Can't get LAN traffic to connect through WAN
-
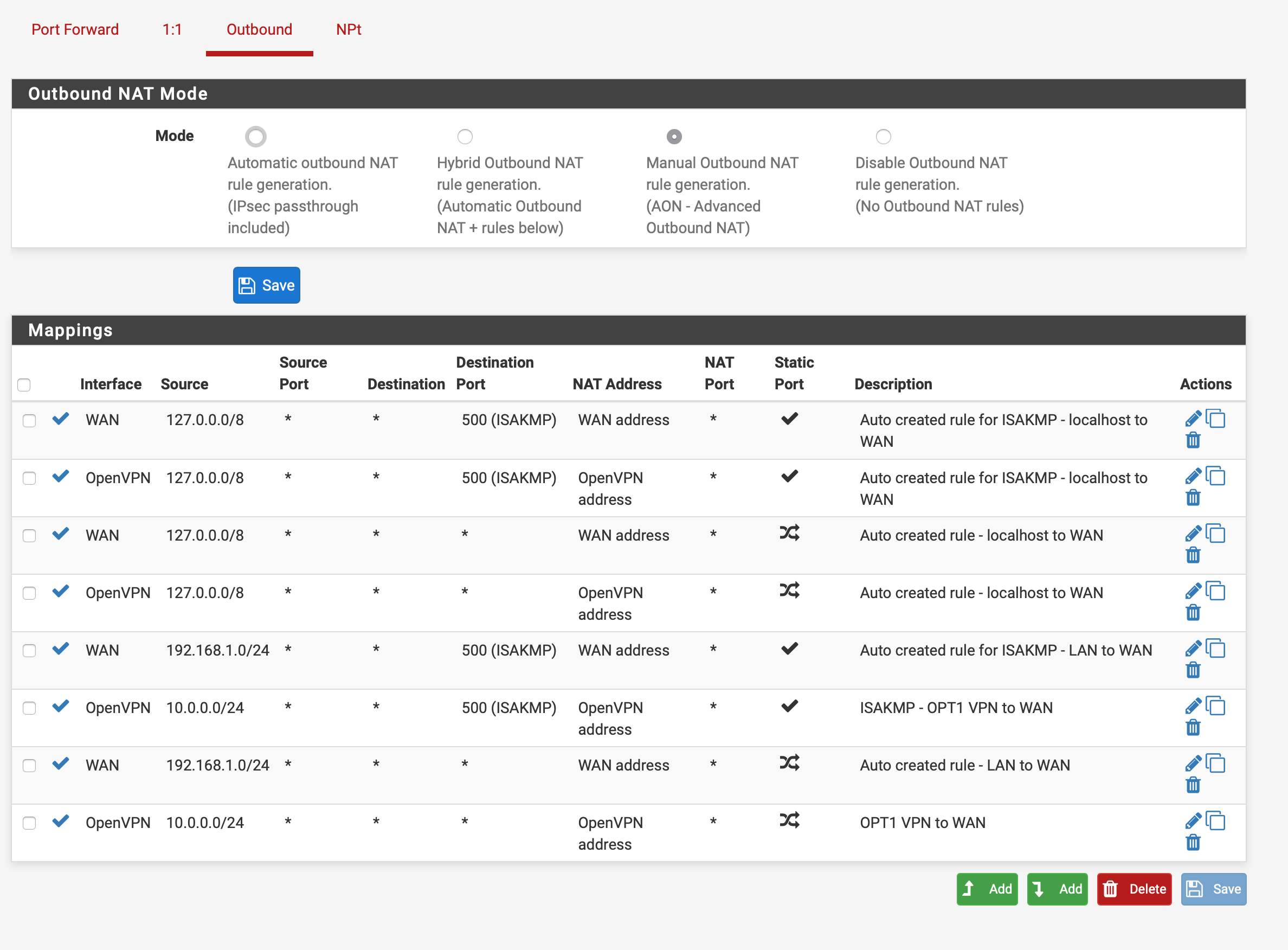
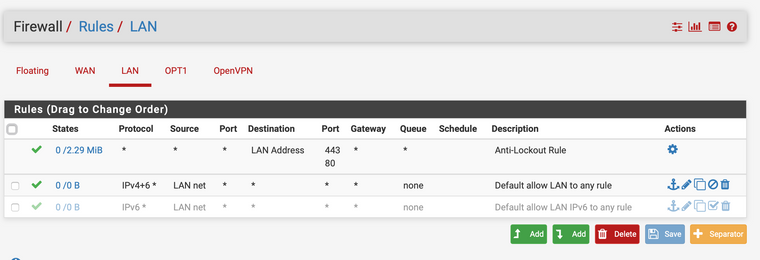
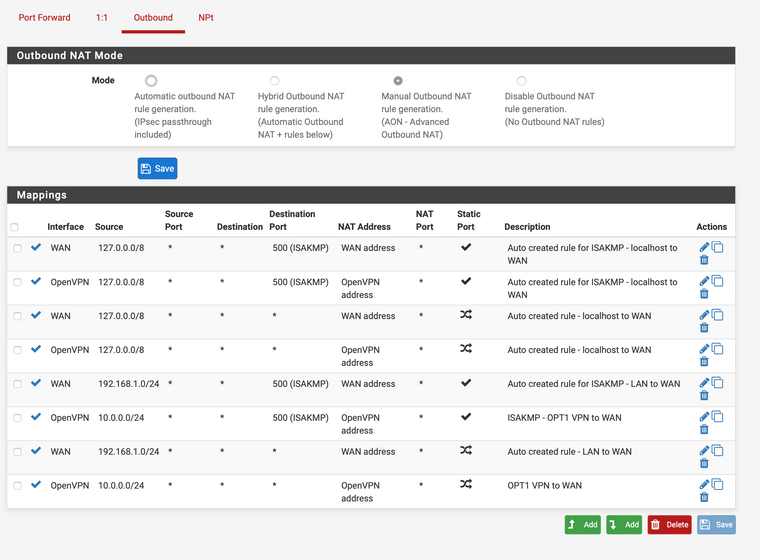
I have an OpenVPN service set up through my OPT1 interface and it is able to connect out through the WAN to the VPN provider. However, now I can not connect through the WAN out to the internet from my LAN interface.
I am stumped. The firewall and NAT rules appear to be allowing LAN traffic out to the WAN.
Screenshots of my settings:
-
@vpnguy said in Can't get LAN traffic to connect through WAN:
I have an OpenVPN service set up through my OPT1 interface and it is able to connect out through the WAN to the VPN provider.
