pfsense CARP/HA not working
-
Hi all,
I'm in the process of setting up a pfsense HA setup at the moment. I'm having a few issues, getting it to work.
My setup is as follows:
pFsense 1:
WAN: 192.168.10.40
LAN: 192.168.100.1pfsense 2:
WAN: 192.168.10.41
LAN: 192.168.100.2Sync Interface: 192.168.20.1 & 192.168.20.2
Virtual IP:
WAN: 192.168.10.45
LAN: 192.168.100.3I have a 5 VLAN with there own DHCPs:
VLAN150: 192.168.150.1
Virtual IP: 192.168.150.3VLAN200: 192.168.200.1
Virtual IP: 192.168.200.3VLAN220: 192.168.220.1
Virtual IP: 192.168.220.3VLAN240: 192.168.240.1
Virtual IP: 192.168.240.3VLAN250: 192.168.250.1
Virtual IP: 192.168.250.3I have configured the HA setup using this guide:
https://vorkbaard.nl/how-to-set-up-pfsense-high-availability-hardware-redundancy/Things that are working:
- Sync works
- Primary and Secondary are identified correctly (Master\Backup)
Issues:
- I cant get my VLANs to work correctly, at the moment my VLANs are identified as master on both my primary and secondary pfsense units.
- I have configured each VLAN as per below:
DNS Server - 192.168.XXX.3 (replace xxx with vlan subnet)
Gateway - same as above
Fallover peer IP: 192.168.100.2 (backup identifies 192.168.100.1 once synced)
I cant workout what I'm missing...
-
@Blue-R And how are the vlans setup?
You also need to assign primary and backup interfaces on each vlan both on primary and secondary.
And vlan interfaces of each node must be able to communicate directly and be on the same broadcast domain. (aka lan)Can you ping from primary interface vlan the backup vlan ip?
I guess you can't -
Thanks for the reply @netblues .
The VLANs are setup in my switch, Master and Backup are connected to trunk ports. All other ports are assigned as required to the applicable VLAN.
When you say you need to assign primary and backup interfaces on each vlan. I think I'm doing this when I set the "Failover peer IP" to 192.168.100.1 on backup and 192.168.100.2 on master?
-
@Blue-R Yes.. carp interfaces don't differ if they are over vlans or physical.
You should be able to ping the two interfaces between them directly.
Carp backup continiously monitors primary via multicast.
Make sure these are allowed in your vlan switch setup -
Bit more info, looking through my logs I found the following:
"Failover CONNECTACK from dhcp_lan: remote failover relationship name dhcp_opt3 does not match " - On master
"Failover DISCONNECT from dhcp_opt3: Connection rejected, invalid failover partner. " - On secondary
My firewall rules are not lock down at the moment.
-
@Blue-R There is no point troubleshooting dhcp when you have two nodes as master.
Solve this first. -
@netblues - Yup, agree. I'm looking through my L2 switch (DGS-3100-24), I've confirmed:
- IGMP snooping is off.
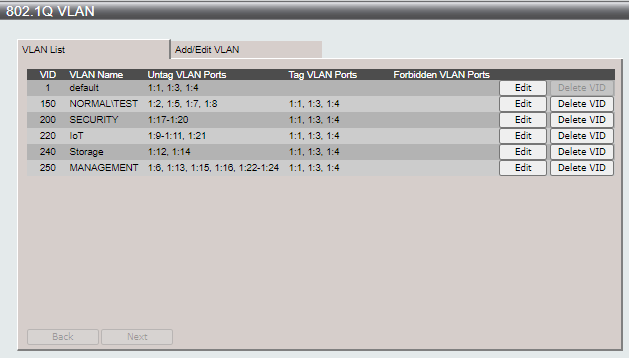
- VLAN are setup as follows:
- All other functions are turn off.
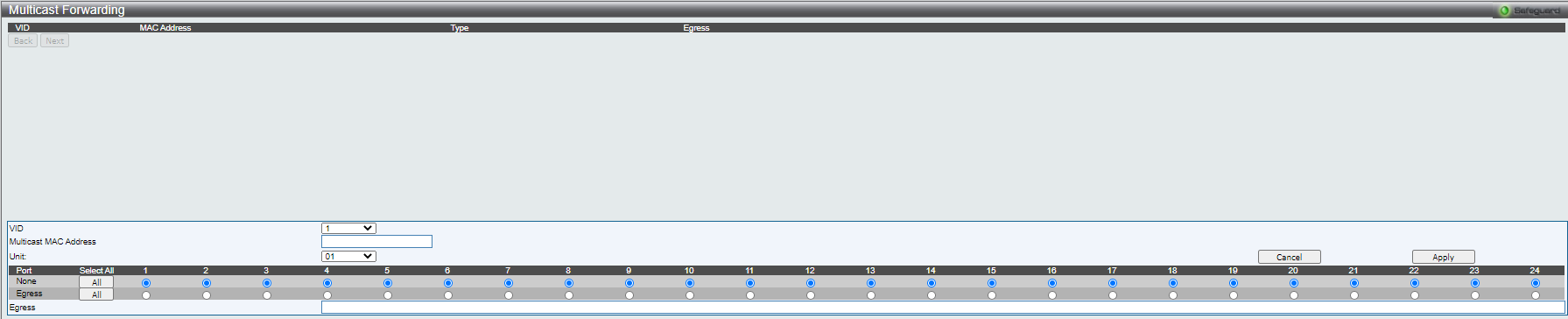
- In the forwarding and filtering sections, there is a option to do multicast forwarding which is currently turn off.
-
@netblues said in pfsense CARP/HA not working:
@Blue-R Yes.. carp interfaces don't differ if they are over vlans or physical.
You should be able to ping the two interfaces between them directly.
Carp backup continiously monitors primary via multicast.
Make sure these are allowed in your vlan switch setupWhen you said "You should be able to ping the two interfaces between them directly."
Do you mean 192.168.100.1 and 192.168.100.2? -
@Blue-R All the lans (and the vlans too) pinging within the same subnet
-
Thanks @netblues
I worked out what my issue was, I made a rookie mistake when creating the VLANs on the secondary pfsense machine.
The VLAN subnet should have been 192.168.150.2, but I assigned 192.168.150.1 which meant .1 was duplicated twice on the network.
Once that was corrected, everything works fine now.