IPSEC established but no tftp or UDP
-
So here is the deal. I know I am missing something simple.
I have a pfsense virtual machine for a client. Its behind an old cisco buisness router. The cisco router has the vm in a DMZ so as to not prevent the VM from connecting to any external IPs.
So to my surprise pfsense is able to make a connection with AWS VPC via IPSEC this way. I would show you the picture of the IPSEC status page but I'm at work not home. The status page for IPSEC has been up for like a week now straight like a boss.
So the way Pfsense VM is configured is it has 2 NICs. 1 WAN and 1 LAN. WAN has a static ip of 192.168.1.201. LAN has a DHCP from the cisco firewall, 192.168.1.50 I think. (I am aware I can disable the firewall and firewall scrub all together and that is what I have set but I figured the WAN side was causing an issue)
So it works. I can ping my VM in AWS VPC. After some googling the only thing I had missed was setting rules in the firewall to allow all traffic to and from the IPSEC. (all using the WAN ip address with the firewall and firewall scrub disabled)
However this client needs to use tftp to get and put to the AWS cloud but whenever I try to send or receive any data it times out.
I put in a ticket with AWS and they have assured me that UDP ins't being blocked. The cisco router on the client end isn't blocking UDP. I was able to download a torrent and send/recieve data via tftp to and from the WAN device on pfsense to another node in the system.
I can ping. I can ssh to the host. But UDP traffic seems to be blocked by the tunnel on the firewall in both directions.
Are there any more seasoned and experience pfsense gurus with any tips and or advice?
I know this post may seem vauge so if there is something you feel you need to know let me know.
-
@joedoe47 said in IPSEC established but no tftp or UDP:
However this client needs to use tftp to get and put to
Hi,
if TFTP - pfSense, then this is my idea....

BTW:
@joedoe47 "I know this post may seem vauge so if there is something........................."
but otherwise you really showed little of your system, rules, etc.
-
heh. I know I constantly hear people say that they need pictures to see what the heck a user has done.
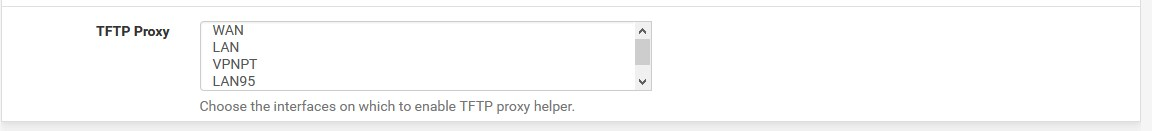
I googled on netgate and they said as a troubleshooting technique I should first make sure the tftp proxy is disabled and then if it still doesn't work on pfsense to enable it.
So at the moment it is enabled for both WAN and LAN.
Give me a second. I'll get you some more detailed images sir.
-
This post is deleted! -
Okay so update. It seems there is a firewall rule thats the issue. Not even with pfsense.
There is another firewall in between the pfsense and the internet. So the assumption was that "well since we are doing a 1:1 nat nothing should stop UDP packets.
But the problem is on the side of this router which is blocking tftp packets.
Pfsense is doing its job as it should. The issue is the primary gateway.
-
@joedoe47 said in IPSEC established but no tftp or UDP:
Pfsense is doing its job as it should. The issue is the primary gateway.
I believed it was not a pfSense issue
since I have been using TFTP for a long time to upgrade IT devices FWsdual -NAT is never good, try to eliminate it if possible...
(as if we were wrapping the gift in two separate boxes (which we put on top of each other) at Christmas, more exciting but takes longer to obtain)