Windows Server DNS Server can't forward to pfSense
-
USER COMMAND PID FD PROTO LOCAL ADDRESS FOREIGN ADDRESS root sockstat 96752 13 stream /var/run/php-fpm.socket unbound unbound 52451 3 udp6 *:53 *:* unbound unbound 52451 4 tcp6 *:53 *:* unbound unbound 52451 5 udp4 *:53 *:* unbound unbound 52451 6 tcp4 *:53 *:* unbound unbound 52451 7 tcp4 127.0.0.1:953 *:* unbound unbound 52451 12 stream /var/run/php-fpm.socket unbound unbound 52451 13 stream /var/run/php-fpm.socket unbound unbound 52451 14 udp4 *:52518 *:* root syslogd 45622 6 dgram /var/dhcpd/var/run/log root syslogd 45622 7 udp6 *:514 *:* root syslogd 45622 8 udp4 *:514 *:* root syslogd 45622 9 dgram /var/run/log root syslogd 45622 10 dgram /var/run/logpriv root syslogd 45622 12 stream /var/run/php-fpm.socket root syslogd 45622 13 stream /var/run/php-fpm.socket root php-fpm 17426 3 dgram (not connected) root php-fpm 17426 4 udp4 *:* *:* root php-fpm 17426 5 udp6 *:* *:* root php-fpm 17426 13 stream /var/run/php-fpm.socket root ntpd 37361 20 udp6 fe80::20c:29ff:fe82:c819%em0:123 *:* root ntpd 37361 21 udp4 192.168.101.40:123 *:* root ntpd 37361 22 udp6 fe80::20c:29ff:fe82:c823%em1:123 *:* root ntpd 37361 23 udp4 172.16.1.2:123 *:* root ntpd 37361 24 udp6 fe80::20c:29ff:fe82:c82d%em2:123 *:* root ntpd 37361 25 udp4 172.16.101.2:123 *:* root ntpd 37361 26 udp6 fe80::20c:29ff:fe82:c837%em3:123 *:* root ntpd 37361 27 udp4 172.16.4.2:123 *:* root ntpd 37361 28 udp6 fe80::20c:29ff:fe82:c841%em4:123 *:* root ntpd 37361 29 udp4 172.16.200.2:123 *:* root ntpd 37361 30 udp6 ::1:123 *:* root ntpd 37361 31 udp4 127.0.0.1:123 *:* root login 80435 3 dgram (not connected) root charon 22942 5 dgram (not connected) root charon 22942 8 stream /var/run/charon.wlst root charon 22942 11 udp6 *:500 *:* root charon 22942 12 udp6 *:4500 *:* root charon 22942 13 udp4 *:500 *:* root charon 22942 14 udp4 *:4500 *:* root charon 22942 20 stream /var/run/charon.ctl root charon 22942 21 stream /var/run/charon.vici root starter 22764 5 dgram (not connected) root nginx 57467 5 tcp4 *:443 *:* root nginx 57467 6 tcp6 *:443 *:* root nginx 57467 7 tcp4 *:80 *:* root nginx 57467 8 tcp6 *:80 *:* root nginx 57350 5 tcp4 *:443 *:* root nginx 57350 6 tcp6 *:443 *:* root nginx 57350 7 tcp4 *:80 *:* root nginx 57350 8 tcp6 *:80 *:* root nginx 57077 5 tcp4 *:443 *:* root nginx 57077 6 tcp6 *:443 *:* root nginx 57077 7 tcp4 *:80 *:* root nginx 57077 8 tcp6 *:80 *:* root dpinger 27696 5 dgram (not connected) root dpinger 27696 6 stream /var/run/dpinger_GW_WAN~192.168.101.40~192.168.101.2.sock root devd 415 4 stream /var/run/devd.pipe root devd 415 5 seqpac /var/run/devd.seqpacket.pipe root check_relo 358 3 stream /var/run/check_reload_status root php-fpm 322 3 dgram (not connected) root php-fpm 322 4 udp4 *:* *:* root php-fpm 322 5 udp6 *:* *:* root php-fpm 322 13 stream /var/run/php-fpm.socket root php-fpm 321 3 dgram (not connected) root php-fpm 321 4 udp4 *:* *:* root php-fpm 321 5 udp6 *:* *:* root php-fpm 321 13 stream /var/run/php-fpm.socket root php-fpm 321 14 dgram (not connected) root php-fpm 319 3 dgram (not connected) root php-fpm 319 4 udp4 *:* *:* root php-fpm 319 5 udp6 *:* *:* root php-fpm 319 15 stream /var/run/php-fpm.socket -
@Hekmil as you see, service unbound is listening on all interfaces.
