PPPoE connection problem
-
I am running into a similar problem and @Plittle solution might help out, though he never posted details on how he fixed his issue.
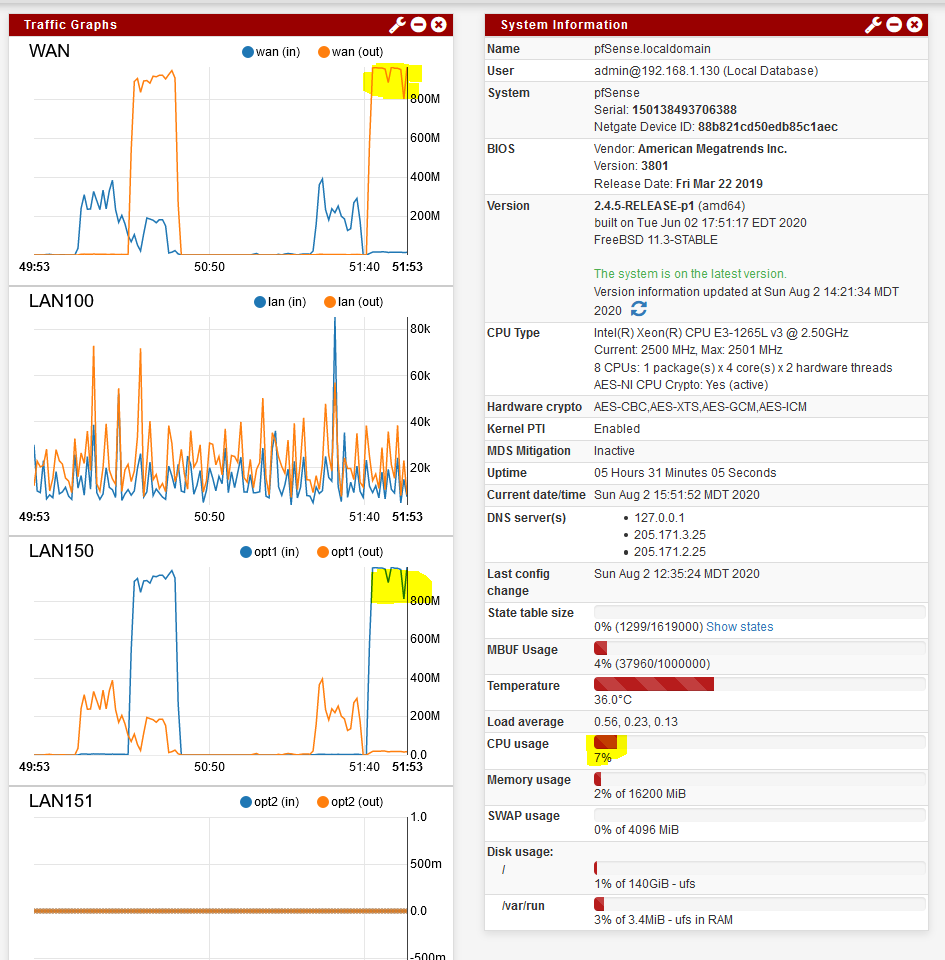
I have my WAN with PPOE configured, and it is showing up/up, with no issues. On the LAN side, I have a LAGG0 configured (4 x 1GE, to make sure I can switch between VLANs within my network and not suffer from any data throughput limitations), with VLAN 100 for "trusted" stations, assigned as LAN interface on pfSense. Interfaces are up, I can access GUI @ 192.168.1.110 with no issues.