I guess you're talking about an OpenVPN client which connects to a VPN provider, not a service.
If so, what do you try to achieve? Route out your whole LAN to the provider or only certain devices and other should go out to WAN?
To direct traffic over the VPN, you probably have to correct the Outbound NAT rules. What is 10.0.0.0/24? It seems not to be your LAN network. The source in the rule has to be the LAN net and the interface should be OPT1, if it's that one you have assigned to the OpenVPN client instance.
-
This post is deleted! -
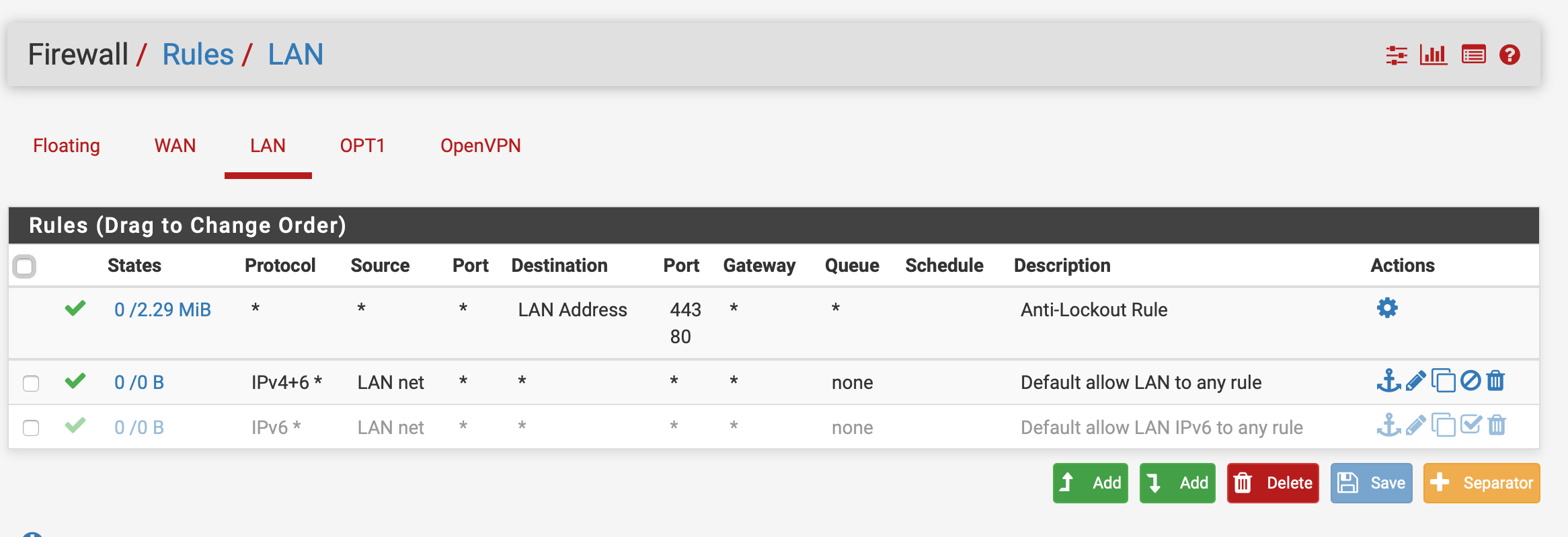
Only the hosts connected to OPT1 should use the OpenVPN interface. The remaining hosts connected to LAN interface should use WAN.