So nslookup shouldn't be complaining.
This is really strange.Can you telnet 172.16.1.2 (pfsense lan) on port 53 from pf cli?
-
@netblues Yes indeed
Yes it works :
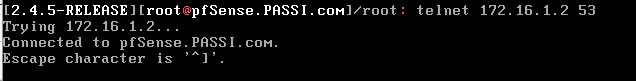
-
@Hekmil so unbound works.
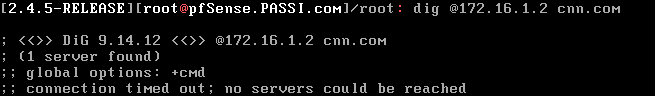
dig @172.16.1.2 cnn.comalways from cli.
-
You need to let the
unboundDNS server within pfSense do the name resolution for you. Forget your NAT gateway DNS. And remove those two IP addresses from the General Settings tab in pfSense. Out of the box,unboundis ready to operate in resolver mode, which means it will query the root servers and proceed down the domain tree to find the IP for the FQDN. If you want to put any address on the General Settings page in that DNS box, put 127.0.0.1. And uncheck that "DNS Server Override" box. You don't want that in your setup.Once you do that, go under DIAGNOSTICS > DNS LOOKUP and see if a domain such as "cnn.com" or "google.com" resolves properly. It should.
Once you get that working, then go back and point your AD DNS Server to forward to pfSense instead of that NAT gateway. DNS lookups should then work properly.
Last tip -- sounds like you may not be fully versed in DNS terminology. Make sure you understand the distinction between a DNS resolver and a DNS forwarder. They are not the same. In your case, I think letting
unboundon pfSense operate in its normal resolver mode is what you need. However, if you truly want to use DNS forwarding, then you will need to configure that setup inunboundon pfSense. -
And you may have an issue with routing while trying to use that NAT gateway DNS server. Does it have a proper route back to your Windows client? In other words, can it find it?
The fact you mentioned pings not working from the Windows client side would indicate either a firewall rule or rules that is blocking it, or there is a routing problem upstream such that the pinged host doesn't know where to send the reply.
First thing to check would be to sniff the WAN interface of pfSense while pinging an external host from the Windows client. Do you see the packet leave the pfSense WAN? If not, check firewall rules and default routes on the Windows client. If you see the packet leave the WAN but no reply comes back, then check upstream routing and/or firewall settings. You can use the built-in sniffer tool available under the DIAGNOSTICS menu on pfSense.
-
@netblues Result of dig :
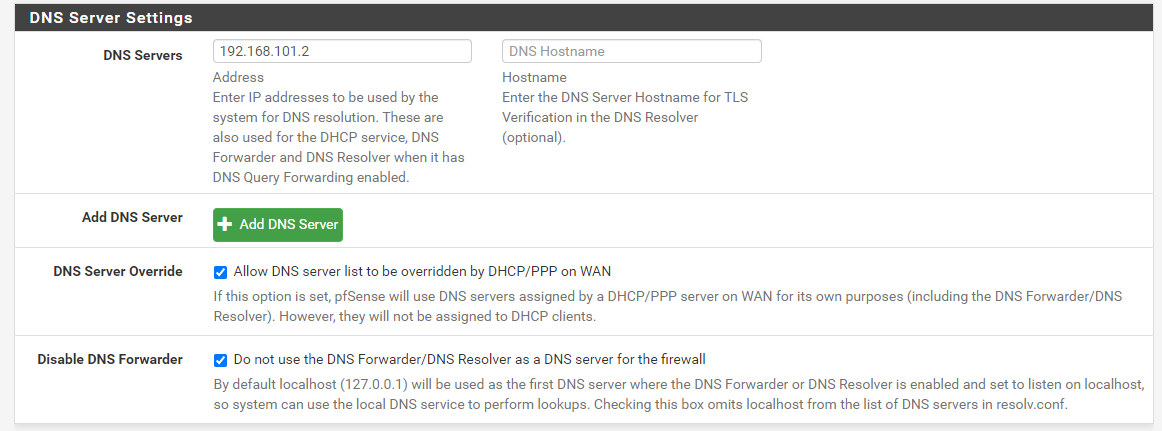
@bmeeks Hum, if I follow what you have said I can't resolve anymore any domain. Only theses settings works for me to resolve domain from pfSense :
My AD DNS Server was never forwarding to my NAT gateway, only my pfSense LAN ip address
About terminology I want to use the resolver mode, I only used the forwarding term to mention the redirection from my AD DNS to pfSense.