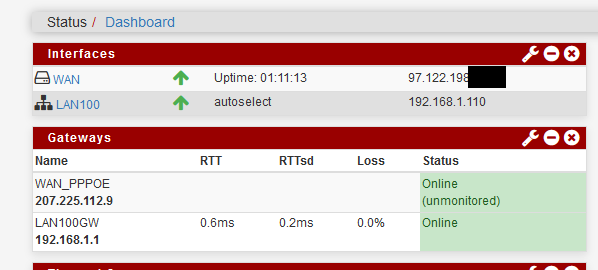
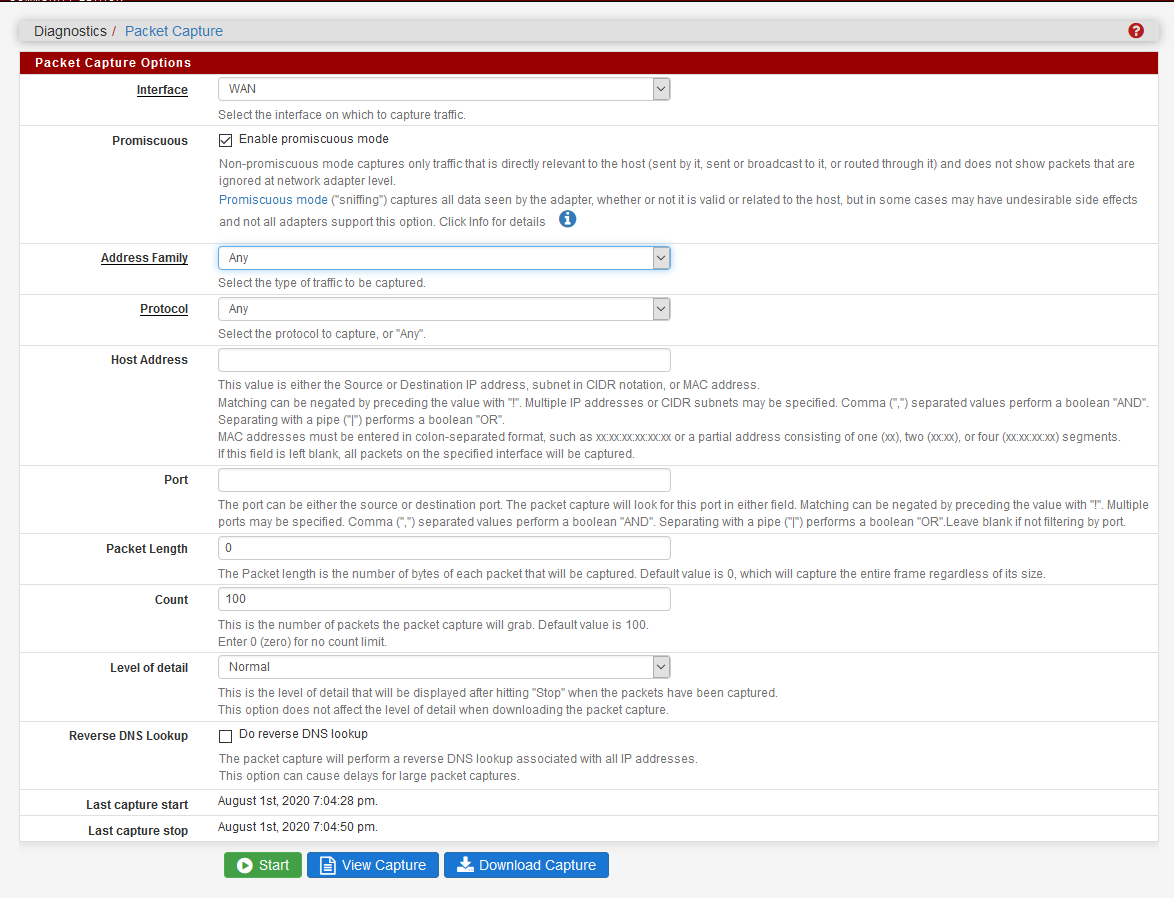
When I point one of the PCs to 192.168.1.110 as gateway out of the network, I am not getting any traffic through, though. Packet capture on WAN interface shows nothing leaving the network for some reason. I looked though NAT and it seems to be fine, with the only two automatically created rules showing in output NAT group, sourcing from 192.168.1.0/24 subnet to WAN with full port mapping.