The VPN traffic works fine with those NAT rules but I can not get any hosts on the LAN to connect through WAN.
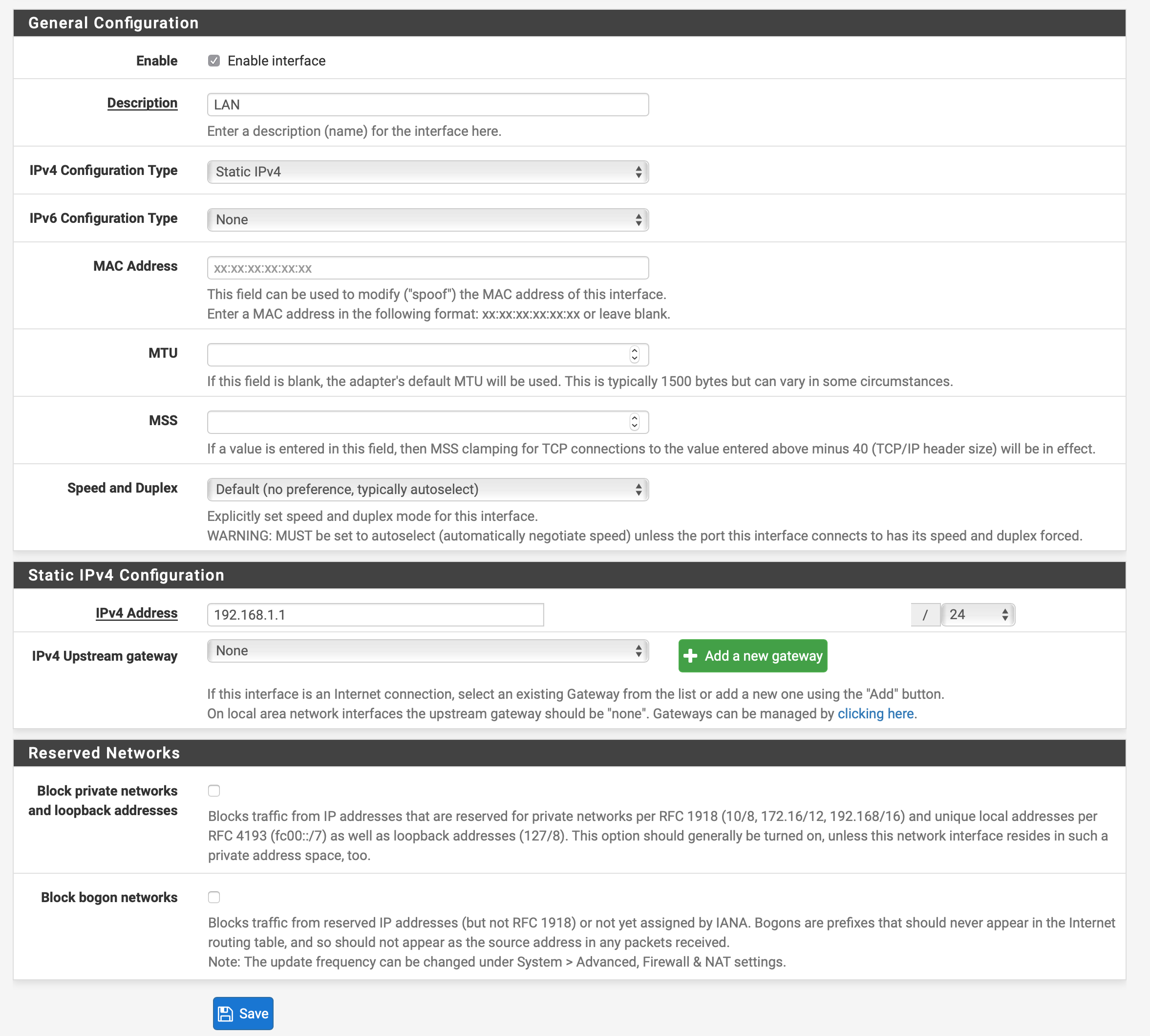
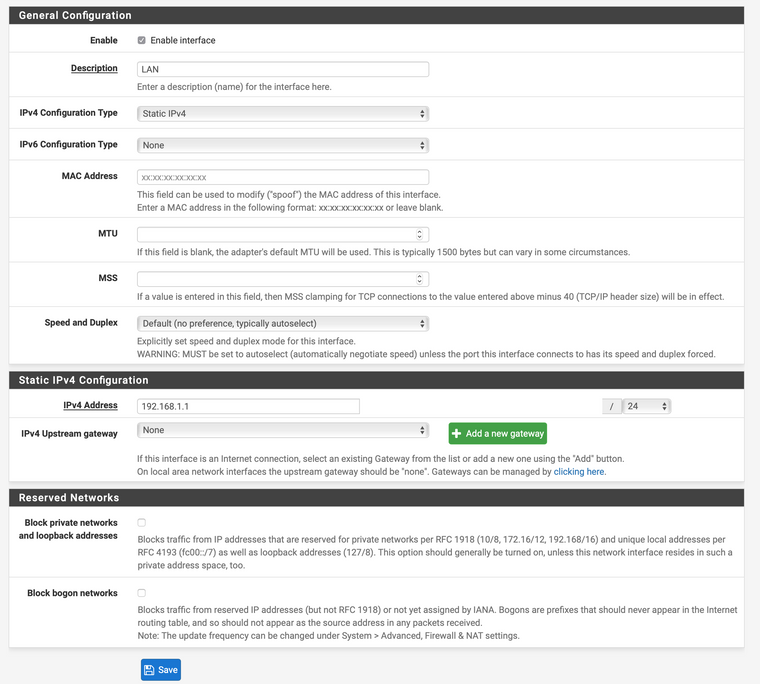
10.0.0.0/24 is the OPT1 subnet. The LAN is 192.168.1.0/24
-
So you need to do policy routing on one of the internal interfaces.
Best practice is to check "Don't pull routes" in the OpenVPN client settings. This prevents that you get the default route set to the OpenVPN and all traffic go out WAN again, though if the vpn client is connected.
Then edit the rule on OPT1 which is allowing outgoing traffic, expand the advanced options, go down to gateway and select OpenVPN gateway.
Consider that after doing this, this rule only allows traffic to the OpenVPN gateway, but no more internal. If you want to access internal addresses from OPT1 (e.g. DNS on pfSense) you have to add an additional rule for allowing it without the gateway set and put it above the policy routing rule. -
@viragomann
For the OPT1 interface Firewall rule "allow IPv4" to any, the Gateway advanced setting only has two options: "default" and "[commercial isp]" I do not want to use my commercial ISP, but there is no OpenVPN option.
In the OpenVPN client settings, under gateway creation, I have selected IPv4 only.
Under my System/Routing/Gateways setting, the default gateway is set as my commercial ISP. I have three choices: [commercial ISP], Automatic, None.How can I create an "OpenVPN" gateway?
-
You have to assign an interface to the OpenVPN client instance first.
Go to Interfaces > Assignments, select the VPN client instance at "available network ports" and press Add. Open the interface settings, enable it and set a proper name. Do no further settings, it is configured by OpenVPN and a gateway is automatically added.
After that you can select the OpenVPN clients gateway in the firewall rule. -
@viragomann Thanks a lot! You were very helpful.