My guess was also a route issue, but I have no clue how and where to configure it as my NAT settings come from the Virtual Network Editor of VMware Workstation
-
@Hekmil said in Windows Server DNS Server can't forward to pfSense:
n its DNS server parameters I have set the forward address to my pfSense IP (LAN or WAN interface does it matter ?) which has set my NAT gateway (192.168.101.2) as DNS Server
The DNS setting in that Window you show in your screen cap only affects lookups done from the firewall console. Stated another way, this tells the local DNS client on the firewall (not server) which DNS server to use for lookups the firewall itself is doing (like from that DIAGNOSTICS menu window).
The only time the IP addresses put on this screen matter to
unbound(and external clients using pfSense for their DNS lookups) is whenunboundis configured to use forwarding mode. There is a check box on the DNS Resolver page for turning on forwarding.Since resolving does not work, perhaps someplace upstream firewall rules are restricting DNS lookups to only be allowed when originating from the 192.168.101.2 server. So
unboundin resolving mode is getting blocked. If that is the case, turn on forwarding mode withunboundand see if that works. -
@bmeeks I'm not sure which screen cap you are mentionning, the Geneal settings right ? I'm getting a bit confused sorry due to many information here.
So I should keep the same configuration but turning off Resolver and on Forwarder to see if it works (but with a nslookup on the Windows Server)?
-
@Hekmil said in Windows Server DNS Server can't forward to pfSense:
@bmeeks I'm not sure which screen cap you are mentionning, the Geneal settings right ? I'm getting a bit confused sorry due to many information here.
So I should keep the same configuration but turning off Resolver and on Forwarder to see if it works (but with a nslookup on the Windows Server)?
The DNS Settings on the pfSense GENERAL SETTINGS screen (that box where you have put in the 192.168.101.2 server).
pfSense now comes with two different DNS server components. The new one is
unbound, and this program can be either a resolver or a forwarder. The old DNS component isdnsmasq, and it can only be a forwarder. The default out-of-the-box configuration of pfSense is withunbound(the DNS Resolver) enabled and operating in resolver mode. Unless you put something in those DNS boxes on the General Setup page, the firewall will use the localunboundDNS Resolver for name lookups, and the DNS Resolver will attempt to resolve with the DNS root servers by default.The old
dnsmasqDNS Forwarder is disabled by default now. You really don't want to use it. It is under SERVICES > DNS FORWARDER. It should be disabled. You can't run it and the Resolver at the same as both will try to use the same port 53 to listen for DNS requests.If you want to use
unboundin forwarding mode, there is a checkbox on the SERVICES > DNS RESOLVER setup screen to enable forwarding. The help text in that box says that when you enable forwardingunboundwill then forward DNS requests to whatever server you have entered on the SYSTEM > GENERAL SETUP tab down in the DNS Server Settings section.So what I suggested you try is go to SERVICES > DNS RESOLVER. Make sure the checkbox for Enable DNS Resolver is checked. Then scroll down that page to about the middle and check the box for DNS Query Forwarding. The checkbox says "Enable Forwarding Mode".
Since the DNS lookup failed from pfSense when you took out the 192.168.101.2 DNS server, that indicates to me that perhaps something upstream from pfSense is only allowing DNS requests to be handled by that 192.168.101.2 address. So when
unboundtries to contact the DNS root servers directly, it is blocked from doing so. -
@bmeeks Even though what you say is valid, however no matter what settings are in dns resolver, (forwarded, root servers etc, ) under no circumstances dig would return no servers can be reached
for example, digging for something non existent on a pf that has access to internet disconnected..
dig @192.168.31.25 pf.dontexist.net
; <<>> DiG 9.11.13-RedHat-9.11.13-5.el8_2 <<>> @192.168.31.25 pf.dontexist.net
; (1 server found)
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: SERVFAIL, id: 10679
;; flags: qr rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 1;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 512
;; QUESTION SECTION:
;pf.dontexist.net. IN A;; Query time: 2 msec
;; SERVER: 192.168.31.25#53(192.168.31.25)
;; WHEN: Jul 22 22:49:13 EEST 2020
;; MSG SIZE rcvd: 45It returns server fail because IT FAILED upstream.