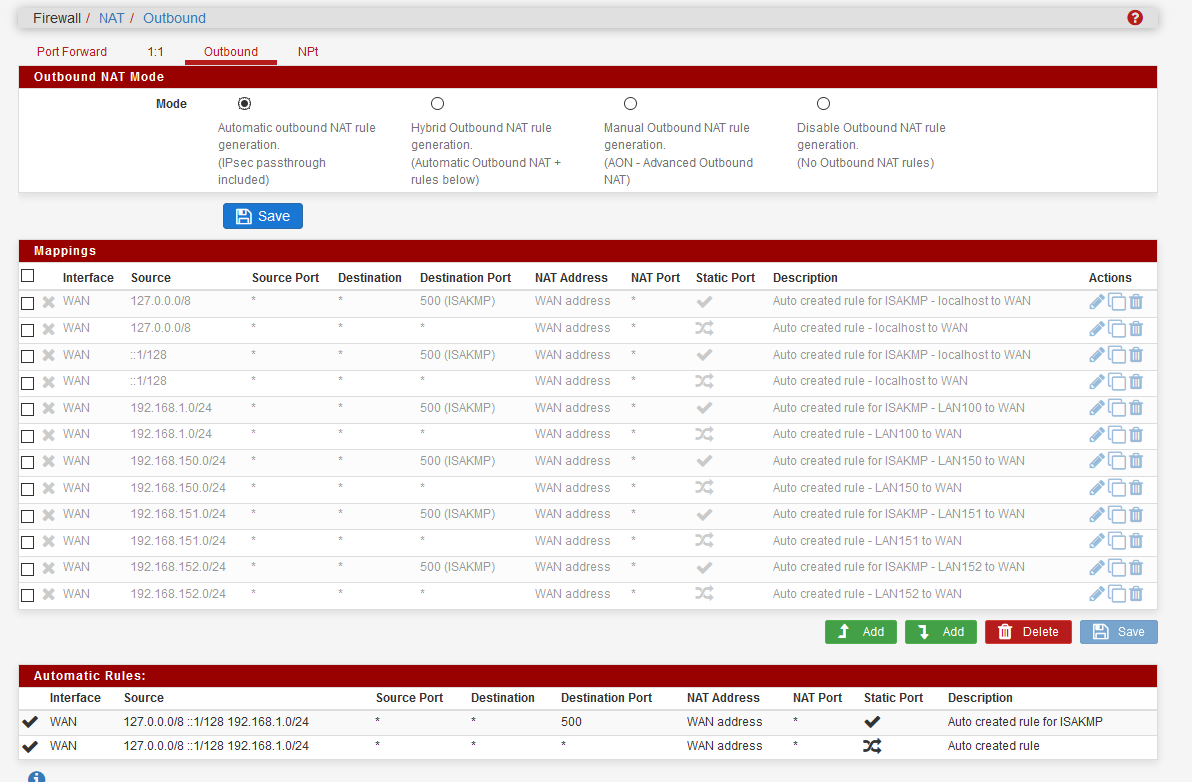
Since I do not see any traffic on WAN leaving the WAN interface, I wonder, though, what the problem might be. I capture on WAN (physical interface) and in promiscuous mode, so I should be able to see everything leaving and entering WAN interface on all subinterfaces, PPOE on VLAn 201 included. I see absolutely nothing.
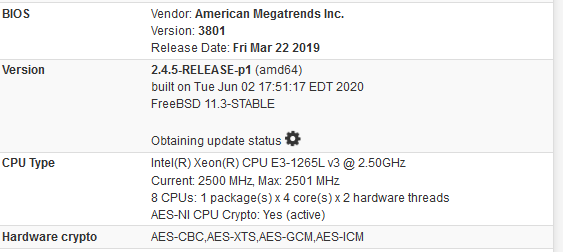
I restarted pfSense a few times, made sure interfaces do come up right, but it still remains a mystery to me what the problem is. I am on the latest build, with plenty of hardware
Any pointers would be welcome. I am slowly going insane here.
-
I split this into a new thread. Your PPPoE connection is UP unlike that other thread.
What us the LAN gateway for at 192.168.1.1?
Most likely the LANGW became the default and hence default route.
Go to Sys > Routing > Gateways and make sure WANGW is set as default and not 'automatic'.Steve
-
Hey there Mmmzon.
I was able to resolve the issue, but Im sorry to say I don't recall what the solution was. What I do remember was working through various iterations of the combination of recommendations in the previous posts, and eventually one or two small settings changes resolved it...
If you don't get anywhere I will goin and check my settings and compare them to what you have posted here for you...so keep me posted please. -
@stephenw10 that is what the issue was, indeed. The Automatic setting was picking the LAN local gateway and not forwarding. I feel stupid now, having looked at it a few times and not connected the dots. For my own personal justification, it was already way past 11pm and I was tired.
Now with the gateway set right, I discovered also I had cables on my central switch messed up, so it was also adding to confusion for sure. Now WAN comes up, stays up and forwards frames correctly.
The last piece of the puzzle was the WAN running at 100M only, when both sides (NIC and switch) are 1GE capable. After poking in settings for some time, I replaced the cable and voila, that was the thing - it seems that one of the pairs is degraded and prevents the link coming up at full 1G/FD.