What would you recommend is best way to troubleshoot making sure that there is no cross traffic between OPT1/VPN subnet and LAN subnet? I have been using the built-in pfsense packet capture tool and seeing if there is any "crosstalk." Would Wireshark be more informative?
And it seems that if I enable "Don't pull routes" I can't get connection through VPN, even with all of the other settings mentioned working. When I turn this off, it works fine.
-
@vpnguy said in Can't get LAN traffic to connect through WAN:
I have been using the built-in pfsense packet capture tool and seeing if there is any "crosstalk." Would Wireshark be more informative?
The packet capture shows you the source and destination IP of each packet. What information you need for investigation?
You can also download the capture and import it into Wireshark.@vpnguy said in Can't get LAN traffic to connect through WAN:
And it seems that if I enable "Don't pull routes" I can't get connection through VPN
Have you edited you OPT1 rule for policy routing as mentioned above?
Furthermore ensure that DNS is working on OPT1 devices. You will need to use public DNS server on theses devices to prevent DNS leaking. If you want pfSense to resolve DNS requests you will need an additional firewall rule to allow that. -
@vpnguy said in Can't get LAN traffic to connect through WAN:
@viragomann Thanks a lot! You were very helpful.
What would you recommend is best way to troubleshoot making sure that there is no cross traffic between OPT1/VPN subnet and LAN subnet?
You can setup an explicit BLOCK or DENY rule on the OPT1/VPN subnet from getting into the LAN subnet. Do it like this:
Action: Block or Reject
Interface: OPT1/VPN
Address Family: IPv4+IPV6 (or IPv4 if you've turned off IPv6)
Protocol: Any
Source: OPT1/VPN Net
Destination: LAN NetGive it a good description and save the new firewall rule. Make sure it's at the TOP of your list of rules, and it should work fine. Hope that helps!
Jeff