No servers can be reached indicates a local connectivity problem.
and since we have verified that it is the unbound process that listens on port 53, it can't be a dns forwarder issue.No servers can be reached, means it got nothing back after contacting port 53
Since this is a test environment under vm, I would install a fresh copy of pf, on another machine and I would try digging on its resolver, as a next step. -
@netblues:
I think we are both saying the same thing but in a slightly different manner.I understood the OP to say that when he puts his upstream NAT gateway DNS server IP in the General Setup box on pfSense (that 192.168.101.2 address) that a DNS lookup performed directly on the pfSense console works. And when he removes that IP address and puts in nothing in the box, or else 127.0.0.1 to tell pfSense to use the localhost as the DNS server, his lookup fails. So in that first case, with an upstream DNS server listed in the General Setup tab for pfSense,
digwill use that defined server to make DNS requests to. But if that General Setup tab DNS server IP box is blank (or points to 127.0.0.1), thendigwill attempt to useunbound(the local resolver) for lookups.So to me that indicates that DNS Resolver on pfSense, when it is used and tries to contact the root servers, is unable to do so. Hence the "server fail" message. One reason this might be true is if some upstream network component (remember he described this as a lab VM setup) is restricting all DNS lookups to just that 192.168.101.2 server. So a rule upstream that says "if the destination for DNS port 53 traffic is not 192.168.101.2, then drop it" will cause DNS Resolver on pfSense to fail in contacting the root servers (and any other servers if you were to enable forwarding unless you forward only to the 192.168.101.2 box).
-
@bmeeks I have lab tested these scenarios. The only way to get a timeout- no servers can be reached, is by digging to an non existent dns server, or putting a firewall rule on dns.
Everything else will be a case when unbound can BE reached.
Yes, there are issues with the resolver setup and how it connects to the greater internet, but, the local timeout issue is something different.
To sum it up.
Unbound is running fine on 53, listening on all interfaces, and it cannot be contacted by dig or nslookup from pf cli using the lan ip of pf.
No floating rules. And certainly this should work irrelevant of internet connectivity etc. This is where I start suspecting the vm/or the installation. Any ideas more than welcome. -
Ok so I fully understood what you both said.
I can try make a fresh install with on a different machine to try out if it comes from the VM.
I'll put nothing in the DNS Server boxes of the General Setup to try only using the
unboundfor lookups and set the pfSense to use DNS Resolver -
So I did a fresh install.
I can't check the box "Enable Forwarding Mode" in DNS Resolving tab if I don't specify one DNS Server in General Setup. On both install i get that
Are you really sure I musn't had my NAT Gateway as a DNS server ? Because that's the only way I could resolve something, at least on the WAN interface. If I do that, i get the same error using the LAN ip address when using nslookup SERVFAIL
Old and fresh install appear to have the same issueAlso what's the difference between the DNS Resolving mode + "Enable Forwading Mode" enabled, and the DNS Forwarding mode ?
Edit : With the DNS Resolver + Enable Forwarding Mode checked, I get this from the dig command (both install) :
; <<>> DiG 9.14.12 <<>> @172.16.1.2 cnn.com ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: SERVFAIL, id: 3781 ;; flags: qr rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 512 ;; QUESTION SECTION: ;cnn.com. IN A ;; Query time: 84 msec ;; SERVER: 172.16.1.2#53(172.16.1.2) ;; WHEN: Thu Jul 23 13:35:05 CEST 2020 ;; MSG SIZE rcvd: 36I'm strill not getting why I can't resolve from a LAN interface
-
@Hekmil Now that we have unbound (the pfsense dns resolver) talking to the world, we can move forward.
The best is letting pfsense contact root servers and work the hierarchy until name resolution.
This requires internet access to port 53 servers.
If thats not the case, then you need to specify a forwarder.
(as the webinterface dictates).The difference between resolver with forwarder and plain forwarder is local caching, negative caching, local names, dhcp integration, to name a few.
dns forwarder is a rather old, solution to the same problem.Obviously your nat gateway is filtering dns requests, so using it is the only way to get dns to resolve.
-
@Hekmil said in Windows Server DNS Server can't forward to pfSense:
I'm strill not getting why I can't resolve from a LAN interface
What do you mean ? dig says you can.
-
@netblues yes dig says I can, but if I nslookup again from my lan IP I can't. Still getting the SERVFAIL.
-
@Hekmil server fail means can't get response from upstream.
This is expectedEnable dns resolver forwading to your dns gateway and it will also work
-
@netblues DNS Resolver Forwarding mode is enabled