All in all, the last thing on my plate to validate and fix is the 4x1GE LAG coming up as 1GE only, likely due to some configuration issue on pfSense side.
Unfortunately, in pfSense menu, under LAGG0 port, I do not see any speed settings at all
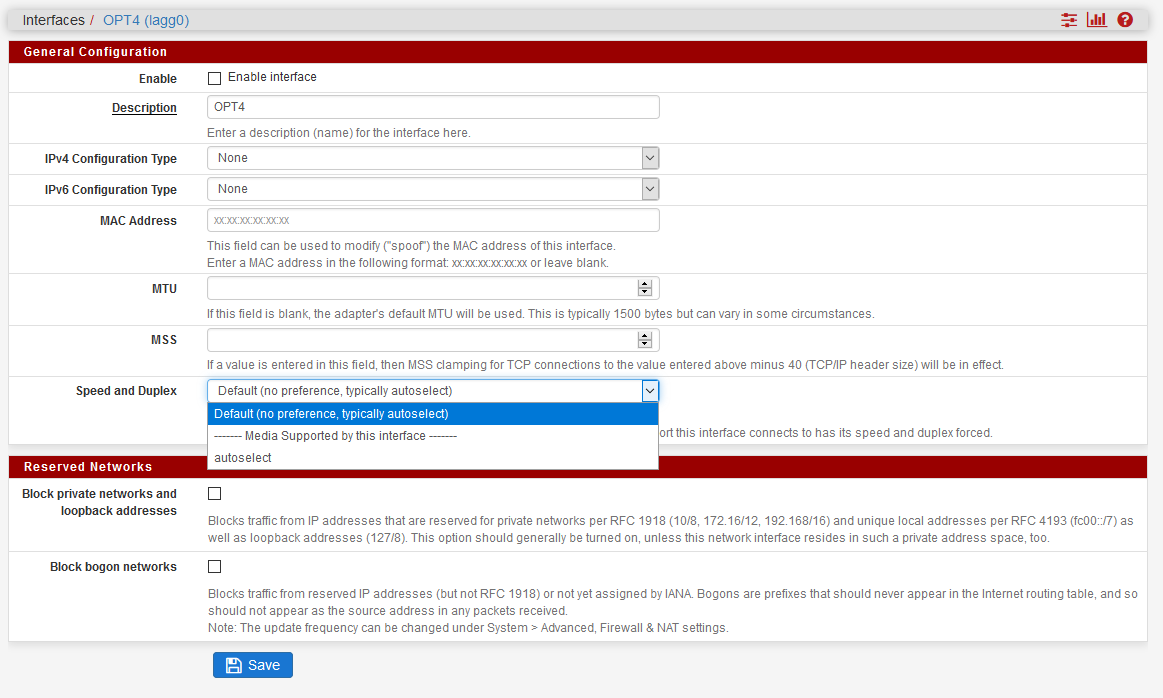
and LAG is already configured in LACP-based mode.

-
The lagg interface type will not show a connection speed in pfSense/FreeBSD or allow you set one. If you needed to it would have to be on the parent interfaces.
