I need to set a rule for the client above the NAT rule but not sure how to or what it should be.
Can anyone assist?
-
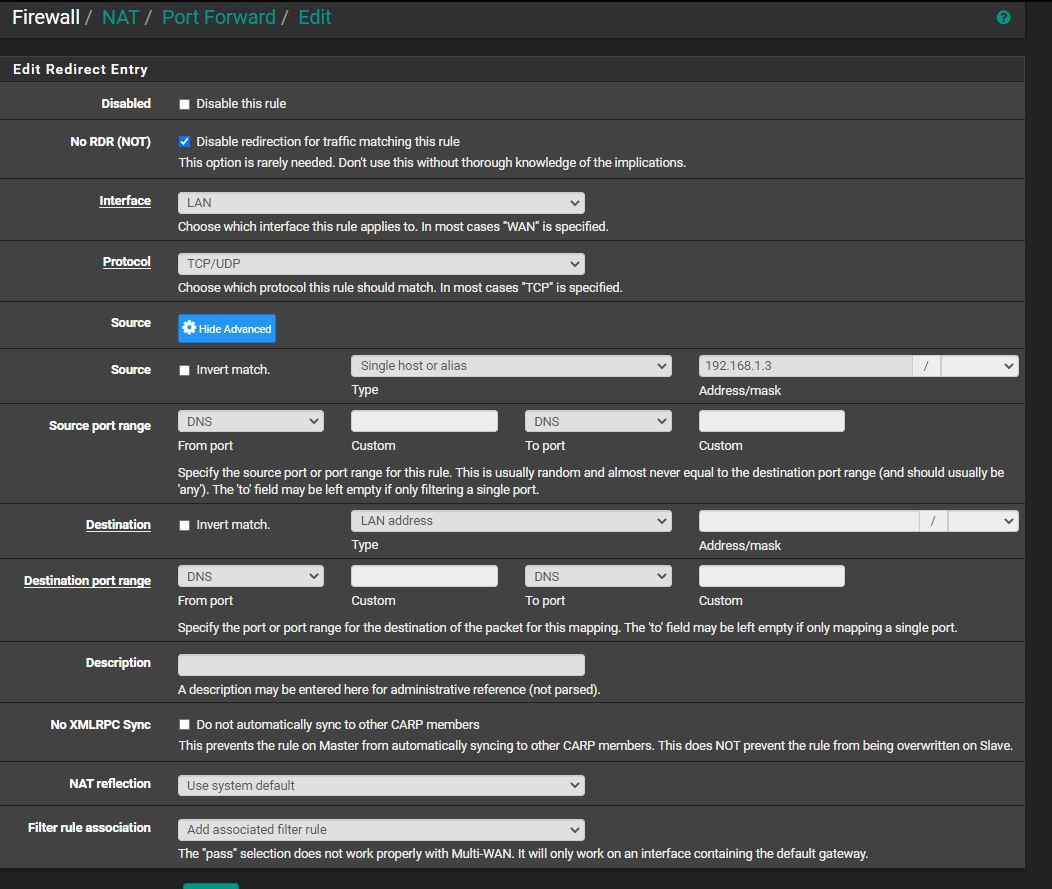
Make a DO NOT NAT rule on that interface with the IP address of the unraid as the source and put it above the general port forward. It should be what amounts to a copy of the redirect rule that forwards DNS for everyone but with No RDR checked (which eliminates the target fields) and a limited source address to match. The ports should still be TCP/UDP 53.
-
Thanks for the reply and help Derelict.
Can you tell me if I have it right in the pic below?
-
Don't set source ports.
-
Awesome, thank you.