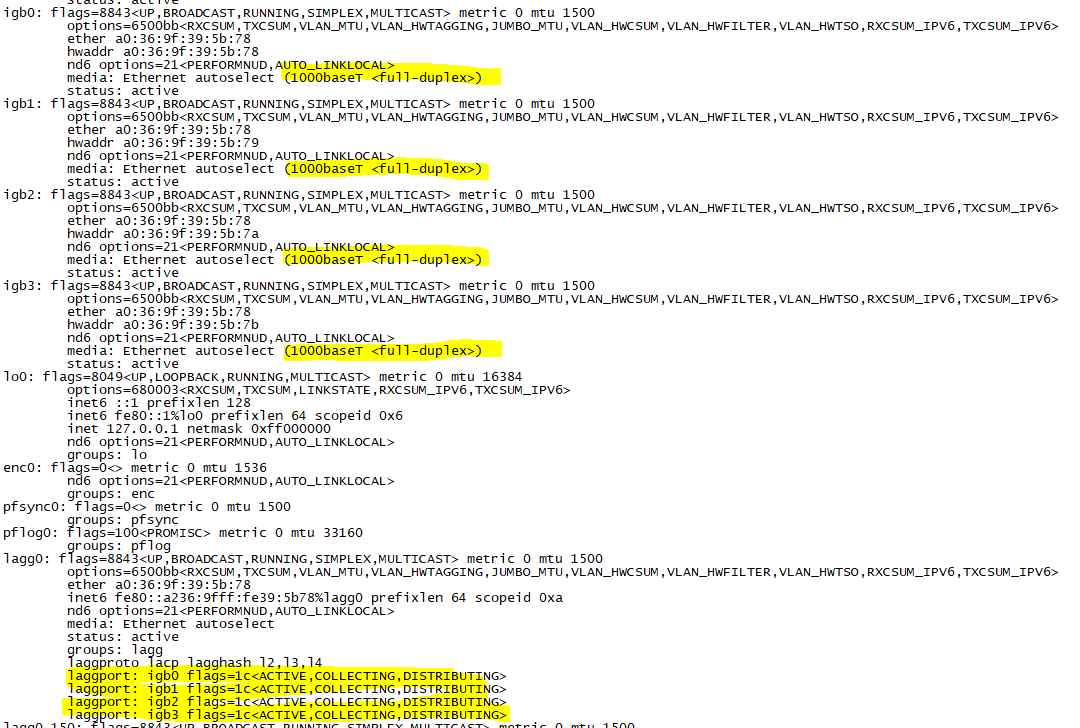
If you runifconfig -aat the command line you will see what they are linked it though.Steve
-
@stephenw10 shell claims all 4 links are connected and distributing
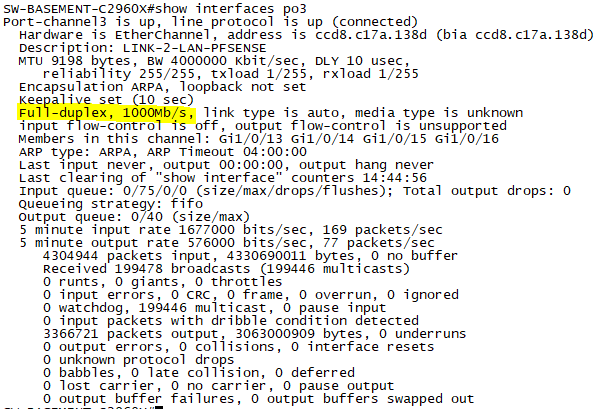
but when I check bandwidth on the Cisco switch side, it claims the whole LAG is only running at 1G, even though I can see all 4 LAG members active and distributing
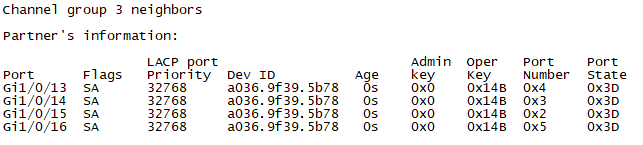
Maybe it is just a quirk of the Cisco iOS CLI, nothing more. I will see whether I can push more than 1Gbps between individual VLANs.
On a good side, doing speed test through FW at 1Gbps, CPU is barely busy, hitting max 4% utilization. Inter VLAN routing will be likely more resource intensive, especially since I want to constrain traffic for specific VLANs to WAN only, and then also speed limit the guest network and IOT network as well.
-
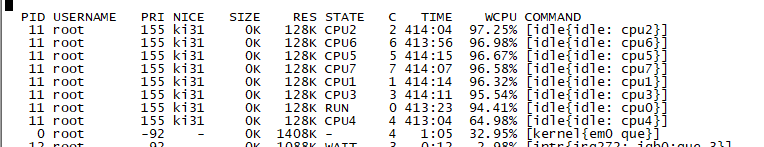
Just for reference if anybody cares, running 1 Gbps upload to OOkla, CPU is barely being used.
-
You should really run
top -aSHat the command line while testing to see how that load is spread across the cores. 7% could be one core at 56%, but it probably isn't. A Xeon E3-v3 isn't going to be troubled by 1Gbps.
Steve
-
@stephenw10 this was the best application for the mobo, CPU, and some memory I had lying around. Plus, I got sick and tired of all the limitations of the stock gateway from Centurylink. pfSense is so much better now that it is running as expected.
Being able to set things up the way I want them to be and control cross VLAN traffic is precisely what I wanted. And I did not feel like spending money on some hardware FW appliance with all the issues they usually run into.